Prime Numbers
Prime Numbers Prime Numbers
8.1 Cryptography 389 is, if an oracle could tell you g ab on input of g a and g b , could you use this oracle to quickly solve for discrete logarithms? 8.1.2 RSA cryptosystem Soon after the Diffie–Hellman ideas, the now prevalent RSA cryptosystem was invented by Rivest, Shamir, and Adleman [Rivest et al. 1978]. Algorithm 8.1.2 (RSA private/public key generation). In this algorithm we generate an individual’s private and associated public keys for the RSA cryptosystem. 1. [Choose primes] Choose two distinct primes p, q under prevailing safety criteria (see text); 2. [Generate public key] N = pq; ϕ =(p − 1)(q − 1); // Euler totient of N. Choose random integer E ∈ [3,N − 2] coprime to ϕ; Report public key as (N,E); // User publishes this key. 3. [Generate private key] D = E −1 mod ϕ; Report private key as D; // User keeps D secret. The primary observation is that because of the difficulty of factoring N = pq, the public integer N does not give an easy prescription for the private primes p, q. Furthermore, it is known that if one knows integers D, E in [1,n− 1] with DE ≡ 1(modϕ), then one can factor N in (probabilistic) polynomial time [Long 1981] (cf. Exercise 5.27). In the above algorithm it is fashionable to choose approximately equal private primes p, q, but some cryptographers suggest further safety tests. In fact, one can locate in the literature a host of potential drawbacks for certain p, q choices. There is a brief but illuminating listing of possible security flaws that depend on the magnitudes and other number-theoretical properties of p, q in [Williams 1998, p. 391]. The reference [Bressoud and Wagon 2000, p. 249] also lists RSA pitfalls. See also Exercise 8.2 for a variety of RSA security issues. Having adopted the notion that the public key is the hard-to-break (i.e., difficult to factor) composite integer N = pq, we can proceed with actual encryption of messages, as follows: Algorithm 8.1.3 (RSA encryption/decryption). We assume that Alice possesses a private key DA and public key (NA,EA) from Algorithm 8.1.2. Here we show how another individual (Bob) can encrypt a message x (thought of as an integer in [0,NA)) to Alice, and how Alice can decrypt said message. 1. [Bob encrypts] y = x EA mod NA; // Bob is using Alice’s public key. Bob then sends y to Alice; 2. [Alice decrypts]
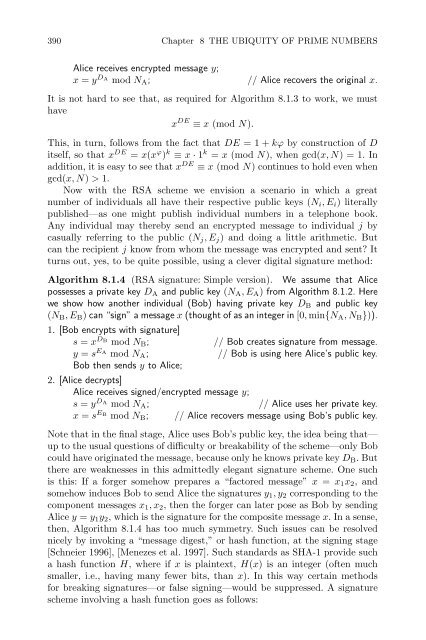
390 Chapter 8 THE UBIQUITY OF PRIME NUMBERS Alice receives encrypted message y; x = y DA mod NA; // Alice recovers the original x. It is not hard to see that, as required for Algorithm 8.1.3 to work, we must have x DE ≡ x (mod N). This, in turn, follows from the fact that DE =1+kϕ by construction of D itself, so that x DE = x(x ϕ ) k ≡ x · 1 k = x (mod N), when gcd(x, N) = 1. In addition, it is easy to see that x DE ≡ x (mod N) continues to hold even when gcd(x, N) > 1. Now with the RSA scheme we envision a scenario in which a great number of individuals all have their respective public keys (Ni,Ei) literally published—as one might publish individual numbers in a telephone book. Any individual may thereby send an encrypted message to individual j by casually referring to the public (Nj,Ej) and doing a little arithmetic. But can the recipient j know from whom the message was encrypted and sent? It turns out, yes, to be quite possible, using a clever digital signature method: Algorithm 8.1.4 (RSA signature: Simple version). We assume that Alice possesses a private key DA and public key (NA,EA) from Algorithm 8.1.2. Here we show how another individual (Bob) having private key DB and public key (NB,EB) can “sign” a message x (thought of as an integer in [0, min{NA,NB})). 