CS Jul-Aug 2023
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
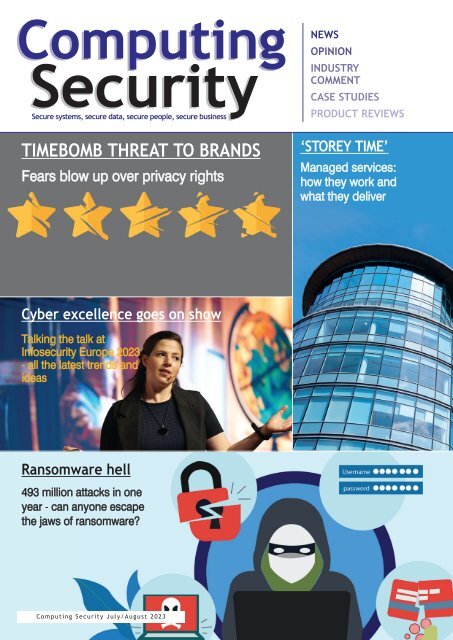
Computing<br />
Security<br />
Secure systems, secure data, secure people, secure business<br />
TIMEBOMB THREAT TO BRANDS<br />
Fears blow up over privacy rights<br />
NEWS<br />
OPINION<br />
INDUSTRY<br />
COMMENT<br />
CASE STUDIES<br />
PRODUCT REVIEWS<br />
‘STOREY TIME’<br />
Managed services:<br />
how they work and<br />
what they deliver<br />
Cyber excellence goes on show<br />
Talking the talk at<br />
Infosecurity Europe <strong>2023</strong><br />
- all the latest trends and<br />
ideas<br />
Ransomware hell<br />
493 million attacks in one<br />
year - can anyone escape<br />
the jaws of ransomware?<br />
Computing Security <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong>
comment<br />
UPSKILLING DRIVE LURES THOUSANDS<br />
According to the UK government, more than 3,600 people are looking to embark<br />
on a new career in cyber this year through applications to its 'Upskill in Cyber'<br />
programme. Aimed at people from a non-cyber background and delivered in<br />
partnership with the SANS Institute, the scheme is the latest in a series of ambitious<br />
programmes delivered through the government's £2.6 billion National Cyber Strategy.<br />
Michael Smith, CTO at Vercara (former security advisor for 2014 World Cup) welcomes<br />
the announcement: "Cyber skills are in huge demand across the economy. New industry<br />
and government-led initiatives such as this one can attract more people to the cybersecurity<br />
field, but a long-term solution to the skills gap requires a more holistic<br />
approach, led by cybersecurity leaders, that prioritises developing talent from within"<br />
It's more than a recruitment plan, he points out: it's a practical long-term cybersecurity<br />
strategy. "This is necessary, because, when we hire staff in this industry, we expect them<br />
to have such a wide range of skills that no one person will have the exact combination<br />
that is in the job description. When we do find somebody with all of those skills, they<br />
are usually outside of commuting distance and they're incredibly expensive."<br />
Smith believes this longer-term approach to nurturing talent from within can make<br />
knowledge-sharing and upskilling an integral part of a company's culture, delivering<br />
significant long-term skills benefits for new and existing practitioners within an<br />
organisation, as well as addressing the UK's wider talent gap. "After all, it will be<br />
a collective effort; every organisation has a part to play."<br />
Brian Wall<br />
Editor<br />
Computing Security<br />
brian.wall@btc.co.uk<br />
EDITOR: Brian Wall<br />
(brian.wall@btc.co.uk)<br />
LAYOUT/DESIGN: Ian Collis<br />
(ian.collis@btc.co.uk)<br />
SALES:<br />
Edward O’Connor<br />
(edward.oconnor@btc.co.uk)<br />
+ 44 (0)1689 616 000<br />
Daniella St Mart<br />
(daniella.stmart@btc.co.uk)<br />
+ 44 (0)1689 616 000<br />
Stuart Leigh<br />
(stuart.leigh@btc.co.uk)<br />
+ 44 (0)1689 616 000<br />
PUBLISHER: John Jageurs<br />
(john.jageurs@btc.co.uk)<br />
Published by Barrow & Thompkins<br />
Connexions Ltd (BTC)<br />
35 Station Square,<br />
Petts Wood, Kent, BR5 1LZ<br />
Tel: +44 (0)1689 616 000<br />
Fax: +44 (0)1689 82 66 22<br />
SUBSCRIPTIONS:<br />
UK: £35/year, £60/two years,<br />
£80/three years;<br />
Europe: £48/year, £85/two years,<br />
£127/three years<br />
R.O.W:£62/year, £115/two years,<br />
£168/three years<br />
Single copies can be bought for<br />
£8.50 (includes postage & packaging).<br />
Published 6 times a year.<br />
© <strong>2023</strong> Barrow & Thompkins<br />
Connexions Ltd. All rights reserved.<br />
No part of the magazine may be<br />
reproduced without prior consent,<br />
in writing, from the publisher.<br />
www.computingsecurity.co.uk <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> computing security<br />
@<strong>CS</strong>MagAndAwards<br />
3
Secure systems, secure data, secure people, secure business<br />
Computing Security <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong><br />
inside this issue<br />
CONTENTS<br />
Computing<br />
Security<br />
TIMEBOMB THREAT TO BRANDS<br />
Fears blow up over privacy rights<br />
Cyber excellence goes on show<br />
NEWS<br />
OPINION<br />
INDUSTRY<br />
COMMENT<br />
CASE STUDIES<br />
PRODUCT REVIEWS<br />
‘STOREY TIME’<br />
Managed services:<br />
how they work and<br />
what they deliver<br />
Talking the talk at<br />
Infosecurity Europe <strong>2023</strong><br />
- all the latest trends and<br />
ideas<br />
Ransomware hell<br />
COMMENT 3<br />
Upskilling drive lures thousands<br />
493 million attacks in one<br />
year - can anyone escape<br />
the jaws of ransomware?<br />
NEWS 6<br />
Backup Bible's sustainable strategies<br />
IBM expands QRadar brand<br />
Data protection update response<br />
Stepping up cyber resilience<br />
ARTICLES<br />
‘PAM BEFORE IAM’? 8<br />
PAM and IAM are both crucial areas of<br />
protection - though PAM should always<br />
come first, says one advocate<br />
CELEBRATION OF EXCELLENCE 14<br />
Infosecurity Europe <strong>2023</strong> enabled industry<br />
leaders, professionals and aspiring cybersecurity<br />
enthusiasts to come together<br />
under one roof to exchange knowledge<br />
and explore solutions designed to combat<br />
the vast array of ever-evolving threats<br />
RUSSIA'S CYBER RAMPAGE 10<br />
Businesses warned to brace for impact<br />
from barrage of attacks<br />
BELATED HAPPY BIRTHDAY, GDPR! 24<br />
WHY BEING AGILE MATTERS 11<br />
How do you measure the success of<br />
Steve Usher, Brookcourt Solutions, offers<br />
something as complex and far-reaching as<br />
his insights on staying ahead of the game<br />
the General Data Protection Regulation?<br />
when it comes to ransomware<br />
Brought into existence some five years ago to<br />
replace the 1995 Data Protection Directive<br />
TIMEBOMB TARGETING BRANDS 12<br />
used across various European countries, it<br />
Many companies are said to be ‘breaching<br />
has its supporters and detractors<br />
consumers online privacy rights’<br />
FORCES TO BE RECKONED WITH 16<br />
MDR, EDR and NDR - what exactly is the<br />
power behind these acronyms?<br />
AI - APPROPRIATE INTERRUPTION? 28<br />
BURNOUT! 18<br />
Should AI be stopped in its tracks, as many<br />
Stress and breakdown are ‘reaching<br />
influential observers are demanding, on<br />
epidemic levels amongst cyber security<br />
the grounds that it could run out of<br />
professionals’, it is stated<br />
control - or is that simply a knee-jerk<br />
reaction to a technology that will change<br />
IAM AIMS HIGH 20<br />
our lives for ever, to the benefit of all<br />
National roadmap for identity and access<br />
management - IAM - singles out key goals<br />
MAKING OF A MANAGED SERVICE 22<br />
Mike Richmond, Brookcourt Solutions,<br />
RANSOMWARE RAMPAGE 32<br />
discusses how managed services work<br />
Ransomware attacks are continuing their<br />
and bring benefits to a business<br />
rampage. In May <strong>2023</strong> alone, two cities,<br />
SECURITY BY DESIGN 31<br />
many healthcare organisations, an airline,<br />
Cybersecurity measures being imposed in<br />
educational institutions and tech giants<br />
the US will hit software companies hard.<br />
were all victims, according to the Cyber<br />
What might this mean for the UK?<br />
Management Alliance. "Almost nobody<br />
seems to have been spared," it warns<br />
computing security <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk<br />
4
Your Sensitive Data is stored in<br />
all areas of your digital estate.<br />
Find out how easy it could be<br />
to manage everything under<br />
the surface<br />
Less Time. Less Resources. Less Costs.<br />
www.geolang.com
news<br />
Gary Barlet, Illumio.<br />
IBM EXPANDS QRADAR BRAND<br />
IBM has unveiled its new security suite<br />
IBM cyber range.<br />
designed to unify and accelerate the<br />
security analyst experience across the<br />
full incident lifecycle. The IBM Security<br />
QRadar Suite is said to represent a major<br />
evolution and expansion of the QRadar<br />
brand, spanning all core threat detection,<br />
investigation and response technologies,<br />
with significant investment in innovations<br />
across the portfolio.<br />
Delivered as a service, the IBM Security<br />
QRadar Suite is built on an open foundation and designed specifically for the demands of<br />
hybrid cloud. "It features a single, modernised user interface across all products," says the<br />
company, "embedded with advanced AI and automation designed to empower analysts to<br />
work with greater speed, efficiency and precision across their core toolsets".<br />
STEPPING UP CYBER RESILIENCE<br />
News of the US launching its<br />
National Cybersecurity Strategy<br />
Implementation Plan (N<strong>CS</strong>IP) has<br />
prompted the following comment from<br />
Gary Barlet, federal CTO at Illumio.<br />
"The [plan] gives much-needed<br />
guidance for agencies on improving<br />
cyber resilience. It assigns timebound<br />
goals and initiatives to each agency -<br />
giving them direction on how to reach<br />
the strategy's clear objectives.<br />
"These goals and initiatives also display<br />
a sense of urgency, which is important,<br />
as the pace of technology makes it<br />
impossible to imagine the impact it<br />
will have on security in three, five or<br />
ten years.<br />
It focuses on building cyber resilience<br />
now as well as down the road, he adds.<br />
"The plan reflects the urgency of today's<br />
cyber threats, and also demonstrates<br />
an understanding of the resource and<br />
fiscal challenges agencies face in overcoming<br />
these dangers."<br />
MIXED RECEPTION FOR DATA PROTECTION UPDATE<br />
The UK government's claim that its new GDPR<br />
legislation will deliver savings of up to £4.7bn over<br />
the coming decade - while bolstering data protection<br />
and privacy - has drawn this response from Edward<br />
Machin, a senior lawyer in Ropes & Gray's data, privacy<br />
& cybersecurity practice.<br />
"The GDPR is far from perfect and the UK is bucking<br />
the global trend of heavily regulating personal data,<br />
but I think that some of its proposals - those around<br />
scientific research, in particular - will in time come to<br />
be seen as an improvement on the status quo."<br />
Meanwhile, a New Economics Foundation report<br />
estimates that compliance costs alone could reach<br />
£1.6 billion for British businesses.<br />
BACKUP BIBLE'S SUSTAINABLE STRATEGIES<br />
Hornetsecurity has launched its new Backup Bible -<br />
a guide to support businesses through all stages<br />
of preparing for, responding to and recovering<br />
from a substantial data loss event. The Backup Bible<br />
features 150-plus pages of actionable content,<br />
divided into four core parts, including customisable<br />
templates enabling business owners to create their<br />
own personalised backup strategy.<br />
Hornetsecurity CEO Daniel Hofmann believes that<br />
the online content enables businesses "to create<br />
sustainable backup strategies to ensure they are<br />
prepared in the event of a data breach".<br />
Edward Machin, Ropes &<br />
Gray.<br />
Daniel Hofmann,<br />
Hornetsecurity.<br />
6<br />
computing security <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
technology focus<br />
'PAM BEFORE IAM'?<br />
PAM AND IAM ARE BOTH CRUCIAL AREAS OF PROTECTION - THOUGH PAM<br />
SHOULD LEAD THE WAY, ARGUES ONE ADVOCATE OF THE TECHNOLOGIES<br />
Graham Hawkey, Osirium.<br />
Identity and Access Management is a<br />
critical consideration in cybersecurity,<br />
says the National Institute of Standards<br />
and Technology, which is working on an<br />
IAM roadmap (see pages 20-21) - that is<br />
welcomed by Graham Hawkey, PAM<br />
specialist, Osirium.<br />
"NIST says the purpose is to present 'a set<br />
of strategic objectives, priorities, and<br />
initiatives' and it's clear that this is a project<br />
looking at the long-term strategy and<br />
requirements," he says. "With that in mind,<br />
it is important that this roadmap should<br />
also seriously consider and factor in the role<br />
of Privileged Access Management (PAM)<br />
and the way it couples with and complements<br />
IAM, combining to create a powerful,<br />
complete solution for a modern IT<br />
environment. NIST says IAM is a 'key<br />
component to creating trusted, modern<br />
digital services' and 'a fundamental and<br />
critical cybersecurity capability'. Some<br />
would view IAM as being so critical that<br />
it is the central view of truth, delivering a<br />
'single pane of glass' to control everything<br />
they can do within an organisation by<br />
knowing everything about a person's<br />
identity. Somewhat akin to George Orwell's<br />
dystopian view of the future."<br />
But this is an illusion, he adds, and breaks<br />
down when it is realised you need to take<br />
into account what a privilege (or attribute<br />
that maps to a privilege) means. "Because<br />
these privileges are so contextual, the<br />
further you are from a device, the further<br />
you are from the truth of privilege-based<br />
risk," states Hawkey. "So, although IAM is<br />
one piece of the puzzle in building robust<br />
cyber resilience, it leaves a hole in the<br />
bigger picture, with a crucial component<br />
missing. What it boils down to is that IAM<br />
is essentially about proving who you are,<br />
but it doesn't provide any help in controlling<br />
what users can do once they've<br />
retrieved credentials and logged in. You<br />
also need to be able to control what you<br />
can do and how you do it. IAM tools authenticate<br />
the person, then PAM manages the<br />
system access for that user. It's a powerful<br />
combination."<br />
