GSN_Mar_YUMPU
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
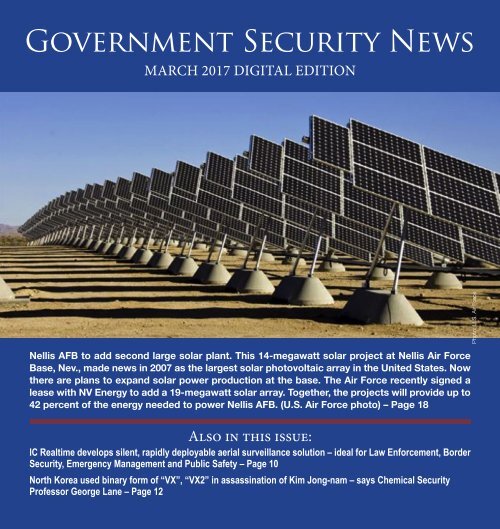
Government Security News<br />
MARCH 2017 DIGITAL EDITION<br />
Photo: U.S. Air Force<br />
Nellis AFB to add second large solar plant. This 14-megawatt solar project at Nellis Air Force<br />
Base, Nev., made news in 2007 as the largest solar photovoltaic array in the United States. Now<br />
there are plans to expand solar power production at the base. The Air Force recently signed a<br />
lease with NV Energy to add a 19-megawatt solar array. Together, the projects will provide up to<br />
42 percent of the energy needed to power Nellis AFB. (U.S. Air Force photo) – Page 18<br />
Also in this issue:<br />
IC Realtime develops silent, rapidly deployable aerial surveillance solution – ideal for Law Enforcement, Border<br />
Security, Emergency Management and Public Safety – Page 10<br />
North Korea used binary form of “VX”, “VX2” in assassination of Kim Jong-nam – says Chemical Security<br />
Professor George Lane – Page 12
<strong>GSN</strong> <strong>Mar</strong>ch 2017 Digital<br />
NEWS<br />
4<br />
6<br />
8<br />
10<br />
12<br />
15<br />
17<br />
18<br />
31<br />
33<br />
Tianjin Rail Transit (TRT) in China extends its<br />
Qognify video management system to cover new lines<br />
with 4,000 video cameras<br />
Hikvision and Eagle Eye Networks announce<br />
technology partnership<br />
Heightening security verification with<br />
self-service kiosks<br />
IC Realtime develops silent, rapidly-deployable aerial surveillance solution<br />
North Korea used binary form of “VX”, “VX2”<br />
in assassination of Kim Jong-nam<br />
Making microgrids work: send in the <strong>Mar</strong>ines?<br />
Aerojet Rocketdyne supports ULA launch of Wideband<br />
Global SATCOM spacecraft for the<br />
U.S. Military<br />
Bipartisan bill supports Department of Defense<br />
Cyber Scholarships<br />
New York Democrats rally to resist voter suppression, calling for action from<br />
NY Governor Cuomo<br />
New York Congressman Nadler blasts Trump budget<br />
as “Absurd”<br />
Image from a CCTV footage of one of the woman attackers<br />
2
Edition Table of Contents<br />
34<br />
38<br />
Biennial Women in Cybersecurity Report reveals that female representation<br />
in industry remains stagnant, as cyber workforce gap expected to reach<br />
1.8 million by 2022<br />
Hikvision and L.A. contemporary dance company illustrate<br />
the Art of Video Surveillance<br />
FEATURES<br />
SPECIAL REPORT ON BORDER SECURITY AND IMMIGRATION<br />
19<br />
Trump scapegoats immigrants with creation of “Office of<br />
Victims of Immigration and Crime Engagement”<br />
20<br />
21<br />
22<br />
23<br />
24<br />
25<br />
This immigration enforcement program has a troubled history,<br />
and Trump wants to restart it<br />
Trump’s immigration remarks at Joint Session of Congress once again packed<br />
with inaccurate statements and false blaming of immigrants<br />
Second “Muslim Ban” meets renewed litigation<br />
These changes may keep Asylum seekers from<br />
getting their day in court<br />
Homeland Security unions testify in support of more staff but not a border<br />
“wall”<br />
America’s treatment of asylum seekers reviewed by<br />
regional human rights body<br />
3
Tianjin Rail Transit (TRT) in China extends its<br />
Qognify video management system to cover<br />
new lines with 4,000 video cameras<br />
Qognify, formerly NICE Security,<br />
today announced that the Tianjin<br />
Rail Transit (TRT) in China will be<br />
extending its Qognify video management<br />
system (VMS) to provide<br />
coverage for the city’s Metro expansion.<br />
In total, Qognify technology<br />
will be helping to secure over 273<br />
kilometers of transit lines and 42<br />
stations, by effectively managing<br />
output from over 4,000 video cameras.<br />
Tianjin, a metropolis in northern<br />
coastal China located near Beijing,<br />
is experiencing steady population<br />
growth with currently over 15<br />
million inhabitants. In 2015, the<br />
Tianjin Transit Group, the body<br />
responsible for managing the city’s<br />
major Metro construction project,<br />
deployed Qognify’s video management<br />
solution. Since then, the solution<br />
has been a vital part of security<br />
management, which enabled the<br />
Group officials to confidently make<br />
the choice to extend the solution to<br />
the newly built lines.<br />
“For large-scale metros, managing<br />
security in a unified, centralized and<br />
robust way is always a big challenge<br />
to operators, public security,<br />
and government authorities,”<br />
said Mr. Song, Director<br />
of Construction, Tianjin<br />
Transit Group. “With Qognify’s<br />
advanced technology<br />
and deep transportation<br />
industry experience, we’re<br />
able to provide passengers<br />
a safe and secure environment,<br />
and to our employees<br />
an easy to access, scalable,<br />
and stable system to monitor and<br />
manage our entire Metro. These capabilities<br />
give us confidence to build<br />
more metro lines in Tianjin, which<br />
will greatly increase the friendliness<br />
of the city. We trust Qognify and believe<br />
they have the depth of experience<br />
we need.”<br />
“There is a unique combination of<br />
the right technology and breadth of<br />
transportation relevant experience<br />
that makes a massive difference to<br />
the success of large scale transportation<br />
projects such as the Tianjin<br />
Metro,” commented Moti Shabtai,<br />
President of Qognify. “Tianjin Metro<br />
sets an example for public transport<br />
organizations and we’re proud<br />
4<br />
to be able to provide the required<br />
level of expertise as we solidify<br />
our market-leading position in the<br />
transportation sector.”<br />
About Qognify<br />
Qognify helps organizations mitigate<br />
risk, maintain business continuity,<br />
and optimize operations. The<br />
Qognify portfolio includes video<br />
management, video and data analytics,<br />
and PSIM/ Situation Management<br />
solutions that are deployed<br />
in financial institutions, transportation<br />
agencies, airports, seaports,<br />
utility companies, city centers, and<br />
to secure many of the world’s highest-profile<br />
public events.
PROVEN TECHNOLOGY<br />
FOR SERIOUS THREATS<br />
PERIMETER PROTECTION<br />
FOR HIGH-RISK FACILITIES<br />
Designed to deter and withstand today’s increasing threats<br />
to government buildings, commercial properties and critical<br />
infrastructure, Ross Technology anti-ram vehicle barriers,<br />
bollards, gates and fencing offer unique features that minimize<br />
cost and maximize durability.<br />
We specialize in designing and manufacturing unique products that<br />
are tested to US Department of State (DOS) and ASTM standards,<br />
while addressing common challenges associated with installation,<br />
maintenance, restrictive site conditions and harsh environments.<br />
Trusted in embassies and high-risk facilities across the globe,<br />
Ross Technology offers you powerful protection against serious threats.<br />
Learn more at www.rosstechnology.com/perimeter-security/<br />
ARCHITECTURAL SECURITY | SAFETY WORKS<br />
PERIMETER SECURITY | INDUSTRIAL STORAGE<br />
XT-4000 Anti-Climb Sliding Gate<br />
XL-501 Post & Beam Anti-Ram Fence
Hikvision and Eagle Eye Networks<br />
announce technology partnership<br />
Integrators will benefit from easy-to-install cloud-based security system<br />
with extra cybersecurity measures<br />
6<br />
CITY OF INDUSTRY, CA and AUS-<br />
TIN, TX—<strong>Mar</strong>ch 15, 2017—Hikvision<br />
USA Inc., the North American<br />
leader in innovative, award-winning<br />
video surveillance products and solutions,<br />
and Eagle Eye Networks,<br />
Inc., the leading cloud-based video<br />
surveillance provider, today announced<br />
a technology partnership<br />
to deliver customers a seamless and<br />
cybersecure cloud video surveillance<br />
solution.<br />
Hikvision and Eagle Eye are expanding<br />
an established business relationship<br />
with its new technology<br />
partnership. It will enable a deeper<br />
bi-directional integration between<br />
Hikvision’s world class products<br />
and Eagle Eye’s purpose-built cloud<br />
platform, which will have significant,<br />
direct benefits for systems<br />
integrators. Those benefits include<br />
ease of installation and even more<br />
extensive technical support. Integrators<br />
and their end user customers<br />
will also reap the benefits associated<br />
with cloud platforms: lower<br />
up-front costs, flexibility, scalability,<br />
cyber-secure remote management<br />
and flexible on-premise cloud storage.<br />
“We are pleased to be working<br />
with a partner so clearly focused<br />
on cybersecurity and ease of use for<br />
our integrator partners,” said Jeffrey<br />
He, president of Hikvision USA Inc.<br />
“Eagle Eye’s Cloud Security Camera<br />
VMS provides businesses with a true<br />
cloud solution that is cyber-secured<br />
with multiple levels of encryption<br />
and advanced security features.”<br />
Those features include Eagle Eye’s<br />
recently announced Camera Cyber<br />
Lockdown, which blocks cameras<br />
from communicating with the Internet,<br />
blocks attacks from reaching<br />
cameras, and will not allow any Trojans<br />
ex-filtration. The feature greatly<br />
increases the security of video surveillance<br />
systems, reduces risk, and<br />
reduces camera maintenance.<br />
While the Eagle Eye Cloud Security<br />
Camera VMS works with hundreds<br />
of manufacturers’ cameras,<br />
the Hikvision partnership is particularly<br />
valuable for customers who<br />
don’t have in-house IT resources.<br />
The combined Hikvision/Eagle<br />
Eye technology is particularly well<br />
suited to multi-site enterprises with
small camera counts at each site, including<br />
retail, banking, and quick<br />
serve restaurants.<br />
Eagle Eye Network’s CEO Dean<br />
Drako stated “Hikvision’s leadership<br />
team has been exemplary to work<br />
with for making a great customer<br />
solution. They really understand<br />
the benefits of solving installation<br />
and cyber problems in a way that<br />
makes it easier for the customer.<br />
Hikvision’s global presence aligns<br />
with Eagle Eye’s global data center<br />
investment.”<br />
Eagle Eye Networks’ global footprint<br />
of data centers enables its customers<br />
to easily deploy surveillance<br />
video systems at<br />
their sites around the<br />
world while maintaining<br />
consistency<br />
and cybersecurity.<br />
Hikvision will exhibit<br />
its enterpriselevel<br />
security solutions<br />
at ISC West,<br />
Booth 18037, in Las<br />
Vegas, April 5-7,<br />
2017. Eagle Eye Networks<br />
will be exhibiting in<br />
Booth 23109.<br />
About Hikvision<br />
Hikvision is the world’s leading<br />
supplier of video surveillance<br />
solutions. Featuring<br />
the industry’s strongest R&D<br />
workforce, Hikvision designs,<br />
develops, and manufactures standard-<br />
and high-definition cameras,<br />
including a variety of IP cameras,<br />
analog cameras, and cameras featuring<br />
the latest in high-definition<br />
analog technology. Hikvision’s<br />
product suite also includes digital<br />
video servers, hybrid and standalone<br />
DVRs, NVRs, and other elements<br />
of sophisticated security systems<br />
for both indoor and outdoor<br />
use.<br />
About Eagle Eye Networks<br />
Eagle Eye Networks delivers the<br />
fastest growing, on-demand cloud<br />
based security and operations video<br />
management system<br />
(VMS) providing<br />
both cloud and<br />
on-premise recording.<br />
Eagle Eye also<br />
provides a cloud<br />
video API for integrations<br />
and application<br />
development.<br />
The Eagle<br />
Eye Platform offers<br />
secure, encrypted<br />
7<br />
recording, camera management,<br />
mobile viewing and alerts – all 100%<br />
cloud managed. The API platform<br />
uses the Eagle Eye Big Data Video<br />
Framework, with time based data<br />
structures used for indexing, search,<br />
retrieval and analysis of the live and<br />
archived video. Eagle Eye Networks<br />
sells through authorized reseller<br />
and installation partners.<br />
FREE SUBSCRIPTION<br />
SIGN-UP<br />
Monthly Digital Edition<br />
Airport/Seaport Newsletter<br />
Daily Insider Newsletter<br />
Cybersecurity Newsletter<br />
CLICK HERE
Heightening security verification with<br />
self-service kiosks<br />
By Gerald Hubbard,<br />
Business Development,<br />
Global Enterprise<br />
Technology Corp.<br />
The issuance and verification<br />
of identity credentials<br />
are currently managed<br />
by different agencies<br />
in different ways. Given the variations<br />
in resources, technology and<br />
security requirements, this is not<br />
surprising. Emerging technologies<br />
are now creating opportunities to<br />
achieve greater consistency across<br />
platforms and agencies which may<br />
enable greater efficiencies and better<br />
accuracy throughout the spectrum<br />
of security needs.<br />
One promising modality is the<br />
standalone, self-service ID kiosk. Its<br />
simplest form is similar to the electronic<br />
check-in kiosks at airports,<br />
where passengers insert their credit<br />
cards or scan their passports to verify<br />
identity. Those kiosks serve as an<br />
initial security point, but they do<br />
not support biometric data recognition<br />
(such as fingerprints, iris scan<br />
or facial recognition). They reduce<br />
the need for clerks to perform the<br />
check-in at the airline counter, without<br />
replacing TSA checkpoints<br />
where passengers<br />
show picture IDs along<br />
with boarding passes.<br />
Still, the check-in machine<br />
allows reasonable<br />
labor savings for airlines.<br />
It also provides<br />
a conceptual backdrop<br />
for the type of self-service<br />
kiosks that could enable<br />
greater levels of efficiency,<br />
savings and accuracy in security<br />
credentials issuance<br />
and authentication. This<br />
could be useful in government<br />
embassies and facilities,<br />
as well as in airports<br />
and other locations where<br />
security needs are high.<br />
The enrollment process<br />
for issuing ID credentials<br />
must still begin with a face-toface<br />
encounter with an officer or<br />
agent of the issuing body. For example<br />
a passport, driver’s license<br />
or global entry pass requires the<br />
completion and transfer of<br />
data such as birth certificates,<br />
fingerprints,<br />
signature, etc. Biomet-<br />
8<br />
ric data capture can be performed<br />
automatically with the use of a machine,<br />
such as the Speed Identity kiosk,<br />
or by a trained security agent.<br />
A combination of the two can also<br />
be used to speed up the process.<br />
The security officer is usually vested<br />
with the skills to recognize human<br />
factors, such as nervousness,<br />
that provide subjective<br />
cues about an applicant’s<br />
authenticity, for example.<br />
While fingerprints and<br />
photographs are collected<br />
automatically, the officer’s<br />
attention can be focused<br />
on observing behaviors<br />
that a machine can’t see or<br />
understand.<br />
The real benefit of a selfservice<br />
ID kiosk is after the<br />
credentials have been issued –<br />
when they are checked at the point<br />
of entry to an airport terminal,<br />
area or building. Here, biometric<br />
data can be matched against<br />
a central database. Fingerprints<br />
can be quickly scanned and<br />
matched. A signature can<br />
be validated. Or a photo<br />
can be used for a facial<br />
More on page 40
HIGH-ENERGY SCREENING<br />
FOR INCREASED SECURITY<br />
At Varex Imaging, our Linatron® technology is designed to scan,<br />
identify and detect potential threats. With a variety of high-energy<br />
imaging linear accelerators, we are your source solution.<br />
To learn more about Varex Imaging and our products, visit<br />
www.vareximaging.com.