1. [Bob encrypts with signature] s = x DB mod NB; // Bob creates signature from message. y = s EA mod NA; // Bob is using here Alice’s public key. Bob then sends y to Alice; 2. [Alice decrypts] Alice receives signed/encrypted message y; s = y DA mod NA; // Alice uses her private key. x = s EB mod NB; // Alice recovers message using Bob’s public key. Note that in the final stage, Alice uses Bob’s public key, the idea being that— up to the usual questions of difficulty or breakability of the scheme—only Bob could have originated the message, because only he knows private key DB.But there are weaknesses in this admittedly elegant signature scheme. One such is this: If a forger somehow prepares a “factored message” x = x1x2, and somehow induces Bob to send Alice the signatures y1,y2 corresponding to the component messages x1,x2, then the forger can later pose as Bob by sending Alice y = y1y2, which is the signature for the composite message x. In a sense, then, Algorithm 8.1.4 has too much symmetry. Such issues can be resolved nicely by invoking a “message digest,” or hash function, at the signing stage [Schneier 1996], [Menezes et al. 1997]. Such standards as SHA-1 provide such a hash function H, whereifx is plaintext, H(x) is an integer (often much smaller, i.e., having many fewer bits, than x). In this way certain methods for breaking signatures—or false signing—would be suppressed. A signature scheme involving a hash function goes as follows:
- Page 348 and 349: 7.4 Elliptic curve method 339 facto
- Page 350 and 351: 7.4 Elliptic curve method 341 propa
- Page 352 and 353: 7.4 Elliptic curve method 343 As fo
- Page 354 and 355: 7.4 Elliptic curve method 345 if(1
- Page 356 and 357: 7.5 Counting points on elliptic cur
- Page 358 and 359: 7.5 Counting points on elliptic cur
- Page 360 and 361: 7.5 Counting points on elliptic cur
- Page 362 and 363: 7.5 Counting points on elliptic cur
- Page 364 and 365: 7.5 Counting points on elliptic cur
- Page 366 and 367: 7.5 Counting points on elliptic cur
- Page 368 and 369: 7.5 Counting points on elliptic cur
- Page 370 and 371: 7.5 Counting points on elliptic cur
- Page 372 and 373: 7.5 Counting points on elliptic cur
- Page 374 and 375: 7.5 Counting points on elliptic cur
- Page 376 and 377: 7.5 Counting points on elliptic cur
- Page 378 and 379: 7.6 Elliptic curve primality provin
- Page 380 and 381: 7.6 Elliptic curve primality provin
- Page 382 and 383: 7.6 Elliptic curve primality provin
- Page 384 and 385: 7.7 Exercises 375 7.4. As in Exerci
- Page 386 and 387: 7.7 Exercises 377 (some Bj equals A
- Page 388 and 389: 7.7 Exercises 379 This reduction ig
- Page 390 and 391: 7.8 Research problems 381 multiply-
- Page 392 and 393: 7.8 Research problems 383 highly ef
- Page 394 and 395: 7.8 Research problems 385 is prime.
- Page 396 and 397: Chapter 8 THE UBIQUITY OF PRIME NUM
- Page 400 and 401: 8.1 Cryptography 391 Algorithm 8.1.
