C&L May 2018
INTERVIEW Training your workforce on digital transformation Pg 8 COLUMN How to steer clear of GDPR violations? Pg 18 Volume 07 Issue 02 May 2018 150 TRACK TECHNOLOGY BUILD BUSINESS SHAPE SELF A 9.9 Group Publication
- Page 2 and 3: DON’T GAMBLE, BE PRACTICAL Join u
- Page 4 and 5: TRACK TECHNOLOGY BUILD BUSINESS SHA
- Page 6 and 7: around thetech WHAT CIOs ARE TIRED
- Page 8 and 9: Around The Tech UNCHAINED MELODY ma
- Page 10 and 11: INTERVIEW How are you upskilling yo
- Page 12 and 13: Interview Anand Narayanan, Simplile
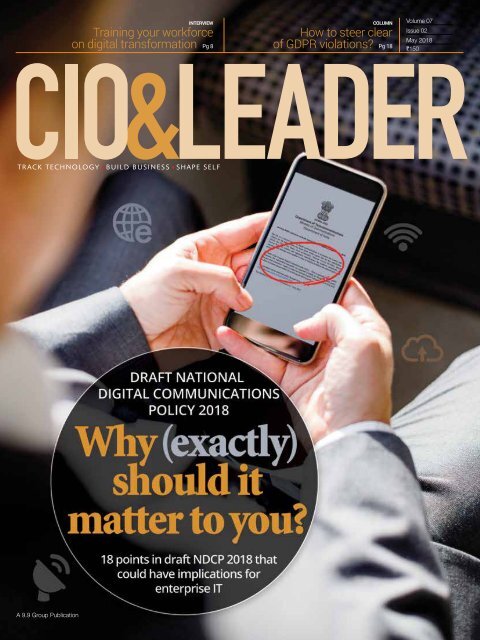
- Page 14 and 15: Cover Story 12 CIO&LEADER | May 201
- Page 16 and 17: Cover Story By its content, specifi
- Page 18 and 19: Cover Story 3 Transition to IPv6 fo
- Page 20 and 21: COLUMN How to build better data pro
- Page 22 and 23: Column Understanding APIs for priva
- Page 24 and 25: Column Five questions post Pichai
- Page 26 and 27: Column Bringing IoT sensors to the
- Page 28 and 29: FACE OFF // SHOULD CIOs BE HIRED FR
- Page 30 and 31: SECURITY Information sharing is key
- Page 32 and 33: INSIGHT Mixing digital technologies
- Page 34 and 35: Insight CEOs priorities shifting to
- Page 36 and 37: Insight Artificial intelligence see
- Page 38 and 39: Insight Facebook seeks a 'friend' i
- Page 40 and 41: Insight The dirty secrets of networ
- Page 42 and 43: Insight Organization’s firewall i
INTERVIEW<br />
Training your workforce<br />
on digital transformation Pg 8<br />
COLUMN<br />
How to steer clear<br />
of GDPR violations? Pg 18<br />
Volume 07<br />
Issue 02<br />
<strong>May</strong> <strong>2018</strong><br />
150<br />
TRACK TECHNOLOGY BUILD BUSINESS SHAPE SELF<br />
A 9.9 Group Publication
DON’T GAMBLE,<br />
BE PRACTICAL<br />
Join us at<br />
https://bit.ly/2JCxZ0w<br />
RSVP - Abhishek Jain<br />
abhishek.jain@9dot9.in | +91 9312119363<br />
To register<br />
please scan<br />
#thepracticalcio #cioannual
EDITORIAL<br />
Shyamanuja Das<br />
shyamanuja.das@9dot9.in<br />
CIOs badly<br />
need an<br />
outside-in<br />
perspective…<br />
A<br />
All that we do<br />
in this issue is<br />
to highlight the<br />
important points<br />
within the draft<br />
(communication<br />
policy) that<br />
have direct<br />
and indirect<br />
implications for<br />
IT and security<br />
managers<br />
good two weeks after the Srikrishna Committee<br />
released its whitepaper outlining various<br />
issues to consider in a possible data privacy<br />
legislation in India, I tried to informally seek<br />
the opinion of delegates—CIOs, CISOs and<br />
other senior security professionals—participating<br />
in a security-themed event. Just 3-4 out<br />
of more than 30 delegates knew something<br />
about the report.<br />
I was not exactly shocked. I was already working<br />
on a story on the digitalization journey of<br />
large Indian corporations then and was getting<br />
a strong message that if not many CIOs are leading<br />
the digitalization journey, it is not<br />
because they are devoid of any skills but<br />
many of them cannot draw on a blank<br />
canvas. They are excellent problem solvers<br />
but they expect the ‘problem’ to be<br />
defined for them. Digitalization—where<br />
‘use cases’ is the ruling catchphrase—<br />
does not work that way.<br />
Earlier, enterprise IT managers<br />
understood only technology; then,<br />
understood processes and corresponding<br />
metrics; now, many of them have<br />
a fairly good understanding of their<br />
own business dynamics. That is good<br />
enough to derive value from technology<br />
for ‘business as usual’ part. But<br />
to derive value from new technology, new changes<br />
in economy, business environment, regulatory<br />
regimes, they need to keep their eyes and ears open.<br />
Unlike the Srikrishna Committee white paper, the<br />
new national digital communication policy is a fullfledged<br />
policy document. Despite its positioning as<br />
the latest update to the country’s telecom policy, it<br />
is not a mere sectoral policy draft—partly because<br />
communication itself has broadened its scope and<br />
partly because the government has chosen to include<br />
certain policy positions—such as data privacy itself—<br />
within this policy draft.<br />
Yet, the awareness about its provisions is also low<br />
among the community. All that we do in this issue is<br />
to highlight the important points within the draft that<br />
have direct and indirect implications for IT and security<br />
managers. To that extent, it is not even a story.<br />
But carrying it on cover is also our way of reiterating<br />
that environmental changes are as important as<br />
changes in an organization or a particular industry<br />
in what has already become an outside-in regime<br />
<strong>May</strong> <strong>2018</strong> | CIO&LEADER<br />
1
TRACK TECHNOLOGY BUILD BUSINESS SHAPE SELF<br />
A 9.9 Media Publication<br />
INTERVIEW<br />
Training your workforce<br />
on digital transformation Pg 8<br />
COLUMN Volume 07<br />
Issue 02<br />
How to steer clear<br />
<strong>May</strong> <strong>2018</strong><br />
of GDPR violations? Pg 18<br />
150<br />
CONTENT<br />
MAY <strong>2018</strong><br />
COVER STORY<br />
12-17 | Why the new<br />
policy matters…<br />
Despite a narrower positioning by Department of<br />
Telecommunications, the new digital communication<br />
policy is a statement of intent to improve the digital<br />
environment holistically<br />
Cover Design by:<br />
Manoj Kumar VP<br />
advertisers ’<br />
index<br />
Accenture<br />
BC<br />
Please Recycle<br />
This Magazine<br />
And Remove<br />
Inserts Before<br />
Recycling<br />
COPYRIGHT, All rights reserved: Reproduction in whole or in part without written permission<br />
from Nine Dot Nine Mediaworx Pvt Ltd. is prohibited. Printed and published by Vikas Gupta for<br />
Nine Dot Nine Mediaworx Pvt Ltd, 121, Patparganj, <strong>May</strong>ur Vihar, Phase - I, Near Mandir Masjid,<br />
Delhi-110091. Printed at Tara Art Printers Pvt ltd. A-46-47, Sector-5, NOIDA (U.P.) 2013011<br />
This index is provided as an<br />
additional service.The publisher<br />
does not assume any liabilities<br />
for errors or omissions.<br />
2 CIO&LEADER | <strong>May</strong> <strong>2018</strong>
AROUND THE TECH<br />
04<br />
Bending the issue<br />
www.cioandleader.com<br />
COLUMN<br />
20-21<br />
Understanding APIs<br />
for private cloud<br />
implementations<br />
By Abhinav Asthana<br />
24-25<br />
Bringing IoT sensors to<br />
the farm<br />
By Adam Drobot<br />
SECURITY<br />
28-29<br />
Information sharing is<br />
key to ward off cyber<br />
threats<br />
INSIGHT<br />
30-31<br />
Mixing digital<br />
technologies<br />
34-35<br />
Artificial<br />
intelligence sees<br />
big business<br />
38-40<br />
The dirty secrets of<br />
network firewalls<br />
MANAGEMENT<br />
Managing Director: Dr Pramath Raj Sinha<br />
Printer & Publisher: Vikas Gupta<br />
EDITORIAL<br />
Managing Editor: Shyamanuja Das<br />
Associate Editor: Shubhra Rishi<br />
Content Executive-Enterprise Technology:<br />
Dipanjan Mitra<br />
DESIGN<br />
Sr Art Director: Anil VK<br />
Art Director: Shokeen Saifi<br />
Visualisers: NV Baiju & Manoj Kumar VP<br />
Lead UI/UX Designer: Shri Hari Tiwari<br />
Sr Designers: Charu Dwivedi, Haridas Balan & Peterson PJ<br />
SALES & MARKETING<br />
Director-Community Engagement<br />
for Enterprise Technology Business:<br />
Sachin Mhashilkar (+91 99203 48755)<br />
Brand Head: Vandana Chauhan (+91 99589 84581)<br />
Assistant Product Manager-Digital: Manan Mushtaq<br />
Community Manager-B2B Tech: Megha Bhardwaj<br />
Community Manager-B2B Tech: Renuka Deopa<br />
Associate-Enterprise Technology: Abhishek Jain<br />
Regional Sales Managers<br />
North: Deepak Sharma (+91 98117 91110)<br />
West: Prashant Amin (+91 98205 75282)<br />
South: BN Raghavendra (+91 98453 81683)<br />
Ad Co-ordination/Scheduling: Kishan Singh<br />
PRODUCTION & LOGISTICS<br />
Manager Operations: Rakesh Upadhyay<br />
Asst. Manager - Logistics: Vijay Menon<br />
Executive Logistics: Nilesh Shiravadekar<br />
Logistics: MP Singh & Mohd. Ansari<br />
OFFICE ADDRESS<br />
9.9 Group Pvt. Ltd.<br />
(Formerly known as Nine Dot Nine Mediaworx Pvt. Ltd.)<br />
121, Patparganj, <strong>May</strong>ur Vihar, Phase - I<br />
Near Mandir Masjid, Delhi-110091<br />
Published, Printed and Owned by 9.9 Group Pvt. Ltd.<br />
(Formerly known as Nine Dot Nine Mediaworx Pvt. Ltd.)<br />
Published and printed on their behalf by<br />
Vikas Gupta. Published at 121, Patparganj,<br />
<strong>May</strong>ur Vihar, Phase - I, Near Mandir Masjid, Delhi-110091,<br />
India. Printed at Tara Art Printers Pvt Ltd., A-46-47, Sector-5,<br />
NOIDA (U.P.) 201301.<br />
Editor: Vikas Gupta<br />
<strong>May</strong> <strong>2018</strong> | CIO&LEADER<br />
3
around<br />
thetech<br />
WHAT<br />
CIOs ARE<br />
TIRED OF<br />
HEARING...<br />
“We don't have<br />
the budgets but<br />
let's make it<br />
work!"<br />
GENDER<br />
Bending the issue<br />
We have talked a great deal about<br />
gender equality in the workforce.<br />
In enterprise IT and security, the<br />
percentage of women in the workforce is<br />
strikingly poor. Take for instance, ISACA’s<br />
annual State of Cybersecurity <strong>2018</strong><br />
report, a 31-point perception gap exists<br />
between male and female respondents,<br />
with 82% of male respondents saying<br />
men and women are offered the same<br />
opportunities for career advancement in<br />
cybersecurity, compared to just 51% of<br />
female respondents.<br />
The report also found that while gender<br />
disparity exists, it can be mitigated<br />
through effective diversity programs. In<br />
organizations that have one, men and<br />
women are much more likely to agree<br />
that men and women have the same<br />
career advancement opportunities. A<br />
full 87% of men say they have the same<br />
opportunities, as compared to 77% of<br />
women.<br />
A lot of companies are publicly taking<br />
up this cause to improve diversity in<br />
the workforce. Take for instance, staff<br />
in Starbucks' outlets that the company<br />
owns in the U.S.—more than 8,000 in<br />
total—are undergoing racial-bias training.<br />
The city of Boston is also addressing<br />
the cause by offering to train women in<br />
negotiating their salaries better.<br />
In Hollywood too, women are speaking<br />
up about gender bias.<br />
However, IT and security leaders need<br />
to do more. By hiring qualified women,<br />
companies can tackle the widening<br />
skill gap. They can create a cohesive<br />
work environment and help make IT<br />
a preferred career choice for women<br />
employees. How are you addressing the<br />
issue in your organization?<br />
4 CIO&LEADER | <strong>May</strong> <strong>2018</strong>
Around The Tech<br />
BY THE BOOK<br />
This book takes you on a journey to<br />
project a worldview where women<br />
haven't asked for permission from<br />
Silicon Valley to chase their dreams.<br />
They are going for it -- building the next<br />
generation of tech start-ups, investing<br />
in each other's ventures, crushing<br />
male hacker stereotypes and rallying<br />
women and girls everywhere to join<br />
the digital revolution. Geek Girl Rising<br />
isn't about the famous tech trailblazers<br />
you already know, like Sheryl Sandberg<br />
and Marissa <strong>May</strong>er. Instead, veteran<br />
journalists Heather Cabot and<br />
Samantha Walravens introduce readers<br />
to the fearless female entrepreneurs and<br />
technologists fighting at the grassroots<br />
level for an ownership stake in the<br />
revolution that's changing the way we<br />
live, work and connect to each other.<br />
Readers will be introduced to Debbie<br />
Sterling, inventor of GoldieBlox, the first<br />
engineering toy for girls, which topples<br />
the notion that only boys can build.<br />
They'll get a peek inside YouTube sensation<br />
Michelle Phan's ipsy studios, where<br />
she is grooming the next generation<br />
of digital video stars while leading her<br />
own mega e-commerce beauty business.<br />
makingheadlines<br />
The General Data Protection Regulation (GDPR) is newest regulation to come<br />
into effect in the European Union. However, it hasn't deterred two of the Big Four<br />
from being hit with a handful of lawsuits having to do with how they share data.<br />
The Verge, citing the lawsuits, reported they are seeking to hit Facebook and<br />
Google with fines that collectively amount to around USD 8.8 billion. The<br />
lawsuits were filed by Max Schrems, an Australian activist who has long<br />
criticized how the companies collect data on their users.<br />
Under the new regulation, companies have to provide clear consent and justify<br />
why they are collecting data on their users, as well as clarify what they intend to<br />
do with it. They are also required to overhaul their privacy and data collection<br />
policies to better protect consumers.<br />
Google and Facebook have been addressing GDPR before it was law, rolling out<br />