IC Realtime develops silent, rapidly-deployable<br />
aerial surveillance solution<br />
Called PLAS (Persistent Low Altitude<br />
Surveillance), the package is<br />
comprised of a flight deck, imaging<br />
unit and tactical grade balloon system<br />
capable of reaching an altitude<br />
of 455-feet. Ideal applications include<br />
border protection; emergency management<br />
and security, public safety<br />
and intrusion defense at large-scale<br />
special events.<br />
POMPANO BEACH, FL – April 4,<br />
2017 – IC Realtime has developed a<br />
silent, rapidly-deployable aerial surveillance<br />
solution that provides law<br />
enforcement, border patrol and special<br />
event personnel the ability to remotely<br />
monitor events taking place<br />
in large areas.<br />
Called PLAS (Persistent Low Altitude<br />
Surveillance), the solution is<br />
comprised of a flight deck and imaging<br />
unit attached to a tactical-grade<br />
balloon that is released into the air<br />
by security personnel on the ground<br />
via a carbon fiber power tether /<br />
mini CAT6 cable. PLAS may also<br />
be battery-operated.<br />
PLAS can be used stationary or<br />
attached to personnel or vehicles to<br />
move about areas of interest. Because<br />
the system requires no propulsion,<br />
its silent operation makes<br />
it advantageous for drone hunting/<br />
deterring operations. While normally<br />
flown at 250-feet, it may be<br />
deployed as high as 455-feet.<br />
The PLAS flight deck is a 6- x 3-<br />
x 3-inch carbon fiber housing that<br />
contains all command, control, and<br />
communications equipment (i.e. the<br />
brains for the system), as well as onboard<br />
microphones for drone detection.<br />
These integrated components<br />
provide encrypted communications<br />
to either fixed or mobile command<br />
10<br />
center(s) as well as authorized mobile<br />
users. Total weight of the flight<br />
deck including an imaging unit is 5<br />
pounds.<br />
PLAS is compatible with any of IC<br />
Realtime’s video, thermal imaging<br />
and infrared cameras. Air sampling<br />
sensors such as CBRNE (chemical,<br />
biological, radiological and nuclear<br />
defense) can also be deployed<br />
through the PLAS on-board network<br />
connection. At present PLAS<br />
is delivered with an IC Realtime<br />
I-Sniper nighttime camera (.0 lux<br />
light handling capability).<br />
Communications are sent by<br />
point-to-multipoint 5.8 GHz or<br />
public safety frequencies. Transmission<br />
is sent via IP connectivity<br />
(as opposed to traditional remote<br />
control) which makes it possible<br />
for one operator to control multiple<br />
PLAS systems at once (for example<br />
a wide variety of control commands,<br />
or pan, tilt, and zoom of cameras,<br />
etc.). This makes the PLAS system<br />
unlike other aerial platforms.<br />
The PLAS balloon system is both<br />
industrial- and tactical-grade. Designed<br />
by Altametry Aerostatic<br />
Engineering located in Miami, FL,<br />
it is comprised of an inner bladder
and outer balloon that has a 6-foot<br />
circumference. Depending on the<br />
mission, the balloon is filled with<br />
either hydrogen or helium.<br />
Ideal applications for PLAS include<br />
border protection; emergency<br />
management / natural disasters and<br />
security, public safety, and intrusion<br />
defense at large-scale special events.<br />
PLAS was recently flown at the<br />
Hard Rock Stadium in Miami Gardens;<br />
the Homestead Motor Speedway<br />
Sprint Cup; the Fort<br />
Lauderdale international<br />
Boat Show; the Daytona<br />
500 race and ULTRA Festival<br />
in South Beach, FL.<br />
At the 2017 ISC West<br />
tradeshow, PLAS will be<br />
demonstrated live from<br />
above IC Realtime’s exhibit<br />
booth (#16059).<br />
Parties interested in<br />
PLAS can contact IC Realtime<br />
Government Practice<br />
and Law Enforcement<br />
Division Director Robert<br />
Mitchell at robertmitchell@icrealtime.com<br />
or<br />
631.455.2001.<br />
About IC Realtime<br />
Established in 2006, IC<br />
Realtime is an Americanowned<br />
and operated digital<br />
surveillance and technology<br />
product innovator and<br />
manufacturer that serves<br />
many facets of the government, military,<br />
commercial and residential<br />
channels. The company’s mission<br />
statement is to innovate, deliver and<br />
support global video technology.<br />
IC Realtime’s technological breakthroughs<br />
include pioneering the<br />
introduction of the Cloud Video<br />
Recorder and most recently the<br />
ground-breaking IC720 360° x 360°<br />
situational awareness video surveillance<br />
camera. The company is also<br />
11<br />
a strong supporter of the UL2802<br />
performance testing standard for<br />
camera image quality.<br />
In the 2012 - 2016 CEPro Magazine<br />
CE Pro 100 Brand Analysis, IC<br />
Realtime ranked as #1 IP camera /<br />
surveillance brand. IC Realtime is<br />
part of parent / holding company IC<br />
Real Tech, formed in 2014. www.<br />
icrealtime.com, www.twitter.com/<br />
icrealtime, www.facebook.com/increaltimeus<br />
FREE SUBSCRIPTION<br />
SIGN-UP<br />
Monthly Digital Edition<br />
Airport/Seaport Newsletter<br />
Daily Insider Newsletter<br />
Cybersecurity Newsletter<br />
CLICK HERE
North Korea used binary form of “VX”,<br />
“VX2” in assassination of Kim Jong-nam<br />
by George Lane,<br />
Director Chemical Security<br />
Using “VX2”, the binary<br />
form of “VX”, an extremely<br />
toxic nerve agent, in an international<br />
airport in the<br />
heart of Asia, North Korea<br />
sent a very clear message to<br />
the world that it will find and strike<br />
its enemies anywhere in the world.<br />
Kim Jong-nam, half-brother of<br />
North Korean leader Kim Jong-un,<br />
was in Malaysia assassinated with<br />
“VX” found on his face on February<br />
11.<br />
Kim was able to walk home, but<br />
about half an hour later realized<br />
everything seemed to be dark, an<br />
effect of nerve agents causing his<br />
pupils to shrink. He started feeling<br />
hot and, sweating, and took off his<br />
clothes. He had a seizure and died<br />
on the way to hospital. The “V” in<br />
“VX” stands for “venom”, a tribute<br />
to its high potency and a characteristic<br />
ability to penetrate the skin.<br />
The two components of “VX2”<br />
were applied separately and in sequence<br />
by two women at the airport.<br />
Police arrested a Vietnamese and an<br />
Indonesian woman suspected of<br />
smearing the chemicals<br />
on Kim’s face. Authorities<br />
reported that one of<br />
the women suspected of<br />
applying the nerve agent<br />
experienced some physical<br />
symptoms of “VX”<br />
poisoning.<br />
The Indonesian woman<br />
said she was paid $90 to apply<br />
a baby oil-like liquid to his face in<br />
what she believed was a “prank” as<br />
part of a reality show. While both<br />
said they were duped into the attack,<br />
Malaysian police say she and the<br />
other female suspect, a Vietnamese<br />
12<br />
woman who also is in custody, knew<br />
what they were doing because they<br />
were caught washing their hands<br />
immediately after the attack.<br />
In Malaysia’s underworld, these<br />
two “good time girls” admitted they<br />
had worked in massage parlors and<br />
made themselves easy targets for<br />
North Korean agents looking for<br />
women who could assume harmless<br />
identities for the deadly roles for<br />
which they were needed.<br />
Because “VX”<br />
fumes would<br />
have killed the<br />
suspected at-<br />
Image from a CCTV footage of one of the woman at<br />
Image from a CCTV footage appears to show (circled in red) a man purported to be Kim Jong Nam<br />
being accosted by a woman in a white shirt at Kuala Lumpur International Airport.<br />
Image from a CCTV footage appears to show (circled in red) a man purported to be Kim Jong
tackers<br />
tackers even if they had been wearing<br />
gloves, this indicates that “VX2”<br />
was applied as a binary weapon<br />
with two non-fatal components that<br />
would produce “VX” only on the<br />
victim’s face.<br />
North Korea wanted the West to<br />
know what it is capable of, but without<br />
causing mass casualties. They<br />
wanted everyone, especially the<br />
U.S., to know they used “VX”. Doing<br />
it publicly but not killing anyone<br />
else is a very visual way to reveal<br />
that capability and deterrent.<br />
Kim’s assassination is an insult to<br />
China, which had protected him for<br />
years by allowing him to live in the<br />
Chinese territory of Macau. This is<br />
clearly an embarrassment for the<br />
Chinese state security and to a lesser<br />
extent to the Malaysian government.<br />
Kim’s assassination has frayed<br />
relations between North Korea and<br />
Malaysia, which this week recalled<br />
its ambassador from Pyongyang.<br />
After North Korea’s ballistic missile<br />
launch and the assassination of<br />
Kim Jong Nam, China, announced<br />
it would ban all coal imports from<br />
North Korea, and according to CBS<br />
News was preparing for “regime collapse”<br />
in North Korea, and according<br />
to a defense official would “take<br />
the necessary measures to safeguard<br />
national security in the event of the<br />
collapse of the neighboring North Korean<br />
regime”.<br />
The economic impact of suspending<br />
coal imports would be severe<br />
and may force Pyongyang to the<br />
negotiating table. China imported<br />
about $1.89 billion of coal from<br />
North Korea last year, a significant<br />
proportion of the $2.5 billion in total<br />
Chinese imports from North Korea<br />
that year.<br />
Binary nerve agents<br />
In the 1950s, the U.S. Army began<br />
to develop “binary” nerve agent<br />
weapons to provide increased safety<br />
during storage and handling.<br />
In “unitary” agents, the chemicals<br />
were produced together. Because<br />
the nerve agents are highly toxic,<br />
storage, handling, and deployment<br />
13<br />
need to be performed with extreme<br />
caution. Unitary weapons therefore<br />
pose a risk to people who work<br />
with the chemicals. Binary weapon<br />
development began in the 1960s.<br />
Binary weapons involve non-toxic<br />
precursors that can be loaded in<br />
munitions. Once deployed, the precursors<br />
mix and produce the nerve<br />
agent.<br />
“VX and VX2”<br />
“VX2” is the name for “VX” formed<br />
in binary reactions. “VX2”, binary<br />
“VX”, is formed by the reaction of<br />
an organophosphate compound<br />
with Sulfur. The chemicals used to<br />
produce the binary nerve agents
are not chemical agents; however,<br />
“VX” is an extremely toxic organophosphate,<br />
a tasteless and odorless<br />
liquid with an amber-like color that<br />
severely disrupts the body’s nervous<br />
system. Ten milligrams (0.00035 oz)<br />
is fatal through skin contact. “VX” is<br />
far more potent than Sarin, another<br />
well-known nerve agent toxin, but<br />
works in a similar way.<br />
With its high viscosity and low<br />
volatility, “VX” has the texture of<br />
motor oil and can take days or even<br />
weeks to evaporate. This makes<br />
it especially dangerous, providing<br />
an extended persistence in the<br />
environment. It is odorless and<br />
tasteless, and can be distributed as<br />
a liquid, either pure or as a mixture.<br />
Also because of its density<br />
and vapor pressure as motor oil<br />
“VX” is not actually a “nerve gas”,<br />
used to describe Sarin.<br />
However, Sarin itself is a liquid<br />
pesticide and also has high vapor<br />
pressure, so it is not an effective<br />
“nerve gas” by itself. Initially investigators<br />
believe the Sarin used in the<br />
attacks in the 1995 attacks on Tokyo<br />
subways was contaminated with<br />
industrial chemicals. Subsequent<br />
analyses of the Sarin revealed the<br />
presence of a single common industrial<br />
chemical, added to the Sarin as<br />
a binary weapon to reduce the vapor<br />
pressure of the mixture, making<br />
more Sarin evaporate into vapor<br />
phase, making Sarin more effective.<br />
“VX” is an “acetyl cholinesterase<br />
inhibitor”, blocking the function of<br />
the enzyme “acetyl cholinesterase”.<br />
Normally, when a motor neuron<br />
is stimulated, it releases the neurotransmitter<br />
Acetylcholine into<br />
the space between the neuron and<br />
an adjacent muscle cell. When this<br />
Acetylcholine is taken up by the<br />
muscle cell, it stimulates muscle<br />
contraction (attached).<br />
To avoid a state of constant muscle<br />
contraction, the Acetylcholine is<br />
then broken down to non-reactive<br />
substances, Acetic acid and Choline,<br />
by the enzyme acetyl cholinesterase.<br />
“VX” blocks the action of<br />
Acetyl cholinesterase, resulting in<br />
an accumulation of Acetylcholine in<br />
the space between the neuron and<br />
muscle cell, leading to uncontrolled<br />
muscle contraction. This results in<br />
initial violent contractions. Sustained<br />
paralysis of the diaphragm<br />
muscle causes death by asphyxiation.<br />
14<br />
“VX” is the most toxic nerve agent<br />
ever synthesized for which activity<br />
has been independently confirmed.<br />
The median lethal dose (LD50) for<br />
humans is estimated to be about 10<br />
mg (0.00035 oz) through skin contact<br />
and for inhalation is estimated<br />
to be 30–50 mg·min/m3.<br />
Chemists Ranajit Ghosh developed<br />
the VX at the British firm Imperial<br />
Chemical Industries (ICI) in<br />
1952. The discovery occurred when<br />
the chemist was investigating a class<br />
of organophosphate compounds.<br />
Like Gerhard Schrader, who developed<br />
Sarin for I.G. Farben in<br />
Germany in 1932 as a pesticide,<br />
Ghosh found that “VX” was also<br />
an effective pesticide.<br />
In 1954, ICI put “VX” on the<br />
market under the trade name<br />
“Amiton”; however, it was withdrawn<br />
when it was found too<br />
toxic for use. Further commercial<br />
research on similar compounds<br />
ceased in 1955 when its lethality to<br />
humans was discovered. The toxicity<br />
did not go unnoticed, and samples<br />
of “VX” were sent to the British<br />
Armed Forces for evaluation. After<br />
the evaluation was complete, several<br />
members of this class of compounds<br />
became a new group of nerve agents,<br />
the “V agents”. The U.S. produced<br />
large amounts of “VX” in 1961. The<br />
name is a contraction of the words<br />
“venomous agent X”.
