CIO&Leader_July 2017 (1)
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
EVENT REPORT<br />
Meet this year's 24 brightest<br />
security professionals Pg 08<br />
INTERVIEW<br />
Mandar Marulkar on the CDO Role<br />
Pg 38<br />
Volume 06<br />
Issue 04<br />
<strong>July</strong> <strong>2017</strong><br />
150<br />
TRACK TECHNOLOGY BUILD BUSINESS SHAPE SELF<br />
SPECIAL AWARDS COVERAGE ISSUE<br />
Featuring the finest moments from the two-day<br />
security conference and awards ceremony<br />
that felicitated India's future CSOs<br />
A 9.9 Media Publication
EDITORIAL<br />
Shyamanuja Das<br />
shyamanuja.das@9dot9.in<br />
Whither<br />
Security<br />
<strong>Leader</strong>ship?<br />
T<br />
Security is getting<br />
aligned more and<br />
more with the<br />
organizational<br />
risk management<br />
even though in<br />
some cases older<br />
structures have<br />
not changed<br />
he issue that you are holding in your<br />
hand carries the report on our recent security<br />
conference where, along with some<br />
really compelling content, we felicitated<br />
the winners of our NEXTCSO award winners.<br />
NEXTCSO, to the uninitiated, is our<br />
small contribution to identify and honor<br />
the security professionals who have it in<br />
them to become the next chief information<br />
security officers.<br />
As we present the highlights of the event<br />
in this issue, I would like to bring out a<br />
couple of observations during the event<br />
and while analyzing the data pertaining to<br />
demographic and professional profiles of<br />
the winners and other applicants.<br />
First, security is becoming more interesting.<br />
In the conference, speaker after<br />
speaker spoke about security threats,<br />
future challenges, and risks to business<br />
in a language and with ex<strong>amp</strong>les that all<br />
of us can relate to. There was very little of<br />
those highly technical schematic diagrams<br />
that were the mainstay of any security<br />
presentation earlier. The bad news is, if<br />
we can so closely identify with the threats,<br />
they are so much more real than they used<br />
to be—and for most of us.<br />
The second—not entirely isolated from the<br />
first—is the emergence of ‘leaders’ rather<br />
than techies or even managers who are now<br />
required to lead this war against the big,<br />
bad world of cyber criminals. It was quite<br />
evident from the data that I analyzed. There<br />
is little difference between the hard skills of<br />
the winners and the non-winners. The differences<br />
are all primarily about soft skills<br />
like innovation, entrepreneurial skills and<br />
people skills. That is a definite change.<br />
This time, I got a chance to get into deeper<br />
conversations with a lot more CISOs. That<br />
gave me a good idea of what is going on in<br />
their minds. While the space is too short<br />
to get into that, we will carry some of those<br />
videos in our website. One thing is clear<br />
–Security is getting aligned more and more<br />
with the organizational risk management<br />
even though in some cases older structures<br />
have not changed.<br />
More about that later—especially as we<br />
have done a survey around this very phenomenon.<br />
<strong>July</strong> <strong>2017</strong> | CIO&LEADER<br />
1
A 9.9 Media Publication<br />
EVENT REPORT<br />
Meet this year's 24 brightest<br />
security professionals Pg 08<br />
INTERVIEW Volume 06<br />
Issue 04<br />
Mandar Marulkar on the CDO Role<br />
<strong>July</strong> <strong>2017</strong><br />
Pg 38<br />
150<br />
TRACK TECHNOLOGY BUILD BUSINESS SHAPE SELF<br />
SPECIAL AWARDS COVERAGE ISSUE<br />
Featuring the finest moments from the two-day<br />
security conference and awards ceremony<br />
that felicitated India's future CSOs<br />
CONTENT<br />
JULY <strong>2017</strong><br />
EVENT REPORT<br />
08-29| NEXTCSO<br />
Awards <strong>2017</strong><br />
Featuring the finest moments from the two-day<br />
security conference and awards ceremony<br />
that felicitated India's future CSOs<br />
advertisers ’ index<br />
Infocom<br />
Airtel<br />
Cover Design by:<br />
Manoj Kumar VP<br />
IFC<br />
BC<br />
Please Recycle<br />
This Magazine<br />
And Remove<br />
Inserts Before<br />
Recycling<br />
COPYRIGHT, All rights reserved: Reproduction in whole or in part without written permission from<br />
Nine Dot Nine Interactive Pvt Ltd. is prohibited. Printed and published by Vikas Gupta for Nine Dot Nine<br />
Mediaworx Pvt Ltd, 121, Patparganj, Mayur Vihar, Phase - I, Near Mandir Masjid, Delhi-110091. Printed at<br />
Tara Art Printers Pvt ltd. A-46-47, Sector-5, NOIDA (U.P.) 201301<br />
This index is provided as an<br />
additional service.The publisher<br />
does not assume any liabilities<br />
for errors or omissions.<br />
2 CIO&LEADER | <strong>July</strong> <strong>2017</strong>
CASE STUDY<br />
04-06<br />
Intelenet Global Services'<br />
CIO 'taps' into AI<br />
www.cioandleader.com<br />
INSIGHT<br />
30-31<br />
The new workplace<br />
mojo<br />
32-33<br />
How to identify<br />
early AI adopters<br />
34-35<br />
Mind the fence<br />
36-37<br />
The glitch that<br />
brought down NSE<br />
INTERVIEW<br />
38-39<br />
The 'safa' wearing safe<br />
brigade<br />
MANAGEMENT<br />
Managing Director: Dr Pramath Raj Sinha<br />
Printer & Publisher: Anuradha Das Mathur<br />
EDITORIAL<br />
Managing Editor: Shyamanuja Das<br />
Associate Editor: Shubhra Rishi<br />
Content Executive-Enterprise Technology:<br />
Dipanjan Mitra<br />
DESIGN<br />
Sr Art Director: Anil VK<br />
Associate Art Director: Shokeen Saifi<br />
Visualiser: NV Baiju<br />
Lead UI/UX Designer: Shri Hari Tiwari<br />
Sr Designers: Charu Dwivedi, Haridas Balan,<br />
Manoj Kumar VP & Peterson PJ<br />
Sr Photographer: Jiten Gandhi<br />
SALES & MARKETING<br />
Director-Community Engagement<br />
for Enterprise Technology Business:<br />
Sachin Mhashilkar (+91 99203 48755)<br />
Brand Head: Vandana Chauhan (+91 99589 84581)<br />
Assistant Product Manager-Digital: Manan Mushtaq<br />
Community Manager-B2B Tech: Megha Bhardwaj<br />
Community Manager-B2B Tech: Renuka Deopa<br />
Assistant Manager Community: Mirzanoor Rahman<br />
Associate-Enterprise Technology: Abhishek Jain<br />
Assistant Brand Manager-B2B Tech: Mallika Khosla<br />
Regional Sales Managers<br />
South: Ashish Kumar (+91 97407 61921)<br />
North: Deepak Sharma (+91 98117 91110)<br />
West: Prashant Amin (+91 98205 75282)<br />
Ad Co-ordination/Scheduling: Kishan Singh<br />
Assistant Manager - Events: Naveen Kumar<br />
Assistant Manager - Events: Himanshu Kumar<br />
PRODUCTION & LOGISTICS<br />
Manager Operations: Rakesh Upadhyay<br />
Asst. Manager - Logistics: Vijay Menon<br />
Executive Logistics: Nilesh Shiravadekar<br />
Logistics: MP Singh & Mohd. Ansari<br />
OFFICE ADDRESS<br />
Nine Dot Nine Mediaworx Pvt Ltd<br />
121, Patparganj, Mayur Vihar, Phase - I<br />
Near Mandir Masjid, Delhi-110091<br />
Published, Printed and Owned by Nine Dot Nine Mediaworx<br />
Private Ltd. Published and printed on their behalf by<br />
Anuradha Das Mathur. Published at 121, Patparganj,<br />
Mayur Vihar, Phase - I, Near Mandir Masjid, Delhi-110091, India.<br />
Printed at Tara Art Printers Pvt Ltd., A-46-47, Sector-5,<br />
NOIDA (U.P.) 201301.<br />
Editor: Anuradha Das Mathur<br />
<strong>July</strong> <strong>2017</strong> | CIO&LEADER<br />
3
CASE STUDY<br />
Intelenet Global<br />
Services' CIO 'taps'<br />
into AI<br />
The IT leader is using a design thinking approach to<br />
nurture a new level of cross-departmental proximity<br />
with the help of T.A.P framework<br />
By Shubhra Rishi<br />
4 CIO&LEADER | <strong>July</strong> <strong>2017</strong>
Case Study<br />
The T.A.P team contributed to the<br />
success of the AI tool, with the help<br />
of which the company was able to<br />
cut down 10-11% in operational cost<br />
Ask a CIO about business alignment<br />
and he/she will emphasize on the<br />
need of it but do very little for it.<br />
Not Rajendra Deshpande; the Chief<br />
Information Officer at Intelenet<br />
Global Services (formerly Serco) has<br />
adopted a design thinking approach<br />
to "business alignment" into a new<br />
avatar: T.A.P.<br />
Deshpande’s role isn’t just limited<br />
to providing IT solutions for business.<br />
Instead he has a customer-facing<br />
role and is expected to constantly<br />
create business value for his organization<br />
as well as customers.<br />
Attuned to the role, two years ago,<br />
Deshpande came up with an innovative<br />
idea to create the T.A.P framework<br />
in order to build the capability<br />
to align IT activities to business strategy<br />
and performance goals. The T.A.P<br />
framework comprises teams from<br />
three functions namely Technology,<br />
Analytics and Process Excellence.<br />
Deshpande followed a creative process<br />
when it comes to harnessing the<br />
IT team’s potential. "Conventionally<br />
The Creative CIO<br />
Rajendra Deshpande is combining the power of creativity<br />
and technical expertise at his workplace. The T.A.P framework<br />
is a result of this genius. He is a doodler, photographer<br />
and a traveler. He possesses many diverse talents and that’s<br />
what keeps him inspired at work. He is a mentor for many of<br />
his team members. Sometimes in his rare free time, Deshpande<br />
sketches infographics; his most recent on Conference<br />
Call – A Reality Show. He works collaboratively, has great<br />
client focus, and brings a real depth of technical expertise<br />
across a number of IT disciplines<br />
<strong>July</strong> <strong>2017</strong> | CIO&LEADER<br />
5
Case Study<br />
"Adopting a design<br />
thinking approach and<br />
ensuring cross training<br />
of team members has<br />
helped us create a strong<br />
value proposition for<br />
business as well as<br />
customers"<br />
- Rajendra Deshpande<br />
CIO, Intelenet Global Services<br />
IT is always seen as a hindrance for<br />
implementing business initiatives.<br />
Not anymore.<br />
"With T.A.P, a new business initiative<br />
involves inputs from tech, business<br />
and process excellence ch<strong>amp</strong>ions,<br />
where we identify all new ideas,<br />
understand the priorities, and collect<br />
the few ideas that are most compelling<br />
for business," says Deshpande.<br />
One such idea was the in-house<br />
implementation of an artificial intelligence<br />
(AI) tool to allow retrieving<br />
airline ticketing fare rules across<br />
multiple time zones and websites.<br />
Deshpande says that there was a<br />
need for a system that is capable<br />
of communicating with the client<br />
systems and Global Distribution<br />
Systems (GDS) in order to simplify<br />
the fare rules.<br />
The company wanted to build this<br />
tool to serve all different time zones<br />
in the most efficient manner in order<br />
to serve their customers in the travel<br />
or tourism industry.<br />
“Companies across the globe are<br />
willing to invest millions in developing<br />
a product which can talk to multiple<br />
GDS’ across multiple time zones<br />
and POS,” says Deshpande.<br />
The T.A.P team closely worked with<br />
the development team to design the<br />
AI tool that communicates with the<br />
GDS and retrieves the PNR details,<br />
reads through the fare rules and<br />
check the applicable conditions,<br />
thereby calculating the applicable<br />
charge or refund due post an amendment<br />
or a cancellation.<br />
“Adopting a design thinking<br />
approach and ensuring cross training<br />
of team members has helped us<br />
create a strong value proposition for<br />
business as well as customers,” says<br />
Deshpande.<br />
The T.A.P team contributed to the<br />
success of the AI tool, with the help<br />
of which the company was able to cut<br />
down 10-11% in operational cost – the<br />
processing time required to process<br />
a request using the tool and improve<br />
their first call resolutions.<br />
“The AI tool was among the several<br />
projects that the T.A.P team<br />
undertook and effectively delivered,”<br />
says Deshpande<br />
Moreover, the team now works<br />
with different customers instead of<br />
working for them.<br />
Currently, there are 150 people in<br />
the T.A.P framework who are allocated<br />
to different projects. For each<br />
project, Deshpande says, while the<br />
core T.A.P team remains the same,<br />
different resources – based on their<br />
domain expertise— are allocated to<br />
different projects.<br />
As a result, Deshpande has also<br />
been able to address the talent gap in<br />
the organization. “We have been able<br />
to create positive synergies within the<br />
teams and improve the overall organizational<br />
culture,” he says.<br />
Deshpande’s goal has been to<br />
keep IT aligned with shifting business<br />
priorities. In a way, he has set<br />
an ex<strong>amp</strong>le for other CIO peers by<br />
constantly reinventing the wheel;<br />
taking business and customer-facing<br />
responsibilities; addressing the skill<br />
gap; recognizing talent.<br />
But above all, Deshpande is transforming<br />
organizational culture,<br />
thereby fostering a new level of<br />
cross-departmental proximity; not<br />
just alignment<br />
6 CIO&LEADER | <strong>July</strong> <strong>2017</strong>
#TheBigPicture<br />
Applicants from<br />
companies with over<br />
48% 2500 employees<br />
Applicants handling<br />
IT budgets of more than<br />
53% 5cr each<br />
Come and establish<br />
camaraderie with the<br />
IT giants of tomorrow<br />
For engagement opportunities, please contact<br />
Sachin Mhashilkar<br />
sachin.m@9dot9.in, +919920348755<br />
Vandana Chauhan<br />
vandana.chauhan@9dot9.in, +9199589 84581
NEXTCSO Event Coverage<br />
Featuring the finest moments from the two-day<br />
security conference and awards ceremony<br />
that felicitated India's future CSOs<br />
8 CIO&LEADER | <strong>July</strong> <strong>2017</strong>
NEXTCSO Event Coverage<br />
T<br />
he worst thing about a security breach is<br />
neither reputation risk nor the data theft<br />
that compromises the privacy of an individual.<br />
The worse is the inability to learn<br />
from them - to turn the reactive approach<br />
to a strategic one.<br />
In the last one year, an average of 36.6M<br />
records has been stolen in India - a 14%<br />
increase from 2015. WannaCry and Petya<br />
are recent ransomware attacks that have<br />
yet again, raised questions about enterprises'<br />
security preparedness.<br />
Unfortunately, the cyber security professionals<br />
haven't been able to keep up. Apex<br />
body NASSCOM claims that India has a<br />
50,000 cyber security workforce; however,<br />
it predicts that we will need at least one<br />
million skilled people by 2020.<br />