new policies and products to better protect the data, but those steps aren't enough.<br />
What happens when an entire city tries to close the<br />
gender pay gap? In the last few years, the city of<br />
Boston has doubled down on a commitment made<br />
in 2013 by its former <strong>May</strong>or, Thomas M. Menino, to<br />
bring pay equity to the city’s workforce. The Boston<br />
Women’s Workforce Council teams up with the area’s<br />
companies and institutions, including major ones<br />
like Morgan Stanley, Zipcar and the Massachusetts<br />
Institute of Technology, to help them figure out<br />
ways to advance women, which they share with one<br />
another in quarterly best-practice meetings.<br />
The city has also trained over 7,000 women<br />
in salary negotiation, with a goal of training an<br />
additional 78,000 by 2021. A more immediate<br />
deadline: The Massachusetts Equal Pay Act,<br />
passed by the legislature in 2016, goes into effect<br />
in July <strong>2018</strong>.<br />
gender<br />
bender<br />
<strong>May</strong> <strong>2018</strong> | CIO&LEADER<br />
5
Around The Tech<br />
UNCHAINED MELODY<br />
matter of<br />
twitter<br />
The ability of blockchain to track, trace, and authenticate products,<br />
record contracts, guarantee the movement of information and<br />
record transactions means it can be put to use across the entire<br />
value chain, with the benefits consequently being passed on to the<br />
consumer in the form of savings, increased trust and transparency,<br />
and safer and higher quality products.<br />
In this new Deloitte report, we examine the implications and<br />
assess the value of specific blockchain use-cases, analyzing how<br />
they could be used to resolve key business issues.<br />
Deloitte has predicted that blockchain technology will reach a tipping<br />
point in the next five years, moving from a fringe technology<br />
associated with dubious cryptocurrency investments and get rich<br />
quick stories to a standard operational technology across the financial,<br />
manufacturing and consumer industries.<br />
Along the way, blockchain will face significant challenges, but if<br />
these can be overcome and the technology continues to develop as<br />
expected, there could be widespread adoption among enterprises.<br />
The ultimate beneficiary will be the consumer. If blockchain can<br />
create efficiencies and save costs throughout the supply chain.<br />
VITAL<br />
STATISTICS<br />
Why are so few<br />
women investing<br />
into bitcoin?<br />
94.73%<br />
5.27%<br />
*Note –the responses to these questions should be<br />
evaluated based on the facts and circumstances in<br />
your organization and discussed with legal counsel.<br />
6 CIO&LEADER | <strong>May</strong> <strong>2018</strong>
Around The Tech<br />
These five companies have secured the<br />
top five spots in Fortune 500 Companies<br />
<strong>2018</strong> list. Amazon entered the top 10 list<br />
of Fortune 500 companies for the first<br />
time. It became the second tech company<br />
after Apple to be in Top 10. Telecom<br />
major AT&T follows Amazon in the list.<br />
Alphabet, Microsoft, IBM, Dell and<br />
Intel are the other tech companies<br />
who feature among the top 10. While<br />
Apple dropped one position in the<br />
revenue ranking, technology companies<br />
till create the most value. The<br />
four most valuable companies on the<br />
list are all technology firms—Apple,<br />
Alphabet, Microsoft and Amazon.<br />
Walmart<br />
Rank: 1<br />
Revenues: USD500,343<br />
Walmart business in the U.S. is<br />
transforming its website into an<br />
online mall offering a slew of brands<br />
and expanding its grocery delivery.<br />
It is also making big moves in both<br />
Five companies in the<br />
FORTUNE500 <strong>2018</strong> LIST<br />
China and India, looking to rev up<br />
international growth again.<br />
Exxon Mobil<br />
Rank: 2<br />
Revenues: USD244,363<br />
Oil giant is enjoying the same momentum<br />
as the rest of the energy sector, posting<br />
a 151% year-over-year earnings gain<br />
for 2017 on revenues of USD 244 billion.<br />
Berkshire Hathaway<br />
Rank: 3<br />
Revenues: USD242,137<br />
The conglomerate holding company–<br />
whose many subsidiaries include Geico<br />
and the railroad Burlington Northern–<br />
struggled to grow through acquisitions<br />
in 2017, losing out on its bid for Oncor<br />
when it refused to raise its offer.<br />
Apple<br />
Rank: 4<br />
Revenues: USD 229,234<br />
Apple took a small step back, from<br />
No. 3 to No. 4, despite a 6% gain in<br />
annual sales, but it led the way in<br />
profits with more than $48 billion<br />
in net income. In short, the Apple<br />
juggernaut continues at tremendous<br />
scale and despite the overall saturation<br />
of smartphones, which make up<br />
the vast majority of the company’s<br />
sales and profits.<br />
In a year dominated by proposed<br />
cross-sector health care mega-mergers<br />
like the CVS-Aetna deal, United-<br />
Health Group flew somewhat under<br />
the radar. But America’s largest<br />
health insurer was far from idle.<br />
UnitedHealth Group<br />
Rank: 5<br />
Revenues: USD 201,150<br />
UnitedHealth’s 2017 revenues<br />
spiked 9% compared with 2016 to<br />
$201 billion. That was mirrored<br />
by a 9.1% year-over-year boost in<br />
Optum’s revenues, which grew to<br />
$91.2 billion.<br />
<strong>May</strong> <strong>2018</strong> | CIO&LEADER<br />
7
INTERVIEW<br />
How are you<br />
upskilling your<br />
IT team on digital<br />
transformation<br />
initiatives?<br />
Simplilearn has launched a digital transformation<br />
academy for enterprises. Have IT leaders enrolled yet?<br />
By Shubhra Rishi<br />
8 CIO&LEADER | <strong>May</strong> <strong>2018</strong>
Anand Narayanan, Simplilearn<br />
Interview<br />
In the last few years, CIOs have been<br />
chanting the ‘digital transformation’<br />
catchphrase as if it is a common cure for<br />
all enterprise IT worries. However, a lot of<br />
organizations have embarked on standalone<br />
digital initiatives and are slowly<br />
evolving their digital readiness. However,<br />
a frequent issue that companies face is<br />
the lack of available talent to lead these<br />
innovations. As a result, a lot of companies<br />
are looking at hiring outside skills<br />
for the duration of the initiative. Some are<br />
also working with startups or external<br />
vendors. What about enterprises/CIOs<br />
that are planning to upskill their existing<br />
workforce on digital skills?<br />
A quick Google search displays several<br />
courses offered by premiere institutions<br />
such as Indian School of Business (ISB),<br />
and online courses by platforms, such as<br />
Udemy, Coursera, edX among others. Simplilearn,<br />
a professional online certification provider,<br />
recently launched Digital Transformation Academy<br />
– a complete suite of courses tailored for<br />
enterprise needs.<br />
We spoke to Anand Narayanan, Chief Product<br />
Officer at Simplilearn, to find out how the Academy<br />
aims to bridge the digital skill gap.<br />
Digital Transformation is a very<br />
broad concept. How do you define it<br />
at Simplilearn?<br />
We believe that, to successfully drive Digital<br />
Transformation, any organization needs to pay<br />
attention to three foundational aspects: People,<br />
Process, and Technology. The people aspect<br />
includes the process of transforming the mindset<br />
of an organization and creating an innovation<br />
driven culture from the grounds up. Process<br />
involves the ability to be “agile” and always follow<br />
“devops” principles. And finally technology allows<br />
an organization to change the way business is<br />
performed. Digital transformation isn’t just about<br />
technology but is also about the people that drive it<br />
and the processes that foster innovations.<br />
Can you talk about the skill gap<br />
issue in enterprise IT?<br />
Digital transformation is already disrupting traditional<br />
technologies, replacing them with digital<br />
domains, such as AI & Machine Learning,<br />
Analytics, Cloud, and Robotic Process Automation.<br />
It is also clear that these skills are not<br />
easily acquired due to their rapid evolution.To<br />
remain competitive and efficient, organizations<br />
have tried hiring for these skills, but the talent<br />
<strong>May</strong> <strong>2018</strong> | CIO&LEADER<br />
9
Interview<br />
Anand Narayanan, Simplilearn<br />
The Academy has<br />
a suite of training<br />
programs that<br />
help organizations<br />
become competent<br />
in digital<br />
technologies<br />
pool remains small. This leads to a skill gap that can only<br />
be overcome with a strong upskilling program.<br />
We conducted a survey of IT Managers<br />
recently and found that only less than half<br />
of them have completed any kind of certification<br />
in the last two years. Every three out of four of<br />
the respondents said they have done some kind<br />
of certification in the last five years. Why do you<br />
think CIOs/IT managers will be interested in taking<br />
up what you have to offer?<br />
Enterprises, more than ever, are measuring the ROI of their<br />
employees and realizing that they are falling behind on key<br />
skills in the digital domain. Online learning does not drive<br />
user engagement and the completion rates are abysmal as<br />
a result. The Simplilearn learning approach drives user<br />
engagement and skill achievement through a high-engagement,<br />
outcome centric model. Online self learning content,<br />
skills assessments, live classes with industry grade faculty,<br />
teaching assistants to intervene when required and hands<br />
on projects, have helped us to deliver an industry high 72%<br />
completion rate on our curriculum. Being able to achieve the<br />
learning outcomes and truly transform their organization is<br />
what makes our offer exciting to these CIOs/IT managers.<br />
Another survey finding that we encountered<br />
was that 28% of IT Managers said they<br />
would go for learning new technologies; however,<br />
leadership skills still topped the choice list.<br />
Clearly leadership skills are a CIO's top priority<br />
and they would rather spend dollars on hiring<br />
temporary skills. Then why would CIOs reskill at<br />
all or do you feel differently about this?<br />
In recent focus groups and discussions that Simplilearn<br />
has had with CIOs and L&D heads, it was clear that<br />
while the target group thought that leadership skills<br />
were important, a majority of their budgets were going<br />
towards technology training. IT Managers and CIOs<br />
are realizing that there is a significant technology shift<br />
happening in the industry with the mainstream use of<br />
digital technologies and this is clear from the way their<br />
training budgets are being allocated.<br />
While there has been intermittent use of a transient<br />
workforce, this approach has not delivered a culturally<br />
aligned outcome for these corporations. This transient<br />
workforce solves for the technology aspect, but it fails<br />
to deliver on the people and process aspects due to poor<br />
alignment of outcomes. It has become an imperative for<br />
corporations to upskill their employees or risk being left<br />
behind as a result.<br />
What's the vision and mission of the Simplilearn<br />
Digital Transformation Academy for<br />
enterprises?<br />
The Simplilearn Digital Transformation Academy is our<br />
flagship initiative to enable enterprises become digital ready.<br />
We are partnering with organizations to equip them with the<br />
skills needed to survive the digital era. The Academy has a<br />
suite of training programs that help organizations become<br />
competent in digital technologies. The program covers all<br />
knowledge aspects of the people, processes and technology<br />
framework and allows any organization to quickly move up<br />
the digital transformation capability ladder.<br />
What is the broad breakup of the course<br />
module?<br />
The Simplilearn Digital Transformation Academy covers<br />
varied topics across the people, process and technology<br />
aspects. On the people side, the academy provides<br />
training around design thinking, and UX principles<br />
which can lead to a more innovative, customer centric<br />
approach within an organization.<br />
On the process side, the academy covers core topics<br />
such as Agile and DevOps which allow an organization to<br />
run lean and fast. And on the technology side core digital<br />
disciplines are covered such as AI and machine learning,<br />
robotic process automation, big data, data analytics, digital<br />
marketing, and cloud computing.<br />
Our outcome centric curriculum is a blend of online selflearning<br />
and live instructor led classroom, allowing the<br />
learner to learn from anywhere. The courses are designed<br />
