Serial Killer Silently Pwning Your Java Endpoints
asd-f03-serial-killer-silently-pwning-your-java-endpoints asd-f03-serial-killer-silently-pwning-your-java-endpoints
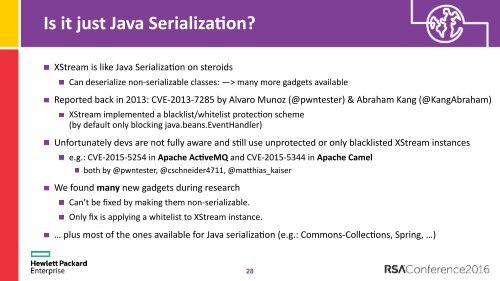
Is it just Java Serializa;on? XStream is like Java Serializa@on on steroids Can deserialize non-serializable classes: —> many more gadgets available Reported back in 2013: CVE-2013-7285 by Alvaro Munoz (@pwntester) & Abraham Kang (@KangAbraham) XStream implemented a blacklist/whitelist protec@on scheme (by default only blocking java.beans.EventHandler) Unfortunately devs are not fully aware and s@ll use unprotected or only blacklisted XStream instances e.g.: CVE-2015-5254 in Apache Ac;veMQ and CVE-2015-5344 in Apache Camel both by @pwntester, @cschneider4711, @maEhias_kaiser We found many new gadgets during research Can’t be fixed by making them non-serializable. Only fix is applying a whitelist to XStream instance. … plus most of the ones available for Java serializa@on (e.g.: Commons-Collec@ons, Spring, …) 28
Exploi;ng JNA 1 2 calc.exe 3 4 java.lang.Comparable 5 6 7 8 140735672090131 9 10 c 11 libc.dylib 12 13 system 14 15 16 17 29
- Page 1 and 2: SESSION ID: ASD-F03 Alvaro Muñoz S
- Page 3 and 4: What is Java Serializa;on again? Ta
- Page 5 and 6: Standing on the Shoulder of Giants
- Page 7 and 8: Triggering Execu;on via "Magic Meth
- Page 9 and 10: Exploi;ng "Magic Methods" But what
- Page 11 and 12: Exploi;ng Invoca;onHandler (IH) Gad
- Page 13 and 14: New RCE Gadget in BeanShell (CVE-20
- Page 15 and 16: New RCE Gadget in Jython (CVE pendi
- Page 17 and 18: Demo of aMack Let’s take a look a
- Page 19 and 20: Exis;ng Mi;ga;on Advice Simply remo
- Page 21 and 22: Exis;ng Mi;ga;on Advice Simply remo
- Page 23 and 24: Bypassing LookAhead Blacklists New
- Page 25 and 26: Example (has been fixed) org.apache
- Page 27: Demo of bypass Let’s take a look
- Page 31 and 32: #RSAC Finding Vulnerabili;es & Gadg
- Page 33 and 34: Finding Direct Deserializa;on Endpo
- Page 35 and 36: Finding Gadgets for Fun & Profit Si
- Page 37 and 38: Passive Deserializa;on Endpoint Det
- Page 39 and 40: Hardening Advice #RSAC
- Page 41 and 42: Apply What You Have Learned Today N
Is it just <strong>Java</strong> <strong>Serial</strong>iza;on?<br />
XStream is like <strong>Java</strong> <strong>Serial</strong>iza@on on steroids<br />
Can deserialize non-serializable classes: —> many more gadgets available<br />
Reported back in 2013: CVE-2013-7285 by Alvaro Munoz (@pwntester) & Abraham Kang (@KangAbraham)<br />
XStream implemented a blacklist/whitelist protec@on scheme <br />
(by default only blocking java.beans.EventHandler)<br />
Unfortunately devs are not fully aware and s@ll use unprotected or only blacklisted XStream instances<br />
e.g.: CVE-2015-5254 in Apache Ac;veMQ and CVE-2015-5344 in Apache Camel<br />
both by @pwntester, @cschneider4711, @maEhias_kaiser<br />
We found many new gadgets during research<br />
Can’t be fixed by making them non-serializable.<br />
Only fix is applying a whitelist to XStream instance.<br />
… plus most of the ones available for <strong>Java</strong> serializa@on (e.g.: Commons-Collec@ons, Spring, …)<br />
28