ENFORCEMENT
eop_ipec_jointstrategicplan_hi-res
eop_ipec_jointstrategicplan_hi-res
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Office of the Intellectual Property Enforcement Coordinator<br />
crash injury research. The device would later be<br />
perfected by Nils Bohlin at Volvo. Other seatbelt<br />
research would be conducted at the University of<br />
Minnesota by James “Crash” Ryan in 1963, further<br />
pushing forward the science of safety.<br />
But this kind of success story does not exist in<br />
isolation and cannot survive without the proper<br />
regulatory framework.<br />
ACTION NO. 4.18: Foster broader recognition<br />
of the promise of university-led research<br />
and development as a driver of innovation.<br />
The Federal Government will work with other<br />
countries, bilaterally and through appropriate<br />
multilateral fora, to advocate for IP systems<br />
that help enable university-led research to drive<br />
innovation.<br />
F. SUPPORT STRATEGIES THAT MITIGATE THE THEFT<br />
OF U.S. TRADE SECRETS.<br />
U.S. companies face a growing and persistent threat by<br />
individuals, rival companies, and foreign governments<br />
that seek to steal some of their most valuable intangible<br />
assets—their trade secrets. 42 Trade secrets consist of<br />
non-public, commercially valuable information, including<br />
confidential formulae, programs, devices, processes or<br />
techniques for manufacturing a product. 43 “Protecting the<br />
trade secrets of American businesses sustains the integrity<br />
and competitiveness of the American economy, and<br />
encourages the development of new products, including<br />
advanced technologies.” 44<br />
As reported in the U.S. “Strategy on Mitigating the<br />
Theft of U.S. Trade Secrets,” issued in February 2013,<br />
“[e]merging trends indicate that the pace of economic<br />
espionage and trade secret theft against U.S. corporations<br />
is escalating.” 46 However, the exact cost of trade secret<br />
theft has gone largely unknown due to the difficulty in<br />
measuring such losses. 47<br />
Advancements in technology, increased mobility,<br />
globalization, and the anonymous nature of the Internet<br />
together contribute to growing challenges in protecting<br />
trade secrets. Bad actors acquire trade secrets in a<br />
variety of ways. In addition to taking photos, making<br />
sketches, or asking detailed technical questions about<br />
technologies on display at conferences, conventions<br />
and trade shows—methods that have been exploited<br />
for years—rogue actors are increasingly targeting the<br />
electronic information databases of U.S. companies, law<br />
firms, academia and financial institutions. Indeed, hacking<br />
is emerging as the preferred method of trade secret theft,<br />
given that, through a single breach, one person can steal<br />
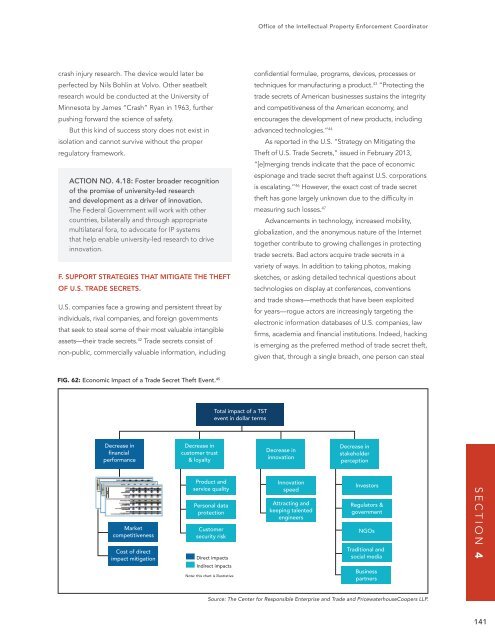
FIG. 62: Economic Impact of a Trade Secret Theft Event. 45<br />
Total impact of a TST<br />
event in dollar terms<br />
Decrease in<br />
financial<br />
performance<br />
Decrease in<br />
customer trust<br />
& loyalty<br />
Decrease in<br />
innovation<br />
Decrease in<br />
stakeholder<br />
perception<br />
Market<br />
competitiveness<br />
Cost of direct<br />
impact mitigation<br />
Product and<br />
service quality<br />
Personal data<br />
protection<br />
Customer<br />
security risk<br />
Direct impacts<br />
Indirect impacts<br />
Note: this chart is illustrative<br />
Innovation<br />
speed<br />
Attracting and<br />
keeping talented<br />
engineers<br />
Investors<br />
Regulators &<br />
government<br />
NGOs<br />
Traditional and<br />
social media<br />
Business<br />
partners<br />
SECTION 4<br />
Source: The Center for Responsible Enterprise and Trade and PricewaterhouseCoopers LLP.<br />
141