You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
One other unique property <strong>of</strong> this attack is that standard jailbreak detections fail to report that the device has been exploited.<br />
The attack and installation <strong>of</strong> the spying s<strong>of</strong>tware is designed to be as silent as possible to the target.<br />
Pr<strong>of</strong>essional Grade Development<br />
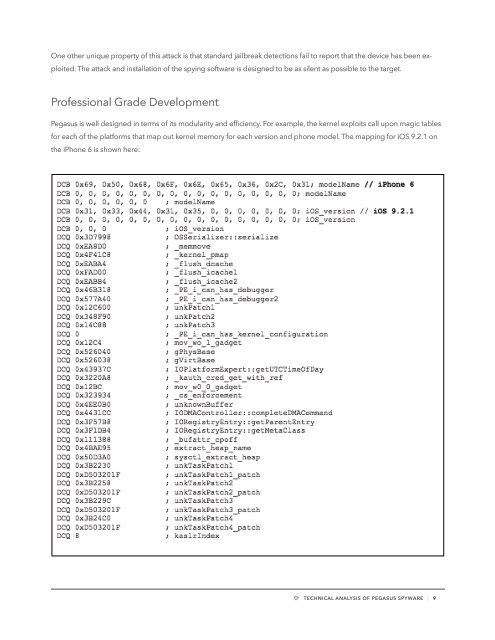
<strong>Pegasus</strong> is well designed in terms <strong>of</strong> its modularity and efficiency. For example, the kernel exploits call upon magic tables<br />
for each <strong>of</strong> the platforms that map out kernel memory for each version and phone model. The mapping for iOS 9.2.1 on<br />
the iPhone 6 is shown here:<br />
TECHNICAL ANALYSIS OF PEGASUS SPYWARE | 9