for three levels of training - Practitioner, Consultant, and<br />
CXO, and are based on the depth of knowledge and digital<br />
expertise required for various roles. Additionally the<br />
academy provides the capability to customize the curriculum<br />
for specific verticals<br />
10 CIO&LEADER | <strong>May</strong> <strong>2018</strong>
A PEER-POWERED,<br />
KNOWLEDGE - BASED AND<br />
COMMUNITY-LED INITIATIVE<br />
FOR CFOS
Cover Story<br />
12 CIO&LEADER | <strong>May</strong> <strong>2018</strong>
Cover Story<br />
Why the<br />
new policy<br />
matters…<br />
Despite a narrower positioning by Department<br />
of Telecommunications, the new digital communication<br />
policy is a statement of intent to<br />
improve the digital environment holistically<br />
By CIO&Leader<br />
On 1 <strong>May</strong> <strong>2018</strong>, the Department<br />
of Telecommunications (DoT)<br />
released the draft, National<br />
Digital Communication Policy<br />
<strong>2018</strong> for public consultation. The<br />
latest national communication policy is the fifth<br />
overall communication policy document from<br />
the government. For long, communication in the<br />
country was governed by the Indian Telegraph<br />
Act 1885. It took 109 years to get the first national<br />
telecom policy of India, in 1994. Since then, this is<br />
the third policy statement, the other two having<br />
been released in 1999 and 2012.<br />
The significant ways in which it differs from<br />
the other three in recent times (1994, 1999 and<br />
2012 versions) is that while all of them were called<br />
National Telecom Policy, the current draft replaces<br />
‘telecom’ with broader and more contemporary<br />
‘communication’, while ‘digital’ has been inserted.<br />
The policy is available on the DoT website<br />
and is open for public comments, at the time of<br />
writing this.<br />
According to the policy document, the policy<br />
aims to accomplish the following strategic objectives<br />
by 2022:<br />
1. Provisioning of broadband for all<br />
2. Creating 4 million additional jobs in the Digital<br />
Communications sector<br />
3. Enhancing the contribution of the Digital<br />
Communications sector to 8% of India’s GDP<br />
from ~ 6% in 2017<br />
4. Propelling India to the top 50 nations in the ICT<br />
Development Index of ITU from 134 in 2017<br />
5. Enhancing India’s contribution to global<br />
value chains<br />
6. Ensuring digital sovereignty<br />
While the first five objectives have traditionally<br />
guided policymaking in all sectors, the last two—<br />
that deal with India’s position in the world—are<br />
new additions to this policy statement.<br />
Beyond Telecom<br />
When we asked about the policy to CIOs and some<br />
senior IT managers, few had any knowledge about<br />
<strong>May</strong> <strong>2018</strong> | CIO&LEADER<br />
13
Cover Story<br />
By its content, specific<br />
goals and possible<br />
implications, the policy<br />
goes well beyond<br />
telecom sector. Yet, both<br />
its stated objective and<br />
the channel through<br />
which it was released<br />
(the administrative<br />
department DoT rather<br />
than a NITI Aayog or<br />
PMO), tends to indicate it<br />
is a sectoral policy.<br />
what it contains, other than the fact that such a policy has<br />
been announced. The only respondent who seemed to be<br />
familiar with the policy was from the telecom industry!<br />
While we are not defending the lack of awareness by the<br />
IT managers’ community, part of the blame should go to the<br />
government. Despite being fairly holistic, it has been positioned<br />
as just the latest ‘telecom’ policy.<br />
By its content, specific goals and possible implications,<br />
the policy goes well beyond telecom sector. Yet, both its<br />
stated objectives—enable creation of a vibrant competitive<br />
telecom market to strengthen India’s long-term competitiveness—and<br />
the channel through which it was released<br />
(the administrative department DoT rather than a NITI<br />
Aayog or PMO), tends to indicate that it is a sectoral policy.<br />
Take for ex<strong>amp</strong>le, the specific goal, ‘establish a strong,<br />
robust and flexible’ data protection regime, on which the<br />
Government has already acted by establishing a committee<br />
headed by Justice B.N Srikrishna.<br />
What is ‘telecom’ about it?<br />
There are three mission statements mentioned in the<br />
policy—Connect India (creating robust infrastructure),<br />
Propel India (promoting innovation and tech ecosystem<br />
and leverage emerging technologies) and Secure India<br />
(ensuring privacy, security and digital sovereignty). Only<br />
the first part is a logical sequel to previous telecom policies<br />
in its scope. The rest two are completely new additions.<br />
In that sense, it is a digitech policy, rather than a telecom<br />
policy.<br />
Not too surprisingly, one of the areas for which the<br />
provisions have direct implications, is enterprise IT,<br />
including information security.<br />
While almost the entire policy has implications for IT, there<br />
are several provisions and objectives that will have direct<br />
impact on enterprise IT operations (including information<br />
security). We have identified 18 such specific points from the<br />
draft policy text. You are advised to go through the entire policy<br />
at the DoT’s website though by the time the issue reaches you,<br />
the time for registering your comments would have elapsed.<br />
Here are the 18 points we strongly suggest you need to<br />
go through, and take them as inputs while working out<br />
your long-term plans. Most of them have positive implications<br />
but nevertheless, if you miss them, in a highly competitive<br />
market, you may just incur an opportunity cost!<br />
We have indicated the specific clause in the policy within<br />
parentheses () against each of the points. This will help you<br />
locate them within policy text easily in case you need to<br />
understand the context, know specific actions points, etc.<br />
Here we go…<br />
1<br />
Ensuring inclusion of uncovered<br />
areas and digitally deprived segments<br />
of society (1.4)<br />
Possible impact: Expansion of access today means<br />
expansion of the market. For many products and services,<br />
this will give access to new market segments, some of<br />
which are at the ‘bottom of the pyramid’. That itself may<br />
foster further innovation!<br />
This is also the only point from the first section of the<br />
policy (Connect India) that finds a place in this listing.<br />
2<br />
Deployment and adoption of new<br />
and emerging technologies (2.2.a)<br />
The policy talks about creating a roadmap for emerging<br />
technologies, such as 5G, Artificial Intelligence, Robotics,<br />
Internet of Things, Cloud Computing and M2M by simplifying<br />
licensing and regulatory frameworks whilst ensuring<br />
appropriate security frameworks for IoT/ M2M.<br />
It also explicitly mentions another emerging challenge—earmarking<br />
adequate licensed and unlicensed<br />
spectrum for IoT/M2M service.<br />
Encouraging use of Open APIs for emerging technologies<br />
is another progressive stance that the policy envisages.<br />
Possible impact: Today, most of the experimentations<br />
with new technologies like IoT and M2M do not scale up<br />
because businesses are unwilling to take the investment<br />
risks, because the regulatory directions in a lot of issues<br />
including spectrum availability are still unknown. A proactive<br />
policy stance like this will open up investments and<br />
accelerate the deployment of new technologies.<br />
14 CIO&LEADER | <strong>May</strong> <strong>2018</strong>
Cover Story<br />
The Policy at a Glance<br />
Vision<br />
To fulfil the information and communication needs of citizens and enterprises by establishment of a ubiquitous,<br />
resilient, secure and affordable Digital Communications Infrastructure and Services; and in the process,<br />
support India’s transition to a digitally empowered economy and society<br />
Mission Description Objective 2022 Goals<br />
Points in<br />
our Story<br />
pertaining<br />
to the<br />
mission<br />
Connect<br />
India<br />
Creating Robust<br />
Digital Communications<br />
Infrastructure<br />
To promote Broadband<br />
for All as a tool for<br />
socio-economic development,<br />
while ensuring<br />
service quality and<br />
environmental sustainability<br />
a. Provide Universal broadband coverage at 50 Mbps to<br />
every citizen<br />
b. Provide 1 Gbps connectivity to all Gram Panchayats of<br />
India by 2020 and 10 Gbps by 2022<br />
c. Enable 100 Mbps broadband on demand to all key development<br />
institutions; including all educational institutions<br />
d. Enable fixed line broadband access to 50% of households<br />
e. Achieve ‘unique mobile subscriber density’ of 55 by 2020<br />
and 65 by 2022<br />
f. Enable deployment of public Wi-Fi Hotspots; to reach 5<br />
million by 2020 and 10 million by 2022<br />
g. Ensure connectivity to all uncovered areas<br />
a. Attract investments of USD 100 Billion in the Digital<br />
Communications Sector<br />
b. Increase India’s contribution to Global Value Chains<br />
c. Creation of innovation led Start-ups in Digital Communications<br />
sector<br />
d. Creation of Globally recognized IPRs in India<br />
e. Development of Standard Essential Patents (SEPs) in the<br />
field of digital communication technologies<br />
f. Train/ Re-skill 1 Million manpower for building New Age<br />
Skills<br />
g. Expand IoT ecosystem to 5 Billion connected devices<br />
h. Accelerate transition to Industry 4.0<br />
a. Establish a comprehensive data protection regime for<br />
digital communications that safeguards the privacy,<br />
autonomy and choice of individuals and facilitates India’s<br />
effective participation in the global digital economy<br />
b. Ensure that net neutrality principles are upheld and<br />
aligned with service requirements, bandwidth availability<br />
and network capabilities including next generation access<br />
technologies<br />
c. Develop and deploy robust digital communication network<br />
security frameworks<br />
d. Build capacity for security testing and establish appropriate<br />
security standards<br />
e. Address security issues relating to encryption and security<br />
clearances<br />
f. Enforce accountability through appropriate institutional<br />
mechanisms to assure citizens of safe and secure digital<br />
communications infrastructure and services<br />
#1<br />
Propel<br />
India<br />
Enabling Next<br />
Generation Technologies<br />
and<br />
Services through<br />
Investments,<br />
Innovation and<br />
IPR generation<br />
To harness the power of<br />
emerging digital technologies,<br />
including 5G,<br />
AI, IoT, Cloud and Big<br />
Data to enable provision<br />
of future ready products<br />
and services; and<br />
to catalyse the fourth<br />
industrial revolution<br />
(Industry 4.0) by promoting<br />
Investments,<br />
Innovation and IPR<br />
#2 through<br />
#9<br />
Secure<br />
India<br />
Ensuring Sovereignty,<br />
Safety and<br />
Security of Digital<br />
Communications<br />
To secure the interests<br />
of citizens and safeguard<br />
the digital sovereignty<br />
of India with a<br />
focus on ensuring individual<br />
autonomy and<br />
choice, data ownership,<br />
privacy and security;<br />
while recognizing data<br />
as a crucial economic<br />
resource.<br />
#10 through<br />
#18<br />
<strong>May</strong> <strong>2018</strong> | CIO&LEADER<br />
15
Cover Story<br />
3<br />
Transition to IPv6 for all existing<br />
communications systems,<br />
equipment, networks and devices (2.2.c)<br />
Possible impact: For network managers, especially those<br />
managing large and complex networks, everything changes.<br />
4<br />
Enabling hi-speed Internet, IoT and<br />
M2M by 5G rollout (2.2.d)<br />
Possible impact: As sensor technologies become mainstream,<br />
the demand for speed will go up exponentially. And<br />
most of that speed has to be on wireless networks. So, 5G is<br />
a natural evolution. Just that a proactive stance like a policy<br />
statement makes the evolution a bit faster and seamless.<br />
5<br />
Establishing India as a global hub<br />
for cloud computing, content hosting<br />
and delivery, and data communication<br />
systems and services (2.2.f)<br />
The policy promises regulatory frameworks for promoting<br />
international data centers, content delivery networks<br />
and independent in exchanges in India, while promising<br />
a light-touch regulation.<br />
Possible impact: Lower latency, drop in prices and<br />
more choice<br />
6<br />
Leveraging AI and Big Data to<br />
enhance the overall quality of<br />
service, spectrum management, network<br />
security and reliability (2.2.g)<br />
Possible impact: Though it is targeted at the telecom sector,<br />
a large and mature sector like telecom can drive down<br />
