Jail Management System - Maricopa County
Jail Management System - Maricopa County
Jail Management System - Maricopa County
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
A Report<br />
to the<br />
Board of<br />
Supervisors<br />
<strong>Maricopa</strong> <strong>County</strong><br />
Internal Audit<br />
Department<br />
Ross L. Tate<br />
<strong>County</strong> Auditor<br />
<strong>Jail</strong> <strong>Management</strong> <strong>System</strong><br />
Application Controls Need<br />
Improvement<br />
May 2012<br />
Executive Summary 1<br />
Introduction 2<br />
IT Control Environment 7<br />
Network Security 9<br />
Personnel Screening and Access Reviews 10<br />
Change <strong>Management</strong> 12<br />
IT Strategic Planning and Project <strong>Management</strong> 13<br />
IT Policies and Procedures 15<br />
Sheriff’s Office Response 16
The mission of <strong>Maricopa</strong> <strong>County</strong> is to provide regional<br />
leadership and fiscally responsible, necessary public services<br />
so that residents can enjoy living in a healthy and safe<br />
community.<br />
The mission of the Internal Audit Department is to provide<br />
objective information on the <strong>County</strong>’s system of internal controls<br />
to the Board of Supervisors so they can make informed<br />
decisions and protect the interests of <strong>County</strong> citizens.<br />
The <strong>County</strong> Auditor reports directly to the <strong>Maricopa</strong> <strong>County</strong><br />
Board of Supervisors, with an advisory reporting relationship<br />
to the Citizen’s Audit Advisory Committee.<br />
Audit Team Members<br />
Eve Murillo, CPA, MBA, CFE, ITIL, Deputy <strong>County</strong> Auditor<br />
Patra Carroll, CPA, MSIM, CIA, ITIL, IT Audit Supervisor<br />
Susan Adams, MBA, CISA, ITIL, CLEA, Senior IT Auditor<br />
KPMG LLP<br />
<strong>Maricopa</strong> <strong>County</strong> Internal Audit<br />
301 West Jefferson Suite 660<br />
Phoenix, AZ 85003<br />
(602) 506-1585<br />
www.maricopa.gov/internal_audit<br />
“Do the Right Things Right!”
301 West Jefferson St<br />
Suite 660<br />
Phx, AZ 85003-2148<br />
Phone: 602-506-1585<br />
Fax: 602-506-8957<br />
www.maricopa.gov<br />
<strong>Maricopa</strong> <strong>County</strong><br />
Internal Audit Department<br />
May 15, 2012<br />
Max W. Wilson, Chairman, Board of Supervisors<br />
Fulton Brock, Supervisor, District I<br />
Don Stapley, Supervisor, District II<br />
Andrew Kunasek, Supervisor, District III<br />
Mary Rose Wilcox, Supervisor, District V<br />
We have completed our FY 2011-12 review of the <strong>Jail</strong> <strong>Management</strong> <strong>System</strong>. The<br />
review was originally scheduled as part of the FY 2009 Sheriff’s Office Custody<br />
Command review. The specific areas reviewed were selected through a formal riskassessment<br />
process.<br />
Highlights of this report include the following:<br />
Information technology controls generally comply with standards<br />
Some application controls need improvement<br />
Policies and procedures need to be formalized<br />
Within this report you will find an executive summary, specific information on the<br />
areas reviewed, and the Sheriff’s Office response to our recommendations. We have<br />
reviewed this information with Sheriff’s Office management and appreciate the<br />
excellent cooperation provided by management and staff. If you have any questions,<br />
or wish to discuss the information presented in this report, please contact Eve<br />
Murillo, Deputy <strong>County</strong> Auditor, at 506-7245.<br />
Sincerely,<br />
Ross L. Tate<br />
<strong>County</strong> Auditor
Executive Summary<br />
IT Control Environment (Page 7)<br />
The <strong>Maricopa</strong> <strong>County</strong> Sheriff’s Office (MCSO) information technology (IT) control<br />
environment generally follows industry standards in key areas.<br />
Network Security (Page 9)<br />
We tested network security controls in four key areas: (1) The Criminal Justice Network, (2)<br />
password management, (3) remote access security, and (4) patch management. Strong network<br />
security controls reduce the likelihood of system vulnerabilities and breaches. Due to the<br />
sensitive nature of this work, we provided MCSO management with detailed findings in a<br />
separate report.<br />
Personnel Screening and Access Reviews (Page 10)<br />
MCSO personnel screening, security awareness training, and account access review processes<br />
could be improved. Incomplete personnel screening and training processes may leave MCSO<br />
vulnerable to potential abuse of sensitive data. Undocumented user access procedures increase<br />
the risk that unauthorized users may inappropriately access or modify criminal justice<br />
information. MCSO should consider strengthening personnel screening policies, provide user<br />
awareness training, and conduct user access reviews.<br />
Change <strong>Management</strong> (Page 12)<br />
MCSO does not have a formalized change management process for authorizing, testing, and<br />
approving the <strong>Jail</strong> <strong>Management</strong> <strong>System</strong> (JMS) changes. JMS developers have unrestricted<br />
access to the application. If unauthorized or untested changes are introduced into JMS, they<br />
could create data integrity and system availability issues. MCSO should strengthen its change<br />
management controls.<br />
IT Strategic Planning and Project <strong>Management</strong> (Page 13)<br />
MCSO does not have a formal IT strategic plan or project management process that effectively<br />
aligns IT resource spending with MCSO’s core mission. A strategic plan helps ensure that<br />
critical IT projects are completed efficiently and economically. MCSO should consider<br />
developing an IT strategic plan and project management framework.<br />
IT Policies and Procedures (Page 15)<br />
MCSO does not have formal JMS security policies and procedures that should address Criminal<br />
Justice Information Services Security Policy requirements. Formalized IT procedures can help<br />
MCSO implement security and other control activities during personnel absences and turnover.<br />
MCSO should develop formalized JMS IT policies and procedures.<br />
<strong>Maricopa</strong> <strong>County</strong> Internal Audit 1 <strong>Jail</strong> <strong>Management</strong> <strong>System</strong>–May 2012
Introduction<br />
Background<br />
The <strong>Jail</strong> <strong>Management</strong> <strong>System</strong> (JMS) is the primary computer system used by the <strong>Maricopa</strong><br />
<strong>County</strong> Sheriff’s Office (MCSO) to manage jail operations and inmates. JMS includes<br />
information on booking, fingerprinting, food services, housing, transportation, health, inmate<br />
property, and bonding.<br />
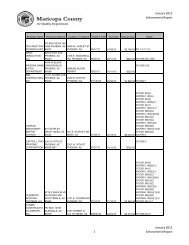
<strong>Jail</strong> <strong>Management</strong> <strong>System</strong> Organization<br />
The MCSO Technology Bureau (MCSO IT) is responsible for maintaining and supporting all<br />
MCSO business systems, including JMS. MCSO has approximately 3,500 employees and<br />
operates 24 hours a day, 7 days a week. MCSO IT’s 65 employees are responsible for ensuring<br />
that critical applications like JMS are available to support those operations. Below is the MCSO<br />
IT organization chart:<br />
Inmate Telephone<br />
<strong>System</strong> (ITS)<br />
Administrator<br />
Commander<br />
Business<br />
Applications<br />
Services<br />
<strong>Jail</strong> <strong>Management</strong> <strong>System</strong><br />
Deputy Director<br />
Commander<br />
Desktop & Client<br />
Support<br />
Commander<br />
Mainframe<br />
Operations &<br />
Technical Support<br />
Commander<br />
Telecom<br />
Technology<br />
JMS Migration Team<br />
MCSO IT began developing JMS in 1990 and moved it into production in 1995. JMS runs on a<br />
mainframe, a powerful computer used for critical applications and bulk data processing. MCSO<br />
employees enter information into JMS throughout an inmate’s incarceration. JMS includes<br />
judicial information (inmate charges, holds, court dispositions, and bond and fine amounts) and<br />
administrative information (personal property inventory, locker assignment, housing location,<br />
restrictions, and emergency medical information). MCSO processes approximately 105 million<br />
transactions per year through the JMS system.<br />
<strong>Maricopa</strong> <strong>County</strong> Internal Audit 2 <strong>Jail</strong> <strong>Management</strong> <strong>System</strong>–May 2012
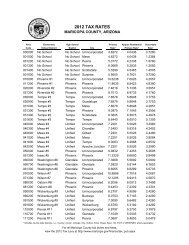
JMS Interfaces<br />
JMS communicates critical information to other justice and law enforcement agencies. Below is<br />
a brief summary of key JMS interfaces.<br />
ICJIS - JMS data feeds into the Integrated Criminal Justice Information <strong>System</strong> (ICJIS) which is<br />
distributed to other <strong>County</strong> law enforcement agencies, including the Courts, <strong>County</strong> Attorney,<br />
Clerk of the Superior Court, and Adult and Juvenile Probation. With the exception of touch-pay<br />
kiosks and inmate telephones, all JMS information flows through the ICJIS interface. MCSO<br />
employees also use JMS (through the ICJIS electronic data exchange) to access state and federal<br />
criminal justice information.<br />
ACJIS - The Arizona Criminal Justice Information <strong>System</strong> (ACJIS) acts as the central state<br />
repository for collecting, storing, and disseminating Arizona criminal history records and related<br />
justice information. The Department of Public Safety (DPS) maintains ACJIS and allows<br />
Arizona law enforcement agencies to share information.<br />
CJIS and NCIC - The Criminal Justice Information Services (CJIS) Division and the National<br />
Crime Information Center (NCIC) are supported by the Federal Bureau of Investigation (FBI),<br />
and are electronic crime data clearinghouses that can be accessed by most criminal justice<br />
agencies nationwide.<br />
The graph below illustrates how JMS interfaces with other agencies and systems:<br />
ACJIS - Arizona Criminal<br />
Justice Information <strong>System</strong><br />
DPS criminal database<br />
CJIS - Criminal<br />
Justice<br />
Information<br />
Services<br />
NCIC - Nation<br />
Crime<br />
Information<br />
Center<br />
FBI criminal database<br />
ICJIS - Integrated<br />
Criminal Justice<br />
Information <strong>System</strong><br />
<strong>Maricopa</strong> <strong>County</strong> Internal Audit 3 <strong>Jail</strong> <strong>Management</strong> <strong>System</strong>–May 2012<br />
<strong>Jail</strong><br />
<strong>Management</strong><br />
<strong>System</strong>
JMS Environment<br />
Because JMS is a mission critical application, MCSO has been assessing future system<br />
requirements. MCSO IT reports several challenges with the current JMS environment.<br />
Mainframe - The mainframe on which JMS is running is supported by the vendor through 2014.<br />
The FY 2012 mainframe software license costs are $1.1 million, with an automatic annual 10<br />
percent increase, and annual mainframe hardware costs are $95,000. MCSO intends to<br />
renegotiate the contract during FY 2014. MCSO reports that for strategic purposes, MCSO may<br />
replace the existing mainframe, but has not submitted a budget request.<br />
Aging Workforce - JMS is a large and complex seventeen-year old system; its software is written<br />
in COBOL, a programming language that is no longer being taught in many universities.<br />
According to MCSO IT, as employees responsible for maintaining JMS retire, it may become<br />
difficult and expensive to replace them, negatively affecting the long-term maintenance of the<br />
system. The <strong>County</strong>’s Office of <strong>Management</strong> and Budget is completing a staffing study for<br />
MCSO IT.<br />
Scope and Methodology<br />
Audit Objectives<br />
The objectives of this audit were to determine that:<br />
Approach<br />
Effective general controls are in place to provide reasonable assurance that information<br />
systems are secure and available to users.<br />
Information technology general controls are overarching policies and procedures that<br />
apply to the network and organization-wide information systems. Reviewing general<br />
controls provides assurance that the controls are working as intended and that systems<br />
are appropriately supporting operations.<br />
Critical application controls are in place to provide reasonable assurance of the<br />
confidentiality, integrity, and availability of data.<br />
Application controls are specific to a single information system, such as JMS.<br />
Application controls are activities designed to support operations, and ensure the<br />
confidentiality, integrity and availability of application data.<br />
To achieve the audit objectives, we:<br />
Interviewed key employees from MCSO, the ICJIS agency, and the Office of Enterprise<br />
Technology (OET)<br />
Obtained and reviewed policies and procedures related to:<br />
o IT governance<br />
o Programs and data access (including application security, operating system<br />
security, database security, user authentication, and segregation of duties)<br />
<strong>Maricopa</strong> <strong>County</strong> Internal Audit 4 <strong>Jail</strong> <strong>Management</strong> <strong>System</strong>–May 2012
o Program development (including project management, authorization, technical<br />
and user testing, user training, and developer/production segregation of duties)<br />
o Program change management (changes to existing applications – including<br />
emergency changes and monitoring, developer segregation of duties, and testing<br />
of requested changes)<br />
o Computer operations (including disaster recovery, system backups, job<br />
scheduling, data conversion, system interfaces, and problem management)<br />
Observed MCSO personnel using JMS<br />
Identified key IT and application controls<br />
MCSO data center IT general controls were not considered during the course of this review.<br />
Internal Audit conducted a separate MCSO Data Center Audit where applicable IT general<br />