Furthermore, he states, IAM and PAM<br />
users enter applications through different<br />
interfaces. "Whilst the audience of IAM<br />
enter through the 'shop door', PAM users<br />
are 'back office' based. Consequently, there<br />
is a difference in attack surface. While both<br />
areas of protection are crucial, it's not a<br />
chicken-and-egg situation. AM should<br />
always come first. This is because PAM<br />
delivers a connection between privileged<br />
users and the role-based accounts that they<br />
need. These accounts exist on the raw<br />
systems before deployment and continue<br />
throughout the lifetime of system, device or<br />
application. In fact, they are so important<br />
that they are the very accounts that are<br />
needed to set up a connection to an IAM<br />
system in the first place. In summary, it's<br />
'PAM' before 'IAM', to protect the 'I' in IAM."<br />
08<br />
computing security <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
DON’T<br />
SaaSSS<br />
GET YOUR<br />
KICKED! !<br />
TAKE CONTROL NOW AND<br />
PROTECT YOUR SaaS DATA<br />
Global SaaS vendors like Microsoft, Google and Salesforce<br />
don’t assume any responsibility for your data hosted<br />
in their applications. So, it’s up to you to take control<br />
and fully protect your SaaS data from cyber threats or<br />
accidental loss. Arcserve SaaS Backup offers complete<br />
protection for your SaaS data, eliminating business<br />
interruptions due to unrecoverable data loss.<br />
Arcserve SaaS Backup<br />
Complete protection for all your SaaS data.<br />
arcserve.com<br />
The unified data resilience platform
cyber attacks<br />
RUSSIA'S CYBER RAMPAGE<br />
BUSINESSES WARNED TO BRACE FOR IMPACT FROM BARRAGE OF ATTACKS<br />
Raghu Nandakumara, Illumio.<br />
Gavin Millard, Tenable Network Security.<br />
UK infrastructure faces destruction<br />
from Russian-backed cyber groups,<br />
says UK minister Oliver Dowden -<br />
a warning that further indicates the battle<br />
of wills and ideologies between the Kremlin<br />
and Western capitals following Russia's<br />
invasion of Ukraine.<br />
Dowden said these politically motivated<br />
groups were now rearing their heads on UK<br />
shores and pleaded with businesses to brace<br />
for their cyber impact. He outlined recent<br />
attempts from 'Wagner-like cyber groups' to<br />
damage UK critical national infrastructure.<br />
These adversaries are ideologically, rather<br />
than financially, motivated, he added,<br />
making them less likely to show the same<br />
level of restraint as national actors,<br />
sharpening concerns around these threats.<br />
In response, UK Government has made<br />
a series of announcements aimed at further<br />
strengthening UK resilience. These include:<br />
The National Cyber Security Centre (N<strong>CS</strong>C)<br />
issuing an official threat notice to<br />
operators to help protect the country<br />
Government to set "specific and ambitious<br />
cyber resilience targets" for all critical<br />
national infrastructure sectors to meet<br />
by 2025<br />
Government exploring how to bring all<br />
private sector businesses working in<br />
critical national infrastructure within the<br />
scope of cyber resilience regulations<br />
Enhanced cyber security measures to<br />
protect the UK Government's critical IT<br />
systems, known as GovAssure.<br />
Gavin Millard, deputy chief technology,<br />
Tenable Network Security, points to how<br />
threats from state-based actors against<br />
critical infrastructure are nothing new and<br />
indeed a constant issue. "With an aging<br />
infrastructure and a vast attack surface<br />
vulnerable to known flaws, it's important to<br />
know the weaknesses threat actors target<br />
and mitigate in a timely manner, as a<br />
successful cyber-attack against critical assets<br />
could have wide-ranging impacts to the<br />
population and economy," he states.<br />
"Attacks, such as those seen against JBS<br />
foods and the Colonial Pipeline, leveraged<br />
flaws such as Remote Desktop Protocol<br />
(RDP) and exposed Virtual Private Networks<br />
(VPNs) to gain initial access. Once a foothold<br />
had been found, gaining privileges and<br />
distributing malicious code was concerningly<br />
easy. To prevent such actions from occurring,<br />
it's critically important that organisations take<br />
a pre-emptive approach to identifying and<br />
addressing these exposures before they are<br />
leveraged."<br />
In response to the comments made by<br />
Dowden, Raghu Nandakumara, senior<br />
director and head of industry solutions at<br />
Illumio, had this to say: ""The introduction<br />
of new targets is a positive move and will<br />
provide a uniform baseline for cyber<br />
resilience across all sectors. However, the<br />
2025 timeline is aggressive and signifies<br />
the severity of the threat. It also raises the<br />
question as to what these targets will be<br />
and how achievable they will be in that<br />
timeframe.<br />
"As a nation, we have to shift the focus<br />
from simply preventing attacks to surviving<br />
them and that requires an 'assume breach<br />
mentality', along with the adoption of riskbased<br />
security models like Zero Trust. The<br />
UK government is leading the way in CNI.<br />
However, I anticipate that cyber resilience will<br />
become an industry-recognised metric for all<br />
companies to achieve and measure against."<br />
10<br />
computing security <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
ansomware<br />
WHY BEING AGILE MATTERS WHEN<br />
IT COMES TO A RANSOMWARE ATTACK<br />
STEVE USHER, SECURITY SERVICES MANAGER, BROOKCOURT SOLUTIONS, OFFERS HIS EXPERT INSIGHTS<br />
Over the course of the last few years,<br />
we have witnessed too many highprofile<br />
companies being featured<br />
in the media who have fallen victim to<br />
ransomware demands. In that moment,<br />
as a business leader, what are your first<br />
thoughts? Imagine for that moment what it<br />
might be like if your organisation was hit by<br />
an attack - would you be ready?<br />
Ransomware attacks are one of the most<br />
significant and rapidly evolving threats in<br />
the cybersecurity landscape. The damage a<br />
ransomware attack can cause to a business<br />
doesn't bear thinking about. The financial<br />
loss, data loss and operational disruption<br />
will all take a toll on the overall reputation<br />
of an organisation.<br />
For senior management, understanding<br />
how and why ransomware attacks happen<br />
is incredibly complex, especially without<br />
knowledge of vulnerabilities, code or a clear<br />
view of the methods, motivations and<br />
current activities of cybercriminals.<br />
In a recent example, a senior security<br />
analyst joined top executives from a Fortune<br />
500 company. He joined the meeting cold,<br />
not knowing what to expect, and was able<br />
to eloquently conduct a live review of threat<br />
intelligence, using the latest technology.<br />
The client struggled to comprehend the<br />
level of detail and how exposed the<br />
business actually was, leading to a greater<br />
understanding and hence the security<br />
posture was elevated.<br />
The threat of ransomware is constantly<br />
evolving and we need to always remain<br />
'threat aware'. It's a game of cat and mouse<br />
where we may often only learn from being<br />
exposed. However, our true strength comes<br />
from how we recover with agility. We need<br />
to educate business leaders to understand<br />
the threat will always be there. There is no<br />
escape; regularly reviewing your security<br />
posture and investing in your cyber security<br />
is paramount to protect your business,<br />
stakeholders and your data.<br />
Here's the five-point plan for better<br />
resilience:<br />
1. Rapid Response: Time is of the essence<br />
in mitigating the impact of a ransomware<br />
attack - helping businesses understand the<br />
key next steps to identify and contain the<br />
attack, minimise its spread and prevent<br />
further damage. Delayed response can lead<br />
to increased data loss, extended downtime<br />
and higher financial costs for the affected<br />
organisation<br />
2. Adaptive Solutions: Ransomware attacks<br />
constantly evolve, with new variants and<br />
techniques emerging regularly. Being ready<br />
to adapt tools, techniques and approaches<br />
to counter an evolving threat is paramount,<br />
having access to the latest threat intelligence,<br />
developing new detection and<br />
prevention mechanisms to help business<br />
with effective solutions to combat the<br />
specific ransomware strain they are facing<br />
3. Collaboration and Information Sharing:<br />
Through active collaboration and information<br />
sharing with relevant stakeholders,<br />
including customers, industry peers,<br />
law enforcement agencies, we can<br />
foster a collaborative environment,<br />
pool resources, share insights and<br />
collectively respond to ransomware attacks<br />
more effectively<br />
4. Incident Management and Recovery:<br />
Helping business to adopt a well-defined<br />
incident management process in place to<br />
handle ransomware attacks. This includes<br />
coordinating with customers, providing<br />
guidance on containment, facilitating<br />
communication and helping organisations<br />
return to normal operations as quickly<br />
as possible, as well as ensuring regular<br />
backups, including tests are put in place<br />
as part of on-going process<br />
5. Continuous Improvement: By analysing<br />
attack patterns, post-incident reviews and<br />
lessons learned from every ransomware<br />
incident, we can refine better solutions<br />
for businesses to update their procedures<br />
and enhance their overall cyber resilience<br />
against future attacks.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> computing security<br />
11
privacy crisis<br />
REPUTATION TIMEBOMB 'WAITING TO BLOW UP MANY BRANDS'<br />
PRIVACY LAW FIRM SCHILLINGS REVEALS THAT MANY COMPANIES ARE<br />
INADVERTENTLY BREACHING CONSUMERS’ ONLINE PRIVACY RIGHTS<br />
Measures taken by companies to<br />
protect consumers data are<br />
"not working" and are exposing<br />
brands to massive reputational risk,<br />
according to research commissioned by<br />
privacy law firm Schillings.<br />
The study found that company data<br />
practices, often owned by marketing and<br />
IT teams, are falling short of legal<br />
requirements - and in some cases are<br />
harming customers by contributing to<br />
incorrect online profiles.<br />
The report, commissioned by Schillings<br />
and conducted by cross-party technology<br />
think tank Demos, tracked volunteers as<br />
they attempted to reclaim and delete the<br />
personal data companies held about<br />
them. In doing so, researchers uncovered<br />
widespread 'data ethics' challenges at<br />
large numbers of companies.<br />
The study found that:<br />
Up to 65% of companies did not<br />
respond to data requests, despite this<br />
being a legal requirement under GDPR<br />
Processes to help consumers take<br />
control of their data - eg, cookie<br />
banners - "actively seek to dissuade"<br />
people from restricting permissions<br />
<br />
<br />
<br />
'Accepting All' cookies on websites<br />
often includes consent for data to be<br />
sold to data brokers - with brands<br />
unable to control how this data is<br />
then used and exposing them to<br />
supply chain risks<br />
Volunteers were "stunned" and<br />
"scared" by how widely their data was<br />
spread and sold by companies - with<br />
one volunteer discovering 2,242<br />
companies were using their 'off-<br />
Facebook' interactions to target them<br />
with advertising<br />
Controlling your data footprint online<br />
is virtually impossible and the idea<br />
that individuals can is "a big lie".<br />
Volunteers found inaccuracies in the<br />
data profiles created about them online -<br />
which can cause real-world problems,<br />
such as applying for credit.<br />
Allan Dunlavy, partner at Schillings, says<br />
the study findings show a crisis waiting<br />
to happen. "Our study shows that we're<br />
in the middle of the largest privacy crisis<br />
in history and there is a reputation<br />
timebomb waiting to blow up many<br />
brands. Brands that are intentionally or<br />
inadvertently misusing our data could<br />
suffer a serious impact to their<br />
reputations, customer base and revenue.<br />
We are in a situation where many<br />
companies are holding consumer data,<br />
not giving people their legal right to<br />
access it, and then selling it on into a<br />
system they have no control over. The<br />
burden is currently on the consumer,<br />
rather than the business, to change this,<br />
but we see the tide turning against<br />
companies that are not helping<br />
consumers."<br />
STUDY AND RESULTS<br />
To create the report, Demos, with<br />
support from consumer rights company<br />
Rightly, worked with volunteers to<br />
discover how far information about them<br />
had travelled online - and how it had<br />
morphed along the way.<br />
Volunteers were helped to exercise their<br />
Right of Access (the right under GDPR to<br />
ask companies if they are using your<br />
personal information and for copies of<br />
what they hold) and The Right To Erasure<br />
(the right to ask for that data to be<br />
deleted - also known as the right to be<br />
forgotten).<br />
Overall, the research found a deeply<br />
frustrating and confusing process, and<br />
12<br />
computing security <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
privacy crisis<br />
an inconsistent picture across data<br />
requests to companies. Responses varied<br />
dramatically: of all the access requests<br />
put out, rates ranged from 65% of<br />