the price as well as help grow skills.<br />
7<br />
Recognizing Digital Communications<br />
as the core of Smart Cities (2.2.h)<br />
The policy proposes developing, in collaboration with<br />
Ministry of Urban Development (MOUD), a Common Service<br />
Framework and Standards for Smart Cities. There are<br />
similar initiatives globally. The government needs to evaluate<br />
whether it makes sense to adapt one of these to India or<br />
start working on it from scratch, though.<br />
Possible impact: Accelerated smart city rollout will<br />
directly impact the volume of sales of many technologies<br />
like IoT/M2M, Big Data, leading to more use cases, availability<br />
of skills and lower cost of these technologies.<br />
8<br />
Promoting Start-ups (2.4)<br />
One of the important objectives and 2022 goals is<br />
supporting start-ups through various fiscal and nonfiscal<br />
benefits, such as academic collaboration, promoting<br />
start-ups in government procurements, measures for<br />
application service providers.<br />
Possible impact: A vibrant start-up environment<br />
leads to better innovation and flexibility of deploying<br />
technologies for enterprises.<br />
9<br />
Accelerating Industry 4.0 (2.8)<br />
The policy lists, among its objectives, creation of a<br />
roadmap for transition to Industry 4.0 by 2020 taking<br />
a sectoral approach. It explicitly mentions development<br />
of markets for IoT/ M2M connectivity services in sectors<br />
including agriculture and smart cities components. It<br />
also talks of establishing a multi-stakeholder led collaborative<br />
mechanism for this purpose.<br />
Possible impact: Faster deployment of robotics, IoT<br />
and other similar technologies leading to not just huge<br />
efficiency gains but also better decision making through<br />
data analytics.<br />
10<br />
Today, most of the<br />
experimentations with<br />
new technologies like IoT<br />
and M2M do not scale<br />
up because businesses<br />
are unwilling to take the<br />
investment risks, thanks<br />
to unclear regulatory<br />
direction. A proactive<br />
policy stance will open<br />
up investments and<br />
accelerate the deployment<br />
of new technologies.<br />
Establish a strong, flexible and<br />
robust Data Protection Regime<br />
(3.1)<br />
While the Government has already taken measures on<br />
this regard, like the appointment of an expert committee<br />
under the chairmanship of Justice Srikrishna, which has<br />
already issued a draft stance document and has taken<br />
feedback from public, it is probably incorporated in the<br />
communication policy document to show its importance<br />
in the overall policy making.<br />
Possible impact: This has major implications for enter-<br />
16 CIO&LEADER | <strong>May</strong> <strong>2018</strong>
Cover Story<br />
prise IT and compliance teams. Compliance with newer<br />
provisions like right to forget may need significant efforts<br />
including investment.<br />
11<br />
Assure Security of Digital<br />
Communications (3.3.a)<br />
The policy talks of infrastructure security (physical<br />
infrastructure, cyber-physical infrastructure, hardware<br />
and network elements), systems security (equipment,<br />
devices, distributed systems, virtual servers) as well as<br />
application and platform security (web, mobile, device<br />
and software security).<br />
Possible impact: One more layer of security at the service<br />
provider level is good news for enterprises, especially<br />
small and medium businesses.<br />
12<br />
Participating in global standard<br />
setting organisations (3.3.c)<br />
The policy talks about establishing comprehensive security<br />
certification regime based on global standards<br />
Possible impact: It was a long-desired requirement. A<br />
country of over a billion people should have a say in what<br />
direction the standards should go.<br />
13<br />
While the Government<br />
has already taken<br />
measures on data<br />
protection legislation,<br />
its incorporation in<br />
the communication<br />
policy document shows<br />
the importance it is<br />
accorded in the overall<br />
policy making.<br />
Formulating a policy on<br />
encryption and data retention<br />
(3.3.e)<br />
This is a hotly debated issue globally. While the government<br />
has made a mention of it in the policy, its exact<br />
stance is not known.<br />
Possible impact: A policy with clear guidelines is<br />
always better than a vague and ad-hoc approach. But keep<br />
your fingers crossed.<br />
14<br />
Facilitating lawful interception<br />
agencies with state-of-art lawful<br />
intercepts (3.3.f.ii)<br />
Mentioned as a sub-point of a clause, this one is tricky. The challenge<br />
is not technology always, though it is also becoming one.<br />
It is how robust is the process and what real powers do the service<br />
providers enjoy to say no to a request that is not mandated<br />
by policy bought sought by the enforcement agencies.<br />
Possible impact: Depends on how the policy making<br />
proceeds, it may make things easier or far more difficult.<br />
15<br />
Establishing a Security Incident<br />
Management and Response System<br />
for communications (3.3.g)<br />
Since communication industry is the basic foundation of<br />
a digital ecosystem, it has to be made thoroughly secure.<br />
Instituting a sectoral CERT that works in tandem with<br />
CERT-in is a welcome step.<br />
Possible impact: More secure infrastructure; also lessons<br />
for other sectors<br />
16<br />
Enforcing obligations on service<br />
providers to report data breaches<br />
(3.3.g.iii)<br />
Part of the requirements is to report data breaches, not just<br />
to authorities but also to affected users. The breach of data<br />
at a major telco in India reported in media sometimes back<br />
was a major cause of concern.<br />
Possible impact: A lot but we have to see how much<br />
teeth the legislation will have.<br />
17<br />
Developing a comprehensive plan<br />
for network preparedness<br />
Targeted at improving network resilience and disaster<br />
response, this will surely help all those who depend on<br />
these networks; i.e., all of us.<br />
Possible impact: More resilient infrastructure is good<br />
news for all users, be it business users or common citizens.<br />
18<br />
Developing a Unified Emergency<br />
Response mechanism<br />
In a natural disaster-prone country like India, creating a permanent<br />
mechanism for emergency response is a welcome step.<br />
While many a times it happens because of alert officials, the<br />
approach is always ad-hoc. An institutional framework with<br />
clearly defined roles and responsibilities, standard operating<br />
procedures and technical guidelines will surely go a long way<br />
in making disaster response far more effective.<br />
One welcome approach is to force service providers<br />
share infrastructure in emergency situations.<br />
Possible impact: Many of the other disaster management<br />
mechanisms can be effective if the basic connectivity<br />
is available<br />
<strong>May</strong> <strong>2018</strong> | CIO&LEADER<br />
17
COLUMN<br />
How to build better<br />
data protection and<br />
steering clear of<br />
GDPR violations<br />
Enforcement means that organizations should already be<br />
processing personal data in accordance with the GDPR —<br />
including provisions for data subject rights<br />
By Nilesh Jain<br />
T<br />
he General Data Protection Regulation (GDPR),<br />
adopted in April 2016 after four years of<br />
deliberations, is now in force. The regulation<br />
made headlines around the globe with its stricter<br />
data protection standards, substantial fines, and<br />
most of all, extensive reach. The GDPR affects any<br />
organization that holds an EU citizen’s personal<br />
data, no matter the size or location. A company<br />
based in Asia is as accountable as a multinational<br />
enterprise with offices across Europe — as long as<br />
it collects and processes the data of EU citizens.<br />
The regulation also delineated the data<br />
protection obligations of affected organizations<br />
— from adopting state-of-the-art security<br />
methods to providing people more access to<br />
and control of their data. Recognizing the<br />
sweeping changes required for compliance,<br />
the EU authorities granted member states<br />
18 CIO&LEADER | <strong>May</strong> <strong>2018</strong>
Column<br />
and organizations two years to get ready and<br />
prepare. And today, the transition stage is over<br />
— the GDPR will now be enforced.<br />
What happens now?<br />
Enforcement means that organizations<br />
should already be processing personal data<br />
in accordance with the GDPR — including<br />
provisions for data subject rights. Data Protection<br />
Authorities (DPAs) of EU member states will also<br />
already be able to penalize organizations that are<br />
not compliant. Depending on the member state,<br />
it is possible that regulators will immediately<br />
take action to address any noncompliance.<br />
Some regulatory bodies, however, plan on being<br />
more lenient with businesses and organizations<br />
that have started but not yet completed their<br />
compliance efforts.<br />
What is the worst-case scenario? An<br />
organization is liable for damages caused by<br />
noncompliance and is subject to corresponding<br />
administrative fines. The heftiest fine is<br />
20,000,000 euros or up to 4% of annual<br />
turnover, whichever is higher.<br />
What is the best-case scenario? If an<br />
organization is fully compliant with the GDPR,<br />
or uses the regulation as a starting-off point<br />
and goes beyond the minimum standards, then<br />
there are significant advantages. Some benefits<br />
would be: Secured valuable information, more<br />
efficient operations with proper archiving and<br />
data management, and increased trust from<br />
customers and users.<br />
While the GDPR applies to personal data of<br />
EU citizens, the GDPR has sparked a change in<br />
privacy regulations across the world. The <strong>2018</strong><br />
enforcement allowed several countries to make<br />
their own legislative improvements — the UK<br />
and Australia are just two of a number of regions<br />
that have also updated their data protection laws.<br />
This only indicates that GDPR compliance is a<br />
good opportunity — not just for multinational<br />
enterprises but smaller organizations as well — to<br />
keep up with global advances in data privacy and<br />
state-of-the-art security.<br />
What should organizations be doing?<br />
Ideally, all the groundwork for compliance<br />
should have been finished by now, and items on<br />
the compliance checklist should have been ticked.<br />
Organizations should already be able to provide<br />
products or services that address their customers’<br />
rights as outlined in the GDPR. Those using<br />
third-party applications or suppliers should<br />
watch for updates concerning issues like the<br />
“right to be forgotten” and stricter user consent<br />
standards and make sure they are working<br />
properly. Several laws as well as software changes<br />
are also expected to be in effect starting today or<br />
in the coming months, and organizations should<br />
be ready for any necessary changes.<br />
For those not yet fully compliant, some member<br />
state DPAs have reassured companies “acting in<br />
An organization is liable for<br />
damages caused by noncompliance<br />
and is subject to<br />
corresponding admin fines<br />
good faith” or on the way to compliance that they<br />
will initially be treated with consideration. It’s<br />
crucial to document steps being taken as well as<br />
to prioritize addressing potential security risks.<br />
Ready or not, the road to GDPR compliance<br />
does not end on enforcement day — assessments<br />
and audits should be regular moving forward.<br />
Building better data protection<br />
The GDPR was enforced to set a new standard<br />
for data privacy and protection. One key<br />
element to this is building in privacy measures<br />
from the first stages of development — not<br />
patching up problems after they occur. As<br />
organizations create new products and<br />
applications post-implementation day, privacy<br />
by design must be kept in mind.<br />
Through its new rules and standards, the GDPR<br />
encourages organizations to rethink existing<br />
data management policies and invest in state-ofthe-art<br />
security for data protection. To reiterate,<br />
compliance efforts should be constant after GDPR<br />
implementation day; staying up to date with<br />
cybersecurity developments plays a major part.<br />
We created an infographic to demonstrate the<br />
path well-protected personal data takes — leaving<br />
the data subject’s hands and on to an organization<br />
for secure processing. It also shows what happens<br />
if something goes wrong and what happens if<br />
everything goes right.<br />