According to ISACA’s State of Cyber Security<br />
<strong>2017</strong>, 37% of respondents say fewer<br />
than 1 in 4 candidates have the qualifications<br />
employers need to keep companies<br />
secure. The survey also reveals that almost<br />
27% of respondents state that they are<br />
unable to fill open cyber security positions<br />
in their enterprises—with another 14% of<br />
respondents unaware as to whether their<br />
enterprises could fill these positions or not.<br />
This leaves a quarter of cyber security<br />
positions unfilled, the survey reports.<br />
In the wake of mounting security incidents<br />
– over 27,482 reported in <strong>2017</strong>—<br />
the government is taking some concrete<br />
steps to appraise the role of the Chief<br />
Information Security Officer (CISO).<br />
Indian-Computer Emergency Response<br />
Team (CERT-In) mandates all ministries,<br />
departments and organisations to<br />
appoint a CISO and have strengthened<br />
the role to implement the right security<br />
controls while promoting a culture of<br />
defense. Banks and insurance companies<br />
have also been mandated by regulatory<br />
bodies such as RBI and IRDAI to appoint<br />
a full-time CISO by April 30 and to formulate<br />
an effective cyber crisis management<br />
plan by June 30 of this year.<br />
While the basic expectations from the<br />
CISO will continue to remain the same:<br />
information security (IS), information risk<br />
management (IRM), data protection, and<br />
oversight of audits, governance and compliance,<br />
as well as technical, operational,<br />
legal and regulatory risks.<br />
But the basics won’t be enough.<br />
With the business and threat landscape<br />
changing rapidly, CISOs will have to<br />
upgrade their skills and ensure that any<br />
cyber security strategy contributes to<br />
financial stability and growth, and embeds<br />
security in all of the organization’s plans.<br />
This means that organizations need to<br />
appoint someone on your board who’s not<br />
only dedicated to cyber security but also<br />
understands regulatory requirements and<br />
overall business strategy.<br />
Perhaps that’s what will make a nextgeneration<br />
CISO?<br />
The aim of NextCSO Awards <strong>2017</strong> is<br />
just that: To find exceptional individuals<br />
who have the ability to take on the top job.<br />
They are selected through a rigorous and<br />
comprehensive process that will evaluate<br />
professional achievements, management<br />
and leadership skills that are essential to<br />
the making of a next-gen CISO.<br />
Here’s a glimpse into the NEXTCSO<br />
Conference that celebrated the triumph<br />
and victory of 24 next-gen CISOs and 20<br />
NEXTCSO jury who handpicked them.<br />
<strong>July</strong> <strong>2017</strong> | CIO&LEADER<br />
9
NEXTCSO Event Coverage<br />
Next-Gen Security For<br />
The New Age CISO<br />
The theme of the mid year conference was to discuss the changing<br />
role of the CSO in the enterprise and how it will be influenced by a<br />
number of factors including new business models and business<br />
channels, new threats, new skills, training and education that will be<br />
needed for both security specialists and leaders<br />
10 CIO&LEADER | <strong>July</strong> <strong>2017</strong>
NEXTCSO Event Coverage<br />
Security is approaching the realm of the sacred in the corporate<br />
world -- and the CISO is its protector. How to safeguard<br />
your assets? - is a question troubling security leaders and<br />
organizations alike. At the NEXTCSO mid-year conference this<br />
year, our goal was simple: To give the security leaders a glimpse<br />
into the future, new opportunities and new possibilities<br />
Vikas Gupta, Publisher & Director, 9.9 Media welcoming delegates at the NEXTCSO Midyear<br />
Conference at Crowne Plaza, Jaipur<br />
R Giridhar, Group Editor, CIO&<strong>Leader</strong> and CSO Forum introducing the first speaker of the<br />
NEXTCSO Mid-year Conference<br />
<strong>July</strong> <strong>2017</strong> | CIO&LEADER<br />
11
NEXTCSO Event Coverage<br />
Sunil Varkey, VP & CISO, Wipro Technologies kicked off the conference with the title session on 'NextGen Cyber Security: Re-thinking<br />
Strategies & Processes'<br />
The first session set the context for the day 1 of the conference where Sunil Varkey presented a CSO's<br />
perspective on the past, present and future of security, its changing landscape and juxtapositioned it with<br />
lessons from Wannacry and Petya. He also discussed the need for creating adaptive architecture and<br />
effective governance as a strategic measure to prepare for the future<br />
Sapan Talwar, Founder & CEO, Aristi<br />
Ninja, delivering a session on 'SecDevOps:<br />
Integrating Security into the Application<br />
Development Process'<br />
InfoSec missteps are becoming extremely<br />
costly, and billions of dollars Enterprises<br />
spend far less on software supply chain<br />
security. Sapan said that SDO best practices<br />
will help organizations implant secure coding<br />
deep in the heart during development.<br />
Automation in coding and workflow security<br />
tests will make secure software an inherent<br />
outcome in today’s agile environment<br />
12 CIO&LEADER | <strong>July</strong> <strong>2017</strong>
NEXTCSO Event Coverage<br />
CISOs listening attentively to the ongoing sessions at the CISO conference<br />
Sanjivan S Shirke, Senior VP - IT & Head -<br />
Information Security, UTI Asset Management<br />
Co enchanted the audience with an interesting<br />
session on 'Handling Ransomware Threats &<br />
Zero Day Attacks'<br />
Ransomware is a threat not in the distant<br />
future, said Sanjivan Shirke at UTI Asset<br />
Management Co. Ransomware is the fastest<br />
growing malware threat, targeting users of<br />
all types—from the ... average, more than<br />
4,000 ransomware attacks have occurred<br />
daily. He also stressed on the need for<br />
security teams to stay current on threat<br />
vectors, and keep operating systems and<br />
applications up to date with current patches.<br />
User education, he said, is the starting<br />
point for enterprise security and is even<br />
more important now<br />
<strong>July</strong> <strong>2017</strong> | CIO&LEADER<br />
13
NEXTCSO Event Coverage<br />
"Organizations have improved<br />
their abilities to resist attacks,<br />
but attacks take different and<br />
increasingly complex forms,"<br />
said Raddad Ayoub at Ernst &<br />
Young. He talked about the executing<br />
control measures in the<br />
corporate shield and how they<br />
work against DDoS or virus<br />
attacks, but not against sophisticated,<br />
persistent attacks that<br />
dedicated and organized cyber<br />
criminals are launching every<br />
day.<br />
He advised that the CIO and<br />
CISO need to fully understand<br />
the organization’s strategic<br />
direction, risk appetite and<br />
operations to support the adapt<br />
and reshape phases.<br />
The session on 'Cyber Resilience: Sense, Resist & React' was conducted by Raddad Ayoub,<br />
Partner, EMEIA Advisory Center for Cyber & Governance Risk and Compliance, Ernst & Young<br />
NEXTCSO Winners and CISOs attentively listening to the ongoing sessions at the CISO conference<br />
14 CIO&LEADER | <strong>July</strong> <strong>2017</strong>
NEXTCSO Event Coverage<br />
IT operations in many organisations<br />