companies not responding to one<br />
volunteer to just 10% not responding to<br />
another. Under GDPR laws, companies<br />
are required to respond to consumer<br />
requests - but many did not or made the<br />
process difficult and time-consuming.<br />
The study also found that processes put<br />
in place to help consumers have more<br />
control over their information online in<br />
fact made them more likely to give it<br />
away. The biggest gateway to personal<br />
data for most users is the GDPRcompliant<br />
'cookie banners' - but Demos<br />
concluded the banner's design often<br />
actively sought to dissuade users from<br />
changing data permissions "through<br />
nudges to incentivise you to agree to the<br />
most permissive settings".<br />
The study also found "accepting all"<br />
on cookie banners frequently gave<br />
companies permission to sell consumer<br />
data onto data brokers - creating a black<br />
hole in their ability to protect customer<br />
data. "One of the biggest problems right<br />
now is companies gathering enormous<br />
amounts of data on people, selling it<br />
off to data brokers and even they don't<br />
know where it ends up," commented one<br />
volunteer.<br />
DOUBTS RAISED<br />
This made them question whether they<br />
wished to continue buying from that<br />
company, explaining: "It's not necessarily<br />
that I don't trust them as a brand not to<br />
misuse my data - it's the fact that I don't<br />
know who they're selling it to and who<br />
that broker is selling it on to".<br />
Study volunteers were also surprised by<br />
the inaccuracy of profile information<br />
companies had compiled about them,<br />
based on their online activity. This<br />
'propensity data' is intended to help<br />
advertisers target users who are most<br />
likely to be interested in their products.<br />
However, this data is also used to make<br />
decisions which have far-reaching<br />
ramifications in the real world, such<br />
as whether an individual would qualify<br />
for a mortgage or credit card.<br />
The study states: "We found a chaotic<br />
system that profits from our data, while<br />
doing little to empower users to exert<br />
their rights: data is collected and inferred<br />
about us, and used to make decisions in<br />
the dark about what sort of person we<br />
are, what sort of products and services<br />
we should be offered - from health<br />
insurance to mortgages."<br />
PANDEMIC HANGOVER<br />
Allan Dunlavy goes on to explain that<br />
much of the issue was born out of<br />
the Covid 19 pandemic: "For many<br />
companies, the rush to move to<br />
an online business model during the<br />
pandemic resulted in shortcuts being<br />
taken. We are seeing a lot of data privacy<br />
codes of practice overlooked, despite<br />
the best of intentions - with many<br />
companies often unknowingly<br />
contravening data legislation through<br />
poorly set up processes. But with privacy<br />
becoming a key focus for consumers,<br />
companies need to take these issues<br />
more seriously.<br />
"It's time every company took a long,<br />
hard look at how confident they are of<br />
their data ethics. This is a strategic<br />
reputational problem that<br />
needs addressing in the<br />
boardroom - not in<br />
isolation by a<br />
marketing or IT<br />
team."<br />
Law firm<br />
Schillings<br />
commissioned<br />
the study as part of its 'Accept All:<br />
Unacceptable?' campaign, highlighting<br />
and addressing the urgent need for<br />
society to do more to protect personal<br />
privacy online. Volunteers from the<br />
study can been seen in the documentary,<br />
'Accept All: Unacceptable?', which was<br />
also commissioned by Schillings, now<br />
available to view on YouTube here. The<br />
film sets out to answer the question :<br />
"Why should we care about online<br />
privacy?"<br />
Allan Dunlavy, Schillings: we're in the<br />
middle of the largest privacy crisis in<br />
history.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> computing security<br />
13
Infosecurity Europe<br />
Infosecurity Europe <strong>2023</strong> proved a fertile environment for exploring<br />
innovative solutions to combat ever-evolving threats.<br />
Visitors to the exhibition were able to equip themselves with<br />
the knowledge and tools to help make them more cyber secure.<br />
CELEBRATION OF CYBERSECURITY EXCELLENCE<br />
INFOSECURITY EUROPE <strong>2023</strong> ONCE<br />
AGAIN SHOWCASED THE LATEST<br />
TRENDS AND IDEAS THAT ARE<br />
SHAPING THE WORLD OF<br />
INFORMATION SECURITY<br />
Infosecurity Europe <strong>2023</strong>, as ever, proved<br />
to be a captivating, visitor-packed event<br />
that brought together professionals<br />
from right across the cybersecurity<br />
industry. With a range of distinguished<br />
speakers, enlightening panel discussions<br />
and groundbreaking innovations, the<br />
conference showcased the latest trends<br />
and ideas that are shaping the world of<br />
information security.<br />
Kicking off the conference, legendary<br />
Olympic gold medallist sprinter Michael<br />
Johnson delivered a keynote that drew out<br />
a number of parallels between his athletic<br />
journey and the challenges that are now<br />
faced every day in the cybersecurity<br />
domain. Johnson's insights emphasised the<br />
importance of perseverance and teamwork<br />
in overcoming obstacles, a valuable lesson<br />
for all professionals in the field.<br />
Matthew Syed, the journalist, author,<br />
broadcaster and former international table<br />
tennis player, focused his discussion on the<br />
significance of embracing the concept of<br />
'black box thinking', and the connection<br />
between mindset and high performance.<br />
He stressed the need for a growth mindset<br />
and encouraged attendees to innovate to<br />
tackle challenges posed by cyber security<br />
to stop attackers in their tracks.<br />
Cybersecurity analyst Keren Elazari<br />
delivered a keynote on the transformative<br />
power of ethical hacking, emphasising the<br />
importance of ethical hackers in identifying<br />
vulnerabilities, enhancing system security<br />
and driving positive change. Her talk shed<br />
light on the vital role that ethical hackers<br />
play in safeguarding our digital infrastructure<br />
and encouraging collaboration<br />
between security professionals.<br />
14<br />
computing security <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
Infosecurity Europe<br />
Matthew Syed's discussion focused on the<br />
significance of embracing the concept of<br />
'black box thinking'.<br />
Cybersecurity analyst Keren Elazari addressed<br />
the transformative power of ethical hacking.<br />
One of the most anticipated events at<br />
Infosecurity Europe <strong>2023</strong> was the Women<br />
in Cybersecurity session, featuring Danni<br />
Brooke. A prominent figure in the industry,<br />
Brooke shared her experiences and highlighted<br />
the need for diversity and inclusion in<br />
cybersecurity.<br />
Her thought-provoking presentation<br />
encouraged women to pursue careers in<br />
the field and showcased the success stories<br />
of female leaders who have already made<br />
a significant impact.<br />
Infosecurity Europe <strong>2023</strong> was very much<br />
about celebrating innovation, with the<br />
announcement of the DSIT (Department of<br />
Science, Innovation and Technology) award.<br />
This year's winner, ANGOKA, was said to have<br />
demonstrated groundbreaking advancements<br />
in for smart cities and smart mobility,<br />
heightening the cybersecurity and safety of<br />
connected devices. ANGOKA's achievement<br />
highlighted the immense potential that exists<br />
for innovative solutions to combat evolving<br />
cyber threats.<br />
Becky Pinkard was inducted into the Hall<br />
of Fame - recognised for her significant<br />
contributions to the field. She commented<br />
on the industry to say, "what I realised is that<br />
security gave me a home." She encouraged<br />
the audience to be open and inclusive in<br />
business and "remember who they are at<br />
home is who they are as a person. That is<br />
who they bring to work and that is why they<br />
are successful". This could be a means to<br />
addressing the cybersecurity talent gap and<br />
the need for more female talent, too.<br />
Overall, Infosecurity Europe <strong>2023</strong> delivered<br />
a valuable platform for industry leaders,<br />
professionals and cybersecurity enthusiasts to<br />
exchange knowledge and explore innovative<br />
solutions to combat ever-evolving threats.<br />
Infosecurity Europe 2024 will take place<br />
from 4-6 June 2024 at the ExCel London.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> computing security<br />
15
MDR-EDR-NDR<br />
ENLISTING THE RIGHT FORCES TO BOLSTER SECURITY<br />
MDR, EDR AND NDR - WHAT<br />
EXACTLY IS THE POWER<br />
BEHIND THESE ACRONYMS?<br />
Mark Watkinson, Adarma: MDR<br />
providers deliver 24/7 threat monitoring,<br />
detection and response outcomes.<br />
MDR (Managed Detection and<br />
Response) and EDR (Endpoint<br />
Detection and Response) and NDR<br />
(Network Detection and Response) have<br />
become really hot topics as security tools. But<br />
what exactly do they do for an organisation?<br />
According to Mark Watkinson, head of<br />
market insights at Adarma, they enable the<br />
move from passive protection to "provide<br />
monitoring, recoding, analytics and detection<br />
capabilities and, most importantly, response<br />
actions to their specific area of coverage -<br />
ie, E = Endpoint, N = Network. These tools<br />
go deep in their coverage of specific areas<br />
and functionality".<br />
There is one major issue, though, he states.<br />
"They create mini 'analytic islands' focused on<br />
doing a particular job very well, but are blind<br />
to other areas of the infrastructure, thus<br />
unable to give coverage or context outside<br />
their specific area. This can create blind spots<br />
and can be difficult to co-ordinate and staff<br />
appropriately to achieve the full coverage<br />
across the various tooling required to cover<br />
your IT environment, from endpoint to<br />
network to cloud."<br />
These issues gave rise to XDR tooling, he<br />
adds. "Buyers can now broaden the scope of<br />
detection beyond the endpoint or network to<br />
cover identify, servers, cloud workloads and<br />
much more. Every vendor has their own<br />
idea of XDR, how it works and<br />
what's included in the X - after<br />
all, 'X' just means extended.<br />
This ambiguity has added<br />
to the confusion across<br />
the cyber security vendor<br />
landscape."<br />
As the security<br />
industry faces an<br />
ongoing talent crisis,<br />
teams often struggle<br />
to recruit and retain the people required<br />
to manage and optimise these tools. The<br />
solution is MDR, he argues. "MDR providers<br />
deliver 24/7 threat monitoring, detection and<br />
response outcomes for the threats the<br />
organisation faces and the coverage they<br />
require. They provide customers with the<br />
people [analysts, hunters, threat intel and<br />
responders], expertise, processes and turnkey<br />
technology stack associated with a Modern<br />
SOC function, in a remotely delivered, shared<br />
model that is easy-to-consume."<br />
Meanwhile, in a survey carried out for<br />
Gatewatcher by Vanson Bourne on APT threat<br />
detection, 25% of respondents said they were<br />
currently seeking to detect and discover APTs,<br />
but faced challenges identifying the method<br />
of entry. A further 21% faced challenges<br />
supporting the technology. When asked to<br />
detail the technology portfolio used against<br />
APTs, Endpoint Detection & Response (EDR)<br />
was the most present, cited by nearly twothirds<br />
(62%) of respondents.<br />
This was followed by firewalls (57%) and<br />
then a very close third and fourth between<br />
Security Information and Event Management<br />
(SIEM), and Network Detection and Response<br />
(NDR), with 56% and 55% respectively.<br />
Philippe Gillet, CTO of Gatewatcher, says<br />
the study shows that businesses are still<br />
relying heavily on endpoint protection,<br />
while recognising that it is visibility across<br />
the network that is now needed to address<br />
APTs. "As recent examples have shown,<br />
these advanced attacks exhibit patience<br />
and strategic thinking. As such, it is time<br />
to evolve and adapt our approach to the<br />
threat landscape and see APTs as the new<br />
normal in cybersecurity. This will mandate<br />
network technologies that offer high visibility<br />
of threats hidden in the network and represent<br />
an essential lever for strengthening the<br />
cybersecurity posture of businesses.''<br />
16<br />
computing security <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
Computing<br />
Security<br />
Secure systems, secure data, secure people, secure business<br />
Product Review Service<br />
VENDORS – HAS YOUR SOLUTION BEEN<br />
REVIEWED BY COMPUTING SECURITY YET?<br />
The Computing Security review service has been praised by vendors and<br />
readers alike. Each solution is tested by an independent expert whose findings<br />
are published in the magazine along with a photo or screenshot.<br />
Hardware, software and services can all be reviewed.<br />
Many vendors organise a review to coincide with a new launch. However,<br />
please don’t feel that the service is reserved exclusively for new solutions.<br />
A review can also be a good way of introducing an established solution to<br />
a new audience. Are the readers of Computing Security as familiar with<br />
your solution(s) as you would like them to be?<br />
Contact Edward O’Connor on 01689 616000 or email<br />
edward.oconnor@btc.co.uk to make it happen.
