GOVRAT V2.0
GovRat-2-FINAL2
GovRat-2-FINAL2
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
<strong>GOVRAT</strong> <strong>V2.0</strong><br />
ATTACKING US MILITARY AND GOVERNMENT<br />
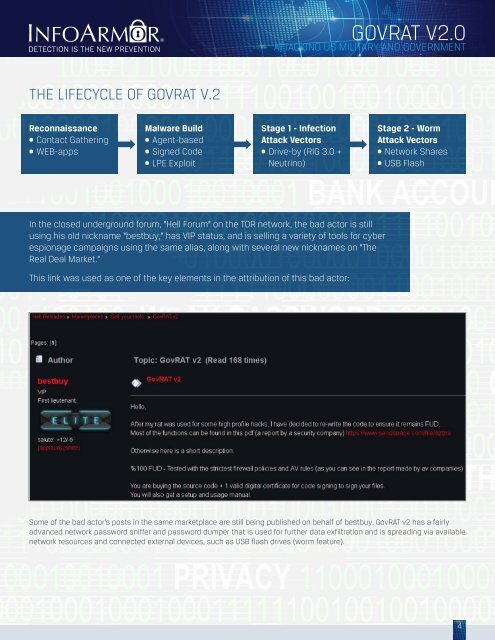
THE LIFECYCLE OF <strong>GOVRAT</strong> V.2<br />
Reconnaissance<br />
• Contact Gathering<br />
• WEB-apps<br />
Malware Build<br />
• Agent-based<br />
• Signed Code<br />
• LPE Exploit<br />
Stage 1 - Infection<br />
Attack Vectors<br />
• Drive-by (RIG 3.0 +<br />
Neutrino)<br />
Stage 2 - Worm<br />
Attack Vectors<br />
• Network Shares<br />
• USB Flash<br />
In the closed underground forum, “Hell Forum” on the TOR network, the bad actor is still<br />
using his old nickname “bestbuy,” has VIP status, and is selling a variety of tools for cyber<br />
espionage campaigns using the same alias, along with several new nicknames on “The<br />
Real Deal Market.”<br />
This link was used as one of the key elements in the attribution of this bad actor:<br />
Some of the bad actor’s posts in the same marketplace are still being published on behalf of bestbuy. GovRAT v2 has a fairly<br />
advanced network password sniffer and password dumper that is used for further data exfiltration and is spreading via available<br />
network resources and connected external devices, such as USB flash drives (worm feature).<br />
4