The author is Vice President – South East Asia and<br />
India, Trend Micro<br />
<strong>May</strong> <strong>2018</strong> | CIO&LEADER<br />
19
Column<br />
Understanding APIs<br />
for private cloud<br />
implementations<br />
Three tips to minimize the development hassles in<br />
your cloud hybridization journey...<br />
By Abhinav Asthana<br />
G<br />
iven the ecosystem complexities of hybrid cloud<br />
deployments, API management can be tough.<br />
While addressing Inspire Partner Conference<br />
in 2017, Microsoft CEO Satya Nadella made an<br />
interesting observation when he opined that in<br />
the fight between public and private cloud, it's<br />
the hybrid cloud that has emerged the winner.<br />
Nadella's statement gets validated when one<br />
views the rise of hybrid cloud as part of the overall<br />
cloud market. According to Markets and Markets,<br />
the global hybrid cloud market is forecast to be<br />
valued at USD 91.74 billion by 2021, growing by<br />
22.5% CAGR. Compare this with the overall cloud<br />
computing revenues of USD162 billion in 2020<br />
(growing from USD 67 billion in 2015).<br />
A highly sought after model by CIOs, hybrid<br />
cloud offers organizations a flexibility to use costeffective<br />
resources and innovative features from<br />
public cloud vendors as and when required while<br />
retaining the advantages of tight management<br />
controls that their private cloud deployments<br />
assure. The hybrid model, however, can be a<br />
challenge to the backend API developer who has<br />
to ensure that users can move from one model<br />
to another seamlessly without compromising<br />
on the organization’s security and compliance<br />
mandates. Let’s explore three API management<br />
good practices companies may follow to get the<br />
best out of their API programmes for hybrid<br />
cloud implementations.<br />
20 CIO&LEADER | <strong>May</strong> <strong>2018</strong>
Column<br />
Streamline the database access needs of<br />
individual components<br />
Generally, a hybrid cloud set-up presents a<br />
complex ecosystem of applications, business<br />
processes, and infrastructure components.<br />
Given this complex environment, when multiple<br />
components spread across business and<br />
application process flows are accessing database,<br />
it may impact performance of the whole system.<br />
In any case when components are moving into the<br />
cloud, performance gets affected further. An aspect<br />
to consider, here is the type of data–whether it is<br />
persistent or non-persistent.<br />
The API management exercise should therefore,<br />
begin with mapping the database access needs of<br />
various application components with the linked<br />
business processes, and application workflows<br />
besides the user access levels. Ensuring that the<br />
database access function is carried out by one or<br />
only a few components may be a good approach<br />
to follow. Creating controlled interface(s) for<br />
public cloud-components to access applications<br />
and data from your private cloud may also be<br />
deemed useful.<br />
Do not ignore security and support<br />
In a hybrid cloud set-up APIs work as the pipe that<br />
provides access to enterprise resources to users<br />
internal as well as external. Safeguarding sensitive<br />
business information is, therefore, an important<br />
task APIs must perform. A combination of security<br />
provisions including basic authentication via API<br />
keys, the advanced authorization model by using<br />
OAuth 2.0, and JSON Web Tokens (JWT) along with<br />
encryption may be considered a reasonable solution<br />
stack to secure API framework for a hybrid cloud<br />
implementation.<br />
In a hybrid cloud environment, requests<br />
continuously flow back and forth between<br />
public cloud and the data center or private cloud.<br />
Therefore, in addition to the standard functions<br />
of visibility, availability, and monitoring, your<br />
APIs, while acting as gatekeepers, also need<br />
to support features such as throttling. When<br />
designed with adequate provisioning for caching<br />
and fair-use as the guiding principle, throttling<br />
can help private cloud administrators achieve<br />
performance optimization while measuring<br />
resource requests on the business criticality<br />
parameters. Allowing developers to request<br />
access to a predefined data-set through a<br />
developer-portal can also build efficiency into<br />
support operations.<br />
In a hybrid cloud set-up<br />
APIs work as the pipe<br />
that provides access to<br />
enterprise resources to<br />
users internal as well<br />
as external<br />
Know your organization’s hybrid cloud<br />
priorities<br />
Hybrid cloud has various usage-driven models.<br />
Some organisations build strong data center<br />
capabilities and a private cloud relying on public<br />
cloud resources only for analytics especially<br />
when big data is involved. In fact, this method<br />
is similar to the model traditionally followed<br />
in third party business intelligence system<br />
deployments wherein data fetched from multiple<br />
enterprise source systems and ETL is fed into a<br />
data warehouse and then to a BI system. In this<br />
method, replace BI system with public cloud.<br />
The public cloud's access is thus limited to the<br />
EDW layer only. The enterprise systems are kept<br />
oblivious and out of reach for the public cloud.<br />
Another practice followed by organizations is<br />
limiting the scope of public cloud to spike-based<br />
provisioning while majority of provisioning<br />
being done by the private cloud. Popularly<br />
termed as cloud-bursting, the public cloud’s role<br />
is of augmentative nature only. Through this<br />
method, CIOs try to keep their risks and costs<br />
under control while ensuring uninterrupted<br />
performance at all times.<br />
Lastly, some organizations take a different<br />
view of public cloud adoption. By breaking down<br />
their applications into back-end and front-end<br />
components, the web-based front-end portions<br />
are moved to the public cloud while retaining the<br />
transaction data processing and analysis at the<br />
private cloud level only. An API developer should<br />
therefore thoroughly review the practices and<br />
risk-return priorities of the organization before<br />
creating a suitable API architecture.<br />
The author is CEO & Co-founder, Postman<br />
<strong>May</strong> <strong>2018</strong> | CIO&LEADER<br />
21
Column<br />
Five questions post<br />
Pichai’s impressive<br />
duplex demo…<br />
And why we must ask them now?<br />
By Shyamanuja Das<br />
22 CIO&LEADER | <strong>May</strong> <strong>2018</strong>
Column<br />
T<br />
how will it feel to<br />
be served by virtual<br />
beings? What<br />
impact could it<br />
make on the way<br />
societies work?<br />
raditionally, people have been trained to talk<br />
to technology. For some time now, research is<br />
directed towards making technology talk to<br />
human beings.<br />
Google CEO Sundar Pichai just showed what<br />
you could possibly see in near future – natural<br />
conversation by an automated assistant over<br />
phone to do specific tasks. He demonstrated<br />
recordings of calls made by Google Duplex,<br />
a new technology for conducting natural<br />
conversations, leaving those who watched it live<br />
thoroughly impressed.<br />
Google Duplex is a new technology for<br />
conducting natural conversations to carry<br />
out “real world” tasks over the phone. The<br />
technology is directed towards completing<br />
specific tasks, such as scheduling certain types<br />
of appointments.<br />
“For such tasks, the system makes the<br />
conversational experience as natural as possible,<br />
allowing people to speak normally, like they would<br />
to another person, without having to adapt to a<br />
machine,” Google said in a blog post.<br />
Here are five questions you could try<br />
answering—or<br />
questioning others. But<br />
please…see the demo<br />
once before trying out.<br />
1. Do you still have<br />
doubts on what is<br />
possible?<br />
Natural language<br />
processing has a long<br />
history—right from<br />
translating “spirit is<br />
willing, flesh is weak”<br />
in English to “vodka is good, meat is rotten” in<br />
Russian…A lot of what Pichai demonstrated on<br />
stage looked like what we have watched so far in<br />
sci-fi movies.<br />
While Pichai himself admitted it is a work in<br />
progress, does anyone have any doubt on the limits?<br />
2. Will the labor displacement happen sooner<br />
than you think?<br />
Unlike many other talks on how it could change<br />
human civilization, Pichai kept talking about how<br />
the technology can change business. And that is<br />
pretty clear. The question is not if, but when, will<br />
start replacing human beings at a scale that will<br />
impact employment—and economies of nations?<br />
For countries like India, celebrating their young<br />
population ‘resource’ in a service centric economy,<br />
what could it mean?<br />
3. How will ‘automated beings’ change society<br />
and culture?<br />
How will it feel to be served by virtual beings?<br />
What impact could it make on the way societies<br />
work? Will humans too be dehumanized?<br />
4. What if it is misused?<br />
Already, people have started discussing its<br />
wrongful application. With every new capability,<br />
a new set of alarming possibilities are presented.<br />
Duplex and its genre are no exception. Imagine<br />
what is possible…<br />
5. Is it time for some regulation?<br />
The ultimate question. Should it be regulated?<br />
(That is a no-brainer) Is it time to start the<br />
debate now? What should be regulated and with<br />
what objective(s)?<br />
<strong>May</strong> <strong>2018</strong> | CIO&LEADER<br />
23
Column<br />
Bringing IoT<br />
sensors to the farm<br />
The sensors we have today (whether video,<br />
hyperspectral or infrared) allow us to understand<br />
many of the conditions of plants in the field<br />
By Adam Drobot<br />
24 CIO&LEADER | <strong>May</strong> <strong>2018</strong>
Column<br />
It all depends on how<br />
the cost can be reduced<br />
enough to match the<br />
economics of farming<br />
There’s a common misconception that<br />
farms are simple places. While that’s<br />
never particularly been the case,<br />
modern agriculture is impressively<br />
complex and technologically<br />
sophisticated, and is becoming more<br />
so with the introduction of a wide<br />
array of sensors.<br />
The sensors we have today (whether<br />
video, hyperspectral or infrared)<br />
allow us to understand many of the<br />
conditions of plants in the field. The<br />
sensors can be based on different<br />
platforms, from satellites and high<br />
altitude aircraft to smaller drones<br />
that are flown and controlled locally,<br />
to permanent sensors mounted on<br />
structures that overlook the field.<br />
The data from these sensors is used<br />
to understand the spatially-resolved<br />
field conditions and how the crop<br />
is progressing. Interpreting sensor<br />
data and the spatial distribution can<br />
be used to determine how the field<br />
should be managed to achieve the<br />
best yields, and where and when to<br />
harvest the crops. In terms of plants,<br />
miniaturized integrated sensors that<br />
are low-cost and can be placed on<br />
individual plants is one direction we<br />
could see. It all depends on how the<br />
cost can be reduced enough to match<br />
the economics of farming.<br />
Also, if we talk of the key<br />
technological advancements that<br />
would allow for the creation of<br />
cheap, miniature sensors, we need to<br />
mention the use of basic components<br />
from consumer electronics where<br />
large markets drive economies of<br />
scale. The best ex<strong>amp</strong>les are cheap<br />
cameras that now cost a few dollars<br />
because of smartphone production<br />
volumes, accelerometers from<br />
MEMS technologies, and other<br />
developments that come from<br />
system-on-a-chip (SOC) design<br />
and manufacturing techniques.<br />
Satellites also play a huge role in<br />
assessing the condition of plants.<br />
Firstly, an increasing number of<br />
satellites use high resolution sensors<br />
– both optical and hyperspectral<br />
– to improve techniques for<br />
interpreting sounding data. There<br />
are also many more low Earth<br />
orbit (LOE) satellites, whose arrays<br />
provide much better coverage,<br />
both geographically and in field<br />
re-visit rates. The second role is as<br />
communications relays for ground<br />
sensors in sparsely-populated and<br />
under-resourced areas.<br />
Drones also have great potential –<br />
they’re just getting started. Because<br />
they can get right to where the<br />
action is, drones can be used to fly<br />
instruments that would not fit or<br />
work on satellites. An ex<strong>amp</strong>le is<br />