controls were considered; the report was issued March 15, 2012.<br />
Due to the sensitive nature of network security issues, the results of our network security testing<br />
were detailed in a separate memo to management.<br />
Audit Timeframe<br />
Our audit included data from July 2010 through October 2011.<br />
Auditing Standards<br />
We conducted this performance audit in accordance with generally accepted government<br />
auditing standards. These standards require the following:<br />
An independent audit staff and audit organization<br />
An objective audit staff performing the work<br />
A competent staff, current with continuing education requirements<br />
A system of quality control procedures<br />
Sufficient and appropriate evidence based on audit objectives<br />
<strong>Maricopa</strong> <strong>County</strong> Internal Audit 5 <strong>Jail</strong> <strong>Management</strong> <strong>System</strong>–May 2012
(Blank Page)<br />
<strong>Maricopa</strong> <strong>County</strong> Internal Audit 6 <strong>Jail</strong> <strong>Management</strong> <strong>System</strong>–May 2012
Issue 1 IT Control Environment<br />
Summary<br />
The <strong>Maricopa</strong> <strong>County</strong> Sheriff’s Office (MCSO) information technology (IT) control<br />
environment generally follows industry standards in key areas.<br />
Criteria<br />
COBIT, an international, generally–accepted, IT control framework, gives guidance about<br />
control requirements, technical issues, and business risks. Internal Audit uses COBIT as an<br />
authority for good IT control practices. The COBIT framework recommends:<br />
Defining and implementing a technology infrastructure plan, architecture, and standards<br />
that leverage technology opportunities<br />
Establishing transparent, flexible, and responsive IT organizational structures, and<br />
defining and implementing IT processes<br />
Segregating responsibilities throughout the enterprise<br />
Establishing preventative and detective controls to protect information systems and<br />
technology from malware (e.g., viruses, worms, spyware, and spam)<br />
Implementing automated solutions to support source code management and change<br />
migration between production environments<br />
Meeting operational service levels for scheduled data processing, protecting sensitive<br />
output, and monitoring and maintaining infrastructure<br />
Establishing interface controls to ensure the accuracy and completeness of data transfers<br />
Establishing backup controls to ensure data availability<br />
Establishing procedures to identify, resolve, and document system and application issues<br />
<strong>Maricopa</strong> <strong>County</strong> Internal Audit 7 <strong>Jail</strong> <strong>Management</strong> <strong>System</strong>–May 2012
Condition<br />
Through observation, limited testing, and interviews, we determined that the following key IT<br />
controls generally followed the COBIT framework.<br />
Information<br />
Architecture<br />
Roles and<br />
Responsibilities<br />
IT Controls Reviewed that Appear to be Adequate<br />
Area Description<br />
MCSO uses the National Crime Information Center (NCIC) and the<br />
Arizona Criminal Justice Information <strong>System</strong> (ACJIS) for<br />
developing applications to interface with state and federal systems.<br />
MCSO has defined roles and responsibilities for supporting IT and<br />
information security responsibilities.<br />
Super User Access JMS super user access appears appropriate.<br />
Computer Virus<br />
Protection<br />
Version Control<br />
Software<br />
Batch Processing and<br />
Job Scheduling<br />
MCSO maintains computer virus protection software for<br />
workstations and servers. During the testing period, virus<br />
definitions were updated daily.<br />
MCSO uses version control software to help manage and control<br />
the development and migration of software and configuration<br />
changes.<br />
MCSO batch and job scheduling procedures are in place and<br />
appear adequate.<br />
<strong>System</strong> Interfaces MCSO system interfaces appear adequately controlled through the<br />
Integrated Criminal Justice Information <strong>System</strong> (ICJIS).<br />
Tape Backups MCSO performs regular backups and rotates its backups between<br />
its primary data centers.<br />
Problem <strong>Management</strong> MCSO tracks, responds, and documents help desk activity.<br />
Recommendation<br />
None, for information only.<br />
<strong>Maricopa</strong> <strong>County</strong> Internal Audit 8 <strong>Jail</strong> <strong>Management</strong> <strong>System</strong>–May 2012
Issue 2 Network Security<br />
Summary<br />
We tested network security controls in four key areas: (1) The Criminal Justice Network, (2)<br />
password management, (3) remote access security, and (4) patch management. Strong network<br />
security controls reduce the likelihood of system vulnerabilities and breaches.<br />
We used COBIT standards and ACJIS requirements governing these areas in our review. Due to<br />
the sensitive nature of this work, we provided MCSO management with detailed findings in a<br />
separate report.<br />
<strong>Maricopa</strong> <strong>County</strong> Internal Audit 9 <strong>Jail</strong> <strong>Management</strong> <strong>System</strong>–May 2012
Issue 3 Personnel Screening and Access<br />
Reviews<br />
Summary<br />
MCSO personnel screening, security awareness training, and account access review processes<br />
could be improved. Incomplete personnel screening and training processes may leave MCSO<br />
vulnerable to potential abuse of sensitive data. Undocumented user access procedures increase<br />
the risk that unauthorized users may inappropriately access or modify criminal justice<br />
information. MCSO should consider strengthening personnel screening policies, provide user<br />
awareness training, and conduct user access reviews.<br />
Criteria<br />
The Arizona Criminal Justice Information <strong>System</strong> (ACJIS) Operating Manual requires that<br />
MCSO conduct criminal justice employment background checks, including a fingerprint check,<br />
for all ACJIS terminal operators. All terminal operators and technical personnel who access the<br />
ACJIS system must be certified through the Terminal Operator Certification (TOC) Program.<br />
The Federal Criminal Justice Information <strong>System</strong> (CJIS) Security Policy requires that MCSO<br />
conduct security policy training for employees based on their job duties. Key training areas<br />
include the handling of criminal justice information, social engineering, media protection,<br />
malware prevention, and patch management. CJIS has established training guidelines for<br />
different employee groups.<br />
COBIT recommends:<br />
Condition<br />
Recruiting and training a competent workforce, and conducting background checks<br />
Educating and training users according to business requirements<br />
Documenting procedures for requesting, establishing, issuing, modifying, and closing<br />
user accounts<br />
Personnel Screening<br />
MCSO’s procedures appear to be in compliance with state (ACJIS) background check policies.<br />
A small number of employees from the Office of Public Defender, Office of <strong>Management</strong> and<br />
Budget, and the Department of Finance, access JMS detention and booking information that is<br />
not part of the state criminal database (ACJIS). Currently, individuals from these agencies do<br />
not go through the required background check, and the required training (TOC and security<br />
awareness).<br />
<strong>Maricopa</strong> <strong>County</strong> Internal Audit 10 <strong>Jail</strong> <strong>Management</strong> <strong>System</strong>–May 2012
Security Awareness Training<br />
MCSO’s TOC training focuses on authorized access and dissemination of criminal justice<br />
information, but does not include all of the security awareness areas required in CJIS policy.<br />
CJIS mandates specific training topics regarding the proper handling of criminal justice<br />
information, based on a user’s exposure to and involvement with the criminal justice<br />
information.<br />
Account Access Reviews<br />
Although MCSO validates TOC identification numbers through a semi-annual, Arizona<br />
Department of Public Safety (DPS) review and reconciliation process, it does not have a<br />
formalized process for validating all JMS and operating system user accounts and their<br />
associated access permissions.<br />
Effect<br />
Personnel Screening - Incomplete personnel screening processes may leave MCSO vulnerable to<br />
potential abuse of sensitive law enforcement data.<br />
Security Awareness Training - JMS users that do not receive the mandated CJIS training may<br />
inadvertently mishandle criminal justice information.<br />
Account Access Reviews - Informally managed user permissions increases the risk that<br />
unauthorized users may inappropriately access or modify criminal justice information.<br />
Cause<br />
Personnel Screening - MCSO has not developed a formalized background check policy for JMS<br />
users without ACJIS database permissions.<br />
Security Awareness Training - Although MCSO’s TOC training program aligns with DPS<br />
guidance, these requirements do not meet the minimum CJIS Security Policy standards.<br />
Account Access Reviews - MCSO has relied on the extensive hands-on experience of longtenured<br />
employees to compensate for formalized procedures, and has invested its resources on<br />