workplace welfare<br />
BURNOUT!<br />
STRESS AND BREAKDOWN ARE SAID TO BE REACHING EPIDEMIC LEVELS AMONGST CYBER SECURITY<br />
PROFESSIONALS. WITHOUT REMEDIAL ACTION, LONG-TERM CONSEQUENCES COULD BE CATASTROPHIC<br />
Burnout has burrowed its way deep into<br />
the cybersecurity industry, but little is<br />
being done to address the attrition it<br />
causes, it is claimed. According to analyst and<br />
research firm Gartner, it is largely overlooked<br />
across the industry. "Insider threat management<br />
is not a focus area for most organisations,<br />
unless they are highly regulated. The<br />
cybersecurity industry has taken limited action<br />
to reduce cybersecurity process friction and<br />
improve user experience." Gartner also states<br />
that poor strategic implementation of topics<br />
like Zero Trust stops organisations from<br />
developing a positive security culture.<br />
According to JJ Gericke, senior manager at<br />
ThreeTwoFour, while burnout is not unique to<br />
the cybersecurity industry, there are certain<br />
factors within cybersecurity that make burnout<br />
and high attrition more likely. "Cybersecurity<br />
professionals are constantly faced with new<br />
and sophisticated threats, which require<br />
continuous learning and skill development.<br />
While learning and development are part of<br />
any job, the scale and rate of emerging<br />
technologies and threats in cybersecurity<br />
create a lot of pressure to stay up to date."<br />
The cybersecurity skills gap and the difficulty<br />
organisations face in recruiting resources is<br />
also a contributing factor, he points out.<br />
"Cybersecurity teams are routinely understaffed<br />
and overburdened with heavy<br />
workloads in which individuals often fill<br />
multiple roles. Protecting an organisation<br />
is a 24/7 job, meaning the industry is<br />
characterised by long working hours, on-call<br />
responsibilities and an 'always-on' mentality.<br />
Cyber security staff responding to incidents<br />
operate in a high-pressure environment,<br />
with a significant risk of substantial losses for<br />
the business. These situations take their toll,<br />
because they often require working extremely<br />
long hours and over weekends, all while<br />
facing significant pressure from the business<br />
leaders to provide a resolution."<br />
There are various initiatives that organisations<br />
can undertake to help reduce burnout,<br />
Gericke says, including:<br />
Ensuring dedicated time off work<br />
for training and development<br />
Offering stress management initiatives<br />
such as mindfulness training and<br />
counselling services<br />
Establishing a long-term relationship<br />
with a trusted service provider that can<br />
provide expert assistance in situations<br />
where there is an increased requirement<br />
for resources, such as after an incident has<br />
taken place or during major transformation<br />
programmes<br />
Making certain that team roles are defined<br />
and there is a clear career path for<br />
progression<br />
Addressing organisational issues that adds<br />
stress, such as excessive bureaucracy and<br />
lack of clear communication<br />
Creating flexible work opportunities by<br />
offering people time off or increased pay<br />
for working on weekends when<br />
responding to incidents.<br />
"Industry wide, it is the responsibility of all<br />
organisations to help grow the talent pool of<br />
cybersecurity resources through internship<br />
programs, training initiatives and ensuring<br />
that people are fairly compensated for<br />
working in a high-stress environment."<br />
MENTAL HEALTH FEARS<br />
Without remedial action, says Jasmine Eskenzi,<br />
founder of The Zensory, it is highly likely that<br />
there will be a further decline in the mental<br />
well-being of cybersecurity professionals, to<br />
the extent where many will be forced to leave<br />
the industry, in order to prioritise their mental<br />
health. "Organisations will then be left to<br />
contend with the decline in staff retention<br />
rates, alongside the existing shortage of talent<br />
18<br />
computing security <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
workplace welfare<br />
within the cybersecurity industry, making them<br />
vulnerable to inevitable and potentially<br />
harmful cyberattacks."<br />
Unless organisations are willing to lead the<br />
change towards protecting the mental health<br />
and well-being of their staff, particularly their<br />
security teams, the issue at hand will continue<br />
to grow, she warns. "Evidently, there is a real<br />
need for organisational leaders to commit to<br />
making a difference which can be achieved<br />
by adopting a 'cyber mindful' mindset.<br />
"This could involve supplying cybersecurity<br />
professionals with a mindfulness toolkit that<br />
encourages them to feel empowered to<br />
prioritise themselves and their wellbeing at<br />
work. This could also include encouraging<br />
the practice of mindful exercises during the<br />
working day, such as enforcing breaks<br />
between meetings or tasks, to enable them<br />
to take time out to decompress their minds,<br />
which could also help to boost productivity."<br />
ALERT FATIGUE<br />
Meanwhile, recent research suggests that alert<br />
fatigue is a huge problem in security teams,<br />
with almost half (48%) of respondents<br />
claiming it impacts them, states Lisa Ventura,<br />
founder, Cyber Security Unity. "This typically<br />
occurs in security operations (SecOps) teams<br />
when they are unable to prioritise multiple<br />
alerts from disparate tools. As a result, 93% of<br />
respondents to the survey undertaken by Expel<br />
in its report, 'The UK cybersecurity landscape:<br />
challenges and opportunities' say they've<br />
regularly missed personal commitments<br />
because of their jobs, while 34% state that<br />
this happens most or all of the time.<br />
"Some 52% agreed that their team spends<br />
too much time dealing with unnecessary<br />
cybersecurity notifications. Over half (52%) of<br />
UK IT decision makers (ITDMs) expect security<br />
team members to leave within the year, due to<br />
burnout."<br />
There are a few factors that contribute to<br />
the increase of stress and burnout in cyber<br />
security, Ventura adds. "The rise in the number<br />
of cyber-attacks has grown exponentially since<br />
the start of the pandemic, with 22% of all<br />
data breaches in 2022 involving phishing<br />
attacks and a 72% to 105% spike in ransomware<br />
attacks since the global pandemic hit in<br />
2020. The speed at which cyber-attacks are<br />
happening and evolving means that many<br />
cyber security professionals experience stress<br />
and burnout when trying to keep up with<br />
them all. The speed of innovation relating to<br />
cyber threats is increasing rapidly."<br />
With a skills shortage in cyber security,<br />
increasing regulation, having to secure masses<br />
of data in many places and the threat of<br />
losing their job or of being disciplined, it is<br />
very rare for cyber security professionals to<br />
seek help when they are feeling overwhelmed.<br />
"It is no wonder that many cyber security<br />
professionals are experiencing high levels of<br />
stress and burnout. Addressing workplace<br />
burnout in cyber security is not an<br />
insurmountable challenge. By actively striving<br />
to alleviate stress among your employees and<br />
fostering a company culture that prioritises<br />
security awareness, your organisation can<br />
effectively tackle this issue."<br />
UNYIELDING BURDEN<br />
A recent report carried out by Mimecast<br />
revealed that the burden of ransomware<br />
attacks hasn't relented for the past few years<br />
and it's becoming clear that these attacks carry<br />
an arduous long-term impact on employees.<br />
Other findings from the research include:<br />
61% say that ransomware attacks have<br />
had a negative impact on their mental<br />
health<br />
58% say that their role gets more stressful<br />
every year, which makes sense as attacks<br />
are becoming more harmful each year.<br />
Many professionals are reaching their<br />
breaking point, adds Mimecast, with 42%<br />
"considering leaving their role in the next two<br />
years, due to stress or burnout".<br />
JJ Gericke, ThreeTwoFour: it’s the<br />
responsibility of all organisations to<br />
ensure people are fairly compensated for<br />
working in a high-stress environment.<br />
Jasmine Eskenzi, The Zensory: a real need for<br />
organisational leaders to commit to making<br />
a difference which can be achieved by<br />
adopting a 'cyber mindful' mindset.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> computing security<br />
19
identity & access<br />
THE NEW ROAD AHEAD<br />
A NEW NATIONAL ROADMAP FOR IDENTITY AND ACCESS MANAGEMENT SINGLES OUT STRATEGIC OBJECTIVES,<br />
ALIGNS EFFORTS WITH NATIONALLY DEFINED PRIORITIES AND SUPPORTS LONG-TERM PLANNING<br />
With the National Institute of<br />
Standards and Technology's draft<br />
roadmap for identity and access<br />
management (IAM) clearly signalling a strong<br />
push for meaningful change, NIST is now<br />
carefully considering the responses that it<br />
sought on where it is hitting the mark and<br />
where the roadmap might need to be beefed<br />
up (feedback closed on 1 June).<br />
Amongst the specific questions that NIST<br />
wanted addressed were:<br />
Are the guiding principles clear? Are any<br />
important principles missing?<br />
Do any of the strategic objectives need<br />
clarification? Are any key objectives<br />
missing?<br />
Are there specific activities, research or<br />
guidance that should be included and,<br />
if so, why?<br />
Which strategic objectives are most<br />
likely to have an impact and<br />
should be prioritised?<br />
Why is the roadmap so important? "As we<br />
become more reliant on connected<br />
technologies, we also become more reliant<br />
on authentication," states Tim Hollebeek,<br />
industry technology strategist, DigiCert.<br />
"Offline, we use our handwritten signatures<br />
or show photo ID against which our visages<br />
can be compared. Online, however, our<br />
identities have to be verified remotely and<br />
many of the ways in which we currently do<br />
that are aging badly. Passwords, for example,<br />
have been an enduring part of authentication<br />
for decades. They've also been an enduring<br />
risk for organisations whose passwords can<br />
often be easily guessed, are easily forgettable<br />
and are often reused across accounts."<br />
Similarly, users are now demanding greater<br />
levels of privacy and greater autonomy over<br />
what they share and with whom. 'Mobile<br />
driver's licence' standards are also emerging<br />
out of private and public sectors - such as<br />
the EU's digital identity wallet - which aim<br />
to provide a digital solution to mirror the<br />
authority of an offline photo ID for remote<br />
identity verification. It is amid this shifting<br />
landscape that the NIST roadmap intends<br />
to guide organisations to a modern<br />
authentication framework, he adds.<br />
"Any new guidance on Identity and Access<br />
Management will have to deal with new<br />
realities, such as the rise of remote work and<br />
the increase of workers accessing corporate<br />
resources through VPNs and from noncorporate<br />
Wi-Fi," adds Hollebeek. "The first<br />
stage of improving authentication is to take<br />
authentication responsibilities out of users'<br />
hands. Humans - as they say - are the<br />
weakest link and so the responsibility for<br />
authentication should be shifted away from<br />
them and towards technical solutions. Digital<br />
certificates offer a way to do that, offering<br />
seamless and strong authentication for users,<br />
based on Public Key Infrastructures."<br />
He argues that authentication processes<br />
should be automated to as great an extent<br />
as possible to handle the variety of devices,<br />
users and other assets that will be requesting<br />
access to a given network. "NIST is absolutely<br />
clear on this when it comes to digital<br />
certificates. It states in its SP 1800-16<br />
framework: 'Automation should be used<br />
wherever possible for the enrolment,<br />
installation, monitoring and replacement of<br />
certificates, or justification should be provided<br />
for continuing to use manual methods that<br />
20<br />
computing security <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
identity & access<br />
may cause operational security risks.'<br />
"However, NIST's IAM guidance eventually<br />
concludes it needs to tackle the reality of<br />
the modern network. That means relying<br />
on automation to take responsibility for<br />
authentication out of users' hands and<br />
leaning towards technical indicators to verify<br />
endpoint, device and user identities."<br />
NEW ERA OF DIGITAL IDENTITY<br />
According to a report from API-focused<br />
identity and access management company<br />
Curity, UK organisations and consumers<br />
are ready to embrace a new era of digital<br />
identity. Some 63% of UK organisations<br />
either currently use digital identity or have<br />
plans to incorporate digital identity solutions<br />
into their operations, it reports, with 61% of<br />
those planning to do so within the next year.<br />
Additionally, 52% of UK firms have plans to<br />
incorporate new and emerging decentralised<br />
identity solutions. UK consumers are also<br />
displaying a growing familiarity with digital<br />
wallets, with 58% of consumers currently<br />
using them and half of consumers that don't<br />
currently use digital wallets considering them<br />
in the future.<br />
The report, titled 'Plotting the Roadmap<br />
for Digital Identity'. surveyed 200 IT decision<br />
makers (ITDMs) in the UK and US as well as<br />
1000 consumers to better understand the<br />
rapidly changing digital identity landscape.<br />
This report comes as the UK government<br />
introduces a new trust framework for digital<br />
identities.<br />
The findings show that 60% of organisations<br />
surveyed expect digital identity to<br />
have a transformative impact on their<br />
industry, with financial services (89%) and<br />
health (86%) seen as two of the industries<br />
that are likely to benefit most from the latest<br />
innovations in this area, according to ITDMs.<br />
Other key findings show that top security<br />
challenges posed by digital identity for ITDMs<br />
are hacker sophistication (39%) and lack of<br />
appropriate infrastructure (37%). With<br />
organisations facing increasing pressure to<br />
protect customers' data, continued<br />
innovation and development in the digital<br />
identity space could not be of greater<br />
importance, states Travis Spencer, Curity CEO.<br />
"While there are encouraging signs that<br />
businesses are adequately prepared for the<br />
paradigm shift that decentralised identity will<br />
cause, the winners after the move will be<br />
those that cultivate trust among consumers.<br />
"The question of how digital identities are<br />
managed and by who will continue to be key<br />
over the coming years. To keep up with this<br />
pace of change and consumer expectations,<br />
digital identity must be on the priority list of<br />