acoustic sensors used to identify<br />
pests and animals, data that’s not<br />
possible to gather from satellites. A<br />
drone can also pick up a soil or plant<br />
s<strong>amp</strong>le that a satellite cannot.<br />
The author is IEEE senior member<br />
and Chair of the IEEE Internet of<br />
Things Activities Board<br />
<strong>May</strong> <strong>2018</strong> | CIO&LEADER<br />
25
FACE OFF<br />
// SHOULD CIOs BE HIRED<br />
FROM BUSINESS?<br />
There are two kinds of organizations.<br />
One is where a user applies IT for<br />
business and the other where the user<br />
becomes the producer of IT products<br />
or services. In the case of former, the<br />
degree of business knowledge and<br />
technology knowledge is 70:30 whereas<br />
in the case of latter, the ratio of business<br />
acumen to technology is 40:60.<br />
Nevertheless, business knowledge is<br />
dominant in both the cases.<br />
Take for instance, in the<br />
manufacturing industry, IT is the<br />
tool to enable business processes<br />
and drive business targets. IT should<br />
align with business strategies and<br />
provide solutions to do business<br />
better and smarter.<br />
This thorough knowledge of<br />
business is only possible if the IT<br />
head is from the business side.<br />
Understanding organization culture,<br />
Quick View<br />
T G Dhandapani, says,<br />
thorough knowledge of business<br />
is only possible if IT head is hired<br />
from business<br />
user behavior, business<br />
requirements and<br />
effective solutioning<br />
for an IT deployment is<br />
possible if he/she is from<br />
business. Today it is not<br />
adequate if the CIO just<br />
responds to business<br />
requirements. He/she<br />
has to be at least six<br />
months ahead of his CXO<br />
peers when it comes to<br />
T G DHANDAPANI<br />
Advisor – Digital<br />
Transformation and<br />
Former Group CIO, TVS<br />
Motor and Sundaram<br />
Clayton Group<br />
planning and executing<br />
digital projects. He/she should be in a<br />
position to predict what they want six<br />
months later. Any requirements of<br />
a CXO that were required yesterday<br />
or they planned for solutions after<br />
they ask for isn't sufficient. They<br />
should be in a position to do shelf<br />
engineering and keep the solution<br />
ready before the business asks for it.<br />
CIOs, if from business can implement<br />
this successfully. Today IT is not<br />
confined to datacenters. The IT folk<br />
should rub shoulders with CXOs and<br />
dirty their palms in the shop floor.<br />
Vanilla CIOs, purely with technology<br />
backgrounds, will take more time to<br />
understand and implement solutions<br />
for business<br />
Understanding<br />
org culture,<br />
user behavior,<br />
biz requirements<br />
is only<br />
possible if he/<br />
she is from<br />
business<br />
26 CIO&LEADER | <strong>May</strong> <strong>2018</strong>
Face Off<br />
ARINDAM<br />
SINGHA ROY<br />
CIO,<br />
East India Udyog<br />
"A CIO should<br />
come from<br />
the heart<br />
of the IT<br />
community<br />
but must be<br />
business<br />
focused<br />
Any CXO position is a combination<br />
of expertise and added layers of<br />
“big picture thinking” ability and<br />
leadership. A CIO/CISO without a<br />
strong IT background is a COO, or<br />
a CEO maybe. The balanced C-level<br />
team requires various perspectives.<br />
For instance, possessing a technical<br />
perspective for a CIO/CISO is paramount.<br />
He/she should be able to<br />
articulate the IT position and vision.<br />
Strategic and business thinking<br />
is one side of the coin for a CIO/<br />
CISO. However, in IT, he/she will<br />
serve as a ‘building with roof’ but<br />
without an IT base.<br />
If you hire a CIO/CISO without<br />
the requisite technical experience in<br />
critical and multi-headed responsibilities,<br />
IT is then managed by someone<br />
who isn't technology oriented,<br />
who then proves ineffective, open<br />
to vendor manipulation, and staff<br />
disrespect. He/she steadily starts<br />
acquiring a ‘herding cats' mentality<br />
on technology matters.<br />
I think what makes it complicated<br />
is the fact that IT is the only department<br />
that is both staff and line. For<br />
Quick View<br />
Arindam Singha Roy, says,<br />
IT experience is , sometimes,<br />
just enough<br />
instance, Finance is staff only while<br />
Sales is line only. But, the leader of IT<br />
is both a staff person (support) and<br />
often a line person (e.g. runs the bit<br />
factory). It is because of this unique<br />
role that he or she needs dual experience.<br />
The CIO/ needs to know what<br />
is right and wrong on projects, what<br />
works and doesn’t. In the end, it is the<br />
CIO that has to buy off on the recommendations<br />
of their reports.<br />
In conclusion, a CIO must come from<br />
the heart of the IT community, but must<br />
be business focused<br />
<strong>May</strong> <strong>2018</strong> | CIO&LEADER<br />
27
SECURITY<br />
Information<br />
sharing is key<br />
to ward off<br />
cyber threats<br />
As per reports, a layered security<br />
approach involves gathering various<br />
security solutions to collectively<br />
protect an organization’s data<br />
By CIO&Leader<br />
S<br />
haring information is an important factor in<br />
helping to defend against cyber threats, according<br />
to Akamai Technologies’ State of the Internet/Security:<br />
Carrier Insights Report for Spring<br />
<strong>2018</strong>. The report analyzes data from more than<br />
14 trillion DNS queries collected by Akamai<br />
between September 2017 and February <strong>2018</strong><br />
from communications service provider (CSP)<br />
networks around the world.<br />
For more than 19 years, Nominum, acquired by<br />
Akamai in 2017, has leveraged in-depth DNS data<br />
to improve overall protection against sophisti-<br />
cated cyberattacks, such as distributed denial of<br />
service (DDoS), ransomware, trojans, and botnets.<br />
Akamai’s Carrier Insight Report builds upon the<br />
Nominum expertise and highlights the effectiveness<br />
of DNS-based security that is enriched with<br />
data coming from other security layers. This layered<br />
security approach involves gathering various<br />
security solutions to collectively protect an organization’s<br />
data.<br />
“Siloed understanding of attacks against individual<br />
systems isn’t enough for defenders to prepare<br />
for today’s complicated threat landscape,”<br />
28 CIO&LEADER | <strong>May</strong> <strong>2018</strong>
Insight<br />
said Yuriy Yuzifovich, Director of Data Science,<br />
Threat Intelligence, Akamai. “Communicating<br />
with varying platforms is critical when acquiring<br />
knowledge across teams, systems and data sets.<br />
We believe that the DNS queries that our service<br />
provides act as a strategic component to arming<br />
security teams with the proper data necessary for<br />
that big picture view of the threat landscape.”<br />
Tackling the Mirai Botnet:<br />
Collaboration in Action<br />
Collaboration between teams within Akamai<br />
played a crucial role in discovering Mirai command<br />
and control (C&C) domains to make future<br />
Mirai detection more comprehensive. The Akamai<br />
Security Intelligence and Response Team (SIRT)<br />
has been following Mirai since its inception, using<br />
honeypots to detect Mirai communications and<br />
identify its C&C servers.<br />
In late January <strong>2018</strong>, Akamai’s SIRT and<br />
Nominum teams shared a list of over 500 suspicious<br />
Mirai C&C domains. The goal of this was<br />
to understand whether, if by using DNS data<br />
and artificial intelligence, this list of C&C could<br />
be augmented, and make future Mirai detection<br />
more comprehensive. Through several layers of<br />
analysis, the combined Akamai teams were able<br />
to augment the Mirai C&C dataset to discover a<br />
connection between Mirai botnets and distributors<br />
of the Petya ransomware.<br />
This collaborative analysis suggested an evolution<br />
of IoT botnets, from a nearly exclusive use<br />
case of launching DDoS attacks to more sophisticated<br />
activities such as ransomware distribution<br />
and crypto-mining. IoT botnets are difficult to<br />
detect because there are very few indicators of<br />
compromise for most users—and yet, the collaborative<br />
research by these teams created the<br />
Siloed understanding of<br />
attacks against individual<br />
systems isn't enough<br />
for defenders to prepare<br />
for today's complicated<br />
threat landscape<br />
chance to find and block dozens of new C&C<br />
domains to control the activity of the botnet.<br />
Javascript Cryptominers: A Shady<br />
Business Model<br />
The exponential rise in public consumption of<br />
cryptocurrency adoption has been reflected in<br />
a sharp, observable increase in the number of<br />
crypto-mining malware strains, and the number<br />
of devices infected with them.<br />
Akamai observed two distinct business models<br />
for large-scale crypto-mining. The first model<br />
uses infected devices’ processing power to mine<br />
cryptocurrency tokens. The second model uses<br />
code embedded into content sites that make<br />
devices that visit the site work for the cryptominer.<br />
Akamai conducted extensive analysis<br />
on this second business model, as it poses a new<br />
security challenge for users and website owners<br />
alike. After analyzing the cryptominer domains,<br />
Akamai was able to estimate the cost, in terms of<br />
both computer power and monetary gains, from<br />
this activity. An interesting implication of this<br />
research shows that cryptomining could become a<br />
viable alternative to ad revenue to fund websites.<br />
Changing Threats: Malware and<br />
Exploits Repurposed<br />
Cybersecurity is not a static industry. Researchers<br />
have observed hackers leveraging old techniques<br />
to reuse in today’s current digital landscape. Over<br />
the six months that Akamai collected this data, a<br />
few prominent malware c<strong>amp</strong>aigns and exploits<br />
show notable changes in their operating procedure,<br />
including:<br />
The Web Proxy Auto-Discovery (WPAD) protocol<br />
was discovered in use to expose Windows<br />
systems to Man-in-the-Middle attacks between<br />
November 24 and December 14, 2017. WPAD<br />
is meant to be used on protected networks (i.e.<br />
LANs) and leaves computers open to significant<br />
attacks when exposed to the Internet.<br />
Malware authors are branching out to the collection<br />
of social media logins in addition to financial<br />
information. Terdot, a branch of the Zeus botnet,<br />
creates a local proxy and enables attackers to perform<br />
cyber-espionage and promote fake news in<br />
the victim’s browser.<br />
The Lopai botnet is an ex<strong>amp</strong>le of how botnet<br />
authors are creating more flexible tools. This<br />
mobile malware mainly targets Android devices<br />
and uses a modular approach that allows owners<br />
to create updates with new capabilities.<br />
<strong>May</strong> <strong>2018</strong> | CIO&LEADER<br />
29
INSIGHT<br />
Mixing digital<br />
technologies<br />
A new World Economic Forum (WEF) research finds<br />
new technologies, deployed in combination, contribute<br />
to significantly higher productivity gains, when deployed<br />
individually. The research also identifies key enablers of<br />
maximizing return on digital investments<br />
By CIO&Leader<br />
he productivity increase due to investments in<br />
new digital technologies is significantly more<br />
when technologies are deployed in combination,<br />
finds a new research by the World Economic<br />
Forum (WEF). The finding is part of a broader<br />
project—Maximizing Returns on Digital Invest-<br />
Tments—by WEF’s Digital Transformation Initiative<br />
(DTI) to understand the relationship between<br />
new technology investment and productivity.<br />
The research found four key trends:<br />
The return on investment in new technologies<br />
is positive overall. The productivity increase<br />
is three times higher when technologies are<br />
deployed in combination.<br />
30 CIO&LEADER | <strong>May</strong> <strong>2018</strong>
Insight<br />
The return on digital investments varies by<br />
industry, and industry leaders achieve a greater<br />
productivity increase from investments in<br />
new technology than followers. The leaders in<br />
a majority of industries tend to be larger companies<br />
by revenue.<br />
Asset-heavy industries realize more value<br />
from robotics; asset-light industries realize<br />
greater value from mobile/social media.<br />
While industry leaders realize higher overall<br />
return from robotics and mobile/social investments,<br />
followers have gained more from IoT<br />
and cognitive technologies.<br />
The WEF research identified three key drivers<br />