Making microgrids work: send in<br />
the <strong>Mar</strong>ines?<br />
By J. Michael Barrett,<br />
Center for Homeland<br />
Security and Resilience<br />
For several decades now<br />
electrical power experts<br />
have been making increasingly<br />
vocal statements<br />
about the utility and significant<br />
potential advantages of embracing<br />
localized power generation and distribution<br />
using microgrids, which<br />
are essentially miniaturized, selfcontained<br />
power grids serving a<br />
discrete set of users.<br />
Crucially, microgrids are small<br />
enough to offer a more manageable<br />
model for ensuring a stable<br />
and more resilient system, and they<br />
can also make the most of emergent<br />
technologies and the latest advances<br />
in distributed generation sources<br />
(such as solar, wind, etc.) while also<br />
spreading costs and sharing assets<br />
on a manageable scale.<br />
This means they could play a major<br />
role in the advent of the so-called<br />
smart grid as well as help to address<br />
a raft of growing cyber security<br />
threats against existing critical infrastructure.<br />
But while the technology<br />
is proven and workable business<br />
cases can be made,<br />
there nonetheless seems to<br />
be something holding back<br />
the concept from truly taking<br />
root. Is it time to send<br />
in the <strong>Mar</strong>ines?<br />
Ok, so not the <strong>Mar</strong>ines<br />
per se, but rather of the<br />
military more broadly, specifically<br />
by harnessing the Department of<br />
Defense’s operational necessity for<br />
energy surety and its enormous<br />
buying power? In other words, even<br />
though military, commercial, civic,<br />
scientific, industrial and other communities<br />
interested in the great potential<br />
of microgrids need to assess<br />
the practical, real-world benefits<br />
and associated costs and trade-offs<br />
involved in a smart, modern and resilient<br />
microgrid project, someone<br />
has to take the first step and help<br />
develop the market.<br />
Could the military lead the way by<br />
showing how cooperation, financing,<br />
planning and shared responsibility<br />
with the local community can<br />
be leveraged to strengthen the power<br />
grid for communities where vital<br />
national security functions overlap<br />
with civilian communities?<br />
If the resistance to microgrid<br />
15<br />
adoption is related mostly to the<br />
difficulty of overcoming marketplace<br />
inertia, is there a way that embracing<br />
the energy surety aspects<br />
of microgrids could make the Department<br />
of Defense more resilient<br />
against power supply disruptions<br />
while also harnessing the power of<br />
Public-Private Partnerships to help<br />
foster the nascent microgrid industry?<br />
This would serve a clear national<br />
security imperative as well as<br />
support economic growth in the important<br />
arena of tailored microgrids<br />
serving specific end-users.<br />
In practical terms, microgrids are<br />
best suited for locations servicing<br />
a discrete user base with relatively<br />
high energy needs and a recognized<br />
emphasis on energy surety. This includes<br />
users such as military bases,<br />
air and sea ports, manufacturing industrial<br />
parks, and research universities.<br />
For example, consider the following<br />
hypothetical set of end-users<br />
prevalent at multiple large military<br />
installations:<br />
• A military installation needing<br />
a high degree of energy security<br />
and resilience, but which also has<br />
available lands for locating solar<br />
arrays;
• A technology research park that<br />
requires unusually precise voltage<br />
and amperage control for use<br />
in sensitive research systems; and<br />
• A large-scale computer server<br />
farm in need of energy security<br />
and resilience while able to harness<br />
significant amounts of the<br />
heat created during the power<br />
generation process to drive<br />
always-on steam-powered air<br />
conditioning units, thereby significantly<br />
increasing overall efficiency<br />
of the microgrid system.<br />
At Fort Carson, Colo., the Army partnered with a local energy provider to build a photovoltaic solar<br />
array on top of a closed landfill. The White Sands Missile Range project in New Mexico, awarded<br />
last December, will provide the Army with 4.44-megawatts of installed photovoltaic capacity saving<br />
10 million kilowatt hours of electricity and $930,000 annually. When finished, the White Sands<br />
project will be the largest renewable energy projectin the Army, more than double the size of this<br />
two-megawatt array at Fort Carson (Photo: U.S. Army)<br />
16<br />
By sharing resources and harnessing<br />
shared assets as well as the<br />
shared need for efficient, stable and<br />
reliable energy in that specific location,<br />
a microgrid developed as a<br />
public-private partnership might<br />
yield great advantages at reasonable<br />
cost, while also helping to get the<br />
market past the ‘tipping point’ beyond<br />
which the microgrid market<br />
can finally emerge and service the<br />
growing need for electrical power<br />
that is more specifically tailored<br />
to the needs and desires of various<br />
end-users.<br />
As with any complex undertaking<br />
there will be many parties ultimately<br />
required to achieve successful<br />
outcomes. For example, the<br />
Department of Energy will need to<br />
continue to support research projects<br />
and advanced design studies<br />
on microgrids around the country,<br />
including through its Grid Modernization<br />
Initiative. And the private<br />
sector as well as an engaged citizenry<br />
are obvious and essential elements<br />
of any effective public-private<br />
partnership effort.<br />
But what is most essential at this<br />
stage seems to be an entity with the<br />
motivation to make the market potential<br />
into reality. Given its relative<br />
size as a potential market driver this<br />
important role could and should be<br />
played by the US military. Indeed,<br />
the DoD uniquely fits the bill, for it<br />
is both a major consumer of energy<br />
and has many specific installations<br />
and functions with a compelling operational<br />
need to ensure resilient access<br />
to electrical power.<br />
Microgrids will play an important<br />
role in the future of U.S. and global<br />
electrical power systems. And, as it<br />
turns out, the DoD is already the<br />
de facto market leader. As recently<br />
observed by industry insider John<br />
Carroll, “The military is the technology<br />
leader. Every utility is looking at<br />
the Department of Defense for how<br />
they are deploying microgrids.”<br />
The next practical step is for the<br />
military to shift from ‘market leader’<br />
More on page 41
Aerojet Rocketdyne supports ULA launch of Wideband<br />
Global SATCOM spacecraft for the U.S. Military<br />
SACRAMENTO, CA, <strong>Mar</strong>ch 18,<br />
2017 (GLOBE NEWSWIRE) –<br />
Aerojet Rocketdyne, Inc., a subsidiary<br />
of Aerojet Rocketdyne Holdings,<br />
Inc. (NYSE:AJRD), played a<br />
major role in successfully launching<br />
and placing the ninth Wideband<br />
Global SATCOM (WGS-9) spacecraft<br />
into orbit for the U.S. military.<br />
The mission was launched from<br />
Cape Canaveral Air Force Station<br />
in Florida aboard a United<br />
Launch Alliance (ULA) Delta<br />
IV rocket. Aerojet Rocketdyne<br />
propulsion systems included<br />
the RS-68A booster engine, the<br />
RL10B-2 upper-stage engine, 14<br />
helium pressurization tanks, and<br />
a 100 lbf bipropellant apogeeraising<br />
engine aboard the WGS-<br />
9 spacecraft.<br />
“The WGS satellites provide critical<br />
communication capabilities for<br />
our nation’s warfighters,” said Aerojet<br />
Rocketdyne CEO and President<br />
Eileen Drake. “We are honored that<br />
our propulsion systems are called<br />
upon to place these critical payloads<br />
into orbit – payloads that will help<br />
protect our nation and allied forces.”<br />
Aerojet Rocketdyne’s role in the<br />
launch began when a single RS-68A<br />
engine ignited to boost the Delta<br />
IV off the pad, providing 702,000<br />
pounds of lift-off thrust. The RS-<br />
68A is the world’s most powerful<br />
liquid hydrogen/liquid oxygen engine.<br />
The RS-68 family of engines<br />
has now flown 35 commercial and<br />
government missions with 100 percent<br />
mission success.<br />
17<br />
After the upper stage separated<br />
from the launch vehicle, a single<br />
RL10B-2 upper-stage engine ignited<br />
to place the payload into orbit. The<br />
RL10B-2 delivers 24,750 pounds of<br />
thrust to power the Delta IV upper<br />
stage, using cryogenic liquid hydrogen<br />
and liquid oxygen propellants.<br />
The RL10B-2 was developed from<br />
the RL10 family of upper-stage engines,<br />
which has accumulated one<br />
of the most impressive track records<br />
of accomplishments in the<br />
history of space propulsion. More<br />
than 475 RL10 engines have supported<br />
launches over the last 50<br />
years, playing a vital role in placing<br />
military, government and commercial<br />
satellites into orbit, and powering<br />
scientific space probes on every<br />
interplanetary mission in our solar<br />
system. ARDÉ, a subsidiary of<br />
Aerojet Rocketdyne based in<br />
New Jersey, manufactures the<br />
pressure vessels on the first and<br />
second stages of the launch vehicle.<br />
Once separated from the<br />
launch vehicle, WGS-9 will perform<br />
multiple burns on Aerojet<br />
Rocketdyne’s High Performance<br />
Apogee Thruster (HiPAT) rocket<br />
engine to complete the orbit raising<br />
from Geosynchronous Transfer<br />
Orbit to its final geosynchronous<br />
orbital position. The HiPAT rocket<br />
engine has a 100 percent mission<br />
success track record spanning over<br />
115 missions, including all WGS<br />
spacecraft.<br />
The Boeing-built WGS satellites<br />
provide increased military communications<br />
capabilities for U.S. and<br />
More on page 41
Bipartisan bill supports Department of Defense<br />
Cyber Scholarships<br />
WASHINGTON, D.C. – Congressman<br />
Jim Langevin (D-RI), joined<br />
by Representatives John Ratcliffe<br />
(R-TX), Pete Aguilar (D-CA), Ted<br />
W. Lieu (D-CA), Rick Allen (R-<br />
GA), and Hank Johnson (D-GA),<br />
today introduced the Department<br />
of Defense (DOD) Cyber Scholarship<br />
Program Act of 2017, legislation that<br />
would improve the cybersecurity<br />
workforce pipeline by reinvigorating<br />
and improving an existing DOD<br />
scholarship program for students<br />
pursuing degrees in cybersecurity<br />
fields. The bill is the House companion<br />
to S. 592, introduced by Senators<br />
Tim Kaine (D-VA), David Perdue<br />
(R-GA), and Mike Rounds (R-SD).<br />
“The Information Assurance<br />
Scholarship Program (IASP) has<br />
boosted the nation’s cyber forces<br />
through scholarships and grant opportunities<br />
at colleges and universities<br />
across the country, and has<br />
strengthened the Department of<br />
Defense as a result,” said Langevin,<br />
the co-founder and co-chair of the<br />
Congressional Cybersecurity Caucus,<br />
who is also a senior member<br />
of the House Armed Services and<br />
Homeland Security Committees.<br />
“I have been a longtime supporter<br />
of these types of initiatives<br />
across the whole of<br />
government, and it is imperative<br />
we reinvigorate<br />
this program, which has<br />
done so much good for<br />
our superiority in cyberspace.”<br />
The DOD Cyber<br />
Scholarship Program<br />
Act would rename the<br />
IASP as the DOD Cyber<br />
Scholarship Program, expand<br />
scholarships to students pursuing<br />
Associate’s Degrees, and authorize<br />
the scholarship program to receive<br />
$10 million in Fiscal Year 2018. Due<br />
to budget constraints, IASP stopped<br />
recruiting new students in 2013,<br />
starving the Department of needed<br />
cyber talent and increasing the difficulty<br />
of recruiting skilled professionals<br />
into government positions.<br />
“America needs the best and<br />
brightest to tackle the cybersecurity<br />
challenges we’re confronted<br />
with each day. Step one is making<br />
cybersecurity service to the nation<br />
more attractive. This bill increases<br />
educational opportunities for those<br />
who can help bolster United States’<br />
own cyber workforce, which will<br />
18<br />
Congressman<br />
Jim Langevin<br />
strengthen our ability to<br />
face growing cybersecurity<br />
challenges both now<br />
and moving forward,”<br />
said Ratcliffe.<br />
“The strength of our<br />
national security is dependent<br />
on the investments<br />
we put into it.<br />
With the rapid advances<br />
we’ve seen in cyberwarfare,<br />
having a trained<br />
and prepared workforce is essential<br />
to protecting the homeland,” said<br />
Aguilar.<br />
“I am pleased to co-lead the bipartisan<br />
DOD Cyber Scholarship<br />
Program Act to provide $10 million<br />
in scholarship funds to aspiring cybersecurity<br />
students. As a Computer<br />
Science major myself, I am well<br />
aware of the threats facing our nation<br />
in the cybersecurity area. The<br />
DOD needs to have the best and<br />
brightest cybersecurity professionals<br />
with eager minds ready to put<br />
their education to work securing the<br />
nation’s military weapons systems<br />
and communication networks,” said<br />
Lieu.<br />
More on page 41
Border Security and Immigration<br />
Trump scapegoats immigrants with creation<br />
of “Office of Victims of Immigration and Crime<br />
Engagement”<br />
President Trump stated that he has<br />
“ordered the Department of Homeland<br />
Security to create an office to<br />
serve American victims during his<br />
Joint Address to congress. The office<br />
is called VOICE – Victims of Immigration<br />
Crime Engagement. Any<br />
victim of crime deserves acknowledgement<br />
and sympathy, and crime<br />
is an issue that must be taken seriously.<br />
However, the emphasis on victims<br />
of immigrant crimes is problematic.<br />
It only serves to scapegoat and demonize<br />
immigrants even though<br />
the data clearly shows that immigrants,<br />