enterprise architects and strategy makers."<br />
ALIGNMENT OF NEEDS<br />
What Belton Flournoy, managing director,<br />
Technology Consulting, Protiviti, finds most<br />
interesting about the NIST's upcoming focus<br />
areas is the alignment to what he perceives<br />
to be growing business needs. "For example,<br />
people are tired of having 20 passwords they<br />
must remember, many of which must be<br />
changed every few months. People want<br />
a seamless and secure experience. We are<br />
also seeing companies speak about the<br />
importance of the 'employee experience'<br />
today, the way they have the 'customer<br />
experience' for years.<br />
"The NIST IAM roadmap will look to address<br />
some next-generation security areas,", he<br />
says, "including enhanced facial recognition<br />
guidelines, enhanced contactless fingerprint<br />
capture, guidance related to identity<br />
management via mobile devices and<br />
an implementor's guide to modern<br />
authentication technology, to name a few.<br />
"This expansion will provide organisations<br />
with a stronger suite of reference materials to<br />
help take their security to the next level. The<br />
future is now, and it is an exciting time to be<br />
working in the identity and access management<br />
space."<br />
To access the NIST IAM roadmap, click here.<br />
Tim Hollebeek, DigiCert: the first stage<br />
of improving authentication is to take<br />
authentication responsibilities out of<br />
users' hands.<br />
Belton Flournoy, Protiviti: people want<br />
a seamless and secure experience.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> computing security<br />
21
managed services<br />
THE MAKING OF A MANAGED SERVICE<br />
MIKE RICHMOND, TECHNICAL SERVICES MANAGER AT BROOKCOURT SOLUTIONS, TOOK TIME<br />
OUT TO TALK TO STEVE USHER, BROOKCOURT'S SECURITY SERVICES MANAGER, TO UNDERSTAND<br />
MORE ABOUT HOW MANAGED SERVICES WORK AND HOW THEY BENEFIT BUSINESS<br />
What is a managed service and<br />
what types of managed<br />
services exist?<br />
A managed service is typically a service,<br />
product or role that is provided by a third<br />
party, where the third-party reports to the<br />
company they are contracted to.<br />
This can be anything from managing the<br />
endpoint anti-malware, to the mail or web<br />
gateways, or, in some cases, having a whole<br />
job role, such a data protection officer<br />
(DPO) or chief information security officer<br />
(CISO) that is carried out by the third party.<br />
How do managed services benefit<br />
a business?<br />
Managed services are of great benefit for<br />
multiple reasons. However, the primary<br />
reason, in my opinion, is the high-quality<br />
skill sets of staff engaged in the managed<br />
service provision (MSP), which is a cost<br />
benefit to the customer as, if the customer<br />
directly employed staff with those skill sets,<br />
their costs would be higher.<br />
Ability to limit full-time employee<br />
(FTE) head count<br />
Ability to have the latest version of a<br />
product and ensure those managing<br />
it are skilled on that product<br />
Access to highly specialised and<br />
experienced resources that would<br />
normally be outside of the budget<br />
of smaller companies<br />
Access to technology that could be<br />
outside the budget/reach of smaller<br />
companies<br />
Ensure the use of industry best<br />
practices for the various products<br />
and services.<br />
Enterprise organisations like financial<br />
institutions and big brands can afford to<br />
buy into the top technology - how do<br />
smaller organisations fare when it comes<br />
to their security posture?<br />
Access to top-tier technology can be a<br />
challenge to smaller companies, due to the<br />
cost of the technology and the skills that are<br />
required to utilise the technology and gain<br />
the most benefit from it. This is where<br />
MSPs can be leveraged to provide tier<br />
technologies that are wrapped in a<br />
service that enhances a company's<br />
security posture.<br />
Last year, we saw the launch<br />
of Mind Security, a new<br />
managed service offering.<br />
Can you tell me how it<br />
helps organisations with<br />
their security?<br />
The service essentially<br />
supports businesses with<br />
managed public breach<br />
monitoring and<br />
endpoint<br />
protection,<br />
and we<br />
plan to<br />
launch<br />
further solutions into the Mind Security<br />
portfolio in the coming months.<br />
What are the top security challenges all<br />
businesses face today?<br />
There are security challenges facing all<br />
companies daily and this list is expanding<br />
constantly.<br />
22<br />
computing security <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
managed services<br />
Unfortunately, many of the challenges that<br />
companies faced decades ago still exist,<br />
alongside newer challenges.<br />
Ransomware<br />
Ransomware is the top of just about every<br />
list, in terms of what concerns not just<br />
cyber security professionals, but anyone<br />
that is involved in the day-to-day activities<br />
of a business. Ransomware can have an<br />
impact on a business, from the internal<br />
disruption, loss or theft of data to the<br />
damaging impact to the company's<br />
reputation and brand in the public eye,<br />
which can result in a loss of income in<br />
the long term. The complexity of the<br />
ransomware is increasing, as are the<br />
vectors for attack and ways in which<br />
the cyber criminals are attempting<br />
to make money from an<br />
incident. Ransomware<br />
is understandably<br />
the top concern,<br />
due to the<br />
numerous<br />
ways in<br />
which an<br />
incident<br />
can impact a company; this is unlikely to<br />
change anytime soon.<br />
Credential Re-use<br />
Closely following ransomware, in terms of<br />
security concerns, is STILL credential reuse,<br />
even in the modern age of security awareness<br />
training, with public campaigns<br />
focusing on password security. Credential<br />
re-use remains a top concern, due to<br />
the fact employees often reuse company<br />
passwords on public sites. An attacker,<br />
with the right level of recon, will be able<br />
to use this to their advantage, if the<br />
employee has appeared in any user<br />
breaches of major sites.<br />
Phishing Attacks<br />
Phishing (Vishing, Smishing etc) and all<br />
attacks of this nature are a major concern,<br />
not just for businesses, but for the public<br />
as well. Phishing is one of the most<br />
common methods of attack and the<br />
complexity of the attacks is increasing<br />
substantially. Phishing is used to deliver<br />
numerous different malicious payloads,<br />
the most concerning being ransomware<br />
or trojans, both of which can have a<br />
devastating impact on the systems and<br />
companies affected.<br />
Mind Security describes itself as Cyber<br />
Security Peace of Mind. Can you explain<br />
the benefits of this service for your<br />
prospective customers?<br />
Mind security provides peace of mind by<br />
addressing two of the most common<br />
cyber security concerns experienced by<br />
businesses. Mind Security has chosen<br />
products that are best-of-breed for<br />
dealing with ransomware and<br />
credential re-use. The endpoint<br />
anti-malware product that has<br />
been adopted has some of the<br />
fastest reaction times of any<br />
product, as well as utilising<br />
AI to detect known and<br />
unknown threats. The<br />
technology adopted for<br />
the breach monitoring service has<br />
demonstrated itself to be one of the most<br />
effective in the industry, utilising one of<br />
the largest and most well-maintained<br />
databases of breached credentials/data.<br />
How do you decide which products are<br />
a good fit for the making of a managed<br />
service?<br />
We look for products that are best of<br />
breed, that are innovative or, if not<br />
innovative, have a solid track record of<br />
providing the service they set out to. There<br />
is a large focus on automation within the<br />
products that have been chosen, along<br />
with additional consideration given to the<br />
use of technologies, such as threat<br />
intelligence and, where feasible, artificial<br />
intelligence. We have been exceptionally<br />
careful to ensure that we only look at<br />
products touting AI, where there is a<br />
legitimate use case for the technology.<br />
The endpoint security offering within the<br />
service is driven by Deep Learning, which is<br />
a variant of Artificial Intelligence. What are<br />
the benefits of this?<br />
I think it is best we allow an AI to answer<br />
this in a few words.<br />
"Deep learning excels at automatically<br />
learning complex patterns from raw data,<br />
enabling hierarchical feature learning and<br />
achieving state-of-the-art performance in<br />
specific domains"<br />
Source: ChatGPT<br />
How do people find out more?<br />
Brookcourt has a team dedicated to<br />
supporting businesses to learn more about<br />
its products and solutions. To find out<br />
more about Mind Security, email the team<br />
at: enquiries@mindsecurity.co.uk<br />
mindsecurity.co.uk<br />
01737 886 111<br />
Useful Link:<br />
https://www.corporatescreening.com/blog/<br />
10-things-to-consider-when-looking-for-amanaged-service-provider<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> computing security<br />
23
GDPR<br />
BELATED HAPPY BIRTHDAY, GDPR!<br />
GDPR - THE GENERAL DATA PROTECTION REGULATION - HAS REACHED A MEMORABLE<br />
LANDMARK: IT IS NOW FIVE YEARS' OLD. HOW SUCCESSFUL HAS IT PROVED SO FAR?<br />
How do you measure the success<br />
of something as complex and<br />
far-reaching as the General Data<br />
Protection Regulation (GDPR), which was<br />
brought into existence five years ago to<br />
replace the 1995 Data Protection Directive<br />
used across various European countries.<br />
"After the internet becomes commonplace,<br />
the EU parliament decided they needed<br />
a new guideline that adapts to a more<br />
connected world where data is the common<br />
currency. The GDPR is designed to better fit<br />
modern technologies and practices," states<br />
Inspired eLearning. "The 1995 data<br />
protection law allows each country to control<br />
and customise its own privacy laws. This<br />
makes it harder for businesses to introduce<br />
their service between countries, since they'd<br />
have to refer to multiple privacy requirements<br />
and keep up with all of them."<br />
The GDPR eliminates all this, since now<br />
businesses only need to refer to one guideline<br />
and requirement to do business across all EU<br />
member states. It has also undergone several<br />
changes in the past few years. "Notably, in<br />
2021 the GDPR introduced major changes to<br />
its terms," adds Inspired eLearning. "For one,<br />
GDPR removed the Privacy Shield that was<br />
put in place to make it easier for US<br />
companies to do business with EU citizens.<br />
The other major change introduced in 2021<br />
would be the regulations for cookie consent,<br />
as GDPR now prevents companies from<br />
blocking access to content, unless a user<br />
consents to cookies."<br />
However, there is much debate about how<br />
effective this last change is proving, as many<br />
companies are making it extremely hard for<br />
people to refuse cookies, often making<br />
refusal difficult and/or pushing them to<br />
accept with various 'inducements'.<br />
The UK's GDPR, not to be confused with the<br />
EU General Data Protection Regulation, is<br />
a standard based on the EU version created<br />
by the UK Information Commissioner's Office<br />
(ICO) and included within their 2018 Data<br />
Protection Act. "This data protection law<br />
serves as a substitute for the EU version after<br />
Brexit. If you regularly process data of<br />
Europe-based customers, you'd have to<br />
adhere to both European data protection<br />
laws. As a result, the overall sum of fines<br />
significantly increases month after month."<br />
For the 12 months up to 1 March <strong>2023</strong>,<br />
1,576 fines were recorded in the CMS<br />
Enforcement Tracker database (an increase<br />
of 545 on 2022), amounting to around<br />
EUR 2.77 billion in fines (up 1.19 billion in<br />
comparison to 2022). The tracker also<br />
indicates1.446 fines have been issued since<br />
2018.<br />
"One might think that the companies who<br />
receive fines maliciously mishandled data, yet<br />
in reality compliance is a complex process,"<br />
points out Inspired eLearning. "When it<br />
comes to GDPR implementation, there are<br />
several grey areas as the provisions cover<br />
many different activities and were designed<br />
to withstand continual innovation. Meaning<br />
GDPR compliance is certainly not an easy box<br />
to check off on a company's to-do list.<br />
"Statistically, the violations with the most<br />
fines are related to data processing noncompliance.<br />
Against this background, luckily,<br />
there are tools put forward by GDPR itself<br />
that businesses can implement to increase<br />
their safeguards and, ultimately, reduce legal<br />
uncertainty and the risk of fines. In this<br />
context, codes of conduct (Art. 40) are one<br />
of the instruments GDPR has introduced to<br />
optimize and harmonise its implementation.<br />
"The EU Cloud Code of Conduct is a tool<br />
24<br />
computing security <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
GDPR<br />
that bridges the gap between the general<br />
provisions of the regulation and their<br />
concrete implementation across the whole<br />
cloud industry. Since its approval in 2021,<br />
the Code has been playing a key role when<br />
it comes to cloud compliance, fostering<br />
the application of robust technical and<br />
organisational measures throughout the<br />
sector.<br />
How has the GDPR gone so far within<br />
the industry? We asked several interested<br />
parties and here are their responses:<br />
Sylvain Cortes, VP of Strategy, Hackuity:<br />
"Compliance is essential, but we urge<br />
organisations to take the opportunity to<br />
think beyond baseline requirements to<br />
develop a culture of continuous cyber<br />
improvement. It's important to remember<br />
that achieving compliance shouldn't be<br />
treated like 'exam-cramming' with last-ditch<br />
efforts to achieve annual or quarterly audits.<br />
The goal is to achieve more than the<br />
minimum requirements and move away<br />
from the tick-box mindset. GDPR compliance<br />
is necessary, but it is far from sufficient for<br />
modern organisations."<br />
Rick Hanson, president, Delinea:<br />
"I've been in the cyber community since<br />
the mid-90s and one consistency over the<br />
years is that personal data has always been<br />
paramount. However, even though the<br />
industry often understood what needed to<br />
be done to protect personal data, it was<br />
frequently deemed to be too costly or<br />
complex to implement.<br />
"Five years ago, I applauded the EU for<br />
taking a stand, and providing guidelines and<br />
a framework to ensure that personal data<br />
and privacy were protected with GDPR. Yet<br />
even as this legislation passed and privacy<br />
advocates celebrated, many businesses<br />
were very concerned, due to perceived<br />