day-to-day functions rather than documenting its operations.<br />
Recommendations<br />
MCSO should consider:<br />
A. Developing a personnel screening policy that covers JMS users who do not access ACJIS<br />
data.<br />
B. Enhancing the security awareness training program to align with the CJIS Security Policy<br />
requirements.<br />
C. Developing formalized policies and procedures to periodically review and validate JMS<br />
access accounts and permissions. Leading practices suggest user access reviews be<br />
conducted at least annually.<br />
<strong>Maricopa</strong> <strong>County</strong> Internal Audit 11 <strong>Jail</strong> <strong>Management</strong> <strong>System</strong>–May 2012
Issue 4 Change <strong>Management</strong><br />
Summary<br />
MCSO does not have a formalized change management process for authorizing, testing, and<br />
approving the <strong>Jail</strong> <strong>Management</strong> <strong>System</strong> (JMS) changes. JMS developers have unrestricted<br />
access to the application. If unauthorized or untested changes are introduced into JMS, they<br />
could create data integrity and system availability issues. MCSO should strengthen its change<br />
management controls.<br />
Criteria<br />
COBIT recommends the following change management practices:<br />
Condition<br />
Ensuring applications are aligned with business requirements<br />
Managing IT changes in a formal, documented, and controlled fashion<br />
MCSO has not formalized its change management policy and procedures. Change management<br />
procedures standardize the system change processes. Currently, the MCSO Technology Bureau<br />
receives and coordinates requested changes via email with the agency requestor. Approvals are<br />
handled informally and are not consistently documented before being moved into production<br />
(where “live” transaction processing occurs). Developer access to the JMS production<br />
environment is not appropriately restricted.<br />
Effect<br />
Formal change management procedures introduce system changes in a controlled and<br />
coordinated manner and prevent unplanned, unauthorized, and untested changes to JMS.<br />
Effective change management procedures also reduce the risk of service disruption and<br />
associated costs.<br />
Cause<br />
MCSO Technology Bureau staff report that resource constraints have prevented them from<br />
documenting change management procedures. Instead, they have relied on their extensive JMS<br />
experience to compensate for this control weakness.<br />
Recommendations<br />
MCSO should:<br />
A. Develop a formalized process for authorizing, testing, and approving JMS changes.<br />
B. Limit developers’ access to JMS and/or implement system monitoring controls to identify<br />
and review the appropriateness of system changes.<br />
<strong>Maricopa</strong> <strong>County</strong> Internal Audit 12 <strong>Jail</strong> <strong>Management</strong> <strong>System</strong>–May 2012
Issue 5 IT Strategic Planning and Project<br />
<strong>Management</strong><br />
Summary<br />
MCSO does not have a formal IT strategic plan or project management process that effectively<br />
aligns IT resource spending with MCSO’s core mission. A strategic plan helps ensure that<br />
critical IT projects are completed efficiently and economically. MCSO should consider<br />
developing an IT strategic plan and project management framework.<br />
Criteria<br />
COBIT recommends establishing an IT strategic plan, an IT steering committee, and a program<br />
and project management framework for IT projects.<br />
Condition<br />
IT Strategic Planning<br />
MCSO does not have a formalized IT strategic plan. Instead, MCSO IT relies on a <strong>System</strong>s<br />
Aging Report to classify applications by their estimated useful life and to prioritize future IT<br />
needs. MCSO IT prepares this report bi-annually and reviews it with other MCSO bureaus for<br />
reasonableness. Recently, MCSO issued a Request for Proposal to upgrade integrated Computer<br />
Aided Dispatch, Records <strong>Management</strong>, Civil Process, and Mobile <strong>System</strong>s resulting, in part from<br />
its review of the <strong>System</strong>s Aging Report.<br />
IT Project <strong>Management</strong><br />
MCSO IT does not use a formalized project management process to oversee large or critical<br />
systems and does not use a steering committee to oversee key project decisions. Instead,<br />
developmental projects are tracked in a spreadsheet and managed informally. The MCSO IT<br />
Deputy Director receives weekly project status reports from various MCSO bureaus and uses this<br />
information to update other MCSO management team members on a monthly basis. A formal<br />