lack process capabilities<br />
for comprehending realtime<br />
intelligence and taking<br />
timely action to safeguard the<br />
assets. Shree Parthasarathy<br />
at Deloitte Touche Tohmatsu<br />
said that threat Intelligence<br />
services enables organisations<br />
to proactively manage technology<br />
resources more effectively<br />
by providing alerts and<br />
advisory related information<br />
on the latest vulnerabilities to<br />
different IT resources.<br />
Shree Parthasarathy, Partner & National <strong>Leader</strong> - Cyber Risk Services, Deloitte Touche<br />
Tohmatsu India addressed the CSO community on 'Threat Intelligence: The New Frontier'<br />
Cyber-attackers are leveraging<br />
automation technology to<br />
launch strikes today. WannaCry<br />
is not a one-off event. Manish<br />
Tewari at Microsoft said<br />
that they has been committed<br />
to ensuring our customers are<br />
protected against these potential<br />
attacks.They recommend<br />
those on older platforms, such<br />
as Windows XP, to upgrade to<br />
the latest platforms. The best<br />
protection is to be on a modern,<br />
up-to-date system that incorporates<br />
the latest defense-indepth<br />
innovations. Older systems,<br />
even if fully up-to-date,<br />
lack the latest security features<br />
and advancements.<br />
The hot topic of 'Protecting Your Critical Information Infrastructure' was delivered by<br />
Manish Tiwari, CISO, Microsoft India<br />
<strong>July</strong> <strong>2017</strong> | CIO&LEADER<br />
15
NEXTCSO Event Coverage<br />
LUNCH<br />
During the Security Cafe, our partners and CISOs grouped for a discussion on a wide range of security topics<br />
The aim of the 'Security Cafe' was to embark on a fresh dialogue on next-gen security. In their effort to launch<br />
new digital initiatives, security is the latest conundrum that's troubling leaders today. Is there a way organizations<br />
can protect their critical assets on cloud? What would be the role of the CISO if they were to embrace<br />
digital? Security leaders were divided into different groups where they engaged with our partners on the<br />
various security challenges and opportunities in the future<br />
9.9 Media conducted a lucky draw and gave away prizes to 10 winners<br />
16 CIO&LEADER | <strong>July</strong> <strong>2017</strong>
NEXTCSO Event Coverage<br />
The NEXTCSO mid-year conference drew a full house comprising an attendee<br />
list of top security delegates from some of the largest companies in India. The<br />
rich content delivery and an elite speaker panel gathered accolades from jury,<br />
winners and speakers alike.<br />
Delegates, CISOs and our<br />
partners networking between<br />
speaker sessions<br />
<strong>July</strong> <strong>2017</strong> | CIO&LEADER<br />
17
NEXTCSO Event Coverage<br />
At the NEXTCSO Conference,<br />
Shivakumar Sriraman at VISA,<br />
spoke about the future of payments.Today<br />
there are more<br />
technology players in the market;<br />
hence, there's even more<br />
disruption. When it comes to<br />
payment security,companies<br />
are in a constant dilemma:<br />
convenience or security? Fraud<br />
remains near historic lows, but<br />
data losses continue to accelerate.Companies<br />
need to constantly<br />
think beyong cards and<br />
passwords. The key to securing<br />
the future of payments lies<br />
with tokenization; expanding<br />
from device-based to card-notpresent<br />
applications.<br />
An impactful session on 'Securing the Future of Payments' was delivered by Shivakumar<br />
Sriraman, Chief Risk Officer – India & South Asia, VISA<br />
Maneesh Dube, Executive Director, Russell Reynolds Associates - India & Tim Cook, Managing Director, Wychwood Partners - UK jointly<br />
delivered a session on 'Keeping Pace with the Evolving Role of the CISO'<br />
While all this is happening globally, only a handful of CISOs get more than INR 1 Cr. in India. So<br />
the big question is: what differentiates the heavy hitters? Tim and Maneesh talked about the five<br />
top capabilities that include experience, intellectual horsepower, vision, leadership and the ability<br />
to collaborate.They also discussed the top job requirements such as application security, product<br />
security, security architects, forensic investigation and behavioral analytics, required to secure a<br />
high-paying CISO role.<br />
18 CIO&LEADER | <strong>July</strong> <strong>2017</strong>
NEXTCSO Event Coverage<br />
As organizations increasingly embrace IoT into<br />
mainstream operations, the onboarding and management<br />
of IoT devices becomes critical to success.,<br />
said Santanu Ghose at HPE Aruba. He said<br />
that companies need a strategy to securely connect<br />
mobile and IoT devices at the edge, to extract the<br />
value associated with smart buildings<br />
Santanu Ghose, Director, HPE Aruba and Arpit Bhatt, Consulting Systems Engineer - Security and IoT,<br />
HPE Aruba delivered a session on 'Smarter Security Across the Intelligent Edge'<br />
CISOs and NextCSOs attending Wine and Cheese session<br />
conducted by Microsoft<br />
Jatinder Singh Pabla, Lead - Office 365 Business,<br />
Microsoft India, spoke to CISOs on 'How to build<br />
a Secure Productive Enterprise'. The session was<br />
moderated by Sachin Mhashilkar, Director-Community<br />
Engagement, 9.9 Media<br />
<strong>July</strong> <strong>2017</strong> | CIO&LEADER<br />
19
NEXTCSO Event Coverage<br />
Rajiv Nandwani at Innodata<br />
discussed the Bimodal<br />
approach in IT- the practice<br />
of managing two separate but<br />
coherent styles of work; one<br />
that is focused on predictability<br />
and the other focused on<br />
exploration. Nandwani said<br />
that both modes are essential<br />
to create substantial value and<br />
drive significant organizational<br />
change, and neither is static.<br />
Marrying a more predictable<br />
evolution of products and<br />
technologies with the new and<br />
innovative is the essence of an<br />
enterprise bimodal capability.<br />
Both play an essential role in<br />
digital transformation<br />
An interesting session on Aligning Security & Risk Management with Bimodal IT was<br />
conducted by Rajiv Nandwani, Director & VP - Global Information Security & CISO, Innodata<br />
Anuj Tewari at HCL Technologies<br />
discussed the growing<br />
dependency of CISOs on third<br />
parties due to globalization<br />
and expanded use to support<br />
core products, economic pressure<br />
– need for efficiencies<br />
and cost savings as well as<br />
growing threats. Today the<br />
third parties are expected to<br />
deliver critical specialized services<br />
and there is a growing<br />
need to maximise value and<br />
deliver great commercial outcomes<br />
through relationships.<br />
He recommended creation of<br />
assess controls based on risk<br />
of product or service.<br />
The highly engaging topic of 'Beyond the Enterprise: Securing the Third Party Ecosystem'<br />
was delivered by Anuj Tewari, CISO, HCL Technologies<br />
20 CIO&LEADER | <strong>July</strong> <strong>2017</strong>
NEXTCSO Event Coverage<br />
Welcome to NextCSO Awards <strong>2017</strong> - The<br />
inaugural speech and presentation was given<br />
by Group Editor, R Giridhar<br />
The NEXTCSO winners were decked in a formal attire along<br />
with the traditional 'safa' at the NextCSO Awards <strong>2017</strong> -<br />
awaiting their turn at the ceremony<br />
The stage was set at The<br />
Crowne Plaza, Jaipur for the<br />
NEXTCSO Awards <strong>2017</strong>. The<br />
award winners were selected<br />
through a rigorous and comprehensive<br />
process that will<br />
evaluate professional achievements,<br />
management and leadership<br />
skills that are essential<br />
to fulfilling the challenging<br />
role of a CISO<br />
An interesting panel discussion on Making the Leap to NextGen Cyber Security Moderated by Faraz Ahmed, CISO, Morgan Stanley<br />
Panelists: Bharat Gautam, CISO, Hero FinCorp, Murli Menon, Director & CSO, Atos and Milind G. Mungale, SVP & CISO, NSDL<br />
e-Governance Infrastructure<br />
<strong>July</strong> <strong>2017</strong> | CIO&LEADER<br />
21
NEXTCSO Event Coverage<br />
Felicitation of NextCSO Awards Winners<br />
The 24 next-gen security leaders receiving the NEXTCSO Awards in a grand ceremony at The<br />
Crowne Plaza, Jaipur on 7-8th <strong>July</strong> <strong>2017</strong><br />
22 CIO&LEADER | <strong>July</strong> <strong>2017</strong>
NEXTCSO Event Coverage<br />
The awards program draws on the support and involvement of India’s top executives and leaders to<br />
select 24 exceptional individuals who have skills, talent and motivation to take on the top job<br />
<strong>July</strong> <strong>2017</strong> | CIO&LEADER<br />
23
NEXTCSO Event Coverage<br />
NextCSO Awards Jury Felicitation<br />
The NEXTCSO jury being felicitated at the awards ceremony. The final selection was made by a prestigious<br />
committee of top 20 information security leaders<br />
From L to R: Manoj Nayak, SBI Life Insurance, Thiyagarajan Saravanan,<br />
HPCL, Indrajit Saha, Indian Oil Corporation, Sanjivan S Shirke,<br />
UTI Asset Co, Faraz Ahmed, Morgan Stanley, Sunil Varkey, Wipro<br />
Technologies, Burgess Cooper, Ernst & Young, Milind Mungale NSDL<br />
e-Governance Infrastructure Ltd, Anuj Tewari, HCL Technologies, Uday<br />
Deshpande, Tata Motors<br />
24 CIO&LEADER | <strong>July</strong> <strong>2017</strong>
NEXTCSO Event Coverage<br />
Entertainment<br />
At the NEXTCSO Awards, Rajasthani artists lit up the stage<br />
with folk music and dance performances. In Matka Bhavai<br />
dance, the number of vessels gradually increase and the dancer<br />
balances up to seven or more on her head. The folk singer<br />
sang traditional songs from Bikaner among other places, as<br />
the audience matched their steps with the dancers<br />
<strong>July</strong> <strong>2017</strong> | CIO&LEADER<br />
25
NEXTCSO Event Coverage<br />
As the awards night came to<br />
a close, Sachin Nandkishor<br />
Mhashilkar, Director - Community<br />
Engagement, at 9.9<br />
Media, looked back at the<br />
event that it had been. He<br />
thanked the winners, jury,<br />
and partners, HPE Aruba,<br />
Microsoft, Sophos, Juniper<br />
and InstaSafe, for their support<br />
and encouragement,<br />
in helping CSO Forum put<br />
together a fantastic NEXTC-<br />
SO conference and awards<br />
ceremony<br />
Vote of thanks by Sachin Nandkishor Mhashilkar, Director-Community Engagement, 9.9 Media<br />
Felicitation of Partners at the NEXTCSO <strong>2017</strong><br />
26 CIO&LEADER | <strong>July</strong> <strong>2017</strong>
NEXTCSO Event Coverage<br />
CSO Mid-year Conference - Day 2<br />
The Day 2 of the NEXTCSO<br />
Conference had an interesting<br />
line up of speakers discussing<br />
a wide range of topics such as<br />
artificial intelligence in security,<br />
IoT intelligence and testing,<br />
connected cars and the<br />
cybersecurity threat - all relevant<br />
and crucial to the future<br />
of enterprise security<br />
In today's unpredictable<br />
times, information security<br />
and cyber security must<br />
co-exist and be balanced<br />
such that the former continues<br />
to strengthen the<br />
foundations,and the latter<br />
becomes a visible business<br />
enabler, based on customer<br />
confidence. He proposed a<br />
framework that should provide<br />
a broad guideline on<br />
Information & cyber security<br />
for insurance industry.<br />
It should be flexible, leverage<br />
existing international<br />
approaches, standards, practices,<br />
focus on risk management<br />
and total compliance<br />
and enable effective understanding<br />
of response recovery<br />
versus prevention<br />
Meeting the Regulatory Bar: Information Security & Regulators by Manoj Nayak, CISO, SBI<br />
Life Insurance Co<br />
<strong>July</strong> <strong>2017</strong> | CIO&LEADER<br />
27
NEXTCSO Event Coverage<br />
Using AI & Machine Learning for Cyber Security<br />
by Venkatsubramanian Ramakrishnan, Head - Information Risk Management, Cognizant<br />
Security professionals are<br />
hesitant to use quantitative<br />
methods because of the following<br />
common misconceptions<br />
that include cyber security is<br />
too complex to model quantitatively.<br />
Venkatakrishnan<br />
Subramanian at Cognizant<br />
says that we have to ask ourselves<br />
exactly how the existing<br />
risk matrices and risk scores<br />
alleviate these issues. Are<br />
they really helping us to make<br />
decisions? The answer is that<br />
quantitative, probabilistic<br />
methods must be used specifically<br />
because of lack of perfect<br />
information, not in spite of<br />
it. If perfect information was<br />
available, probabilistic models<br />
would not be required at all.<br />
Bringing connectivity to<br />
the car has enabled vehicle<br />
manufacturers to offer an<br />
increasing range of services.<br />
This allows users to access<br />
information on the move and<br />
fulfil the promise of seamless<br />
connectivity. Uday Deshpande<br />
at Tata Motors discussed<br />
the transformation of cars<br />
from mechanical systems to<br />
mobile computer networks<br />
has opened up an array of<br />
new attack points. and invited<br />
the attention of hackers to<br />
unleash more organised criminal<br />
activity<br />
Securing the Connected Automotive Ecosystem by Uday Deshpande, CISO, Tata Motors<br />
28 CIO&LEADER | <strong>July</strong> <strong>2017</strong>
NEXTCSO Event Coverage<br />
Towards the end of the NEXTCSO<br />
mid-year conference, Sophos<br />
conducted a lucky draw and gave<br />
away prizes to one lucky winner<br />
IoT will offer opportunities<br />
for companies which are manufacturing<br />
IoT goods, and also<br />
for those companies which<br />
are providing services related<br />
to IoT. Pratiksha Doshi at<br />
E&Y demonstrated different<br />
use cases of IoT across<br />
verticals. The manufacturers<br />
of smart devices, sensors or<br />
actuators, and the application<br />
developers, marketing strategists,<br />
analytic companies and<br />
internet service providers<br />
(ISPs) will all profit from<br />
the evolution of IoT.<br />
The session on IoT Security and Testing was delivered by Burgess Cooper, Partner -<br />
Information & Cyber Security, Ernst & Young and Pratiksha Doshi, Director, E&Y<br />
<strong>July</strong> <strong>2017</strong> | CIO&LEADER<br />
29
INSIGHT<br />
The new<br />
workplace mojo<br />
The study highlights that success lies in the effective<br />
implementation of a digital workplace strategy capable of<br />
driving true cultural change that accelerates business<br />
By CIO&<strong>Leader</strong><br />
30 CIO&LEADER | <strong>July</strong> <strong>2017</strong>
Insight<br />
W<br />