burdensome and costly efforts that would be<br />
required of them to be compliant. Looking<br />
back on this anniversary, I am very encouraged<br />
that the technology community has<br />
innovated and evolved to solve many of<br />
these issues and challenges quickly. My belief<br />
is that it sets a solid foundation that the rest<br />
of the world can follow, as we continuously<br />
work to protect our personal data and<br />
privacy.<br />
"We have come a long way since the early<br />
days of cyber and GDPR makes a significant<br />
impact, yet it does not solve the cybersecurity<br />
threat. It offers a framework that helps<br />
classify and protect - yet these policies<br />
are public, giving any attacker a roadmap<br />
on how to circumvent the policy. As good<br />
as GDPR policy is, it does not mean our<br />
personal data is completely secure. We must<br />
continue to educate and innovate to solve<br />
these ongoing data privacy and security<br />
challenges."<br />
Paul Brucciani, cyber security advisor,<br />
WithSecure<br />
"The European Commission is criticised for<br />
many things, but GDPR is the one thing<br />
where it can hold its head up high and say,<br />
'We've led the world in this'. As regulatory<br />
milestones go, it's the equivalent of climbing<br />
Everest. And it seems to be working, as other<br />
jurisdictions are following suit.<br />
"Internet fragmentation, driven by the quest<br />
for digital power, is creating regulatory complexity<br />
and the EU has an important role in<br />
leading the world through this. For example,<br />
AI is the next big field that will need regulating<br />
and the EU has again made a head<br />
start on this with its proposed AI Act, a legal<br />
framework that is intended to be innovationfriendly,<br />
future-proof and resilient to<br />
disruption."<br />
Michael Covington, VP of Strategy, Jamf:<br />
"The EU's GDPR has had a tremendous<br />
impact on how organisations around the<br />
globe handle personal user data since the<br />
regulation went into effect five years ago.<br />
The threat of substantial fines - including the<br />
almost €3 billion that have been levied since<br />
Paul Brucciani, WithSecure: AI is the next<br />
big field that will need regulating and the<br />
EU has again made a head start on this.<br />
Eduardo Azanza, Veridas: trust in biometric<br />
solutions must be based on transparency<br />
and compliance.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> computing security<br />
25
GDPR<br />
Colum Lyons, ID-Pal: five years on from<br />
the introduction of GDPR and there is still<br />
a long road to go.<br />
Andy Robertson, Fujitsu UK and Ireland:<br />
going forward, the rise of AI-driven<br />
cyberattacks will make data protection all<br />
the more critical.<br />
the regulation went into effect - have forced<br />
companies to take privacy and security more<br />
seriously. And the impact is not just contained<br />
within Europe; GDPR has inspired more<br />
than 100 other regional privacy standards,<br />
including those in many of the individual US<br />
states.<br />
"Of course, with a regulation as complex<br />
as GDPR, there's still work to do, both for<br />
the governing bodies and the organisations<br />
that must achieve compliance. Learnings<br />
from the COVID-19 pandemic have raised<br />
concerns about new public health and data<br />
considerations that should be factored into<br />
future legislation. Additionally, the post-Brexit<br />
version of GDPR for the UK is still a work in<br />
progress, as is a firm stance on how data can<br />
be shared between EU member states and<br />
'partner' countries.<br />
"For individuals, GDPR is making a difference<br />
in how their personal data in safeguarded.<br />
And, for CISOs and data protection<br />
officers, the work continues to ensure<br />
organisations achieve regulatory compliance<br />
in a way that minimises disruption to the<br />
core business, while ensuring employees,<br />
customers and partners have confidence in<br />
how their personal data is being managed."<br />
Eduardo Azanza, CEO, Veridas:<br />
"Without question, GDPR has revolutionised<br />
data privacy and protection, and now, with<br />
the introduction of biometrics, the regulation<br />
takes on even more significance, as it celebrated<br />
its 5th anniversary. As defined by<br />
Article 4 of GDPR, biometric data is a form<br />
of personal data - therefore, businesses must<br />
carefully and securely manage it.<br />
"Earlier in May, Mobile World Congress<br />
(MWG) was slapped with a €200,000 fine<br />
by GDPR after they had collected biometric<br />
data from show attendees. The organisers<br />
failed to demonstrate due diligence before<br />
collecting biometric data, therefore infringing<br />
Article 35 of GDPR, which deals with requirements<br />
for carrying out a data protection<br />
impact assessment (DPIA).<br />
"With the rise of biometrics and AI, the<br />
focus on data protection and privacy has<br />
never been more important. Questions<br />
should be asked of biometric companies to<br />
ensure they are following GDPR laws, and<br />
are transparent in how data is stored and<br />
accessed. Trust in biometric solutions must<br />
be based on transparency and compliance<br />
with legal, technical and ethical standards.<br />
Only by doing this can we successfully<br />
transition to a world of biometrics that<br />
protects our fundamental right to data<br />
privacy."<br />
Colum Lyons, CEO and founder of ID-Pal:<br />
"Five years on from the introduction of GDPR<br />
and there is still a long road to go. Even this<br />
week, Meta has been hit with a record €1.2<br />
billion fine by the Irish Data Protection<br />
Commission (DPC) for violating a GDPR rule,<br />
proof that severe consequences are waiting<br />
for businesses, if the right GDPR-compliant<br />
measures are not in place.<br />
"Customers' personal data must be carefully<br />
managed and a lot of organisations still<br />
struggle to do this. As more and more<br />
industries are being asked to verify their<br />
customer identities, this is even more critical<br />
to get right when verifying identities as part<br />
of Anti-Money laundering (AML) or Know<br />
your Customer (KYC) processes. The onus is<br />
on the organisation to capture, verify and<br />
store their customer's personal data securely.<br />
Identity verification processes that use<br />
document verification, alongside biometrics<br />
and database means a solution meets<br />
regulatory guidelines in a more robust way,<br />
making the process more complex for<br />
fraudsters to outwit but makes the journey<br />
seamless for users."<br />
Andy Robertson, head of Enterprise and<br />
Cybersecurity Business, Fujitsu UK and Ireland<br />
"Once a compliance headache for businesses,<br />
GDPR has since been emulated by similar<br />
26<br />
computing security <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
GDPR<br />
legislation in other parts of the world. Simply<br />
put, data regulations are here to stay. In<br />
addition to safeguarding corporate and<br />
personal data, protocols have also brought<br />
about significant organisational changes.<br />
Many have been forced to examine how<br />
well they are managing and using data and,<br />
like a ruthless spring clean, have been able to<br />
cut down on unnecessary data they were<br />
paying to store.<br />
"Regulation has also helped to level the<br />
playing field by ensuring data use is standardised<br />
and nobody can gain an advantage<br />
through its unethical use - for customer<br />
targeting, for example. GDPR has given<br />
companies the chance to tangibly show<br />
consumers they can be trusted and it's<br />
positive to see how hard they have worked<br />
to be compliant.<br />
"Going forward, the rise of AI-driven<br />
cyberattacks will make data protection all<br />
the more critical. Generative AI platforms<br />
have the ability to create cyber security<br />
attacks, which means even those with<br />
very little cybersecurity and computing<br />
experience can carry them out. To combat<br />
this, organisations must identify equally<br />
sophisticated methods to protect themselves<br />
and their information. At the same time,<br />
they must review their high-level accounts -<br />
who has access to them and when the<br />
passwords were last changed - taking a strict<br />
approach to Multi-Factor Authentication and<br />
Conditional Access.<br />
"New technology creates advanced avenues<br />
for bad actors and shutting these down as<br />
they emerge - or beforehand when possible -<br />
is always a big challenge. While AI may be<br />
the technology that's being talked about<br />
now, there will inevitably be another down<br />
the track and GDPR will need to be adapted<br />
in kind. Similarly, with so many businesses<br />
investigating the use of AI as a productivity<br />
tool, there may be a need for rules that<br />
dictate how data can be used by these<br />
different platforms. As some rely on user<br />
inputs to train the software, one wonders<br />
whether this would constitute a breach of<br />
GDPR, if a particular tool was used to<br />
reformat or analyse sensitive information."<br />
Gert-Jan Wijman, VP of EMEA, Celigo:<br />
"GDPR's introduction five years ago was an<br />
important step for data privacy in Europe,<br />
needed to keep up with technology's rapid<br />
sprawl and privacy concerns that had plagued<br />
consumers. With so much corporate<br />
and personal data moving between systems,<br />
regulating this exchange was inevitable.<br />
"But, in the years since, complying with<br />
new laws and updates to existing regulation<br />
has proven a challenge. Ensuring data use<br />
is compliant is hard enough when an<br />
organisation is only in one market - more so<br />
when it's spread across the continent and<br />
different rules need to be adhered to. Some<br />
countries have stricter enforcement than<br />
others, or differing complementary privacy<br />
laws, and relying on people to ensure<br />
compliance is sustainable. It's a job that's<br />
menial, repetitive and can be overwhelming,<br />
with any human errors putting firms at<br />
reputational and financial risk.<br />
"For example, if a business receives a<br />
request from a customer that they want to<br />
opt out of a service and request the right to<br />
be forgotten, removing their details from<br />
one system and having others automatically<br />
follow suit is more efficient and failsafe than<br />
individually finding and deleting their details<br />
on each and every system.<br />
"Integration ensures that data can be<br />
kept in sync and standardised across linked<br />
applications and departments, so customers<br />
can be assured their data is only being used<br />
in line with existing usage rights and hasn't<br />
unintentionally been fed into - or left out of -<br />
a particular platform. And if they ask for the<br />
personal data being stored on them, workers<br />
won't need to sift through different systems,<br />
because information should be the same in<br />
every system."<br />
Jean-Philippe Deby, director of Global<br />
Accounts at Genetec:<br />
"Coming from the public safety software<br />
industry, we'd often see companies treating<br />
privacy and security as a binary choice. I'm<br />
delighted to say the EU GDPR helped change<br />
that mindset, acting as a major catalyst for<br />
change in Europe and beyond. Part of its<br />
legacy is that we now have explicit legislation<br />
for data and privacy protection in 137<br />
countries around the world. It's now much<br />
more accepted that privacy can be ensured<br />
without compromising security.<br />
"In terms of improvements, I am surprised<br />
how little attention has been paid to the<br />
specific challenges of ensuring compliance<br />
for the operation of video surveillance, access<br />
control and other physical security systems.<br />
Any public or private organisations using<br />
CCTV to monitor public accessible areas<br />
should be concerned and operators need to<br />
focus on adopting privacy by design. Under<br />
the terms of the EU GDPR, data that is<br />
anonymised or pseudonymised is classified as<br />
lower risk. The appropriate use of encryption<br />
and automated privacy tools is, therefore, a<br />
logical first step. For example, video redaction<br />
that blurs out people's faces in video, unless<br />
there is a legitimate reason to reveal their<br />
identity, can minimise the dangers of having<br />
security cameras deployed in public spaces.<br />
"Don't forget, owners of on-premises video<br />
surveillance, access control or ANPR systems<br />
are responsible for all aspects of EU GDPR<br />
compliance, including securing access to the<br />
systems and servers storing the information.<br />
However, by working with an approved cloud<br />
provider, it is possible to offload some of<br />
these responsibilities and significantly reduce<br />
the scope of activities required to ensure<br />
compliance. It is also highly cost effective.<br />
"Nevertheless, it is important to realise that<br />
it isn't a full abdication of responsibility. You<br />
remain accountable for ensuring data is<br />
classified correctly, and share responsibility<br />
for managing users and end-point devices."<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> computing security<br />
27
AI<br />
AI - APPROPRIATE INTERRUPTION?<br />
'TO HALT OR NOT TO HALT?' THAT IS THE QUESTION NOW BRINGING<br />
FORTH A SUCCESSION OF ADVOCATES ON BOTH SIDES OF THE AI DEBATE<br />
so many of these processes will continue at<br />
their own pace, regardless of the rate of<br />
release of new LLMs."<br />
Almer recognises there are two sides to the<br />
equation. "The current AI tools DO pose a<br />
significant risk, as well as a huge opportunity<br />
to change business processes that will affect<br />
many workers and open new possibilities,"<br />
he adds. "I find it hard to believe that ANY<br />
government, much less ALL governments,<br />
will be able to understand all implications<br />
and legislate a useful set of laws within a sixor<br />
12-month period."<br />
The fears and concerns over AI and the<br />
threats it may carry as its influence and<br />
power increases are now an ever-present<br />
across business and society. Such is the anxiety<br />
that it has engendered, more than 26,000<br />
people have signed an open letter asking all<br />
artificial intelligence companies to pause the<br />
training of powerful AI systems for at least<br />
six months, because of threats such as the<br />
proliferation of misinformation and the<br />
replacement of human workers by algorithms.<br />
Signatories include Elon Musk and Apply<br />
co-founder Steve Wozniak.<br />
"Recent months have seen AI labs locked in<br />
an out-of-control race to develop and deploy<br />
ever more powerful digital minds that no one<br />
- not even their creators - can understand,<br />
predict, or reliably control," the letter points<br />
out. Is the pause demanded justified or an<br />
overly cautious reaction to progress? Also,<br />
what benefits might a temporary halt bring?<br />
Ultimately, is AI something to be welcomed<br />
or feared, longer term?<br />
It's a debate that is often swayed by which<br />
side of the 'fence' you inhabit. Microsoft<br />