including unauthorized immigrants,<br />
are less likely than nativeborn<br />
Americans to commit crimes.<br />
The creation of this office had been<br />
included in the interior enforcement<br />
Executive Order that was signed in<br />
January, and in the Department of<br />
Homeland Security (DHS) memo<br />
implementing the Executive Order.<br />
According to the memo, this office<br />
is to be a “programmatic liaison between<br />
ICE and the known victims<br />
of crime committed by removable<br />
aliens,” and will ensure<br />
that victims are<br />
provided information<br />
about the offender<br />
such as immigration<br />
status and<br />
custody status. In<br />
addition to creating<br />
the VOICE office,<br />
the administration<br />
has ordered monthly public reports<br />
on immigrants who have committed<br />
crimes and any local jurisdictions<br />
that release them from custody.<br />
VOICE raises many concerns:<br />
1. Efforts like VOICE may create<br />
a climate of discrimination, suspicion,<br />
and hatred against all immigrants,<br />
and will embolden antiimmigrant<br />
groups.<br />
“It will lead to more harassment,<br />
more hate crimes, more bullying,<br />
and more discrimination against<br />
anybody who looks like he may be<br />
an immigrant,” stated Frank Sharry<br />
of America’s Voice.<br />
The last year has seen an increase<br />
in hate groups, according to the<br />
19<br />
Photo: Elvert Barne<br />
Southern Poverty Law Center, and<br />
very recently several likely hate<br />
crimes have made headlines. In<br />
February an Indian immigrant was<br />
killed by an American man who<br />
thought he was of Middle Eastern<br />
descent and told him to “get out of<br />
my country.” Even more recently, a<br />
Sikh man was shot in Washington<br />
state after being told “Go back to<br />
your own country.”<br />
2. The money going to VOICE<br />
could be better spent to help victims.<br />
In response to the President’s announcement,<br />
the National Center<br />
for the Victims of Crime said that<br />
More on page 26
Border Security and Immigration<br />
This immigration enforcement program has a troubled<br />
history, and Trump wants to restart it<br />
By Michele Waslin<br />
20<br />
Photo: cisci1970<br />
Buried inside the interior enforcement<br />
Executive Order issued by<br />
President Trump in January are the<br />
Administration’s plans to revive the<br />
287(g) program. This is concerning<br />
because the program has experienced<br />
intense criticism over the<br />
years, and efforts to ramp up this<br />
program should be viewed with extreme<br />
caution and skepticism.<br />
The 287(g) program, named for<br />
the section of the law that authorizes<br />
it, allows the Department of<br />
Homeland Security (DHS) to enter<br />
into formal collaborations with state<br />
and local law enforcement agencies<br />
to deputize officers to enforce federal<br />
immigration laws.<br />
While created in 1996, the first<br />
collaboration was not formalized<br />
until 2002 when the state of Florida<br />
became the first 287(g) jurisdiction.<br />
Several localities considered<br />
the program before then, but did<br />
not follow through after community<br />
groups expressed concerns about<br />
the impact of local enforcement of<br />
federal immigration laws. The Bush<br />
Administration encouraged participation<br />
in the 287(g) program as<br />
part of its post-9/11 immigration<br />
enforcement strategy. It was touted<br />
as a “force multiplier” that allowed<br />
Immigration and Customs Enforcement<br />
(ICE) to expand its reach with<br />
the help of other law enforcement<br />
agencies. The program grew quickly<br />
and hit its height in mid-2000s with<br />
more than 70 signed Memorandums<br />
of Agreements.<br />
However, there were serious criticisms<br />
of the 287(g) program, including<br />
the high cost to localities.<br />
The federal government does not<br />
cover the cost of salaries, overtime,<br />
or other costs associated with the<br />
287(g) program and studies have<br />
found that localities have spent millions<br />
of local dollars to implement<br />
it.<br />
In fact, in February 2017, Sheriff<br />
Ed Gonzalez announced that Harris<br />
County, Texas would terminate its<br />
287(g) agreement. Gonzalez noted<br />
that the decision was about resource<br />
allocation and that he would put the<br />
$675,000 spent by the county on the<br />
287 (g) program toward improving<br />
clearance rates of major crimes and<br />
other priorities.<br />
There have also been questions<br />
about how effective it is in targeting<br />
serious threats to public safety.<br />
An extensive study by the Migration<br />
Policy Institute (MPI) found that<br />
the 287(g) program did not target<br />
More on page 26
Trump’s immigration remarks at Joint Session<br />
of Congress once again packed with inaccurate<br />
statements and false blaming of immigrants<br />
This week, President Trump gave<br />
an address to a joint session of<br />
Congress where he continued his<br />
divisive, inaccurate rhetoric on immigration.<br />
Some analysts have said<br />
Trump moderated his tone in this<br />
speech, but in reality Trump isn’t<br />
shifting from his hard-line immigration<br />
policies. In his speech, he<br />
continued to falsely blaming immigrants<br />
for the underlying cause for<br />
many issues our country faces.<br />
Below are five statements from<br />
President Trump’s Joint Address<br />
that need to be corrected and explained.<br />
1. Trump claimed that we’ve left<br />
“our own borders wide open for<br />
anyone to cross.”<br />
This is categorically false Since<br />
the last major overhaul of the U.S.<br />
immigration system in 1986, the<br />
federal government has spent an<br />
estimated $263 billion on immigration<br />
and border enforcement. Currently,<br />
the number of border and interior<br />
enforcement personnel stands<br />
at more than 49,000. The number<br />
of U.S. Border Patrol agents nearly<br />
doubled from Fiscal Year (FY) 2003<br />
to FY 2016 with Border Patrol now<br />
required to have a record 21,370<br />
agents. Additionally, the number of<br />
Immigration and Customs Enforcement<br />
(ICE) agents devoted to its office<br />
of Enforcement and Removal<br />
Operations (ERO) nearly tripled<br />
from FY 2003 to FY 2016.<br />
2. Trump said that immigrants<br />
aren’t contributing to our economy<br />
and instead are “costing the<br />
country billions.”<br />
Once again, Trump is incorrect.<br />
The study Trump cited and misconstrued<br />
was conducted by the National<br />
Academies of Sciences (NAS),<br />
Engineering, and Medicine. The<br />
same report flatly states found that<br />
immigrants have “little to no negative<br />
effects on the overall wages or<br />
21<br />
Photo: C-SPAN<br />
employment of native-born workers<br />
in the long term.” The NAS study<br />
also finds that immigrant workers<br />
expand the size of the U.S. economy<br />
by an estimated 11 percent annually,<br />
which translates out to $2 trillion in<br />
2016. Further, the children of immigrants<br />
were found to be the largest<br />
net fiscal contributors among any<br />
group, native or foreign-born, creating<br />
significant economic benefits<br />
for every American.<br />
3. Trump said that the government<br />
is “removing gang members, drug<br />
dealers and criminals that threaten<br />
our communities and prey on<br />
our citizens.”<br />
Despite the rhetoric, Trump has<br />
complicated immigration enforcement<br />
by making virtually all of the<br />
undocumented population a priority.<br />
The new administration is ignoring<br />
priorities that were put into<br />
place by the Obama Administration<br />
as a way to manage limited law enforcement<br />
resources and prioritize<br />
those who pose a threat to public<br />
safety and national security. The<br />
More on page 27
Border Security and Immigration<br />
Second “Muslim Ban” meets<br />
renewed litigation<br />
By <strong>Mar</strong>y Kenney<br />
In the week following President<br />
Trump’s issuance of a second travel<br />
ban targeting six Muslim-majority<br />
countries, several states and a number<br />
of immigrant rights groups immediately<br />
returned to federal courts<br />
throughout the country to urge that<br />
this ban, like the first, be enjoined.<br />
Trump’s initial Muslim travel ban,<br />
an Executive Order issued on January<br />
27, targeted Iran, Iraq, Libya,<br />
Somalia, Sudan, Syria, and Yemen.<br />
On February 2, a Seattle district<br />
court judge enjoined this order<br />
nationally in the case Washington<br />
v. Trump. Deriding this decision,<br />
Trump immediately asked the Ninth<br />
Circuit Court of Appeals to stay the<br />
injunction, a request which the appeals<br />
court rejected.<br />
For weeks after this, Trump and<br />
his close advisors indicated that a<br />
second Executive Order would be<br />
issued soon. They made clear that<br />
this second Order would “maintain<br />
the same basic policy outcome as<br />
the first.” True to their word, this is<br />
precisely what it attempts to do. In<br />
particular, the second travel ban,<br />
which is scheduled to take effect on<br />
<strong>Mar</strong>ch 16, retains two key aspects<br />
of the earlier one. First, it reinstates<br />
a 90-day ban on issuance of visas<br />
to nationals of six of the originally<br />
targeted countries, thus barring<br />
their entry into the United States.<br />
Iraq is the only country taken off the<br />
original list. Moreover, because it includes<br />
a complex, multi-step process<br />
for determining whether each of the<br />
targeted countries satisfies certain<br />
as-yet undetermined “informationsharing”<br />
capabilities, the 90 days<br />
almost certainly will be extended<br />
for an indefinite period for most if<br />
not all six countries. Second, it also<br />
reinstates the 120-day suspension<br />
on refugee processing contained in<br />
the first Order, eliminating only the<br />
earlier, indefinite ban on processing<br />
Syrian refugees.<br />
Significantly, both a ban on visa<br />
issuance and a suspension of refugee<br />
processing were included in the<br />
first Order and were enjoined by<br />
the Seattle district court. The proper<br />
method for seeking a modification<br />
of an injunction is to either request<br />
a reconsideration from the court<br />
that issued the injunction—which<br />
Trump tried and lost—or to appeal<br />
the injunction to the court of<br />
appeals. Within days of issuing the<br />
second Executive Order, Trump<br />
dismissed his pending Ninth Circuit<br />
appeal of the injunction, thus closing<br />
this second proper avenue for<br />
review. As the States of Washington<br />
22<br />
Photo: Geoff Livingston<br />
and Minnesota argue in response to<br />
the second Order in Washington v.<br />
Trump, the federal government is attempting<br />
to evade the injunction by<br />
improperly repackaging previously<br />
enjoined conduct as a new Executive<br />
Order.<br />
Other lawsuits also have renewed<br />
their challenges to the travel bans<br />
in response to the second Executive<br />
Order. Hawaii was the first, followed<br />
soon after by the American Immigration<br />
Council, which on Friday<br />
filed an amended complaint, a new<br />
request for injunctive relief, and a<br />
new motion class certification in Ali<br />
v. Trump. The plaintiffs in these and<br />
the other cases updated this past<br />
week make a strong showing that<br />
the second order continues the unlawful<br />
discrimination against Muslims<br />
contained in the first Order,<br />
and must be rejected on this basis.
These changes may keep Asylum seekers<br />
from getting their day in court<br />
By Katie Shepherd<br />
Effective February 27, 2017, new<br />
changes to the asylum screening<br />
process could lead to an increased<br />
number of deportations of asylumseekers<br />
who fear persecution upon<br />
return to their home country.<br />
On February 13, 2017, U.S. Citizenship<br />
and Immigration Services<br />
(USCIS) revised its Asylum Division<br />
Officer Training Course (ADOTC)<br />
lesson plans on how to assess an<br />
asylum seeker’s credible and reasonable<br />
fear of persecution or torture.<br />
The lesson plans were revised to be<br />
consistent with the January 25, 2017<br />
Executive Order on border security<br />
and immigration enforcement and<br />
provide guidelines to the asylum officers<br />
when conducting credible fear<br />
interviews (for those at the border<br />
or port of entry who were never previously<br />
deported) and reasonable<br />
fear interviews (for those who were<br />
previously order deported but who<br />
later seek asylum).<br />
The changes to the lesson plans are<br />
significant and may cause the denial<br />
rate to skyrocket, in which case<br />
thousands of asylum seekers would<br />
be wrongfully denied a meaningful<br />
day in court . Not only does the new<br />
guidance provide asylum officers<br />
with greater discretion to deny an<br />
applicant for reasons which may be<br />
out of the applicant’s control, but the<br />
applicant will essentially be forced<br />
to undergo a full asylum hearing<br />
with none of the safeguards in place<br />
to ensure a meaningful opportunity<br />
to present a claim for relief.<br />
Before the changes, recent arrivals<br />
to the U.S. subject to expedited<br />
removal were forced to undergo a<br />
fear screening just days after traversing<br />
hundreds of miles, sometimes<br />
by foot. Some were separated<br />
from loved ones at the border and<br />
processed by U.S. Customs and Border<br />
Protection<br />
(CBP) in a<br />
language they<br />
did not understand;<br />
many<br />
were detained<br />
for long hours<br />
or days in a<br />
cold, sterile<br />
facility, and,<br />
when the time<br />
came for their<br />
23<br />
fear interview with an Asylum Officer,<br />
they often had great difficulty<br />
articulating their story due to medical<br />
problems, psychological trauma,<br />
competency issues, or having their<br />
children with them listening in. In<br />
short, the odds were already stacked<br />
against them. The revised lesson<br />
plans create additional potential<br />
hurdles to those seeking humanitarian<br />
relief. Only time will tell if the<br />
revisions will lead to higher rates of<br />
deportation of asylum seekers with<br />
strong claims for relief.<br />
Now, under the new instructions,<br />
applicants in the credible and reasonable<br />
fear interview processes are<br />
required to meet a higher standard<br />
More on page 28
Border Security and Immigration<br />
Homeland Security unions testify in support of more<br />
staff but not a border “wall”<br />
By Joshua Breisblatt<br />
As part of the President’s immigration<br />
executive order on Border Security<br />
and Immigration Enforcement<br />
Improvements the Department of<br />
Homeland Security (DHS) was directed<br />
to hire 5,000 additional<br />
border patrol agents and 10,000<br />
additional Immigration and Customs<br />
Enforcement (ICE) officers.<br />
With record numbers of ICE officers<br />
and Border Patrol agents<br />
already in place, it is unclear how<br />
or why this additional hiring is<br />
needed. This week, the Senate<br />
Homeland Security and Government<br />
Affairs Committee held a<br />
hearing to discuss these additions<br />
with DHS union representatives.<br />
First, Brandon Judd, President of<br />
the National Border Patrol Council<br />
which endorsed the President,<br />
parted ways with him when he said,<br />
“We do not need a wall along the<br />
entire 2,000 miles of border.” In an<br />
interview after the 2016 election he<br />
went on to say, “If I were to quantify<br />
an actual number, I would say that<br />
we need about 30 percent. Thirty<br />
percent of our border has to have an<br />
Chris Crane, head of the National Immigration<br />
and Customs Enforcement Council<br />
actual fence [or] wall.” However according<br />
to the most recent information<br />
from DHS, there is already 650<br />
miles of fencing which makes up<br />
more than 30 percent of the 2,000<br />
mile border.<br />
With respect to staffing, Judd discussed<br />
how additions are needed<br />
but that the agency faces hiring and<br />
funding challenges. Border Patrol is<br />
required to have 21,370 agents however<br />
they currently are at 19,627,<br />
over 1,700 agents below the required<br />
levels. Border Patrol has had significant<br />
issues with hiring, low morale<br />
and high attrition rates, making it<br />
hard to increase staff quickly even<br />
24<br />
if additional funds from Congress<br />
materialize. Yet Judd suggested in<br />
the hearing that pay needs to be increased<br />
and the current polygraph<br />
requirement need to not be so stringent<br />
because two-thirds of applicants<br />
fail the test.<br />
However, after Border Patrol<br />
staffing doubled in the early 2000s,<br />
which has led to it being considered<br />
“America’s most out-ofcontrol<br />
law enforcement agency,”<br />
Congress passed the “Anti-Border<br />
Corruption Act” in 2010 mandating<br />
polygraph exams for border<br />
patrol agents. Former head of CBP<br />
Internal affairs, James Tomsheck<br />
has noted that changing the polygraph<br />
requirement will create new<br />
corruption issues.<br />
Antony Reardon, the President<br />
of the National Treasury Employees<br />
Union, which represents over 25,000<br />
Customs and Border Protection officers<br />
stationed at the nation’s air,<br />
land and seaports of entry also testified.<br />
He stated that even though the<br />
Administration has not asked for it,<br />
CBP officers at ports of entry have<br />
1,400 open positions and need 2,100<br />
More on page 28
America’s treatment of asylum seekers<br />
reviewed by regional human rights body<br />
By Karolina Walters<br />
The Inter-American Commission<br />
on Human Rights (IACHR)<br />
heard testimony today about<br />
policies that prevent access to<br />
the U.S. asylum process for those<br />
fleeing grave danger in their<br />
home countries.<br />
U.S. law guarantees the right<br />
to seek asylum to all who flee persecution<br />
and arrive at our border<br />
looking for protection. And yet, the<br />
testimony heard in Washington,<br />
D.C. today demonstrated that U.S.<br />
officials regularly deny individuals<br />
this right. Notably, no one from the<br />
U.S. government attended to refute<br />
the claims.<br />
The hearing opened with testimony<br />
highlighting the barriers put<br />
in place during asylum seekers’<br />
initial encounters with Customs<br />
and Border Protection (CBP) officers<br />
at ports of entry. The practice<br />
of turning away asylum seekers has<br />
become all too common and was<br />
recently brought to the attention of<br />
the U.S. government in a complaint.<br />
Despite the evidence presented and<br />
media coverage, this practice seems<br />
to be on the rise. According to one<br />
asylum seeker recently turned away<br />
by CBP, whose declaration was read<br />
at the hearing:<br />
“I told [the CBP official] that I<br />
wasn’t from here, that I was from<br />
Honduras, and that I wanted asylum.<br />
He told me that there was no<br />
longer asylum for Hondurans. . . . I<br />
pled with him for help and told him<br />
that I couldn’t return to Honduras.<br />
I started to explain why I couldn’t<br />
return and what I was fleeing from<br />
but he interrupted me and said that<br />
everyone comes with the same story,<br />
that he couldn’t help me . . .”<br />
In addition, Nicole Ramos of Al<br />
Otro Lado described her experiences<br />
witnessing CBP officers attempting<br />
to turn away and deny access to<br />
the asylum process to sixty-eight<br />
25<br />
asylum seekers she escorted to<br />
the San Ysidro port of entry in<br />
Tijuana, Mexico, over a fifteenmonth<br />
period. Daniella Burgi-<br />
Palomino of the Latin American<br />
Working Group testified about<br />
the extreme violence and impunity<br />
in Mexico’s northern border<br />
region, which awaits asylum<br />
seekers turned away at ports of<br />
entry, subjecting them to further<br />
danger.<br />
The hearing also covered the horrible<br />
conditions and deplorable<br />
treatment of asylum seekers in CBP<br />
detention facilities, and the negative<br />
effects of detaining asylum seekers<br />
while their claims are pending. Joanna<br />
Williams of the Kino Border<br />
Initiative described her organization’s<br />
work with detained asylum<br />
seekers in Arizona and noted that<br />
CBP officials “willfully ignore and<br />
discourage” asylum applications.<br />
Theodora Simon of the Hope Border<br />
Institute explained that the systematic,<br />
prolonged detention of asylum<br />
seekers ultimately leads some<br />
to withdraw their applications.<br />
At the end of the hearing, Com-<br />
More on page 29
Border Security and Immigration<br />
Trump scapegoats immigrants<br />
with “Office of Victims of Immigration<br />
and Crime Engagement”<br />
Continued from page 19<br />
VOICE is a “poor use of scarce resources<br />
for crime victims and may<br />
actually block victims from exercising<br />
their rights.” They rightly point<br />
out that Trump has promised severe<br />
funding cuts to existing offices<br />
within the Department of Justice<br />
(DOJ) – like the Office for Victims<br />
of Crime and the Office on Violence<br />
Against Women – with proven records<br />
of helping victims.<br />
3. This administration’s policies<br />
interfere with the ability of local<br />
police to fight crime.<br />
Trump has threated to take DOJ<br />
funding away from law enforcement<br />
agencies that have “sanctuary” policies<br />
intended to allow immigrant<br />
victims to come forward and report<br />
crimes without fear of deportation.<br />
Police authorities have stated that<br />
enforcing immigration laws makes<br />
it harder for them to maintain good<br />
community relations and steers<br />
scare resources away from crime<br />
fighting.<br />
4. Trump’s anti-immigrant polices<br />
may interfere with efforts to prosecute<br />
criminals and hold them accountable.<br />
For example, U visas are for victims<br />
of crime who have suffered<br />
substantial mental or physical abuse<br />
and are willing to assist law enforcement<br />
in the investigation or<br />
prosecution of the crime. Since the<br />
election, immigrants and advocates<br />
have been concerned about the future<br />
of the U visa. While eliminating<br />
the visa category would be difficult,<br />
the Trump administration<br />
could slow processing or issue far<br />
fewer visas. Regardless, immigrant<br />
victims may be far more hesitant to<br />
come forward and report crimes.<br />
Immigrants contribute a great<br />
deal to this country. The fact that<br />
some have committed serious<br />
crimes is reprehensible, but it is one<br />
small piece of a complex story. To<br />
counter VOICE, Rep. Jared Polis<br />
launched a database intended to tell<br />
positive stories about immigrants<br />
called SAINT – Saved by American<br />
Immigrants National Taskforce. The<br />
purpose is to collect stories of immigrants<br />
who have performed heroic<br />
or lifesaving acts. In this environment,<br />
telling positive stories about<br />
immigrant contributions is more<br />
important than ever.<br />
26<br />
Immigration enforcement<br />
program has a troubled history,<br />
and Trump wants to restart it<br />
Continued from page 20<br />
serious criminal offenders. In fact,<br />
half of all detainers issued through<br />
the program were on people who<br />
committed misdemeanors and traffic<br />
offenses. MPI also found that jurisdictions<br />
tend to use their 287(g)<br />
authority in different ways. Some<br />
do target serious criminals, while<br />
others operate a “universal” model<br />
designed to deport as many unauthorized<br />
immigrants as possible, regardless<br />
of criminal history.<br />
Critics also identify racial profiling<br />
and pretextual arrests as a serious<br />
problem with the 287(g) program.<br />
The most egregious example<br />
was Sheriff Joe Arpaio of <strong>Mar</strong>icopa<br />
County, Arizona who conducted<br />
sweeps in Latino neighborhoods<br />
and stopped drivers who “looked”<br />
Latino. But similar patterns of racial<br />
profiling have also been found elsewhere.<br />
The DHS Inspector General and<br />
the Government Accountability Office<br />
(GAO) both issued reports on<br />
the 287(g) program and found that<br />
ICE managed the program poorly.<br />
ICE failed to articulate the program’s<br />
objectives and priorities consistently,<br />
did not comply with the express
objectives of the program, and did<br />
not provide sufficient oversight.<br />
In light of these concerns, and<br />
with the rise of the Secure Communities<br />
program, the Obama administration<br />
eventually drew down the<br />
287(g) program. With Secure Communities,<br />
ICE could share information<br />
with local enforcement without<br />
the hassles of directly supervising<br />
local cops.<br />
Now the Trump administration<br />
wants to re-boot 287(g) program.<br />
However, it’s unclear whether Congress<br />
will fund an expanded program.<br />
The upcoming appropriations<br />
season is likely to include a battle<br />
over funding for the program.<br />
While some locals may be open to<br />
the revival of 287(g) program, many<br />
other local jurisdictions are limiting<br />
their cooperation and have restricted<br />
compliance with the federal government’s<br />
immigration detainers.<br />
Therefore, these places are unlikely<br />
to enter into formal agreements of<br />
this kind.<br />
The 287(g) program has a long and<br />
troubled history. States and localities<br />
should take a good, hard look<br />
at its track record before making a<br />
decision to restart this program that<br />
could have a harmful impact on<br />
their communities.<br />
Trump’s immigration remarks<br />
packed with inaccurate statements<br />
Continued from page 21<br />
priorities recognized that there is a<br />
finite budget available for immigration<br />
enforcement, thus making prioritization<br />
important. The approach<br />
now being pursued by the Trump<br />
Administration casts a very wide net<br />
and will result in an aggressive and<br />
unforgiving approach to immigration<br />
enforcement moving forward.<br />
4. Trump believes a merit-based<br />
immigration system will improve<br />
the economy.<br />
The idea of a merit-based system is<br />
not new but it usually has been discussed<br />
as one piece to updating our<br />
immigration system, not the only<br />
piece as discussed in this speech.<br />
At its core, the allocation of points<br />
is not a neutral act, but instead reflects<br />
a political view regarding the<br />
“desired immigrant.” Since the enactment<br />
of the Immigration and<br />
Nationality Act in 1965, legal immigration<br />
to the United States has<br />
been based primarily on the family<br />
ties or the work skills of prospective<br />
immigrants.<br />
The contributions of family-based<br />
immigrants to the U.S. economy, local<br />
communities, and the national<br />
fabric are many. They account for<br />
a significant portion of domestic<br />
27<br />
economic growth, contribute to the<br />
well-being of the current and future<br />
labor force, play a key role in business<br />
development and community<br />
improvement, and are among the<br />
most upwardly mobile segments of<br />
the labor force. And if cutting family-based<br />
immigration becomes part<br />
of a trade-off for a merit-based system,<br />
we would be turning our back<br />
on a centuries’ old tradition of family<br />
members already in the United<br />
States supporting newcomer relatives<br />
by helping them get on their<br />
feet and facilitating their integration.<br />
5. Trump attempted to make the<br />
link between immigrants and<br />
crime through his newly created<br />
office of Victims Of Immigration<br />
Crime Engagement (VOICE).<br />
Despite the implications of this<br />
new office at DHS which seeks to demonize<br />
all immigrants, immigrants<br />
are actually less likely to commit serious<br />
crimes or be behind bars than<br />
the native-born. Additionally, high<br />
rates of immigration are associated<br />
with lower rates of violent crime<br />
and property crime. This holds true<br />
for both legal immigrants and the<br />
unauthorized, regardless of their<br />
country of origin or level of education.
Border Security and Immigration<br />
Changes may keep Asylum seekers<br />
from getting their day in court<br />
Continued from page 23<br />
in proving their identity, and the<br />
asylum officer is required to make<br />
a full and final determination as<br />
to the applicant’s credibility. Previously,<br />
the applicant needed to only<br />
show a “significant possibility” that<br />
the assertions underlying her claim<br />
were credible.<br />
Before these changes were announced,<br />
the lesson plans stated<br />
that making a full assessment of<br />
credibility was the job of the immigration<br />
judge, who the applicant<br />
sees if she passes the asylum officer’s<br />
screening. The asylum officer<br />
was tasked with assessing credibility<br />
only to determine an applicant’s eligibility<br />
for a full asylum hearing in<br />
immigration court. The 2014 lesson<br />
plan states in part (emphasis added):<br />
“Because the credible fear determination<br />
is a screening process, the<br />
asylum officer does not make the final<br />
determination as to whether the<br />
applicant is credible. The immigration<br />
judge makes that determination<br />
in the full hearing on the merits of<br />
the claim.”<br />
The revised plan explicitly states<br />
that the asylum officer should take<br />
into account “the same factors considered<br />
in evaluating credibility in<br />
the affirmative asylum context.” In<br />
short, what this means is that the<br />
applicant will effectively undergo a<br />
full asylum hearing just after arriving<br />
in the United States, with limited<br />
access to counsel while detained<br />
or the ability to obtain evidence or<br />
counseling services that will enable<br />
them to prevail.<br />
Further, an applicant is now required<br />
to credibly establish her<br />
identity by a heightened evidentiary<br />
standard – “preponderance of the<br />
evidence” – which is typically met if<br />
the asylum officer believes the evidence<br />
has more than a 50 percent<br />
likelihood of being true. According<br />
to the revised lesson plan, credible<br />
testimony alone should be enough<br />
to establish identity; however, the<br />
new plans also state that the officer<br />
may “consider information provided<br />
by ICE or … CBP.” Of course<br />
this is problematic because the transcripts<br />
from interviews conducted<br />
by CBP and ICE at the border regularly<br />
contain many errors.<br />
These changes to the asylum process<br />
are likely to have serious consequences<br />
for people facing persecution<br />
in their home countries<br />
and undermine American values<br />
including humanitarian assistance<br />
and due process.<br />
28<br />
Homeland Security unions testify<br />
in support of more staff but not a<br />
border “wall”<br />
Continued from page 24<br />
officers on top that just to meet their<br />
staffing needs. A lack of Officers at<br />
ports of entry can have significant<br />
consequences for the economy with<br />
over $2.2 trillion in imports coming<br />
through the ports every year.<br />
Reardon also noted that much of<br />
the drugs seized come through our<br />
ports of entry, with 600,000 pounds<br />
of drugs seized just last year. Therefore,<br />
if the goal is stop the flow of<br />
narcotics, Congress may want to<br />
fund these positions first and foremost.<br />
Lastly, Chris Crane, the head of<br />
the National Immigration and Customs<br />
Enforcement Council, testified<br />
regarding ICE’s need for additional<br />
staffing. However, he focused more<br />
on issues related to retaliation by<br />
managers against front line agents<br />
and bemoaned the amount of paper<br />
work ICE enforcement officers have<br />
to do as opposed to being out in the<br />
field. There is significant concern<br />
about current ICE immigration enforcement<br />
agents already due to the<br />
dozens who according to the New<br />
York Times have been “charged with<br />
beating people, smuggling drugs<br />
into detention centers, having sex
America’s treatment of asylum<br />
seekers reviewed by regional<br />
human rights body<br />
Continued from page 25<br />
with detainees and accepting bribes<br />
to delay or stop deportations.” The<br />
idea of adding more ICE agents to<br />
an agency who does not even currently<br />
require a polygraph test could<br />
be an invitation for more abuse by<br />
rogue agents.<br />
Members of Congress seemed<br />
sympathetic to the agents needs and<br />
wanted to work with them to fix<br />
morale and other issues with management.<br />
However, it remains to be<br />
seen if Congress will actually spend<br />
the billions of dollars that would be<br />
needed for these staff—especially in<br />
light of the problems related to corruption<br />
and oversight.<br />
missioner <strong>Mar</strong>garette May Macaulay<br />
stated that the Commission<br />
“cannot accept” these violations and<br />
emphasized asylum seekers’ “necessary,<br />
fundamental right to due<br />
process,” and the importance of a<br />
“dignified hearing” and a “fair and<br />
judicious decision.” She also asked<br />
petitioners to provide the Commission<br />
with written guidance about<br />
what the IACHR can do immediately<br />
that would effectively address<br />
these barriers to the U.S. asylum<br />
process.<br />
Nineteen petitioning organizations,<br />
including the American Immigration<br />
Council, the American<br />
Immigration Lawyers Association,<br />
the Women’s Refugee Commission,<br />
and the American Civil Liberties<br />
Union, called on the IACHR to:<br />
• Hold the United States accountable<br />
for policies inhibiting access<br />
to asylum;<br />
• Conduct a site visit to the U.S.-<br />
Mexico border;<br />
• Hold a follow up round-table<br />
dialogue with representatives<br />
of the United States, Mexico, El<br />
Salvador, Guatemala, Haiti and<br />
Honduras, to discuss the on-going<br />
obligations these countries<br />
have to ensure the full rights of<br />
migrants, and the special protections<br />
due to asylum seekers;<br />
• Encourage CBP to address deficiencies<br />
and improve officers’<br />
training, guidelines and practices<br />
and create specific oversight<br />
mechanisms to promote transparency<br />
and investigate complaints,<br />
in order to avoid mistreatment<br />
and abuse of migrants.<br />
Today, the international community<br />
stopped and listened to what is hap-<br />
29<br />
pening at the southern border of the<br />
United States. Isn’t it time policymakers<br />
in the U.S. did the same.<br />
FREE SUBSCRIPTION<br />
SIGN-UP<br />
Monthly Digital Edition<br />
Airport/Seaport Newsletter<br />
Daily Insider Newsletter<br />
Cybersecurity Newsletter<br />
CLICK HERE
<strong>GSN</strong>’s 2017 Airport/Seaport/Border Security Awards<br />
Now Including Cybersecurity Solutions for Airport, Seaport, Border Security <strong>Mar</strong>kets<br />
All Winners in this program are entitled to<br />
a Full-Page Advertisement (8.5” x 9.0”) in<br />
your choice of <strong>GSN</strong>’s Digital Magazine or<br />
Leaderboard in any edition of the Airport,<br />
Seaport, Rail, Border Security Weekly<br />
Newsletter.<br />
NEW IN 2017:<br />
All Finalists are entitled to a Half-Page<br />
Advertisement (8.5” x 4.5”) in your choice<br />
of <strong>GSN</strong>’s Digital Magazine or Leaderboard<br />
in any edition of the Airport, Seaport, Rail,<br />
Border Security Weekly Newsletter.<br />
CLICK HERE TO SUBMIT ENTRIES<br />
Adrian Courtenay<br />
Managing Partner, CEO<br />
Government Security News<br />
917-696-5782<br />
acourtenay@gsnmagazine.com<br />
Steve Bittenbender<br />
Managing Editor<br />
Government Security News<br />
502-552-1450<br />
sbittenbender@gsnmagazine.com<br />
Gerry O’Hara<br />
Designer<br />
OHDesign3<br />
203-249-0626<br />
gerry@ohd3.com
New York Democrats rally to resist voter suppression,<br />
calling for action from NY Governor Cuomo<br />
NEW YORK, NY, 03/19/2017 (read-<br />
Media)—With backing from Common<br />
Cause, New York City elected<br />
officials, unions and grassroots organizations<br />
rallied at Battery Park to<br />
resist voter suppression, calling on<br />
Governor Andrew Cuomo and the<br />
State Legislature to modernize our<br />
elections by funding Early Voting<br />
and Automatic Voter Registration<br />
in the state budget, due April 1st.<br />
Enacting Early Voting would allow<br />
New Yorkers to cast their ballot<br />
at polling locations before the<br />
traditional Election Day. 34 states<br />
already have some form of Early<br />
Voting, leaving New York as one of<br />
only 16 states without any means to<br />
vote early except via absentee ballot.<br />
New York does not have any<br />
form of Automatic Voter Registration<br />
either. Automatically registering<br />
eligible voters encourages civic<br />
participation, and provides a vehicle<br />
for state agencies to efficiently transfer<br />
voter registration information to<br />
the Board of Elections. Outdated<br />
elections is in part why only 29 percent<br />
of the state’s eligible population<br />
voted in 2014, putting New York in<br />
the bottom third nationally.<br />
The rally was co-sponsored by<br />
Common Cause New York, SEIU<br />
32BJ, NY Immigration Coalition,<br />
NYCLU, NY Civic Engagement<br />
Table, TWU 100, Hispanic Federation,<br />
2 hours A Week, Public Citizen,<br />
Citizen Action New York, Citizens<br />
Union, NYC Votes, New York<br />
Working Families, DuBois Bunche<br />
Center For Public Policy, Hugh L.<br />
Carey Institute, NYPIRG, Community<br />
Voices Heard, Women’s City<br />
Club, Make the Road NY, NCAACP<br />
Brooklyn Chapter, Daily<br />
Kos, VOCAL, and the NY<br />
Progressive Action Network.<br />
Featured speakers including<br />
Congressmembers<br />
Jerry Nadler, NYC Comptroller<br />
Scott Stringer, and<br />
Manhattan Borough President<br />
Gale Brewer spoke<br />
about the importance of<br />
modernizing our elections especially<br />
in response to national efforts to<br />
strip voting rights.<br />
“New York has been a bastion of<br />
democracy, and leader of progressive<br />
activism during these difficult<br />
times facing our country,” said Congressman<br />
Jerrold Nadler (D-NY).<br />
“But unfortunately, our state has<br />
not been a leader when it comes to<br />
modernizing our voting systems. It<br />
31<br />
Congressman<br />
Jerrold Nadler (D-NY)<br />
is time to simplify our voting process<br />
and increase voter accessibility,<br />
by adding early voting, automatic<br />
and same-day voter registration,<br />
consolidated primaries and shortened<br />
party registration deadlines.”<br />
“At a time when we need to boost<br />
voter participation, we should make<br />
it easier, not harder, to vote,” said<br />
New York City Comptroller Scott<br />
Stringer. “This is critical to ensuring<br />
accountable and effective<br />
government. New<br />
York’s antiquated voting<br />
laws already lag behind<br />
most of the country. From<br />
early voting to same day<br />
registration, we need to<br />
implement smart reforms<br />
that expand the franchise<br />
and make our democracy<br />
more inclusive. That’s why<br />
we have to speak out against the<br />
President’s fraudulent claims of illegal<br />
voting and resist new barriers<br />
to the ballot.”<br />
“Now is the time for New York<br />
to be an example,” said Manhattan<br />
Borough President Gale A. Brewer.<br />
“Modern voting laws will help<br />
more people vote at a time of renewed<br />
civic participation, and they<br />
will save taxpayers time, money, and
aggravation and reduce barriers to<br />
voting. There’s no good reason we<br />
can’t have early voting and a modernized,<br />
automatic voter registration<br />
system. We just need leaders<br />
in Albany to step up and insist on<br />
these reforms.”<br />
State Senator Brad Hoylman (D-<br />
27) said: “Since the Supreme Court<br />
invalidated part of the Voting Rights<br />
Act in 2013, state legislatures across<br />
the country have worked to disenfranchise<br />
voters at a level not seen<br />
since the Jim Crow era. With just<br />
31 reported cases of voter fraud out<br />
of one billion votes cast between<br />
2004 and 2014, the Trump Administration’s<br />
arguments for a national<br />
voter fraud commission are<br />
not just wrong, they’re dangerous<br />
and misleading. I’m proud to stand<br />
with Common Cause, SEIU, Make<br />
the Road New York and others in<br />
pushing back against voter disenfranchisement,<br />
and look forward to<br />
working with them to enact reforms<br />
that will protect and expand the<br />
right to vote.”<br />
“New York state should be a national<br />
leader in voter rights,” said<br />
Council Member Ben Kallos (D-<br />
5). “Albany must implement voting<br />
reforms like early voting, no-fault<br />
absentee voting and automatic voter<br />
registration this year, because the<br />
health of our democracy depends<br />
on real electoral reform.”<br />
Said Council Member Brad<br />
Lander (D-39): “It really is this<br />
simple: By failing to adopt common-sense<br />
reforms like automatic<br />
voter registration and early voting,<br />
Albany is denying New Yorkers the<br />
right-to-vote. Who benefits? You<br />
know the answer. New data from<br />
2016 election makes it clear. Those<br />
states who care about democracy<br />
and implemented voting reforms<br />
saw big increases in voter turnout.<br />
Sadly, New York State was not on<br />
the list. At this critical moment,<br />
if they care about our democracy,<br />
New York State Legislators will put<br />
these fundamental voting reforms<br />
into the budget, and adopt them this<br />
month.”<br />
“We need to break down the barriers<br />
that keep New Yorkers from<br />
casting their vote and making their<br />
voices heard,” said Hector Figueroa,<br />
President of SEUI 32BJ. “Early voting<br />
and automatic voter registration<br />
are policies that are good for our<br />
state and good for our country. This<br />
vital legislation will expand voting<br />
rights and ensure we have real democracy.”<br />
“With the Trump regime already<br />
broadcasting pernicious lies about<br />
‘voter fraud’ and planning to suppress<br />
the vote nationwide, New York<br />
can show the way forward by fixing<br />
our own broken electoral system<br />
here at home,” said Bill Lipton, New<br />
York State Director of the Working<br />
Families Party. “We urge the<br />
state legislature to include early voting<br />
and automatic voter registration<br />
32<br />
in the budget that will be adopted<br />
by April 1 so that New York can become<br />
a national leader in protecting<br />
and expanding voting rights.”<br />
“Voting is the lifeblood of our democracy<br />
and together we demand<br />
that our elections encourage full<br />
participation by all eligible New<br />
Yorkers,” said Susan Lerner, executive<br />
Director of Common Cause<br />
New York. “We are demonstrating<br />
today to show our elected representatives<br />
that we want voter protection<br />
not voter suppression. It is time to<br />
make essential voting reforms like<br />
Early Voting and Automatic Voter<br />
Registration part of the state budget<br />
that will be adopted by April 1st.”<br />
“New York State must modernize<br />
our electoral process and make it<br />
accessible. Election reform can not<br />
continue to be a talking point for<br />
the NYS legislature. Now is the time<br />
to include early voting and automatic<br />
voter registration in the NYS budget.<br />
We call on the NYS legislature<br />
and Governor Cuomo to ensure that<br />
AVR and early voting are actualized<br />
by April 1,” said Steve Choi, Executive<br />
Director of the New York Immigration<br />
Coalition.<br />
“The fight for women’s suffrage<br />
was started by New Yorkers and<br />
our state was once a leader in advancing<br />
voting rights. But now our<br />
outdated laws severely obstruct our<br />
right to cast a ballot,” said Onida<br />
Coward Mayers, Director of Voter<br />
Assistance at the New York City
Campaign Finance Board. “We<br />
need common sense reforms like<br />
early voting, automatic registration,<br />
same-day registration, and preclearance<br />
of voting regulations to<br />
ensure that no eligible voter in New<br />
York is ever prevented from casting<br />
a ballot that counts.”<br />
Javier H. Valdés, Co-Executive<br />
Director of Make the Road New<br />
York, said, “Immigrant communities<br />
around New York urgently need<br />
Albany’s leaders to expand and defend<br />
voting rights. With the Trump<br />
administration already beginning<br />
its efforts to use lies about our voting<br />
system to justify voter suppression,<br />
it’s more important than ever<br />
that we make it as easy as possible<br />
for New Yorkers to register to vote<br />
and cast their ballots.”<br />
“At the core of all of our national<br />
issues is limited access to voting,<br />
voter suppression and disenfranchisement,”<br />
said Shabd Simon-<br />
Alexander, co-founder, 2 Hours A<br />
Week. “We can complain, march,<br />
call our reps all we want, but unless<br />
we also get to the polls and elect the<br />
right people, nothing will change.<br />
Yet so many people are kept from<br />
voting - either actively, through voter<br />
suppression, or passively, through<br />
arcane laws and complicated and<br />
discouraging registration and voting<br />
processes. So our fight is clear:<br />
we must make voting not only legal,<br />
but also accessible to all New Yorkers.”<br />
New York Congressman Nadler blasts<br />
Trump budget as “Absurd”<br />
WASHINGTON, DC, <strong>Mar</strong>ch 16,<br />
2017 – Today, Congressman Jerrold<br />
Nadler (D-NY), issued the following<br />