Smarter workspaces don’t just<br />
create happier employees – they also<br />
help in creating newer and authentic<br />
relationships with customers and<br />
the ecosystem as a whole<br />
orkspace is no longer seen as a<br />
physical environment as the disruptive<br />
impact of digital transformation<br />
spreads across organizations<br />
and industries, according to a latest<br />
IDC study. As per the study, entitled<br />
“Workspace Transformation: The Key<br />
to Tomorrow’s Digital Enterprise,” success<br />
lies in the effective implementation<br />
of a digital workplace strategy capable<br />
of driving true cultural change that<br />
accelerates business.<br />
The detailed IDC study outlined<br />
current enterprise trends along with<br />
appropriate use cases to support<br />
informed decision making about<br />
market offerings. It also assessed<br />
a real-world solution – Dimension<br />
Data’s Workspaces for Tomorrow on<br />
Microsoft Office 365 – which aims to<br />
address enterprise needs for a reliable,<br />
mobile, flexible, secure, and costeffective<br />
solution.<br />
“Can business leaders, CIOs, and IT<br />
leaders today claim to have enabled<br />
truly digital workspaces – where<br />
employees and the overall ecosystem<br />
can share knowledge and forge more<br />
productive business relationships<br />
beyond natural work groups? The<br />
answer more often than not will be<br />
"No." Should they be worried? The<br />
answer is a resounding "Yes." The Digital<br />
Workspace is no longer an option<br />
– it is an imperative,” said Arjun<br />
Vishwanathan, Associate Director –<br />
Emerging Technologies, IDC India.<br />
According to Vishwanathan, smarter<br />
workspaces don’t just create happier<br />
employees – they also help in creating<br />
newer and authentic relationships<br />
with customers and the ecosystem as a<br />
whole. “Although newer technologies<br />
and increased training are the standard<br />
go-to models, it is becoming clear<br />
that perhaps the most effective strategy<br />
is in creating an enhanced and<br />
adaptive workspace through improving<br />
the workspace itself,” he said.<br />
The report notes that Dimension<br />
Data is uniquely poised to enable<br />
solutions around this with its Enduser<br />
Computing Development Model<br />
(EUCDM), which allows organisations<br />
to identify not only the current<br />
state, but also define the future road<br />
map and requirements. As well as<br />
assessing the way employees meet,<br />
work, and collaborate, the Dimension<br />
Data solution also offers the<br />
implementation and management of<br />
user-aligned technologies via planning,<br />
deployment, integration, and<br />
managed services.<br />
A critical part of the picture is the<br />
global partnership between Dimension<br />
Data and Microsoft; which aims<br />
to drive value for organisations. As<br />
a key alliance partner to Microsoft,<br />
Dimension Data brings enhanced<br />
access to early adopter programs,<br />
technical support, and Microsoft’s<br />
future direction.<br />
The study indicates that digital<br />
transformation efforts are going to<br />
continue to dramatically change the<br />
workspace landscape – particularly<br />
at the edge. An explosion of new<br />
device types and applications are<br />
being fueled by trends, such as<br />
Internet of Things (IoT), augmented<br />
reality/virtual reality (AR/VR), and<br />
cognitive computing.<br />
“The ability of our Workspaces<br />
for Tomorrow solution to support a<br />
variety of services, including advisory<br />
and management and to be an allaround<br />
partner in progress is symbolized<br />
by the tangible business value on<br />
offer. That includes cost savings, business<br />
and operational efficiencies, security,<br />
and enhanced user experience<br />
and satisfaction,” said Kiran Bhagwanani,<br />
CEO, Dimension Data India.<br />
“When viewed from the perspective<br />
of an organisation that is traversing<br />
its own DX journey, these attributes<br />
have the potential to deliver seamless<br />
transformation and outcomes that are<br />
predictable, and place the enterprise<br />
on a forward- looking growth trajectory,”<br />
said Bhagwanani<br />
<strong>July</strong> <strong>2017</strong> | CIO&LEADER<br />
31
Insight<br />
How to identify<br />
early AI adopters<br />
In a new research paper, McKinsey & Company aims to<br />
explore the potential of artificial intelligence (AI) to become<br />
a major business disrupter<br />
By CIO&<strong>Leader</strong><br />
A<br />
rtificial Intelligence creates news almost<br />
every day. In the last year, tech giants, such as<br />
Google and Baidu invested between USD 26B<br />
to USD 39B in artificial intelligence. However,<br />
according to a research paper titled Artificial<br />
Intelligence: The Next Digital Frontier?’ published<br />
by Mckinsey & Company, the adoption<br />
of AI in <strong>2017</strong> has remained low - with 41% of<br />
enterprises said that they are still uncertain<br />
about the benefits of the technology.<br />
The survey that gathered responses from<br />
3,000 businesses around the world also<br />
32 CIO&LEADER | <strong>July</strong> <strong>2017</strong>
Insight<br />
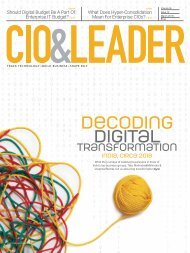
How companies are adopting AI<br />
AI adoption is greatest in sectors that are already strong digital adopters<br />
High AI<br />
adoption<br />
Medium<br />
AI<br />
adoption<br />
Low AI<br />
adoption<br />
•<br />
•<br />
•<br />
•<br />
found that many business leaders<br />
are uncertain about what exactly<br />
AI can do for them, where to obtain<br />
How AI-aware are you?<br />
20% they are adopters<br />
3+ technologies<br />
3%<br />
2 technologies 7%<br />
1 technology<br />
41%<br />
say they are uncertain<br />
of AI<br />
Retail<br />
Media / entertainment<br />
CPG<br />
Assets<br />
Usage<br />
Digital Maturity<br />
Six characteristics of early AI adopters<br />
Digitally mature<br />
Adopt multiple<br />
technologies<br />
31%<br />
10%<br />
Partial adopters<br />
Larger<br />
businesses<br />
Focus on growth<br />
over savings<br />
10%<br />
40%<br />
Experimenters<br />
Contemplators<br />
Adopt AI in<br />
core activities<br />
C-level<br />
support for AI<br />
Source: McKinsey Global Institute, McKinsey&Company<br />
AI-powered applications, how to<br />
integrate them into their companies,<br />
and how to assess the return on an<br />
Labor<br />
investment in the technology.<br />
For the rest, Mckinsey & Company<br />
defines six characteristics of early<br />
AI adopters that differentiates them<br />
from late bloomers:<br />
The first feature is that early AI<br />
adopters are from verticals already<br />
investing at scale in related technologies,<br />
such as cloud services and big<br />
data. Those sectors are also at the frontier<br />
of digital assets and usage. This<br />
is critical, as it suggests that there is<br />
limited evidence of sectors and firms<br />
catching up when it comes to digitization,<br />
as each new generation of tech<br />
builds on the previous one.<br />
Second, independently of sectors, large<br />
companies tend to invest in AI faster<br />
at scale. This again is typical of digital<br />
adoption, in which, for instance, small<br />
and midsized businesses have typically<br />
lagged behind in their decision to invest<br />