- Page 402 and 403: 8.1 Cryptography 393 just to genera
- Page 404 and 405: 8.1 Cryptography 395 where in the l
- Page 406 and 407: 8.2 Random-number generation 397 ar
- Page 408 and 409: 8.2 Random-number generation 399 Al
- Page 410 and 411: 8.2 Random-number generation 401 }
- Page 412 and 413: 8.2 Random-number generation 403 is
- Page 414 and 415: 8.3 Quasi-Monte Carlo (qMC) methods
- Page 416 and 417: 8.3 Quasi-Monte Carlo (qMC) methods
- Page 418 and 419: 8.3 Quasi-Monte Carlo (qMC) methods
- Page 420 and 421: 8.3 Quasi-Monte Carlo (qMC) methods
- Page 422 and 423: 8.3 Quasi-Monte Carlo (qMC) methods
- Page 424 and 425: 8.4 Diophantine analysis 415 [Tezuk
- Page 426 and 427: 8.4 Diophantine analysis 417 9262 3
- Page 428 and 429: 8.5 Quantum computation 419 We spea
- Page 430 and 431: 8.5 Quantum computation 421 three H
- Page 432 and 433: 8.5 Quantum computation 423 for a n
- Page 434 and 435: 8.6 Curious, anecdotal, and interdi
- Page 436 and 437: 8.6 Curious, anecdotal, and interdi
- Page 438 and 439: 8.6 Curious, anecdotal, and interdi
- Page 440 and 441: 8.7 Exercises 431 universal Golden
- Page 442 and 443: 8.7 Exercises 433 standards insist
- Page 444 and 445: 8.7 Exercises 435 of positive compo
- Page 446 and 447: 8.8 Research problems 437 element o
390 Chapter 8 THE UBIQUITY OF PRIME NUMBERS<br />
Alice receives encrypted message y;<br />
x = y DA mod NA; // Alice recovers the original x.<br />
It is not hard to see that, as required for Algorithm 8.1.3 to work, we must<br />
have<br />
x DE ≡ x (mod N).<br />
This, in turn, follows from the fact that DE =1+kϕ by construction of D<br />
itself, so that x DE = x(x ϕ ) k ≡ x · 1 k = x (mod N), when gcd(x, N) = 1. In<br />
addition, it is easy to see that x DE ≡ x (mod N) continues to hold even when<br />
gcd(x, N) > 1.<br />
Now with the RSA scheme we envision a scenario in which a great<br />
number of individuals all have their respective public keys (Ni,Ei) literally<br />
published—as one might publish individual numbers in a telephone book.<br />
Any individual may thereby send an encrypted message to individual j by<br />
casually referring to the public (Nj,Ej) and doing a little arithmetic. But<br />
can the recipient j know from whom the message was encrypted and sent? It<br />
turns out, yes, to be quite possible, using a clever digital signature method:<br />
Algorithm 8.1.4 (RSA signature: Simple version). We assume that Alice<br />
possesses a private key DA and public key (NA,EA) from Algorithm 8.1.2. Here<br />
we show how another individual (Bob) having private key DB and public key<br />
(NB,EB) can “sign” a message x (thought of as an integer in [0, min{NA,NB})).<br />
1. [Bob encrypts with signature]<br />
s = x DB mod NB; // Bob creates signature from message.<br />
y = s EA mod NA; // Bob is using here Alice’s public key.<br />
Bob then sends y to Alice;<br />
2. [Alice decrypts]<br />
Alice receives signed/encrypted message y;<br />
s = y DA mod NA; // Alice uses her private key.<br />
x = s EB mod NB; // Alice recovers message using Bob’s public key.<br />
Note that in the final stage, Alice uses Bob’s public key, the idea being that—<br />
up to the usual questions of difficulty or breakability of the scheme—only Bob<br />
could have originated the message, because only he knows private key DB.But<br />
there are weaknesses in this admittedly elegant signature scheme. One such<br />
is this: If a forger somehow prepares a “factored message” x = x1x2, and<br />
somehow induces Bob to send Alice the signatures y1,y2 corresponding to the<br />
component messages x1,x2, then the forger can later pose as Bob by sending<br />
Alice y = y1y2, which is the signature for the composite message x. In a sense,<br />
then, Algorithm 8.1.4 has too much symmetry. Such issues can be resolved<br />
nicely by invoking a “message digest,” or hash function, at the signing stage<br />
[Schneier 1996], [Menezes et al. 1997]. Such standards as SHA-1 provide such<br />
a hash function H, whereifx is plaintext, H(x) is an integer (often much<br />
smaller, i.e., having many fewer bits, than x). In this way certain methods<br />
for breaking signatures—or false signing—would be suppressed. A signature<br />
scheme involving a hash function goes as follows: