ENFORCEMENT
eop_ipec_jointstrategicplan_hi-res
eop_ipec_jointstrategicplan_hi-res
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Office of the Intellectual Property Enforcement Coordinator<br />
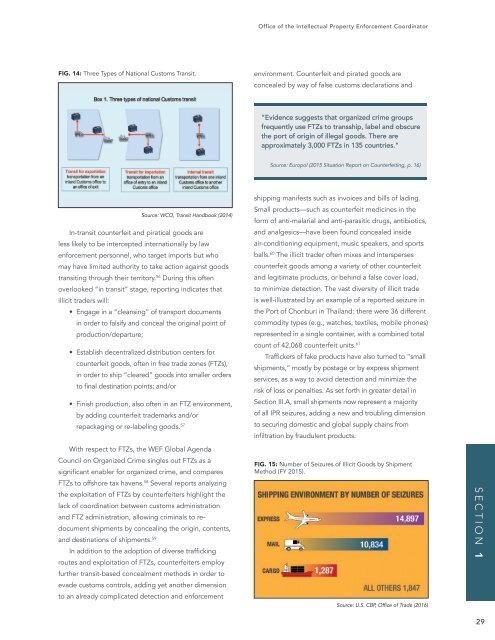
FIG. 14: Three Types of National Customs Transit.<br />
environment. Counterfeit and pirated goods are<br />
concealed by way of false customs declarations and<br />
“Evidence suggests that organized crime groups<br />
frequently use FTZs to transship, label and obscure<br />
the port of origin of illegal goods. There are<br />
approximately 3,000 FTZs in 135 countries.”<br />
Source: Europol (2015 Situation Report on Counterfeiting, p. 16)<br />
Source: WCO, Transit Handbook (2014)<br />
In-transit counterfeit and piratical goods are<br />
less likely to be intercepted internationally by law<br />
enforcement personnel, who target imports but who<br />
may have limited authority to take action against goods<br />
transiting through their territory. 56 During this often<br />
overlooked “in transit” stage, reporting indicates that<br />
illicit traders will:<br />
• Engage in a “cleansing” of transport documents<br />
in order to falsify and conceal the original point of<br />
production/departure;<br />
• Establish decentralized distribution centers for<br />
counterfeit goods, often in free trade zones (FTZs),<br />
in order to ship “cleared” goods into smaller orders<br />
to final destination points; and/or<br />
• Finish production, also often in an FTZ environment,<br />
by adding counterfeit trademarks and/or<br />
repackaging or re-labeling goods. 57<br />
With respect to FTZs, the WEF Global Agenda<br />
Council on Organized Crime singles out FTZs as a<br />
significant enabler for organized crime, and compares<br />
FTZs to offshore tax havens. 58 Several reports analyzing<br />
the exploitation of FTZs by counterfeiters highlight the<br />
lack of coordination between customs administration<br />
and FTZ administration, allowing criminals to redocument<br />
shipments by concealing the origin, contents,<br />
and destinations of shipments. 59<br />
In addition to the adoption of diverse trafficking<br />
routes and exploitation of FTZs, counterfeiters employ<br />
further transit-based concealment methods in order to<br />
evade customs controls, adding yet another dimension<br />
to an already complicated detection and enforcement<br />
shipping manifests such as invoices and bills of lading.<br />
Small products—such as counterfeit medicines in the<br />
form of anti-malarial and anti-parasitic drugs, antibiotics,<br />
and analgesics—have been found concealed inside<br />
air-conditioning equipment, music speakers, and sports<br />
balls. 60 The illicit trader often mixes and intersperses<br />
counterfeit goods among a variety of other counterfeit<br />
and legitimate products, or behind a false cover load,<br />
to minimize detection. The vast diversity of illicit trade<br />
is well-illustrated by an example of a reported seizure in<br />
the Port of Chonburi in Thailand: there were 36 different<br />
commodity types (e.g., watches, textiles, mobile phones)<br />
represented in a single container, with a combined total<br />
count of 42,068 counterfeit units. 61<br />
Traffickers of fake products have also turned to “small<br />
shipments,” mostly by postage or by express shipment<br />
services, as a way to avoid detection and minimize the<br />
risk of loss or penalties. As set forth in greater detail in<br />
Section III.A, small shipments now represent a majority<br />
of all IPR seizures, adding a new and troubling dimension<br />
to securing domestic and global supply chains from<br />
infiltration by fraudulent products.<br />
FIG. 15: Number of Seizures of Illicit Goods by Shipment<br />
Method (FY 2015).<br />
Source: U.S. CBP, Office of Trade (2016)<br />
SECTION 1<br />
29