in new technologies.<br />
Third, early adopters are not specializing<br />
in one type of technology. They<br />
go broader as they adopt multiple AI<br />
tools addressing a number of different<br />
use cases at the same time.<br />
Fourth, companies investing at<br />
scale do it close to their core business.<br />
Fifth, early adopters that adopt at<br />
scale tend to be motivated as much<br />
by the upside growth potential of AI<br />
as they are by cutting costs. AI is not<br />
only about process automation, but<br />
is also used by companies as part of<br />
major product and service innovation.<br />
This has been the case for early<br />
adopters of digital technologies and<br />
suggests that AI-driven innovation<br />
will be a new source of productivity<br />
and may further expand the growing<br />
productivity and income gap<br />
between high-performing firms and<br />
those left behind.<br />
Finally, strong executive leadership<br />
goes hand in hand with stronger AI<br />
adoption. Respondents from firms<br />
that have successfully deployed an<br />
AI technology at scale tended to rate<br />
C-suite support nearly twice as high<br />
as those from companies that had not<br />
adopted any AI technology<br />
<strong>July</strong> <strong>2017</strong> | CIO&LEADER<br />
33
Insight<br />
Mind the fence<br />
Perimeter security may be important, but understanding<br />
of technology and data security is imperative<br />
By CIO&<strong>Leader</strong><br />
Despite the increasing number of data breaches<br />
and nearly 36.6 million data records being<br />
lost or stolen in India in 2016, the vast majority<br />
of IT professionals still believe perimeter<br />
security is effective at keeping unauthorized<br />
users out of their networks, as per Breach<br />
Level Index. However, companies are under<br />
investing in technology that adequately protects<br />
their business, according to the findings<br />
of the fourth-annual Data Security Confidence<br />
Index released recently by Gemalto.<br />
Surveying 1,050 IT decision makers worldwide,<br />
businesses feel that perimeter security is<br />
keeping them safe. Out of the 100 IT decision<br />
makers from India, most (98%) believe that it is<br />
quite effective at keeping unauthorized users<br />
out of their network. However, 49% are not<br />
extremely confident their data would be protected,<br />
should their perimeter be breached, a slight<br />
decrease on last year (58%). Despite this, nearly<br />
seven in 10 (69%) organizations report that they<br />
believe all their sensitive data is secure.<br />
Are you protecting your data?<br />
Many businesses are continuing to prioritize<br />
perimeter security without realizing it<br />
34 CIO&LEADER | <strong>July</strong> <strong>2017</strong>
Insight<br />
Job descriptions of the five CDO archetypes<br />
Progressive<br />
Thinker<br />
Creative<br />
Disruptor<br />
Customer<br />
Advocate<br />
Innovative<br />
Technologist<br />
Universalist<br />
Promotes open,<br />
dialogue-oriented<br />
culture<br />
Industry-wide<br />
reputation<br />
as thought leader<br />
Early adopter<br />
Change agent<br />
Promotes open<br />
culture: innovative,<br />
agile,<br />
experimental<br />
Young, softwareoriented<br />
culture<br />
Promotes open<br />
culture: responsive,<br />
adaptive, customercentric<br />
Client advocate<br />
Promotes open,<br />
agile culture<br />
Change agent<br />
Promotes open<br />
culture, dialogueoriented<br />
and flexible<br />
Industry-wide<br />
reputation as<br />
throught leader<br />
Leading<br />
ambassador for<br />
change<br />
Source: Strategy& analysis, PwC<br />
is largely ineffective against sophisticated<br />
cyber attacks. According to the research findings,<br />
93% of Indian respondents said their<br />
organization had increased investment in<br />
perimeter security technologies such as firewalls,<br />
IDPS, antivirus, content filtering and<br />
anomaly detection to protect against external<br />
attackers. Despite this investment, two thirds<br />
(66%) believe that unauthorized users could<br />
access their network, rendering their perimeter<br />
security ineffective.<br />
These findings suggest that there is a lack<br />
of confidence in the solutions used, especially<br />
as over a third (38%) of organizations<br />
have seen their perimeter security breached<br />
in the past 12 months. The reality of the situation<br />
is worsened when considering that,<br />
on average, less than 10% of data breached<br />
(11%) was encrypted.<br />
Businesses’ confidence is further undermined<br />
by over half of respondents (45%) not<br />
knowing where [all] their sensitive data is<br />
stored. In addition, over a third of businesses<br />
do not encrypt valuable information, such as<br />
payment (33%) or customer (39%) data. This<br />
means that, should the data be stolen, a hacker<br />
would have full access to this information,<br />
and can use it for crimes including identify<br />
theft, financial fraud or ransomware.<br />
As many believe that unauthorised users<br />
could access their organization’s data if<br />
they penetrated the network, the worry<br />
of future breaches is a justified ongoing<br />
concern. According to respondents from<br />
organizations that have suffered a perimeter<br />
security breach, only 8% of breached data<br />
was encrypted, on average. If unauthorised<br />
users access the network and access the data<br />
within it, it is more likely than not that they<br />
have full visibility of that data as well.<br />
Security practices and the link<br />
to data regulations<br />
Over nine in ten (94%) surveyed IT decision<br />
makers believe that two-factor authentication<br />
can help their organization comply with<br />
data protection regulations and pass security<br />
audits. The majority think the same for<br />
encryption of PII (88%) and key management<br />
(84%). However, many organizations do not<br />
even have these measures in place when it<br />
comes to stakeholders accessing company<br />
data (Fig 10). This suggests that there is a<br />
divide between what IT decision makers<br />
believe is best and what organizations currently<br />
have been able to implement<br />
<strong>July</strong> <strong>2017</strong> | CIO&LEADER<br />
35
Insight<br />
The glitch that<br />
brought down NSE<br />
The recent NSE outage was caused by a software error, says<br />
a preliminary SEBI investigation—a reminder that we may be<br />
taking basic availability for granted<br />
By CIO&<strong>Leader</strong><br />
36 CIO&LEADER | <strong>July</strong> <strong>2017</strong>
Insight<br />
Atechnical glitch shut down India’s<br />
largest stock exchange, the National<br />
Stock Exchange, for more than three<br />
hours on June 10, <strong>2017</strong> as the system<br />
failed to boot in its opening time: 9<br />
am. The cash and derivative transactions<br />
were held up, though NSE<br />
halted the futures and options (F&O)<br />
operations too at around 10 am.<br />
After two failed attempts at 10.45<br />
am and 11.15 am, normal trading<br />
could only be resumed at 12.30 pm.<br />
This happened in a day where BSE<br />
Sensex saw a record high and also<br />
gained in volumes because many<br />
traders switched to BSE because of<br />
the NSE glitch.<br />
This outage comes exactly three<br />
years after the <strong>July</strong> 2014 outage<br />