of digital investments: new efficiencies, enhanced<br />
customer experience and new business models.<br />
It concluded that new efficiencies are still the<br />
primary driver for large companies to invest in<br />
new technologies while investing in new business<br />
models is the most difficult and least frequently<br />
targeted of the three drivers.<br />
To read our report on the key imperatives, drivers<br />
and major trends in digital transformation in India,<br />
read Decoding Digital Transformation in India<br />
The research also identified five key enablers<br />
to maximize the return on digital investments<br />
emerged from the discussions with industry<br />
leaders. They are:<br />
Agile and digital-savvy leadership: Maintaining<br />
a strategic vision, purpose, skills, intent and<br />
alignment across management levels to ensure a<br />
nimble decision-making process on innovation<br />
Forward-looking skills agenda: Infusing a<br />
digital mindset in the workforce by making innovation<br />
the focus of training and hiring programs<br />
Ecosystem thinking: Collaborating within the<br />
value chain (e.g. with suppliers, distributors, customers)<br />
and outside (e.g. start-ups, academia)<br />
Data access and management: Driving competitiveness<br />
through strong data infrastructure and<br />
warehouse capability combined with the right<br />
analytics and communication tools<br />
Technology infrastructure readiness: Building<br />
the required technology infrastructure to<br />
WEF research has<br />
identified three key<br />
drivers: new efficiencies,<br />
enhanced customer<br />
experience and new<br />
business models<br />
ensure strong capabilities on cloud, cybersecurity<br />
and interoperability<br />
The project was launched to address the understanding<br />
gap that exists in new technologies’<br />
impact on productivity.<br />
Some of the questions that it addressed are:<br />
How much value are companies getting from<br />
digital investments?<br />
How do returns on digital investments vary by<br />
company, industry and technology?<br />
How can companies maximize return from<br />
their digital investments?<br />
How can companies successfully execute on<br />
digital investment projects?<br />
The research considered four new technology<br />
areas: cognitive technologies including AI and Big<br />
Data; IoT/connected devices; Robotics encompassing<br />
design, construction, implementation and<br />
operation of robots; and Mobile/social media.<br />
The research combined quantitative and qualitative<br />
analyses of new technology investments.<br />
data from over 16,000 public companies across 14<br />
industries to estimate the productivity impact of<br />
investments in new technologies. The industries<br />
were automotive, aviation and travel, chemistry<br />
and advanced materials, consumer, electricity,<br />
financial services, healthcare, logistics, media,<br />
mining and metals, oil and gas, professional services,<br />
retail and telecommunications<br />
<strong>May</strong> <strong>2018</strong> | CIO&LEADER<br />
31
Insight<br />
CEOs priorities<br />
shifting to embrace<br />
digital business<br />
As per Gartner, growth, corporate strategies, IT and<br />
workforce issues continue to top CEO priorities in <strong>2018</strong><br />
By CIO&Leader<br />
Growth is amongst the top CEO business priorities<br />
in <strong>2018</strong> and 2019, according to a recent survey of<br />
CEOs and senior executives by Gartner. However,<br />
the survey revealed as simple, implemental<br />
growth becomes harder to achieve, CEOs<br />
are focusing on changing and upgrading the<br />
structure of their companies, including a deeper<br />
understanding of digital business.<br />
The Gartner <strong>2018</strong> CEO and Senior Business Executive<br />
Survey of 460 CEO and senior business executives<br />
in Q4, 2017 examined their business issues, as<br />
well as some areas of technology agenda impact. In<br />
total, 460 business leaders in organizations with<br />
more than USD 50 million in annual revenue were<br />
qualified and surveyed.<br />
IT remains a high priority coming in at the third<br />
position, and CEOs mention digital transformation,<br />
in particular (see Figure 1). Workforce has risen<br />
rapidly this year to become the fourth-biggest<br />
priority, up from seventh in 2017. The number of<br />
32 CIO&LEADER | <strong>May</strong> <strong>2018</strong>
Insight<br />
CEO Top Business Priorities for <strong>2018</strong> and 2019<br />
Percentage of respondents, ranked by summary top three mentions<br />
(Simple)<br />
Growth<br />
40%<br />
33%<br />
Corporate<br />
(Structural Development)<br />
31%<br />
IT Related<br />
28% 23%<br />
Financial<br />
15% 15%<br />
Workforce<br />
Customer<br />
Product<br />
Improvements<br />
13% 10%<br />
Management<br />
Sales<br />
Cost<br />
Management<br />
9%<br />
9%<br />
Efficiency<br />
and<br />
Productivity<br />
Degree of<br />
increase from<br />
previous year<br />
Degree of<br />
decrease from<br />
previous year<br />
Source: Gartner <strong>2018</strong><br />
CEOs mentioning workforce in their top three<br />
priorities rose from 16% to 28%. When asked about<br />
the most significant internal constraints to growth,<br />
employee and talent issues were at the top. CEOs<br />
said a lack of talent and workforce capability is the<br />
biggest inhibitor of digital business progress.<br />
CEOs recognize the need for<br />
cultural change<br />
Culture change is a key aspect of digital<br />
transformation. The <strong>2018</strong> Gartner CIO Survey found<br />
CIOs agreed it was a very high-priority concern,<br />
but only 37% of CEOs said a significant or deep<br />
culture change is needed by 2020. However, when<br />
companies that have a digital initiative underway<br />
are compared with those that don’t, the proportion<br />
in need of culture change rose to 42%.<br />
Digital business matters to CEOs<br />
Survey respondents were asked whether they<br />
have a management initiative or transformation<br />
program to make their business more digital. The<br />
majority (62%) said they did. Of those organizations,<br />
54% said that their digital business objective is<br />
transformational while 46% said the objective of the<br />
initiative is optimization.<br />
In the background, CEOs’ use of the word “digital”<br />
has been steadily rising. When asked to describe<br />
their top five business priorities, the number of<br />
CEOs in the survey<br />
believe that a lack of<br />
talent and workforce<br />
capability is the biggest<br />
inhibitor of digital<br />
business progress<br />
respondents mentioning the word digital at least once<br />
has risen from 2.1% in the 2012 survey to 13.4% in<br />
<strong>2018</strong>. This positive attitude toward digital business<br />
is backed up by CEOs’ continuing intent to invest in<br />
IT. 61% of respondents intend to increase spending<br />
on IT in <strong>2018</strong>, while 32% plan to make no changes to<br />
spending and only 7% foresee spending cuts.<br />
More CEOs see their companies as<br />
innovation pioneers<br />
The <strong>2018</strong> CEO survey showed that the percentage<br />
of respondents who think their company is an<br />
innovation pioneer has reached a high of 41%<br />
(up from 27% in 2013), with fast followers not far<br />
behind at 37%<br />
<strong>May</strong> <strong>2018</strong> | CIO&LEADER<br />
33
Insight<br />
Artificial intelligence<br />
sees big business<br />
As per Gartner, the growth will be 70% from 2017,<br />
totalling USD 1.2 trillion in <strong>2018</strong><br />
By CIO&Leader<br />
Global business value derived from artificial<br />
intelligence (AI) will total USD 1.2 trillion in <strong>2018</strong>,<br />
a rise of 70% from 2017, according to Gartner.<br />
AI-derived business value will reach USD 3.9<br />
trillion in 2022.<br />
The three different sources of AI business value are:<br />
Customer experience: The positive or negative<br />
effects on indirect cost. Customer experience is a<br />
necessary precondition for widespread adoption<br />
of AI technology to both unlock its full potential<br />
and enable value.<br />
New revenue: Increasing sales of existing products<br />
and services, and/or creating new product or<br />
service opportunity beyond the existing situation.<br />
Cost reduction: Reduced costs incurred in producing<br />
and delivering those new or existing<br />
products and services.<br />
“AI promises to be the most disruptive class of<br />
34 CIO&LEADER | <strong>May</strong> <strong>2018</strong>
Insight<br />
Forecast of Global AI-Derived Business Value (Billions of U.S. Dollars)<br />
2017 <strong>2018</strong> 2019 2020 2021 2022<br />
Business Value 692 1,175 1,901 2,649 3,346 3,923<br />
Growth (%) 70 62 39 26 17<br />
Source: Gartner (April <strong>2018</strong>)<br />
technologies during the next 10 years<br />
due to advances in computational<br />
power, volume, velocity and variety of<br />
data, as well as advances in deep neural<br />
networks (DNNs),” said John-David<br />
Lovelock, research vice president at<br />
Gartner. “One of the biggest aggregate<br />
sources for AI-enhanced products<br />
and services acquired by enterprises<br />
between 2017 and 2022 will be niche<br />
solutions that address one need very<br />
well. Business executives will drive<br />
investment in these products, sourced<br />
from thousands of narrowly focused,<br />
specialist suppliers with specific<br />
AI-enhanced applications.”<br />
As per Gartner, the AI business value<br />
growth rate will be 70%, but it will<br />
slow down through 2022 (see Table 1).<br />
“In the early years of AI, customer<br />
experience (CX) is the primary<br />
source of derived business value, as<br />
organizations see value in using AI<br />
techniques to improve every customer<br />
interaction, with the goal of increasing<br />
customer growth and retention. CX is<br />
followed closely by cost reduction, as<br />
organizations look for ways to use AI to<br />
increase process efficiency to improve<br />
decision making and automate more<br />
tasks,” said Lovelock. “However,<br />
in 2021, new revenue will become<br />
the dominant source, as companies<br />
uncover business value in using AI<br />
to increase sales of existing products<br />
and services, as well as to discover<br />
opportunities for new products and<br />
services. Thus, in the long run, the<br />
business value of AI will be about new<br />
revenue possibilities.”<br />
Breaking out the global business<br />
value derived by AI type, decision<br />
support/augmentation (such as DNNs)<br />
will represent 36% of the global<br />
AI-derived business value in <strong>2018</strong>. By<br />
2022, decision support/augmentation<br />
will have surpassed all other types of<br />
AI initiatives to account for 44% of<br />
global AI-derived business value.<br />
“DNNs allow organizations to<br />
perform data mining and pattern<br />
recognition across huge datasets<br />
not otherwise readily quantified<br />
or classified, creating tools that<br />
classify complex inputs that then<br />
feed traditional programming<br />
systems. This enables algorithms for<br />
decision support/augmentation to<br />
work directly with information that<br />
formerly required a human classifier,”<br />
said Lovelock. “Such capabilities<br />
have a huge impact on the ability of<br />
organizations to automate decision<br />
and interaction processes. This new<br />
level of automation reduces costs<br />
and risks, and enables, for ex<strong>amp</strong>le,<br />
increased revenue through better<br />
microtargeting, segmentation,<br />
marketing and selling.”<br />
Virtual agents allow corporate<br />
organizations to reduce labor costs<br />
as they take over simple requests<br />
and tasks from a call center, help<br />
desk and other service human<br />
agents, while handing over the more<br />
complex questions to their human<br />
counterparts. They can also provide<br />
uplift to revenue, as in the case of<br />
roboadvisors in financial services or<br />
upselling in call centers. As virtual<br />
employee assistants, virtual agents can<br />
help with calendaring, scheduling and<br />
other administrative tasks, freeing up<br />
employees’ time for higher value-add<br />
work and/or reducing the need for<br />
human assistants. Agents account<br />
for 46% of the global AI-derived<br />
business value in <strong>2018</strong> and 26% by<br />
2022, as other AI types mature and<br />
contribute to business value.<br />
Decision automation systems use<br />
AI to automate tasks or optimize<br />
business processes. They are<br />
particularly helpful in tasks such<br />
as translating voice to text and vice<br />
versa, processing handwritten<br />
forms or images, and classifying<br />
other rich data content not readily<br />
accessible to conventional systems.<br />
As unstructured data and ambiguity<br />
are the staple of the corporate<br />