statement in response to Donald<br />
Trump’s budget proposal:<br />
“It’s time to wake up to the malignant<br />
lies of the Trump Administration<br />
before he turns this country<br />
into an autocratic state that sacrifices<br />
the health, safety, and security<br />
George Albro, co-chair NY-<br />
PAN, a new statewide progressive<br />
organization, said, “New York’s<br />
current election laws are a embarrassment<br />
and have made our state,<br />
once a proud leader in progressive<br />
innovations, synonymous with the<br />
purposeful disenfranchisement of<br />
millions: one of the worst registration<br />
and voter turnout rates, one of<br />
only 13 states without early voting,<br />
a Kafkaesque party change enrollment<br />
requirement of 11 months<br />
before a primary, and recurrent illegal<br />
purges of thousands of regular<br />
voters. To Governor Cuomo we say:<br />
enough is enough; 7 years in office,<br />
and nothing has changed. Don’t call<br />
yourself a progressive unless and<br />
until you restore democracy in our<br />
state.”<br />
33<br />
of American families in favor of an<br />
agenda fueled by nationalist propaganda.”<br />
“This so-called “skinny budget”<br />
from President Trump is absurd and<br />
shows his Administration’s true priorities.<br />
“This budget completely eliminates<br />
Community Development<br />
Block Grants, which help working<br />
families stay in safe, affordable<br />
housing and supports programs like<br />
Meals on Wheels that provide food<br />
to the sick and elderly. The Trump<br />
budget would also eliminate programs<br />
to help low-income and older<br />
Americans afford heat in winter.<br />
“The Trump budget cuts the Environmental<br />
Protection Agency<br />
which would make our communities<br />
sicker, cutting off all funding<br />
for alternative energy sources and<br />
Clean Power Plant rules that reduce<br />
emissions.<br />
“The Trump budget would also<br />
slash 20 percent from the National<br />
Institutes of Health, dramatically<br />
undercutting the federal government’s<br />
support of life-saving scientific<br />
research and ceding American<br />
leadership in biomedical advancement.<br />
“Unsurprisingly, Donald Trump<br />
More on page 42
Biennial Women in Cybersecurity Report reveals that<br />
female representation in industry remains stagnant, as<br />
cyber workforce gap expected to reach 1.8 million by 2022<br />
CLEARWATER, FL, <strong>Mar</strong>ch 15,<br />
2017 — According to new research<br />
from the Center for Cyber Safety<br />
and Education (the Center) and<br />
the Executive Women’s Forum on<br />
Information Security, Risk Management<br />
& Privacy (EWF), conducted<br />
by Frost & Sullivan, women comprise<br />
only 11 percent of the information<br />
security workforce – a number<br />
that has remained steady since 2013.<br />
The study also found that women in<br />
cybersecurity have higher levels of<br />
education than men, but fewer hold<br />
senior-level positions, and they earn<br />
less money. The Women in Cybersecurity<br />
report is part of the Center’s<br />
eighth Global Information Security<br />
Workforce Study (GISWS) – sponsored<br />
by Booz Allen Hamilton – and<br />
is based on data that was collected in<br />
the survey.<br />
“It’s disappointing to see that the<br />
number of women in the cybersecurity<br />
workforce continues to remain<br />
low,” said David Shearer, CEO, the<br />
Center for Cyber Safety and Education<br />
and (ISC)²®. “We must encourage<br />
young women; help them to see<br />
that information security is a challenging,<br />
lucrative and exciting career<br />
field. We must also promote women<br />
into leadership positions, and pay<br />
them at levels that are equal to their<br />
male counterparts. There is a large<br />
shortage of skilled cyber professionals,<br />
and women are a valuable resource<br />
that can help to bridge that<br />
gap.”<br />
“For 15 years the Executive Women’s<br />
Forum on Information Security,<br />
Risk Management & Privacy has<br />
been committed to addressing the<br />
very issues highlighted in this report<br />
by delivering programs which<br />
retain and advance women through<br />
education, leadership development<br />
and the creation of trusted relationships.”<br />
said Lynn Terwoerds, executive<br />
director of the Executive Women’s<br />
Forum on Information Security,<br />
Risk Management & Privacy. “I am<br />
34<br />
so proud to be a co-author of the<br />
Women in Cybersecurity report and<br />
hope that the results will promote<br />
both conversations and actions to<br />
advance and retain women in cybersecurity.”<br />
Key takeaways from the Women in<br />
Cybersecurity report include:<br />
• Women comprise only 11 percent<br />
of the global information security<br />
workforce.<br />
• Women have higher levels of education<br />
than men, with 51 percent<br />
holding a master’s degree or<br />
higher, compared to 45 percent of<br />
men.<br />
• Fewer women hold positions of<br />
authority (director level or above)<br />
compared to men.<br />
• Women working in cybersecurity<br />
have a more varied educational<br />
background than men contributing<br />
to the diverse set of skills they<br />
can potentially bring to the industry.<br />
• On average, women in the information<br />
security industry earn a<br />
lower annual salary than their<br />
male counterparts.<br />
• Fifty-one percent of women in<br />
the cybersecurity industry in
North America and<br />
Latin America have experienced<br />
some form<br />
of discrimination, compared<br />
to only 15 percent<br />
of men.<br />
• Women who have higher<br />
levels of access to sponsorship<br />
and leadership<br />
programs report feeling<br />
valued in their role and<br />
are more likely to be successful.<br />
The Center for Cyber Safety<br />
and Education and the Executive<br />
Women’s Forum on Information Security,<br />
Risk Management & Privacy<br />
have joined forces with several industry<br />
leaders to raise awareness of<br />
the need for women in cybersecurity.<br />
Additional sponsors of the report<br />
include: PricewaterhouseCoopers<br />
LLC, IBM, Alta Associates, (ISC)²<br />
and Veracode. Booz Allen Hamilton<br />
sponsored the Global Information<br />
Security Workforce Study (GISWS),<br />
which provided the data for the report.<br />
“I believe it is imperative for the<br />
cybersecurity industry to support<br />
and facilitate the recruiting, retaining<br />
and promoting of women. Proactively<br />
developing this career path<br />
will combat gender inequality and<br />
prevent further decline in the overall<br />
security labor pool,” said Sloane<br />
Menkes, PwC principal and global<br />
crisis center coordinator. “While<br />
Male and female cybersecurity workforce composition, by region<br />
there is significant demand for highskilled<br />
workers, there is also a critical<br />
pipeline issue of women joining<br />
our cybersecurity workforce. Cybersecurity<br />
leaders need to commit to<br />
reversing this trend - from our universities<br />
to our board rooms - before<br />
the issue is irreversible.”<br />
“With increasingly sophisticated<br />
threats and the demand for security<br />
talent soaring, the cybersecurity field<br />
is one that absolutely cannot afford<br />
to neglect the population of women<br />
and the many talents they offer,” said<br />
Shamla Naidoo, global chief information<br />
security officer, IBM. “The<br />
security industry needs the best and<br />
brightest to remain ahead in the fight<br />
against cybercrime, and creating a<br />
workforce with diversity of thought,<br />
gender and backgrounds is essential<br />
to this goal.”<br />
“As the leading executive search<br />
firm specializing in cybersecurity,<br />
35<br />
Alta Associates understands<br />
that building world class<br />
teams and solving complex<br />
cybersecurity challenges requires<br />
diversity of thought.<br />
That’s why we are proud<br />
to report that in 2016 Alta<br />
filled nearly 30 percent of<br />
its cybersecurity searches<br />
with qualified women executives.”<br />
said Joyce Brocaglia,<br />
CEO of Alta Associates<br />
and founder of the<br />
Executive Women’s Forum<br />
on Information Security<br />
Risk Management & Privacy. “I am<br />
proud to co-author this important<br />
report in hopes that it both educates<br />
and inspires action to improve the<br />
representation and advancement of<br />
women in cybersecurity.”<br />
“The Women in Cybersecurity report<br />
found that 52 percent of millennial<br />
women have a computer science<br />
degree, yet the number of women<br />
in the cybersecurity workforce has<br />
remained stagnant for the last two<br />
years,” said Sam King, chief strategy<br />
officer, Veracode. “We are already<br />
facing a significant skills gap in cybersecurity<br />
with positions going unfilled.<br />
If we continue on this track, we<br />
will be unable to secure the digital<br />
economy. We need to examine why it<br />
is that the next generation of workers<br />
is not pursuing careers in cybersecurity,<br />
but especially women. In addition<br />
to focusing on cybersecurity<br />
education at the university level, cre-
ating programs aimed at high<br />
school and middle school<br />
students will help to create<br />
enthusiasm for this industry.”<br />
“Mature cyber security<br />
teams require a mix of skills<br />
and diversity of thought – you<br />
must foster teamwork that’s inclusive<br />
and integrates multi-disciplinary<br />
and diverse perspectives” said Angela<br />
Messer, a Booz Allen executive<br />
vice president, and leader of the<br />
firm’s Cyber innovation business<br />
and cyber talent development champion.<br />
“An overreliance on any one<br />
background or perspective leaves an<br />
organization vulnerable to adversaries<br />
and threats that rapidly change –<br />
only diverse, multidisciplinary teams<br />
can rapidly respond and problem<br />
solve on the next challenge. It’s also a<br />
security imperative that our industry<br />
broaden access to talent by becoming<br />
better at attracting, retaining and<br />
empowering female cyber warriors.”<br />
The largest study of the information<br />
security profession ever conducted,<br />
the 2017 GISWS took place<br />
June-September 2016 through a<br />
web-based survey. Over 19,000 information<br />
security professionals<br />
from 170 nations responded. Since<br />
its first release in 2004, the study<br />
gauges the opinions of information<br />
security professionals, and provides<br />
detailed insight into important<br />
trends and opportunities within<br />
the profession. It aims to provide a<br />
clear understanding of pay scales,<br />
It’s also a security imperative that our<br />
industry broaden access to talent by<br />
becoming better at attracting, retaining<br />
and empowering female cyber warriors.<br />
skills gaps, training requirements,<br />
corporate hiring practices, security<br />
budgets, career progression and corporate<br />
attitudes toward information<br />
security that is of use to companies,<br />
hiring managers and industry professionals.<br />
The full 2017 Women in Cybersecurity<br />
report can be downloaded<br />
here: www.iamcybersafe.org/gisws.<br />
About the Center for Cyber Safety<br />
and Education’s Global Information<br />
Security Workforce Study<br />
The Women in Cybersecurity report<br />
is the second release of data from the<br />
2017 Global Information Security<br />
Workforce Study. The first data set,<br />
released in February 2017, was the<br />
Millennials – the Next Generation<br />
of Information Security Workers.<br />
This is a new format for the biennial<br />
study, and The Center will release<br />
several additional reports throughout<br />
the year with new, previously unpublished<br />
information and insights<br />
about the global information security<br />
workforce.<br />
About the Center for Cyber Safety<br />
and Education<br />
The Center for Cyber Safety and<br />
36<br />
Education (Center), formerly<br />
(ISC)² Foundation, is a nonprofit<br />
charitable trust committed<br />
to making the cyber<br />
world a safer place for everyone.<br />
The Center works to<br />
ensure that people across the<br />
globe have a positive and safe experience<br />
online through their educational<br />
programs, scholarships and<br />
research. Visit www.iamcybersafe.<br />
org.<br />
About the Executive Women’s<br />
Forum on Information Security,<br />
Risk Management & Privacy<br />
Founded in 2002, the Executive<br />
Women’s Forum on Information<br />
Security, Risk Management & Privacy<br />
(EWF) is the largest member<br />
organization dedicated to engaging,<br />
advancing and developing women<br />
leaders in Cybersecurity, IT Risk<br />
Management, Governance Risk &<br />
Compliance and Privacy. The EWF<br />
serves emerging leaders as well as<br />
the most prominent and influential<br />
women in our field by facilitating<br />
programs and events throughout the<br />
year including a National Conference,<br />
regional meetings, leadership<br />
development and mentorship programs<br />
as well as interactions with<br />
global thought leaders through an<br />
online community. For more information<br />
visit, www.ewf-usa.com.<br />
About (ISC)²<br />
(ISC)² is an international nonprofit
membership association focused<br />
on inspiring a safe and secure cyber<br />
world. Best known for the acclaimed<br />
Certified Information Systems Security<br />
Professional (CISSP®) certification,<br />
(ISC)2 offers a portfolio of<br />
credentials that are part of a holistic,<br />
programmatic approach to security.<br />
Our membership, over 123,000<br />
strong, is made up of certified cyber,<br />
information, software and infrastructure<br />
security professionals who<br />
are making a difference and helping<br />
to advance the industry. Our vision<br />
is supported by our commitment to<br />
educate and reach the general public<br />
through our charitable foundation –<br />
The Center for Cyber Safety and EducationTM.<br />
For more information<br />
on (ISC)², visit www.isc2.org, follow<br />
us on Twitter or connect with us on<br />
Facebook.<br />
© 2017 (ISC)² Inc., (ISC)², CISSP, SSCP, CCSP, CAP, CSSLP,<br />
HCISPP, CCFP, ISSAP, ISSEP, ISSMP and CBK are registered<br />
marks, of (ISC)², Inc.<br />
About PricewaterhouseCoopers LLC,<br />
Delaware/USA<br />
At PwC, our purpose is to build trust<br />
in society and solve important problems.<br />
We’re a network of firms in 157<br />
countries with more than 223,000<br />
people who are committed to delivering<br />
quality in assurance, advisory<br />
and tax services. Find out more and<br />
tell us what matters to you by visiting<br />
us at www.pwc.com.<br />
PwC refers to the PwC network<br />
and/or one or more of its member<br />
firms, each of which is a separate legal<br />
entity. Please see www.pwc.com/<br />
structure for further details. © 2017<br />
PwC. All rights reserved.<br />
About IBM Security<br />
IBM Security offers one of the most<br />
advanced and integrated portfolios<br />
of enterprise security products and<br />
services. The portfolio, supported<br />
by world-renowned IBM X-Force®<br />
research, enables organizations to<br />
effectively manage risk and defend<br />
against emerging threats. IBM operates<br />
one of the world’s broadest<br />
security research, development and<br />
delivery organizations, monitors 35<br />
billion security events per day in<br />
more than 130 countries, and holds<br />
more than 3,000 security patents.<br />
For more information, please visit<br />
www.ibm.com/security, follow @<br />
IBMSecurity on Twitter or visit the<br />
IBM Security Intelligence blog.<br />
About Alta Associates, Inc.<br />
Alta Associates is the most prominent<br />
executive search firm specializing<br />
in Cybersecurity and IT Risk<br />
Management. Alta, ranked one of<br />
the top 40 executive search firms in<br />
the US, has an unprecedented track<br />
record of placing CISO’s and building<br />
world class Cybersecurity, Information<br />
Security and IT Risk organizations.<br />
Alta Associates is a certified woman<br />
owned business, with a seasoned<br />
team of specialized recruiters who<br />
have trusted relationships with the<br />
37<br />
most sought after cybersecurity experts<br />
in the US. Most importantly,<br />
Alta is committed to providing its<br />
clients with executives representing<br />
diversity of thought. For more information<br />
visit, www.altaassociates.<br />
com or call 908-806-8442<br />
About Veracode<br />
Veracode is a leader in securing web,<br />
mobile and third-party applications<br />
for the world’s largest global enterprises.<br />
By enabling organizations to<br />
rapidly identify and remediate application-layer<br />
threats before cyberattackers<br />
can exploit them, Veracode<br />
helps enterprises speed their innovations<br />
to market – without compromising<br />
security.<br />
Veracode’s powerful cloud-based<br />
platform, deep security expertise<br />
and systematic, policy-based approach<br />
provide enterprises with a<br />
simpler and more scalable way to<br />
reduce application-layer risk across<br />
their global software infrastructures.<br />
Veracode serves hundreds of customers<br />
across a wide range of industries,<br />
including nearly one-third of<br />
the Fortune 100, three of the top four<br />
U.S. commercial banks and more<br />
than 20 of Forbes’ 100 Most Valuable<br />
Brands. Learn more at www.veracode.com,<br />
on the Veracode blog and<br />
on Twitter.<br />
Copyright © 2006-2017 Veracode, Inc. All Rights Reserved.<br />
All other brand names, product names, or trademarks belong<br />
to their respective holders.