project management methodology could enhance future JMS upgrades.<br />
Effect<br />
MCSO may not be effectively investing financial resources in IT and may be investing in<br />
unsuitable or underperforming IT systems. Also, MCSO IT projects may not: 1) meet desired<br />
functionality requirements, 2) meet completion deadlines, 3) meet established budgets, and 4)<br />
align with MCSO’s strategic direction.<br />
Cause<br />
MCSO does not have a formalized IT governance process that includes the implementation of an<br />
IT strategic plan and project management methodology. MCSO IT’s resource allocation has<br />
been devoted to operating activities (technical, financial, and scheduling).<br />
<strong>Maricopa</strong> <strong>County</strong> Internal Audit 13 <strong>Jail</strong> <strong>Management</strong> <strong>System</strong>–May 2012
Recommendations<br />
MCSO should consider:<br />
A. Developing an IT strategic plan that supports the overall MCSO strategy.<br />
B. Developing a formalized project management methodology to help manage and control<br />
IT-related projects.<br />
<strong>Maricopa</strong> <strong>County</strong> Internal Audit 14 <strong>Jail</strong> <strong>Management</strong> <strong>System</strong>–May 2012
Issue 6 IT Policies and Procedures<br />
Summary<br />
MCSO does not have formal JMS security policies and procedures that should address Criminal<br />
Justice Information Services Security Policy requirements. Formalized IT procedures can help<br />
MCSO implement security and other control activities during personnel absences and turnover.<br />
MCSO should develop formalized JMS IT policies and procedures.<br />
Criteria<br />
The Federal Criminal Justice Information <strong>System</strong> (CJIS) Security Policy requires that MCSO<br />
develop formal, documented procedures to facilitate the implementation of both federal and local<br />
security policies.<br />
COBIT recommends that IT organizations develop and communicate IT policies throughout the<br />
organization.<br />
Condition<br />
MCSO’s policies and procedures do not include formalized information security policies and<br />
procedures over the following key IT processes:<br />
Effect<br />
JMS and remote user account management<br />
JMS security log reviews<br />
Change management and program development<br />
Patch management<br />
Disaster recovery<br />
Without formalized IT policies and procedures, MCSO may not be able to perform security and<br />
control activities during employee absences and staffing changes. Also, ACJIS (Arizona<br />
Criminal Justice Information <strong>System</strong>) and NCIC (National Crime Information Center) may<br />
remove MCSO from their networks because of incomplete security guideline compliance.<br />
Cause<br />
MCSO IT personnel rely on their extensive hands-on experience in operating JMS in lieu of<br />
formal policies and procedures and have focused their limited resources on day-to-day operations<br />
rather than documenting IT operations.<br />
Recommendation<br />
MCSO should develop formalized JMS IT policies and procedures.<br />
<strong>Maricopa</strong> <strong>County</strong> Internal Audit 15 <strong>Jail</strong> <strong>Management</strong> <strong>System</strong>–May 2012
Sheriff’s Office Response<br />
<strong>Maricopa</strong> <strong>County</strong> Internal Audit 16 <strong>Jail</strong> <strong>Management</strong> <strong>System</strong>–May 2012
Issue #1:<br />
For Information. No response required.<br />
Issue #2:<br />
<strong>Jail</strong> <strong>Management</strong> <strong>System</strong> (JMS)<br />
Sheriff's Office- JMS Report<br />
February 2012<br />
Audit Response - April 25, 2012<br />
MCSO network security controls could be strengthened in four key areas: (1) the<br />
Criminal Justice Network, (2) password parameters, (3) remote access security, and (4)<br />
patch management. Stronger network security controls reduce the likelihood of system<br />
vulnerabilities and breaches. MCSO should strengthen network security controls in<br />
these areas.<br />
Response requested for Agency Memo only. See Agency memo (separate).<br />
Issue #3:<br />
MCSO personnel screening, security awareness training, and account access review<br />
processes could be improved. Incomplete personnel screening and training processes<br />
may leave MeSO vulnerable to potential abuse of sensitive data. Undocumented user<br />
access procedures increase the risk that unauthorized users may inappropriately<br />
access or modify criminal justice information. MCSO should consider strengthening<br />
personnel screening policies, provide user awareness training, and conduct user access<br />
reviews.<br />
Recommendation A: MCSO should consider developing a personnel screening policy<br />