founder Bill Gates, for example, has spoken<br />
out against a hiatus, arguing that he doesn't<br />
think the proposed pause will solve the<br />
challenges. "Clearly there's huge benefits to<br />
these things… what we need to do is identify<br />
the tricky areas," Gates told Reuters news<br />
agency. He also had his doubts as to how<br />
exactly the AI pause would be enforced<br />
and what that would solve. "I don't really<br />
understand who they're saying could stop<br />
and would every country in the world agree<br />
to stop, and why to stop," he told Reuters,<br />
while acknowledging that " there are a lot<br />
of different opinions in this area".<br />
THREATS AND OPPORTUNITIES<br />
Edy Almer, Logpoint product manager for<br />
threat detection and incident response,<br />
believes that a few months' pause in the<br />
development of new AI models would do<br />
little to either affect disinformation spread<br />
or protect jobs. "The current class of LLMs<br />
[large language models], with new members<br />
graduating every week, already offers a huge<br />
opportunity for many business processes to be<br />
overhauled. This automation process is already<br />
longer than the release rate of new models,<br />
He points to the voices that are emanating<br />
from the EU trying to completely bar access.<br />
"They do not seem to be successful at this<br />
stage," he suggests. "Some of these leaders<br />
have issued a new and even more urgent<br />
plea: that mitigating the risk of extinction<br />
from AI should be a global priority alongside<br />
other societal-scale risks, such as pandemics<br />
and nuclear war.<br />
"This request, targeting world leaders, does<br />
stress the risk inherent in those models, but<br />
does not offer specific response paths. I would<br />
take it seriously, because the risks are evident.<br />
In our smaller cyber security realm - like, in<br />
many other areas, ignore LLMs at your own<br />
risk - you need to start experimenting with it<br />
or others will.<br />
"Take security orchestration, automation and<br />
response (SOAR), for example. An automated<br />
system that collects, analyses and prioritises<br />
alerts and security data from many sources<br />
and systems, it provides security teams with<br />
all the contextual information and intelligence<br />
they need for rapid detection and response.<br />
Using highly intelligent language learning<br />
models like ChatGPT, it becomes possible to<br />
28<br />
computing security <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
AI<br />
enhance SOAR with a generative AI<br />
integration as part of the SOAR's toolkit.<br />
Doing so can enable security teams to<br />
experiment with the technology to rapidly<br />
speed up time to insight."<br />
UP-CLOSE ENCOUNTERS<br />
For Sophos, the threats AI poses have been<br />
experienced up close - the company has<br />
uncovered multiple apps masquerading<br />
as legitimate ChatGPT-based chatbots to<br />
overcharge users and bring in thousands<br />
of dollars a month, it states. As detailed in<br />
Sophos X-Ops' report, 'FleeceGPT' Mobile<br />
Apps Target AI-Curious to Rake in Cash', these<br />
apps have "popped up in both the Google<br />
Play and Apple App Store, and, because the<br />
free versions have near-zero functionality and<br />
constant ads, they coerce unsuspecting users<br />
into signing up for a subscription that can<br />
cost hundreds of dollars a year".<br />
Comments Sean Gallagher, principal threat<br />
researcher, Sophos: "Scammers have and<br />
always will use the latest trends or technology<br />
to line their pockets. ChatGPT is no exception.<br />
With interest in AI and chatbots arguably<br />
at an all-time high, users are turning to<br />
the Apple App and Google Play Stores to<br />
download anything that resembles ChatGPT.<br />
These types of scam apps - what Sophos has<br />
dubbed 'fleeceware' - often bombard users<br />
with ads until they sign up for a subscription.<br />
"They're banking on the fact that users won't<br />
pay attention to the cost or simply forget that<br />
they have this subscription. They're specifically<br />
designed so that they may not get much use<br />
after the free trial ends, so users delete the<br />
app without realising they're still on the hook<br />
for a monthly or weekly payment."<br />
Sophos X-Ops investigated five of these<br />
Chat-GPT fleeceware apps, all of which<br />
claimed to be based on ChatGPT's algorithm.<br />
In some cases, as with the app 'Chat GBT', the<br />
developers played off the ChatGPT name to<br />
improve their app's ranking in the Google Play<br />
or App Store. While OpenAI offers the basic<br />
functionality of ChatGPT to users for free<br />
online, these apps were charging anything<br />
from $10 a month to $70 a year. The iOS<br />
version of 'Chat GBT', called Ask AI Assistant,<br />
charges $6 a week-or $312 a year-after the<br />
three-day free trial; it netted the developers<br />
$10,000 in March alone, according to<br />
Sophos. "Another fleeceware-like app, called<br />
Genie, which encourages users to sign up<br />
for a $7 weekly or $70 annual subscription,<br />
brought in $1 million over the past month."<br />
The key characteristics of so-called fleeceware<br />
apps, first discovered by Sophos in<br />
2019, states the company, are overcharging<br />
users for functionality that is already free<br />
elsewhere, as well as using social engineering<br />
and coercive tactics to convince users to sign<br />
up for a recurring subscription payment.<br />
Usually, the apps offer a free trial; but, with<br />
so many ads and restrictions, they're barely<br />
useable until a subscription is paid. These<br />
apps are often poorly written and implemented,<br />
meaning app function is often less<br />
than ideal, even after users have switched<br />
over to the paid version. They also inflate their<br />
ratings in the app stores through fake reviews<br />
and persistent requests of users to rate the<br />
app before it has even been used or the free<br />
trial ends.<br />
"Fleeceware apps are specifically designed to<br />
stay on the edge of what's allowed by Google<br />
and Apple, in terms of service, and they don't<br />
flout the security or privacy rules, so they are<br />
hardly ever rejected by these stores during<br />
review," further comments Gallagher. "While<br />
Google and Apple have implemented new<br />
guidelines to curb fleeceware since we<br />
reported on such apps in 2019, developers<br />
are finding ways around these policies,<br />
such as severely limiting app usage and<br />
functionality, unless users pay up.<br />
"While some of the ChatGPT fleeceware apps<br />
included in this report have already been<br />
taken down, more continue to pop up - and<br />
it's likely more will appear. The best protection<br />
is education. Users need to be aware that<br />
Edy Almer, Hors: The current class of<br />
LLMs (large language models) offers<br />
a huge opportunity for many business<br />
processes to be overhauled.<br />
Sean Gallagher, Sophos: his company has<br />
uncovered multiple apps masquerading as<br />
legitimate ChatGPT-based chatbots.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> computing security<br />
29
AI<br />
David Trossell, Bridgeworks: AI should<br />
continue to be embraced by enterprises<br />
and startups developing technologies in<br />
the future.<br />
Boris Cipot, Synopsys Software Integrity<br />
Group: legally, who is the owner or author<br />
of what is provided by AI and what are<br />
the flaws AI may have generated?<br />
these apps exist and always be sure to read<br />
the fine print whenever hitting 'Subscribe'.<br />
Users can also report apps to Apple and<br />
Google, if they think the developers are using<br />
unethical means to profit."<br />
KEEPING CONTROL<br />
People are often suspicious of new technologies,<br />
with Sci-Fi movies, such as 'The<br />
Terminator', playing on this fear, says David<br />
Trossell, CEO and CTO of Bridgeworks. "Sure,<br />
cyber-criminals could use AI against us, but<br />
equally we can use AI to protect ourselves;<br />
or to do more with fewer resources. Machine<br />
learning doesn't mean that autonomous<br />
machines will eventually control us. We<br />
can use AI and ML to maintain control.<br />
For example, new technologies that<br />
incorporate AI to ensure that voluminous<br />
amounts of encrypted data can travel<br />
securely at unrivalled speeds over a Wide<br />
Area Network."<br />
He points to the innovation called WAN<br />
Acceleration, which uses AI, ML and data<br />
parallelisation to mitigate latency and packet<br />
loss. "It permits the secure transport and<br />
ingression of encrypted data. Organisations<br />
can increase their bandwidth utilisation,<br />
without investing in new pipes. Without<br />
AI and ML, data would neither be as secure,<br />
nor as fast, over large distances. Rather than<br />
making IT redundant, it enables CIOs to<br />
focus on strategic tasks," advises Trossell.<br />
"Given the benefits of AI and ML, the<br />
question is: 'Why are they trying to stop the<br />
inevitable?' The genie is out of the bottle.<br />
Rodney Brooks [the Australian roboticist]<br />
argues that you have to be aware that, with<br />
any new technology, 50% of the answers are<br />
incorrect. Don't confuse performance with<br />
competence. It's a bit like the cloud. Everyone<br />
rushed to the cloud to avoid missing out,<br />
only to regret it. In 2017, The Global and<br />
Mail wrote: 'The public cloud provider<br />
Nirvanix, in San Diego, California, went<br />
under in 2013, forcing clients to scramble to<br />
retrieve their data before it was forever lost.'<br />
People should reflect, plan, and re-evaluate<br />
AI and ML, Trossell says. "The big VCs are<br />
piling in with money to get on the bandwagon<br />
and AI isn't new. As for ethics, they've<br />
never prevented the making of a dollar. You<br />
can see this with Meta and Twitter. Generative<br />
AI ChatGPT is going to be the same - just<br />
another tool. Will it cause mass unemployment?<br />
Possibly, but growing global trade<br />
and investment impact these changes as<br />
well. Organisations and consumers adapt,<br />
so AI should continue to be embraced by<br />
enterprises and startups developing technologies<br />
in the future."<br />
LEGAL IMPLICATIONS<br />
Ultimately, there is no denying the importance<br />
AI will have in the future, says Boris Cipot,<br />
senior security engineer at the Synopsys<br />
Software Integrity Group. "AI will change the<br />
way information is generated, processed and<br />
used. However, the primary question at this<br />
point is: who will control the usage of this AI?<br />
It is understandable that some companies<br />
have established policies that their employees<br />
do not use AI-based technology for workrelated<br />
tasks, as there are still many unanswered<br />
questions from a legal or security<br />
standpoint.<br />
"For instance, legally, who is the owner or<br />
author of what is provided by AI and what<br />
are the flaws AI may have generated? Here<br />
the flaws can be interpreted as vulnerabilities<br />
in source code created by AI or misinformation<br />
that it is susceptible to, based on<br />
materials used to train the AI. As learned<br />
from the past, technology can be used for<br />
good, but also for bad. AI, still in its infancy,<br />
is no different.<br />
"We cannot predict every possible decision<br />
for every scenario around which AI may be<br />
used," points out Cipot. "But AI systems need<br />
to be trained with reliable and accurate<br />
information, tested to ensure they're not<br />
spreading vulnerable or inaccurate output,<br />
and maintained to ensure they're leveraged<br />
in a productive and constructive way."<br />
30<br />
computing security <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
cyber strategy<br />
SECURITY BY DESIGN<br />
NEW CYBERSECURITY MEASURES BEING IMPOSED IN THE US WILL HIT<br />
SOFTWARE COMPANIES HARD. WHAT MIGHT THIS MEAN FOR THE UK?<br />
The US recently published its national<br />
cybersecurity strategy. Released by<br />
the Biden administration, it seeks to<br />
impose minimum security standards for<br />
critical infrastructure onto larger software<br />
makers. Equally, it means to shift responsibility<br />
for maintaining the security of<br />
computer systems away from consumers<br />
and small businesses. What impact is this<br />
likely to have on the security industry - and<br />
what implications, in particular, might this<br />
have for the UK? Does it have any other<br />
option but to follow the same path?<br />
Phil Tonkin, senior director of strategy<br />
at Dragos, says that the US National<br />
Cybersecurity Strategy aiming to move<br />
from a voluntary approach to cybersecurity<br />
in many industries to more aggressive,<br />
and mandatory, regulatory standards -<br />
a 'fundamental shift' to rebalance the<br />
responsibility to defend cyberspace -<br />
did not come as a surprise. "For months,<br />
administration officials telegraphed the<br />
intent to use regulatory and market drivers<br />
to shift the burden of mitigating cyber risks<br />
away from end users and to those best<br />
positioned to have earliest and broadest<br />
impact. This includes not just critical<br />
infrastructure owners and operators, but<br />
also technology companies, software<br />
makers and service providers," he says.<br />
However, this is not a shift that will not<br />
happen overnight. "While the US National<br />
Cybersecurity Strategy signals a stronger<br />
regulatory environment in the US, many<br />
different standards bodies and regulatory<br />
agencies oversee a patchwork of regulatory<br />
frameworks and requirements for different<br />
industries. Even as the administration has<br />
rolled out new requirements for certain<br />
industries, including railways and pipelines,<br />
others will require new authorities from<br />
Congress."<br />
REGULATORY ESSENTIALS<br />
What this means is that the US government<br />
and experts from industry have time to<br />
work together toward building regulatory<br />
requirements that achieve the best possible<br />
outcomes for securing infrastructure and<br />
the digital ecosystem, with a focus on real<br />
security and not just simple compliance<br />
advises Tonkin, who also points out how<br />
the strategy highlights the importance of<br />
international coalitions and partnerships to<br />
counter cyber threats, devoting an entire<br />
pillar to those shared goals.<br />
"The consequences of cybercrime are not<br />
geographically restricted, requiring a global<br />
approach to countering threats and managing<br />
vulnerabilities. Economies are interconnected<br />
globally as well, with many<br />
companies operating across countries<br />
and regions. So, any time a new security<br />
standard or regulation is adopted, industry<br />
has to react and this often has a ripple<br />
effect globally."<br />
He adds that the 2016 UK National Cyber<br />
Strategy has focused on developing<br />
capability with a particular focus on critical<br />
infrastructure across all areas. "In 2022, it<br />
began to consider this in the context of<br />
increasing digitisation, sustainability and<br />
reducing international dependence. This<br />