Hikvision and L.A. contemporary dance company<br />
illustrate the Art of Video Surveillance<br />
CITY OF INDUSTRY, CA—<strong>Mar</strong>ch<br />
28, 2017—In its latest advertising<br />
campaign, Hikvision, the North<br />
American leader in innovative,<br />
award-winning video surveillance<br />
products and solutions, collaborated<br />
with the L.A. Contemporary<br />
Dance Company to convey the innovation<br />
and artistry that goes into<br />
making sophisticated video surveillance<br />
products.<br />
At the ISC West show next week,<br />
in addition to enterprise-level video<br />
surveillance solutions, visitors to the<br />
Hikvision booth and Partner Celebration<br />
guests will be able to see<br />
live performances by LACDC dancers<br />
and a “Behind the Scenes” video<br />
of the Hikvision-LACDC collaboration.<br />
Here is a link to the video<br />
“At Hikvision we pride ourselves<br />
on being unique and innovative in<br />
everything we do and the Art of<br />
Video Surveillance campaign is just<br />
that,” said Manny Gonzalez, Hikvision<br />
creative manager.<br />
The LACDC dancers illustrated<br />
Hikvision 360-degree cameras,<br />
PTZs and other specialty cameras.<br />
Whether it was a single dancer or<br />
group, the dancers’ movements<br />
corresponded to different types of<br />
cameras. “It was very cohesive. Who<br />
knew dance and video surveillance<br />
had so much in common,” said<br />
Genevieve Carson, artistic director,<br />
LACDC.<br />
Gonzalez used a 360-degree camera<br />
to explain the metaphor. “There<br />
are many components and lenses in<br />
a 360-degree camera that allow it to<br />
cover vast areas and provide impressive<br />
video at high resolution. The<br />
same is true with dance, whether<br />
it’s one dancer or multiple dancers it<br />
requires the coordination of all the<br />
parts to work in unison to create a<br />
beautiful piece. That’s the link to our<br />
technology.”<br />
LACDC artistic director Carson<br />
said LACDC and Hikvision collaborated<br />
closely on the creative and<br />
choreographic direction, but let the<br />
dancers do what they do best.<br />
“It was really awesome and outthe-box,<br />
pairing a video surveillance<br />
company with a dance company,”<br />
said Carson. The unusual<br />
artistic endeavor flourished on a<br />
well-organized all-day photo shoot<br />
early this year. “Once we got in the<br />
same room it was super comfortable<br />
and exciting to watch the dancers<br />
embody the concepts of Hikvision<br />
38<br />
and its products,” she added.<br />
Alex Asnovich, Hikvision director<br />
of marketing said, “Hikvision supports<br />
the arts, programs in science<br />
and math, and we support communities.<br />
Beyond security and products,<br />
the Art of Video Surveillance<br />
campaign is about our values as a<br />
company.”<br />
Visit Hikvision Booth # 18037 to<br />
see Hikvision’s enterprise-level solutions,<br />
future technology, participate<br />
in Thought Theater events, and to<br />
view the “Behind the Scenes” video<br />
of the Hikvision-LACDC collaboration.<br />
The LACDC dancers will<br />
perform at 11:30, 1:30 and 3:30 on<br />
Wednesday, April 5 and Thursday,<br />
April 6.<br />
About Hikvision<br />
Hikvision is the world’s leading supplier<br />
of video surveillance solutions.<br />
Featuring the industry’s strongest<br />
R&D workforce, Hikvision designs,<br />
develops, and manufactures standard-<br />
and high-definition cameras,<br />
including a variety of IP cameras,<br />
analog cameras, and cameras featuring<br />
the latest in high-definition<br />
analog technology. Hikvision’s<br />
More on page 40
39
Heightening security verification<br />
with self-service kiosks<br />
Continued from page 8<br />
recognition (FR) comparison. Many<br />
of the security functions enabled by<br />
the technology can take place seamlessly<br />
without the user’s explicit<br />
step-by-step direction because they<br />
occur in the background. Once an<br />
individual’s background and identity<br />
are vetted through the appropriate<br />
authoritative agencies, it won’t<br />
have to be done repeatedly.<br />
All of the work is<br />
done up front and subsequent<br />
screenings are<br />
virtually instantaneous.<br />
Gaining entry to a secure<br />
area – for example,<br />
a particular work area in a mission<br />
critical facility or location – can be<br />
done at an unattended gate, simply<br />
by requiring a quick fingerprint, iris<br />
scan, or FR comparison. The potential<br />
for unauthorized access, fraud<br />
and human error is reduced.<br />
Re-entering the US after a trip<br />
abroad can also be made faster<br />
and easier with self-service kiosks.<br />
Instead of manually completing a<br />
US customs form and handing it,<br />
with a passport, to a customs agent<br />
for checking, questions can be answered<br />
on an electronic screen and<br />
the passport can be authenticated at<br />
the same time. The machine does<br />
more than visual inspection of an<br />
ID credential – it can also scan for<br />
invisible security features. The time<br />
and labor savings can be invaluable.<br />
This technology is already being<br />
used at international points of entry.<br />
A common credential for government<br />
facilities and agencies could<br />
also be accommodated. This would<br />
allow authentication between agencies<br />
with a high degree of confidence.<br />
The migration to self-service kiosks<br />
will require planning. Traffic<br />
volume must be carefully considered<br />
when deciding how many<br />
machines to install and in what locations.<br />
They must be easy to find,<br />
and it’s important to<br />
install enough of them<br />
to prevent long lines.<br />
Bottlenecks would defeat<br />
their purpose of<br />
convenience, and discourage<br />
use.<br />
The interface and workflow are<br />
critical points for user adoption. The<br />
kiosk should be inviting and easy to<br />
use and understand. It’s possible for<br />
the interface to adjust workflow in<br />
accordance with the user’s demographic<br />
(age, for example). The user<br />
won’t realize it, but the speed of the<br />
question/answer workflow will be<br />
adjusted to meet the user’s anticipated<br />
needs.<br />
Anti-fraud measures can be<br />
built in as well. Biometrics can be<br />
proofed with background adjudication.<br />
The interactive technology will<br />
detect inconsistencies and adjust<br />
the workflow to allow correction or<br />
to automatically abort an attempt.<br />
Conclusion<br />
The use of self-service kiosks for<br />
identity authentication will become<br />
40<br />
Hikvision and L.A. contemporary<br />
dance company illustrate the Art<br />
of Video Surveillance<br />
Continued from page 38<br />
product suite also includes digital<br />
video servers, hybrid and standalone<br />
DVRs, NVRs, and other elements<br />
of sophisticated security systems<br />
for both indoor and outdoor<br />
use.<br />
About L.A. Contemporary<br />
Dance Company<br />
L.A. Contemporary Dance Company<br />
is the resident contemporary<br />
dance company of Los Angeles<br />
producing innovative dance experiences<br />
for over 10 years with performances<br />
in L.A. and touring productions<br />
worldwide. Learn more at<br />
www.lacontemporarydance.org<br />
commonplace in areas, like airports<br />
and government facilities, where a<br />
high degree of security is required.<br />
These new technologies will enable<br />
faster and more accurate checking<br />
of credentials, saving time and<br />
money and providing a new level of<br />
convenience to the users.<br />
Gerald Hubbard is a Business Development<br />
Manager with over 28 years<br />
of experience in high assurance identity<br />
credentials, access management,<br />
and payment applications.
Making microgrids work:<br />
send in the <strong>Mar</strong>ines?<br />
Continued from page 16<br />
to ‘market maker’ by fully embracing<br />
this opportunity to help usher in<br />
a new era of modern, efficient and<br />
resilient microgrids that can serve<br />
as a feasible supplement to the nation’s<br />
aging power grid.<br />
J. Michael Barrett is Director of the<br />
Center for Homeland Security &<br />
Resilience and a former Director of<br />
Strategy for the White House Homeland<br />
Security Council. This article<br />
is drawn from the author’s recent<br />
White Paper, “Challenges and Requirements<br />
for Tomorrows Electrical<br />
Power Grid”, published by the<br />
Lexington Institute and available at<br />
http://lexingtoninstitute.org/wp-con-<br />
tent/uploads/2016/06/Tomorrows-<br />
Electrical-Power-Grid.pdf.<br />
Bipartisan bill supports Defense<br />
Cyber Scholarships<br />
Continued from page 18<br />
“A skilled workforce is the backbone<br />
of any and every field – and in<br />
cyberspace, we face different threats<br />
from our adversaries each and every<br />
day,” said Allen. “At Fort Gordon, in<br />
my district, our soldiers are on the<br />
frontline of fighting these attacks<br />
– and in the changing electronic<br />
world we live, we must have the best<br />
and the brightest standing ready to<br />
support the needs of our military. I<br />
have always said we must encourage<br />
students to find their passions<br />
early on and allow those interests to<br />
be carried on throughout their educational<br />
careers – the cyber industry<br />
is yet another example. Augusta<br />
University is leading educational<br />
innovation in my district to prepare<br />
the next generation of cyber warriors.<br />
Investing in future generations<br />
makes it possible to field the<br />
cyber threats of today, tomorrow<br />
and years to come.”<br />
“I applaud this very important<br />
bicameral and bipartisan legislation,<br />
which will help bolster the<br />
Department of Defense’s waning<br />
cybersecurity workforce. Competition<br />
from the tech world has made<br />
recruiting and retaining top public<br />
sector cybersecurity professionals<br />
a challenge. I am proud to support<br />
the DOD Cybersecurity scholarship<br />
program at universities across the<br />
41<br />
Aerojet Rocketdyne supports<br />
ULA launch of Wideband Global<br />
SATCOM spacecraft<br />
Continued from page 17<br />
allied forces deployed worldwide.<br />
They help support the exchange of<br />
information, execution of tactical<br />
command and control, intelligence,<br />
surveillance and reconnaissance.<br />
Aerojet Rocketdyne is an innovative<br />
company delivering solutions<br />
that create value for its customers in<br />
the aerospace and defense markets.<br />
The company is a world-recognized<br />
aerospace and defense leader that<br />
provides propulsion and energetics<br />
to the space, missile defense and<br />
strategic systems, tactical systems<br />
and armaments areas, in support of<br />
domestic and international markets.<br />
Additional information about Aerojet<br />
Rocketdyne can be obtained by<br />
visiting our websites at www.Rocket.<br />
com and www.AerojetRocketdyne.<br />
com.<br />
country, as they engage and educate<br />
students from various backgrounds<br />
and at different levels of education.<br />
Georgia universities are leading the<br />
effort to ensure a vibrant and highly-skilled<br />
government and publicsector<br />
cybersecurity workforce, and<br />
the DOD Cyber Scholarship Program<br />
Act of 2017 will help secure<br />
these efforts for years to come,” said<br />
Johnson.
New York Congressman Nadler<br />
blasts Trump budget as “Absurd”<br />
Continued from page 33<br />
takes the lazy route of completely<br />
ending funding for arts and humanities<br />
programs and the Corporation<br />
for Public Broadcasting, which<br />
make up less than 0.01 percent of<br />
the federal budget, not to save money,<br />
but as part of an ideological obsession<br />
with ending federal support<br />
for the arts and culture.<br />
“Furthermore, the Trump budget<br />
frivolously ramps-up military<br />
spending in a chauvinistic show of<br />
force that won’t make our country<br />
any safer and may well provoke<br />
friend and foe alike. It makes devastatingly<br />
unrealistic cuts to the State<br />
Department, which would cripple<br />
our diplomatic efforts to prevent<br />
and solve conflicts peacefully thereby<br />
reducing the need for military<br />
force.<br />
“Everyone should oppose this<br />
budget, which doesn’t even achieve<br />
Republicans’ long-stated goal of deficit<br />
reduction, but does threaten the<br />
lives of every single American.<br />
“It’s time to wake up to the malignant<br />
lies of the Trump Administration<br />
before he turns this country<br />
into an autocratic state that sacrifices<br />
the health, safety, and security<br />
of American families in favor of an<br />
agenda fueled by nationalist propaganda.”<br />
<strong>GSN</strong>’s 2017<br />
Airport/Seaport/Border Security Awards<br />
Now Including Cybersecurity Solutions for Airport, Seaport,<br />
Border Security <strong>Mar</strong>kets<br />
All Winners in this program are<br />
entitled to a Full-Page Advertisement<br />
(8.5” x 9.0”) in your choice of <strong>GSN</strong>’s<br />
Digital Magazine or Leaderboard in<br />
any edition of the Airport, Seaport,<br />
Rail, Border Security Weekly<br />
Newsletter.<br />
Adrian Courtenay<br />
Managing Partner, CEO<br />
Government Security News<br />
917-696-5782<br />
acourtenay@gsnmagazine.com<br />
NEW IN 2017:<br />
CLICK HERE TO SUBMIT ENTRIES<br />
All Finalists are entitled to a Half-<br />
Page Advertisement (8.5” x 4.5”) in<br />
your choice of <strong>GSN</strong>’s Digital Magazine<br />
or Leaderboard in any edition of the<br />
Airport, Seaport, Rail, Border Security<br />
Weekly Newsletter.<br />
Steve Bittenbender<br />
Managing Editor<br />
Government Security News<br />
502-552-1450<br />
sbittenbender@gsnmagazine.com<br />
Gerry O’Hara<br />
Designer<br />
OHDesign3<br />
203-249-0626<br />
gerry@ohd3.com<br />
42
The News Leader in Physical, IT and Homeland Security<br />
CEO/Editorial Director<br />
Adrian Courtenay<br />
917-696-5782<br />
acourtenay@gsnmagazine.com<br />
Editor<br />
Steve Bittenbender<br />
502-552-1450<br />
sbittenbender@gsnmagazine.com<br />
Senior Writer<br />
Karen Ferrick-Roman<br />
412-671-1456<br />
karenferrickroman@gmail.com<br />
Columnist<br />
Shawn Campbell<br />
Campbell on Crypto<br />
shawn.campbell@safenetat.com<br />
Columnist<br />
George Lane<br />
Hazmat Science & Public Policy<br />
georgelane@hotmail.com<br />
Contributing Author<br />
Lloyd McCoy Jr<br />
Immix Group<br />
Contributing Author<br />
Walter Ewing<br />
Contributing Author<br />
Wendy Feliz<br />
Contributing Author<br />
Joshua Breisblatt<br />
Contributing Author<br />
J. Michael Barrett<br />
Contributing Author<br />
Christopher Millar<br />
Gatekeeper Security<br />
Art Director<br />
Gerry O’Hara, OHDesign3<br />
gerry@ohd3.com<br />
203-249-0626<br />
Production Manager<br />
Brenden Hitt<br />
Brenden.hitt@gsnmagazine.com<br />
Direct: 203-216-7798<br />
COMING ATTRACTIONS<br />
April<br />
Late News<br />
Tech Focus<br />
Law Enforcement,<br />
Public Safety<br />
<strong>Mar</strong>ket Sector<br />
Cybersecurity Threats,<br />
Solutions<br />
May<br />
Late News<br />
Tech Focus<br />
License Plate Detection,<br />
Smart Vehicle Surveil<br />
<strong>Mar</strong>ket Sector<br />
<strong>Mar</strong>itime/Coastal/<br />
Port Security<br />
43