that covers JMS users who do not access ACJIS data.<br />
Response: <strong>Management</strong> accepts the risk of this issue. This recommendation applies to a<br />
very small number of <strong>Maricopa</strong> <strong>County</strong> Office of Public Defender, Office of <strong>Management</strong><br />
and Budget and Department of Finance employees. These users access limited data that<br />
is not criminal history information.<br />
Target Completion Date: N/A<br />
Benefits/Costs: Increased accountability and control.<br />
Recommendation B: MCSO should consider enhancing the security awareness training<br />
program to align with the CJIS Security Policy requirements.<br />
Response: Completed. Security awareness training has been automated by the Arizona<br />
Department of Public Safety. <strong>County</strong> employees will complete the computer-based<br />
Page 1 of 4
<strong>Jail</strong> <strong>Management</strong> <strong>System</strong> (JMS)<br />
Sheriff's Office- JMS Report<br />
February 2012<br />
Audit Response - April 25, 2012<br />
training and the test for TOC certification electronically. MCSO will no longer be<br />
conducting security awareness training.<br />
Completion Date: 4/13/12<br />
Benefits/Costs: Increased accountability and control.<br />
Recommendation C: MCSO should consider developing formalized policies and<br />
procedures to periodically review and validate JMS access accounts and permissions.<br />
Leading practices suggest users access reviews be conducted at least annually.<br />
Response: Concur. JMS access accounts and permissions will be reviewed annually<br />
corresponding with a TOC review that is conducted.<br />
Target Completion Date: 6/30/12<br />
Benefits/Costs: Increased accountability and control.<br />
Issue #4:<br />
MCSO does not have a formalized change management process for authorizing,<br />
testing, and approving the <strong>Jail</strong> <strong>Management</strong> <strong>System</strong> (JMS) changes. JMS developers<br />
have unrestricted access to the application. If unauthorized or untested changes are<br />
introduced into JMS, they could create data integrity and system availability issues.<br />
MCSO should strengthen its change management controls.<br />
Recommendation A: MCSO should develop a formalized process for authorizing,<br />
testing, and approving ...IMS changes.<br />
Response: Concur. Changes to JMS "base" programming are rare (five or six annually)<br />
and MCSO's limited technology staff has allowed this process to be very informal.<br />
However, as technology staff increases and the Office moves forward with this and other<br />
systems, this process will have to be formalized.<br />
Target Completion Date: 1/31/13<br />
Benefits/Costs: Increased accountability and control.<br />
Page 2 of 4
<strong>Jail</strong> <strong>Management</strong> <strong>System</strong> (JMS)<br />
Sheriff's Office- JMS Report<br />
February 2012<br />
Audit Response - April 25, 2012<br />
Recommendation B: MCSO should limit developers' access to JMS and/or implement<br />
system monitoring controls to identify and review the appropriateness of system changes.<br />
Response: Concur. This issue will be addressed in the formal change management<br />
process referenced above.<br />
Target Completion Date: 1/31/13<br />
Benefits/Costs: Increased accountability and control.<br />
Issue #5:<br />
MCSO does not have a formal IT strategic plan or project management process that<br />
effectively aligns IT resource spending with MCSO's core mission. A strategic plan<br />
helps ensure that critical IT projects are completed efficiently and economically.<br />
Recommendation A: MCSO should consider developing an IT strategic plan that<br />
supports the overall MCSO strategy.<br />
Response: Concur. As a requirement of the Board of Supervisors' Resolution dated June<br />
20,2011, MCSO and OET are reviewing current systems and future requirements to<br />
develop a strategic technology roadmap for MCSO. This comprehensive plan will closely<br />
align technology initiatives with MCSO core business functions.<br />
Target Completion Date: 12/31/12<br />
Benefits/Costs: Increased accountability and control.<br />
Recommendation B: MCSO should consider developing a formalized project<br />
management methodology to help manage and control IT-related projects.<br />
Response: Concur. MCSO recognizes the importance of a formalized project<br />
management methodology. As additional personnel are employed based upon the<br />
staffing study currently in process, resources will be applied to formalizing the project<br />
management process.<br />
Target Completion Date: 4/30/13<br />
Benefits/Costs: Increased accountability and control.<br />
Page 3 of 4