Jaarboek no. 89. 2010/2011 - Koninklijke Maatschappij voor ...
Jaarboek no. 89. 2010/2011 - Koninklijke Maatschappij voor ... Jaarboek no. 89. 2010/2011 - Koninklijke Maatschappij voor ...
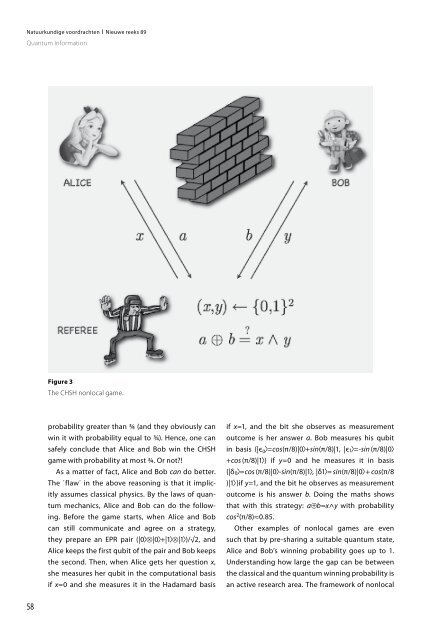
Natuurkundige voordrachten I Nieuwe reeks 89 Quantum Information 58 Figure 3 The CHSH nonlocal game. probability greater than ¾ (and they obviously can win it with probability equal to ¾). Hence, one can safely conclude that Alice and Bob win the CHSH game with probability at most ¾. Or not?! As a matter of fact, Alice and Bob can do better. The ΄flaw΄ in the above reasoning is that it implicitly assumes classical physics. By the laws of quantum mechanics, Alice and Bob can do the following. Before the game starts, when Alice and Bob can still communicate and agree on a strategy, they prepare an EPR pair (|0>⊗|0>+|1>⊗|1>)/√2, and Alice keeps the first qubit of the pair and Bob keeps the second. Then, when Alice gets her question x, she measures her qubit in the computational basis if x=0 and she measures it in the Hadamard basis if x=1, and the bit she observes as measurement outcome is her answer a. Bob measures his qubit in basis {|є0>=cos(π/8)|0>+sin(π/8)|1, |є1>=-sin (π/8)|0> +cos (π/8)|1>} if y=0 and he measures it in basis {|δ0>=cos (π/8)|0>-sin(π/8)|1>, |δ1>= sin(π/8)|0> + cos(π/8 )|1> }if y=1, and the bit he observes as measurement outcome is his answer b. Doing the maths shows that with this strategy: a⊕b=x^y with probability cos2 (π/8)≈0.85. Other examples of nonlocal games are even such that by pre-sharing a suitable quantum state, Alice and Bob’s winning probability goes up to 1. Understanding how large the gap can be between the classical and the quantum winning probability is an active research area. The framework of nonlocal
games not only nicely demonstrates the nonlocal behavior of quantum mechanics, but it also suggests concrete experiments that enable to ΄prove΄ the nonlocal behavior of Nature. Quantum Cryptography The aim of quantum cryptography is to make use of the quantum mechanical behavior of Nature for the design of cryptographic schemes. The most wellknown example is quantum key distribution (QKD). QKD enables two parties, Alice and Bob, who do not share any secret information, to agree on a secret key K, such that an eavesdropper Eve, who can listen into the whole conversation, learns (nearly) no information on K. The secret key K can then for instance be used as an encryption key to encrypt a message that Alice wants to securely communicate to Bob. Without quantum mechanics, the above task of key distribution is known to be impossible, unless Eve’s capabilities are restricted (like her computing power). QKD works as follows. Alice chooses two sequences x1,...,xn and θ1,...,θn of random bits. For every i, she then prepares a qubit in state Hθi |xi> (i.e. |xi> if θi=0 and H θi |xi> if θi=1) and sends that qubit to Figure 4 The BB84 quantum key distribution scheme. Natuurkundige voordrachten I Nieuwe reeks 89 Quantum Information Bob. Bob chooses a sequence θi’,...,θn’ of random bits and measures (for every i) the i-th qubit in the computational basis if θi’=0 and in the Hadamard basis if θi’=1. Let x1’,...,xn’ be the resulting bits that Bob observes. From the elementary properties of the computational and Hadamard bases, as discussed earlier, it follows that xi=xi’ whenever θi=θi’ (and xi and xi’ are independent otherwise). Furthermore, the intuition is that if Eve tries to gain information on xi by measuring H θ i | x i> (when it is communicated to Bob), then, because she does not know θi, it is likely that she uses the wrong basis and that way destroys information on xi; this may then be noticed by Bob (in case θi=θi’). The scheme proceeds as follows. Alice and Bob exchange their choices of θ1,...,θn and θ1’,...,θn’, and they dismiss all positions i with θi≈θi’. Therefore, for all the remaining i-s, xi is supposed to coincide with xi’ (but may not be so due to interference by Eve). Next, Alice and Bob exchange xi and xi’ for a random subset of the i-s, and verify that xi=xi ’ for these i-s. If there are too many errors, then Alice and Bob conclude that an eavesdropper Eve has been interfering with the communicated qubits, and they abort. Otherwise, they conclude 59
- Page 7 and 8: INHOUD Diligentiaprijs voor Scholie
- Page 9 and 10: VERSLAG VAN DE KONINKLIJKE MAATSCHA
- Page 11 and 12: Oprichting in 1793 Het Gezelschap t
- Page 13 and 14: N.Th. Michaelis 1898-1904 Dr. E.H.