continues to mature, in particular as the UK<br />
begins to find its own direction in setting<br />
future Network Security legislation outside<br />
of the European Union. "Both the UK and<br />
EU have begun to move legislation to cover<br />
more entities, closer to the consumer,"<br />
Tonkin concludes. "However, there is a<br />
growing global recognition that the<br />
responsibility to secure digital products<br />
cannot be the responsibility of individuals.<br />
The eyes of the world will be on the US to<br />
learn how security by design is enforced."<br />
Phil Tonkin, Dragos.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> computing security<br />
31
ansomware attacks<br />
RANSOMWARE RAMPAGE<br />
ORGANISATIONS WORLDWIDE DETECTED 493.33 MILLION RANSOMWARE ATTACKS<br />
IN 2022, IT IS REPORTED. THE AVERAGE COST OF THESE ATTACKS WAS $4.54 MILLION,<br />
ACCORDING TO THE LATEST DATA RELEASED BY IBM<br />
The success of ransomware gangs<br />
has spurred a significant trend of<br />
professionalisation amongst<br />
cybercriminals where different groups<br />
develop specialised services to offer one<br />
another, according to a new report from<br />
WithSecure (formerly F-Secure Business).<br />
Ransomware has been around for decades,<br />
but the threat has continuously adapted<br />
to improvements in defences through the<br />
years. One notable development is the<br />
current dominance of multi-point extortion<br />
ransomware groups, which employ several<br />
extortion strategies at once (usually both<br />
encryption to prevent access to data and<br />
stealing data to leak publicly) to pressure<br />
victims for payments.<br />
According to an analysis by WithSecure of<br />
over 3,000 data leaks by multi-point extortion<br />
ransomware groups, organisations in the<br />
United States were the most common victims<br />
of these attacks, followed by Canada, the<br />
UK, Germany, France and Australia. Taken<br />
together, organisations in these countries<br />
accounted for three-quarters of the leaks<br />
included in the analysis.<br />
The construction industry seemed to be<br />
the most impacted and accounted for 19%<br />
of the data leaks. Automotive companies,<br />
on the other hand, only accounted for<br />
about 6%. A number of other industries sat<br />
between the two, due to ransomware groups<br />
having different victim distributions, with<br />
some families targeting one or more<br />
industries disproportionately to others.<br />
While the threat of ransomware has inflicted<br />
considerable pain on organisations in various<br />
countries and industries, its transformative<br />
impact on the cybercrime industry cannot be<br />
overstated, it is pointed out. States senior<br />
threat intelligence analyst Stephen Robinson:<br />
"In pursuit of a bigger slice of the huge<br />
revenues of the ransomware industry,<br />
ransomware groups purchase capabilities<br />
from specialist e-crime suppliers, in much t<br />
he same way that legitimate businesses<br />
outsource functions to increase their profits.<br />
"This ready supply of capabilities and<br />
information is being taken advantage of by<br />
more and more cyber threat actors, ranging<br />
from lone, low-skilled operators, right up<br />
to nation state APTs [advanced persistent<br />
threats]. Ransomware didn't create the<br />
cybercrime industry, but it has really thrown<br />
fuel on the fire."<br />
493 MILLION ATTACKS<br />
Richard Massey, the vice president of sales,<br />
EMEA, at Arcserve, comments that, in 2022,<br />
organisations worldwide detected 493.33<br />
million ransomware attacks. According to<br />
the latest data from IBM, the average cost<br />
of these attacks was $4.54 million.<br />
"Those are astounding numbers," comments<br />
Massey. "And, in response, governments<br />
are taking action. One of the actions they've<br />
taken already is forbidding payments to<br />
ransomware gangs. Recently, the US and UK<br />
announced sanctions, including a payment<br />
ban to Russia's notorious Trickbot ransomware<br />
gang. Florida and North Carolina have<br />
banned state government departments from<br />
paying ransom to cyber gangs; New York is<br />
considering similar legislation."<br />
SPLIT DECISION<br />
Massey continues: "Another action that<br />
governments are mulling is a legal requirement<br />
that companies be ransomware-ready.<br />
Is this a good idea? In a recent survey by<br />
Arcserve, respondents were evenly split on<br />
the question. They were also divided on the<br />
question of whether companies that do pay<br />
a ransom should face penalties. Those<br />
supporting penalties argue that paying a<br />
ransom encourages cybercriminals and<br />
perpetuates the problem. Those against<br />
penalties say that paying the ransom is often<br />
the only way to recover lost data and that<br />
penalising victims amounts to kicking them<br />
when they're down."<br />
These findings demonstrate the complexity<br />
of the issue and the challenges that are faced<br />
by governments and businesses addressing<br />
them, he adds. "For example, legally requiring<br />
companies to be ransomware-ready would<br />
have myriad benefits and drawbacks. On<br />
the benefit side, such laws could improve<br />
cybersecurity and limit ransomware attacks.<br />
They could reduce the financial impact on<br />
companies everywhere and inspire better<br />
consumer confidence in data security. On<br />
the drawback side, such laws would likely<br />
increase compliance costs, more regulatory<br />
complexity, and a false sense of security.<br />
32<br />
computing security <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
ansomware attacks<br />
While laws could establish a baseline<br />
standard for cybersecurity, that standard<br />
would be a challenge for many small and<br />
medium-sized enterprises. And besides,<br />
compliance would not be an ironclad<br />
guarantee of immunity to ransomware<br />
attacks."<br />
MOST VICTIMS PAY UP<br />
Meanwhile, according to the latest Cyber<br />
Confidence Index, from cybersecurity firm<br />
ExtraHop, 83% of victims of ransomware<br />
attacks pay up to the criminals. Whether or<br />
not these ransom payments are a good idea<br />
for those whose data is hacked, or even<br />
prevents the publication of their personal<br />
details, they do incentive criminal behaviour.<br />
This incident was seemingly caused by<br />
a vulnerability in a software supply chain,<br />
meaning a component of the application<br />
these HR teams thought they were buying<br />
was compromised, unknown to them.<br />
ExtraHop's research found that 77% of IT<br />
decision makers blame outdated cybersecurity<br />
practices for contributing to at least<br />
half of all their cybersecurity incidents.<br />
"With proper security processes in place,<br />
you can stop an attack before it develops<br />
into ransomware," says Jamie Moles, senior<br />
technical manager at ExtraHop. "Too often<br />
we see businesses fail to properly secure<br />
their networks and data, leading to breaches<br />
and stolen data. No one is exempt from<br />
ransomware gangs, which is why every<br />
business should prepare to be attacked."<br />
ATTACKS HIT HARD<br />
The recent Sophos 'State of Ransomware<br />
<strong>2023</strong>' report reinforces all of the turmoil that<br />
is generated by ransomware attacks, finding<br />
that, in 76% of ransomware attacks against<br />
surveyed organisations, adversaries succeeded<br />
in encrypting data. This is the highest rate<br />
of data encryption from ransomware since<br />
Sophos started issuing the report in 2020.<br />
The survey also showed that, when organisations<br />
forked out a ransom payment to<br />
get their data decrypted, they also ended up<br />
doubling their recovery costs ($750,000<br />
in recovery costs versus $375,000 for<br />
organisations that used backups to get data<br />
back). Moreover, paying the ransom usually<br />
meant longer recovery times, with 45%<br />
of those organisations that used backups<br />
recovering within a week, compared to just<br />
39% of those that paid the ransom.<br />
Overall, 66% of the organisations surveyed<br />
were attacked by ransomware - which was<br />
the same percentage as the previous year.<br />
This suggests that the rate of ransomware<br />
attacks has remained steady, despite any<br />
perceived reduction in attacks.<br />
"Rates of encryption have returned to very<br />
high levels after a temporary dip during the<br />
pandemic, which is certainly concerning.<br />
Ransomware crews have been refining their<br />
methodologies of attack and accelerating<br />
their attacks to reduce the time for defenders<br />
to disrupt their schemes," states Chester<br />
Wisniewski, field CTO, Sophos.<br />
"Incident costs rise significantly when<br />
ransoms are paid. Most victims will not be<br />
able to recover all their files by simply buying<br />
the encryption keys; they must rebuild and<br />
recover from backups as well. Paying<br />
ransoms not only enriches criminals, but it<br />
also slows incident response and adds cost to<br />
an already devastatingly expensive situation."<br />
When analysing the root cause of ransomware<br />
attacks, the most common was an<br />
exploited vulnerability (involved in 36% of<br />
cases), followed by compromised credentials<br />
(involved in 29% of cases). This is in line with<br />
recent in-the-field incident response findings<br />
from the Sophos '<strong>2023</strong> Active Adversary<br />
Report for Business Leaders'.<br />
MOVING IN ON MOVEIT<br />
According to the latest analysis from NCC<br />
Group's Global Threat Intelligence team,<br />
released in <strong>Jul</strong>y, Ransomware attacks<br />
Richard Massey, Arcserve: organisations<br />
worldwide detected 493.33 million<br />
ransomware attacks in 2022.<br />
Stephen Robinson, WithSecure: ransomware<br />
didn't create the cybercrime industry, but it<br />
has really thrown fuel on the fire.<br />
www.computingsecurity.co.uk @<strong>CS</strong>MagAndAwards <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> computing security<br />
33
ansomware attacks<br />
Chester Wisniewski, Sophos: most victims<br />
will not be able to recover all their files by<br />
simply buying the encryption keys.<br />
Steve O'Malley, Callsign: Organisations need<br />
a comprehensive approach, including using<br />
anti-fraud technologies that address all kinds<br />
of fraud.<br />
continue to hit record levels, with 434 attacks<br />
in June <strong>2023</strong>, a 221% increase on the same<br />
period last year (135 attacks - June 2022).<br />
June's high levels of activity has been mostly<br />
driven by Russian-speaking threat actor<br />
Clop's exploitation of the MOVEit file transfer<br />
software vulnerability, consistently high levels<br />
of activity by groups such as Lockbit 3.0 and<br />
the emergence of several new groups since<br />
May, says NCC. Clop was responsible for 90<br />
of the 434 attacks (21%) in June.<br />
LOCKED IN<br />
Lockbit 3.0, the most active threat actor of<br />
<strong>2023</strong> so far, was responsible for 62 of the<br />
attacks, a fall of 21% from 78 attacks in May.<br />
8base, a new threat actor discovered in May,<br />
stepped up activity with 40 attacks (9%) in<br />
June - making it the third most active threat<br />
group that month. Other notable activity<br />
included 17 attacks from Rhysida and nine<br />
attacks from Darktrace, two ransomware-asa-service<br />
(RaaS) groups that were first<br />
observed in May <strong>2023</strong>.<br />
"The considerable spike in ransomware<br />
activity so far this year is a clear indicator of<br />
the evolving nature of the threat landscape,"<br />
states Matt Hull, global head of threat intelligence<br />
at NCC Group. "The better-known<br />
players, such as Lockbit 3.0, are showing no<br />
signs of letting up, newer groups like 8base<br />
and Rhysida are demonstrating what they're<br />
capable of and Clop have exploited a major<br />
vulnerability for the second time in just three<br />
months.<br />
"It's imperative that organisations should<br />
remain vigilant and adapt their security<br />
measures to stay one step ahead,” he adds.<br />
“We strongly advise any organisation using<br />
MOVEit file transfer software to apply the<br />
recent patch, given this vulnerability is being<br />
actively exploited."<br />
SCAMS: KNOCK-ON IMPACT<br />
Meanwhile, Callsign has issued the results of<br />
its annual scams research, revealing what it<br />
describes as "the true extent of the damage<br />
that scams have to business reputation".<br />
Data from 8,000 consumers polled in nine<br />
countries - 1,000 in the UK - about their<br />
experiences of scams has identified a 40%<br />
increase in UK consumers who have received<br />
a scam message, compared to 2021. 23% of<br />
those who have received a scam message<br />
said this was enough for them to stop using<br />
the company or service associated with the<br />
message.<br />
The research found that over a third (38%)<br />
of UK respondents have lost money to scams<br />
and 35% hadn't received any form of reimbursement<br />
from their bank after becoming<br />
a victim of fraudulent activity.<br />
The types of 'scams' consumers said they<br />
can protect themselves from included all<br />
types of fraud such as phishing for PII data,<br />
romance scams, investment fraud, bots or<br />
malware for account take over purposes,<br />
and other undisclosed vectors.<br />
WHAT DENOTES A ‘SCAM’<br />
However, while the definition of what<br />
constitutes a scam varies across regions and<br />
financial institutions (FIs), only authorised<br />
fraud, such as authorised push payments<br />
(APP), are generally considered by a FI to be<br />
a scam. There appears to be a language gap<br />
between FIs and consumers when it comes<br />
to scams. It is possible the risk to corporate<br />
reputation is being underestimated by FIs,<br />
because banks' reputations are being<br />
impacted by fraud more broadly than just<br />
scams.<br />
"Organisations need a comprehensive<br />
approach, including using anti-fraud<br />
technologies that address all kinds of fraud,"<br />
says Steve O'Malley, chief revenue officer,<br />
Callsign. "This is the first step - along with<br />
finding a common language with customers<br />
around the threat of scams - towards<br />
repairing and rebuilding the trust that fraud<br />
can damage so easily, and better protecting<br />
a business' hard-won reputation."<br />
34<br />
computing security <strong>Jul</strong>y/<strong>Aug</strong>ust <strong>2023</strong> @<strong>CS</strong>MagAndAwards www.computingsecurity.co.uk
Computing<br />
Security<br />
Secure systems, secure data, secure people, secure business<br />
e-newsletter<br />
Are you receiving the Computing Security<br />
monthly e-newsletter?<br />
Computing Security always aims to help its readers as much as possible to do<br />
their increasingly demanding jobs. With this in mind, we've now launched a<br />
Computing Security e-newsletter which is produced every month and is available<br />
free of charge. This will enable us to provide you with more content, more<br />
frequently than ever before.<br />
If you are not already receiving this please send your request to<br />
christina.willis@btc.co.uk and advise her of the best email address for the<br />
newsletter to be sent to.