at Bombay Stock Exchange (BSE)<br />
which had lasted for three hours.<br />
The NSE outage impacted trading<br />
for a longer period.<br />
Two previous cases of trading<br />
halts at BSE have been because of<br />
connectivity issues. NSE too had<br />
experienced a glitch in October 2012<br />
but trading was impacted for less<br />
than fifteen minutes.<br />
In August 2013, the US bourse<br />
NASDAQ, on which the NSE is<br />
modeled, had stopped functioning<br />
for more than three hours,<br />
due to a glitch. Even the New York<br />
Stock Exchange (NYSE), the largest<br />
exchange in the world, had stopped<br />
trading for almost four hours exactly<br />
two years back, on 9 <strong>July</strong> 2015.<br />
“The matter is being examined by<br />
the internal technical team and external<br />
vendors, to analyze and identify<br />
the cause which led to the issue and<br />
to suggest solutions to prevent recurrence,”<br />
NSE said in a press statement.<br />
Lack of Backup?<br />
Three hours is a very long time from<br />
trading point of view and many traders<br />
were unhappy that NSE did not<br />
switch to a backup system.<br />
NSE has been quoted as saying that<br />
it did not invoke its Business Continuity<br />
Plan (BCP) because the plan<br />
was meant to provide continuity in<br />
case of natural disasters, hardware<br />
failures and connectivity-related<br />
issues only.<br />
The stock exchange regulator, Securities<br />
and Exchange Board of India<br />
(SEBI), which was directed by the<br />
Indian Ministry of Finance to investigate<br />
the issue and submit a report by<br />
the day end, clarified that the glitch<br />
was a software issue.<br />
This outage comes exactly three<br />
years after the <strong>July</strong> 2014 outage<br />
at Bombay Stock Exchange (BSE)<br />
which had lasted for three hours.<br />
The NSE outage impacted<br />
trading for a longer period<br />
“On preliminary analysis, the technical<br />
problem apparently is related to<br />
software,” SEBI said in a statement.<br />
The regulator also ruled out the possibility<br />
of cyber attacks. “It does not<br />
seem to be related to any cyber security<br />
related compromise,” it clarified<br />
in the same statement.<br />
SEBI has directed NSE to submit<br />
a detailed report on the matter. The<br />
regulator has also asked NSE to have<br />
a review of their Business Continuity<br />
Plans and to submit a detailed plan<br />
as to what measures are going to be<br />
taken to avoid such recurrences.<br />
What to make out of the<br />
glitch?<br />
At the lack of any detailed public<br />
report, it is difficult to analyze what<br />
caused the delay. However, based on<br />
the information known so far, certain<br />
things are clear.<br />
1. It was not a cyber attack; it was a<br />
system error<br />
2. NSE did not switch to its BCP<br />
because that was reserved for<br />
natural disasters or hardware failures,<br />
meaning it has not taken into<br />
account situations like this where<br />
the business continuity was severely<br />
compromised, for its BCP<br />
This just means that even for mission<br />
critical applications such as stock<br />
market trading, there is serious gap in<br />
business continuity planning. In the<br />
last few months, a series of outages in<br />
airlines, such as Delta, United and British<br />
Airways had brought into limelight<br />
the gaps that remain in the resilience<br />
plans of these airlines, the NSE outage<br />
has once again highlighted that issue.<br />
In none of these cases, any external<br />
attack was involved.<br />
While a stock market outage may<br />
not have seen as much social media<br />
outrage as an Airlines outage, the<br />
potential impact in business terms<br />
could be much bigger.<br />
Are we ignoring the basic reliability<br />
and resilience plans while readying<br />
ourselves for tackling possible<br />
external actors?<br />
<strong>July</strong> <strong>2017</strong> | CIO&LEADER<br />
37
INTERVIEW<br />
“I want to foster a<br />
digital culture in the<br />
organization”<br />
Mandar Marulkar, CIO & CDO, KPIT Technologies, talks<br />
to Sachin Nandkishor Mhashilkar on his new digital role<br />
and what it entails<br />
38 CIO&LEADER | <strong>July</strong> <strong>2017</strong>
Mandar Marulkar, KPIT Technologies<br />
Interview<br />
‘‘With the pace at which<br />
digitization is taking place, it<br />
is important to ensure all your<br />
employees are enabled - both<br />
from a cultural and skill-set<br />
point of view’’<br />
–Mandar Marulkar<br />
CIO & CDO, KPIT Technologies<br />
According to you, what are some<br />
of the scenarios that are likely to<br />
impact your industry by 2020?<br />
Companies are upgrading their IT infrastructure<br />
to support IoT in the future. When we<br />
talk about 20 billion devices in 2020, they will<br />
generate a huge amount of data and that’s where<br />
professional services will be expected to churn<br />
out data and come up with relevant business<br />
use cases. In such a scenario, creating a platform<br />
that will enable interactions between producers<br />
and consumers and monetizing the data will be<br />
extremely important.<br />
What are some of your key priorities<br />
for 2020?<br />
From an automation perspective, embedding<br />
programmability into the infrastructure and<br />
integrating the software-defined with your core<br />
IT infrastructure will give birth to a true DevOps<br />
culture. The next priority will be moving on<br />
from the monolithic application stack and the<br />
waterfall methodology to application development.<br />
It is also important to understand the next<br />
generation threats and build the overall holistic<br />
cyber security platform, not only to protect your<br />
business applications and typical IT stack but<br />
to secure the OT infrastructure, especially as<br />
billions of devices now generate data from an<br />
OT perspective and that needs to be integrated<br />
with IT. The other area will be to build a digital<br />
culture in your organization. With the pace at<br />
which digitization is taking place, it is important<br />
to ensure all your employees are enabled -both<br />
from a cultural and skill-set point of view - in<br />
order to grab the challenge of 2020 and provide<br />
innovative solutions to the industry.<br />
How will the rapid evolution of<br />
technology impact your industry<br />
in the year 2020?<br />
It is very difficult for any organization to cope<br />
up with the rapid pace of innovation happening<br />
around the world. Lot of disruption is<br />
taking place in start-ups and companies you<br />
didn't know about or didn't exist until today.<br />
So we need to ensure that workload migration<br />
from on-premise to public cloud is secure and<br />
cost-effective.<br />
What are your personal goals for<br />
the year 2020?<br />
I’m getting into a new role of a Chief Digital<br />
Officer (CDO) and I’m expected to showcase<br />
our internal innovations to customers. Also, I<br />
want to create a digital culture in our organization,<br />
for the leadership as well as millennials,<br />
who join the company.<br />
<strong>July</strong> <strong>2017</strong> | CIO&LEADER<br />
39
NEW CHALLENGES<br />
NEWER POSSIBILITIES<br />
Come contribute to<br />
CIO Agenda 2020<br />
To know more about the event, log on to<br />
#CIO2020<br />
#Agenda2020