- Page 15 and 16: ALFABETISCH REGISTER VAN DE VOORDRA
- Page 17 and 18: Natuurkundige voordrachten I Nieuwe
- Page 19 and 20: Natuurkundige voordrachten I Nieuwe
- Page 21 and 22: Natuurkundige voordrachten I Nieuwe
- Page 23 and 24: Elektriciteitopslag in batterijen m
- Page 25 and 26: De vermogensdichtheid van een batte
- Page 27 and 28: Figuur 3 Het effect dat vacatures (
- Page 29 and 30: Schakelbare spiegels: een samenspel
- Page 31 and 32: Applications Beside their purely fu
- Page 33 and 34: hydrogen absorption properties of t
- Page 35 and 36: Gammaflitsen: extreem nieuws uit de
- Page 37 and 38: ster ontstaat. Het directe bewijs v
- Page 39 and 40: Figuur 2 Als we voor alle 2704 gamm
- Page 41 and 42: gammaflits kan miljarden jaren na h
- Page 43 and 44: Genetica en genoomonderzoek naar ve
- Page 45 and 46: zingen in de code aanwezig die aang
- Page 47 and 48: omdat we beschikken over de gezondh
- Page 49 and 50: Microreactortechnologie; de chemisc
- Page 51 and 52: matografie, maar is zeer succesvol
- Page 53 and 54: Figuur 5 De economische haalbaarhei
- Page 55 and 56: Natuurkundige voordrachten I Nieuwe
- Page 57: qubit can now be described as follo
- Page 61: Natuurkundige voordrachten I Nieuwe
- Page 64 and 65: Natuurkundige voordrachten I Nieuwe
- Page 66 and 67: Natuurkundige voordrachten I Nieuwe
- Page 68 and 69: Natuurkundige voordrachten I Nieuwe
- Page 70 and 71: Natuurkundige voordrachten I Nieuwe
- Page 72 and 73: Natuurkundige voordrachten I Nieuwe
- Page 74 and 75: Natuurkundige voordrachten I Nieuwe
- Page 76 and 77: Natuurkundige voordrachten I Nieuwe
- Page 78 and 79: Natuurkundige voordrachten I Nieuwe
- Page 80 and 81: Natuurkundige voordrachten I Nieuwe
- Page 82 and 83: Natuurkundige voordrachten I Nieuwe
- Page 84 and 85: Natuurkundige voordrachten I Nieuwe
- Page 86 and 87: Natuurkundige voordrachten I Nieuwe
- Page 88 and 89: Natuurkundige voordrachten I Nieuwe
- Page 90 and 91: Natuurkundige voordrachten I Nieuwe
- Page 92 and 93: Natuurkundige voordrachten I Nieuwe
- Page 94 and 95: Natuurkundige voordrachten I Nieuwe
- Page 96 and 97: Natuurkundige voordrachten I Nieuwe
- Page 98 and 99: Natuurkundige voordrachten I Nieuwe
- Page 100 and 101: Natuurkundige voordrachten I Nieuwe
- Page 103 and 104: LOFAR: op zoek naar de snelste deel
- Page 105 and 106: Figuur 4 Artist impression van het
- Page 107: ichting van inval te bepalen. Naarm
Natuurkundige <strong>voor</strong>drachten I Nieuwe reeks 89<br />
Quantum Information<br />
58<br />
Figure 3<br />
The CHSH <strong>no</strong>nlocal game.<br />
probability greater than ¾ (and they obviously can<br />
win it with probability equal to ¾). Hence, one can<br />
safely conclude that Alice and Bob win the CHSH<br />
game with probability at most ¾. Or <strong>no</strong>t?!<br />
As a matter of fact, Alice and Bob can do better.<br />
The ΄flaw΄ in the above reasoning is that it implicitly<br />
assumes classical physics. By the laws of quantum<br />
mechanics, Alice and Bob can do the following.<br />
Before the game starts, when Alice and Bob<br />
can still communicate and agree on a strategy,<br />
they prepare an EPR pair (|0>⊗|0>+|1>⊗|1>)/√2, and<br />
Alice keeps the first qubit of the pair and Bob keeps<br />
the second. Then, when Alice gets her question x,<br />
she measures her qubit in the computational basis<br />
if x=0 and she measures it in the Hadamard basis<br />
if x=1, and the bit she observes as measurement<br />
outcome is her answer a. Bob measures his qubit<br />
in basis {|є0>=cos(π/8)|0>+sin(π/8)|1, |є1>=-sin (π/8)|0><br />
+cos (π/8)|1>} if y=0 and he measures it in basis<br />
{|δ0>=cos (π/8)|0>-sin(π/8)|1>, |δ1>= sin(π/8)|0> + cos(π/8<br />
)|1> }if y=1, and the bit he observes as measurement<br />
outcome is his answer b. Doing the maths shows<br />
that with this strategy: a⊕b=x^y with probability<br />
cos2 (π/8)≈0.85.<br />
Other examples of <strong>no</strong>nlocal games are even<br />
such that by pre-sharing a suitable quantum state,<br />
Alice and Bob’s winning probability goes up to 1.<br />
Understanding how large the gap can be between<br />
the classical and the quantum winning probability is<br />
an active research area. The framework of <strong>no</strong>nlocal