world, decision automation — as it<br />
matures — will bring tremendous<br />
business value to organizations. For<br />
now, decision automation accounts<br />
for just 2% of the global AI-derived<br />
business value in <strong>2018</strong>, but it will<br />
grow to 16% by 2022.<br />
Smart products account for 18%<br />
of global AI-derived business value<br />
in <strong>2018</strong>, but will shrink to 14% by<br />
2022 as other DNN-based system<br />
types mature and overtake smart<br />
products in their contribution to<br />
business value. Smart products<br />
have AI embedded in them, usually<br />
in the form of cloud systems that<br />
can integrate data about the user's<br />
preferences from multiple systems<br />
and interactions. They learn about<br />
their users and their preferences<br />
to hyperpersonalize the experience<br />
and drive engagement<br />
<strong>May</strong> <strong>2018</strong> | CIO&LEADER<br />
35
Insight<br />
Facebook seeks a<br />
'friend' in blockchain;<br />
will it succeed?<br />
Facebook creates a dedicated team to explore blockchain<br />
potential and appoints Facebook Messenger head to lead<br />
the initiative<br />
By Shubhra Rishi<br />
ccording to news reports, Facebook executive David<br />
Marcus, who has been responsible for managing the<br />
company's standalone messaging app, Messenger,<br />
will head a new team dedicated to exploring the<br />
potential of blockchain technology. This team will<br />
comprise instagram executives including Insta-<br />
Agram's VP of Engineering, James Everingham and<br />
Instagram's VP of Product, Kevin Weil. Prior to joining<br />
Facebook, Marcus was CEO at PayPal.<br />
In lieu of the latest Cambridge Analytica controversy<br />
where the social network was in the line of<br />
fire for endangering data and privacy of its large<br />
user base, the company's move to explore blockchain<br />
has its pros and cons.<br />
36 CIO&LEADER | <strong>May</strong> <strong>2018</strong>
Insight<br />
The Pros<br />
Firstly, a blockchain-based social media platform<br />
will provide a high degree of privacy and<br />
security for its users. Users will have more control<br />
over their information and say Facebook,<br />
will no longer be responsible for managing<br />
this data. There are a number of blockchainbased<br />
platformes such as, Steemit, Numa, Sola,<br />
Indorse, which are experimenting with blockchains<br />
and cryptocurrencies.<br />
Take for instance, Numa, which is like Twitter<br />
– "but with cutting edge distributed technologies,<br />
so no central entity owns your data," it says<br />
on its homepage.<br />
On Numa, you can create an account, message,<br />
follow, or favorite a piece of information, and this<br />
data gets stored on a distributed file sharing protocol<br />
(IPFS). On Numa, all your data is stored in a<br />
public, distributed way, unlike on a central entity<br />
such as Facebook, which makes it impossible for<br />
any entity to revoke your access to your data.<br />
Steemit, on the other hand, is a decentralized<br />
reward platform (a social network built on the<br />
Steem blockchain) meant for publishers/users<br />
to monetize content and grow their community.<br />
Steemit users can earn token-based compensation<br />
(cryptocurrencies) for their posts, pictures, music,<br />
and videos. Steemit is powered by Ethereum, a<br />
decentralized platform that runs smart contracts<br />
or "applications that run exactly as programmed<br />
without any possibility of downtime, censorship,<br />
fraud or third-party interference."<br />
Akasha is another decentralized platform<br />
built by Mihai Alisie, founder of Ethereum and<br />
Bitcoin Magazine. The platform has an interface<br />
like Twitter, can be used to can publish, share<br />
and vote for entries, similar to Medium and<br />
other modern publishing platforms -- with a<br />
marked difference that your content is actually<br />
published over a decentralized network rather<br />
than on Akasha's servers. Subscribes on Akasha<br />
can up-vote your content, where votes are<br />
bundled with micro transactions.<br />
There are several other social media platforms,<br />
such as onG.social, Indorse, The Merkle, and<br />
Sapien, among others, built on blockchain. All<br />
A blockchainbased<br />
social<br />
media platform<br />
will provide a high<br />
degree of privacy<br />
and security for its<br />
users<br />
the above blockchain-based social media platforms<br />
offer use cases in the following areas:<br />
Data integrity and security<br />
Better content control<br />
Earn money in the form of crypto currencies<br />
Freedom of speech<br />
Cons<br />
However, there are also cons that might serve as<br />
barriers to the above advantages the technology has<br />
to offer in ‘regulating’ social media in a way:<br />
The problem of fake news<br />
Crypto currency is still not an accepted form of<br />
payment in many countries<br />
Blockchain technology is still not scalable<br />
With Facebook announcing a new team now, the<br />
ground work for exploring blockchain for future<br />
use, must have began a long time ago. Even if it is<br />
on damage-control mode, it is a step in the right<br />
direction – targeted at improving data integrity<br />
and security of its users’ information. Moreover, it<br />
will be interesting to observe how the blockchain<br />
will combat the above-mentioned cons, which<br />
stand in the way of success of any blockchainbased<br />
social network<br />
<strong>May</strong> <strong>2018</strong> | CIO&LEADER<br />
37
Insight<br />
The dirty secrets of<br />
network firewalls<br />
As per a network study, 61% would like to see better<br />
perimeter security in their organization’s network firewall<br />
along with better threat visibility and better protection<br />
By CIO&Leader<br />
38 CIO&LEADER | <strong>May</strong> <strong>2018</strong>
Insight<br />
M<br />
ajority of Indian IT managers have legal liabilities<br />
when it comes to unidentified traffic in their organizations,<br />
according to India findings of Sophos<br />
survey, The Dirty Secrets of Network Firewalls.<br />
In fact, nearly one in four globally cannot identify<br />
70% of their network traffic. The lack of visibility<br />
creates significant security challenges for today’s<br />
businesses and impacts effective network management.<br />
The survey polled more than 2,700 IT<br />
decision makers across mid-sized businesses in<br />
10 countries worldwide, including the US, Canada,<br />
Mexico, France, Germany, the UK, Australia,<br />
Japan, South Africa and India.<br />
Considering the debilitating impact cyberattacks<br />
can have on a business, it’s unsurprising<br />
that 90% of respondents agree that a lack of<br />
application visibility is a serious security concern.<br />
Without the ability to identify what’s running<br />
on their network, IT managers are blind to<br />
ransomware, unknown malware, data breaches<br />
and other advanced threats, as well as potentially<br />
malicious applications and rogue users. Network<br />
firewalls with signature-based detection are<br />
unable to provide adequate visibility into application<br />
traffic due to a variety of factors such as<br />
the increasing use of encryption, browser emulation,<br />
and advanced evasion techniques.<br />
“Controlling network traffic is an essential role<br />
of every firewall yet 61% IT managers can’t tell<br />
you how their bandwidth is being consumed,”<br />
said Sunil Sharma, Managing Director Sales at<br />
Sophos India & SAARC. “If you can’t see everything<br />
on your network, you can’t ever be confident<br />
that your organization is protected from threats.<br />
IT professionals have been ‘flying blind’ for too<br />
long and cybercriminals take advantage of this.”<br />
As per the survey, 61% would like to see better<br />
perimeter security in their organization’s network<br />
firewall along with better threat visibility<br />
and better protection.<br />
Network firewalls<br />
with signature-based<br />
detection are unable<br />
to provide adequate<br />
visibility into app<br />
traffic due to a<br />
number of factors<br />
<strong>May</strong> <strong>2018</strong> | CIO&LEADER<br />
39
Insight<br />
Organization’s firewall is the gateway between<br />
network and internet. Together with endpoint<br />
protection, it’s an integral pillar of security infrastructure.<br />
Despite the importance of its role in<br />
defenses, the survey revealed that firewalls are<br />
failing organizations when it comes to delivering<br />
the protection they need. On an average, Indian<br />
organizations face 26 infected machines a month;<br />
approximately 60% higher infected devices in<br />
comparison to the global average.<br />
“Ineffective firewalls are costing you time<br />
and money. On an average, organizations are<br />
spending 7 working days to remediate infected<br />
machines,” said Sharma.<br />
“A single network breach often leads to the compromise<br />
of multiple computers, so the faster you<br />
can stop the infection from spreading the more<br />
you limit the damage and time needed to clean it<br />
up,” Sharma further added. “Companies are looking<br />
for the kind of next-generation, integrated<br />
network and endpoint protection that can stop<br />
advanced threats and prevent an isolated incident<br />
from turning into a widespread outbreak. Sophisticated<br />
exploits, such as MimiKatz and Eternal-<br />
Blue reminded everyone that network protection<br />
is critical to endpoint security and vice versa.<br />
Only direct intelligence sharing between these<br />
two can reveal the true nature of who and what is<br />
operating on your network.”<br />
Sharma went onto explain that the findings highlighted<br />
the importance of ‘simplicity’ in all aspects of<br />
the security process; network, endpoint or server.<br />
“Reducing complexity is absolutely fundamental<br />
to ensuring data and device security; a fact reflected<br />
in the research. According to the data, 79% respondents<br />
have security risks from unwanted or unnecessary<br />
apps, and a further 60% are concerned by<br />
productivity loss due to unwanted ones. Unnecessary<br />
complexity compromises transparency for a<br />
network manager and the end user, and can lead to<br />
– not merely security concerns – but, even, liability<br />
and compliance issues. The concept of simplicity<br />
is central to Sophos, in the way our products are<br />
designed and in the counsel we provide. We believe<br />
that the simpler the security protocols are to implement,<br />
the more likely they are to be effective.”<br />
Organizations acknowledge the need for better<br />
protection, visibility and response. The survey<br />
revealed that 84% of IT managers polled want<br />
better protection from their current firewall. 99%<br />
want their firewall technology to automatically<br />
isolate infected computers, and 96% want endpoint<br />
and firewall protection from the same vendor if it<br />
improves detection rates and incident response.<br />
Security is Not the Only Risk to<br />
Businesses<br />
Following security risks, 60% organizations<br />
are concerned about loss of productivity from<br />
unproductive apps. Business productivity can be<br />
negatively impacted if IT is unable to prioritize<br />
bandwidth for critical applications.<br />
For industries that rely on custom software<br />
to meet specific business needs, an inability to<br />
prioritize these mission critical applications<br />
over less important traffic could be costly. 69%<br />
of IT professionals who had invested in custom<br />
applications admitted that their firewall could<br />
not identify the traffic and therefore were unable<br />
to maximize their return on investment. Lack of<br />
visibility also creates a blind spot for the potential<br />
transfer of illegal or inappropriate content<br />
on corporate networks, making companies vulnerable<br />
to litigation and compliance issues.<br />
“Organizations need a firewall that protects<br />
their investment in business-critical and custom<br />
applications by allowing employees to<br />
have prioritized access to the applications they<br />
need,” said Sharma. “Increasing network visibility<br />
requires a radically different approach.<br />
By enabling the firewall to receive information<br />
directly from the endpoint security, it can<br />
now positively identify all applications – even<br />
obscure or custom applications.”<br />
40 CIO&LEADER | <strong>May</strong> <strong>2018</strong>
ns'k dk lcls yksdfiz; vkSj fo‚luh; VsDuksykWth osclkbV<br />
fMftV vc fganh esa miyC/k gSaA u;h fganh osclkbV vkidks<br />
VsDuksykWth ls tqMs+ gj NksVh cM+h ?kVukvks ls voxr j[ksxhA lkFk<br />
esa u, fganh osclkbV ij vkidks fMftV VsLV ySc ls foLr`r xStsV<br />
fjO;q ls ysdj Vsd lq>ko feysaxsA fMftV tYn gh vkSj Hkh vU;<br />
Hkkjrh; Hkk"kkvks esa miyC/k gksxkA<br />
www.digit.in/hi<br />
www.facebook.com/digithindi