iPhone Rootkit? There's an App for that! - Reverse Engineering Mac ...
iPhone Rootkit? There's an App for that! - Reverse Engineering Mac ... iPhone Rootkit? There's an App for that! - Reverse Engineering Mac ...
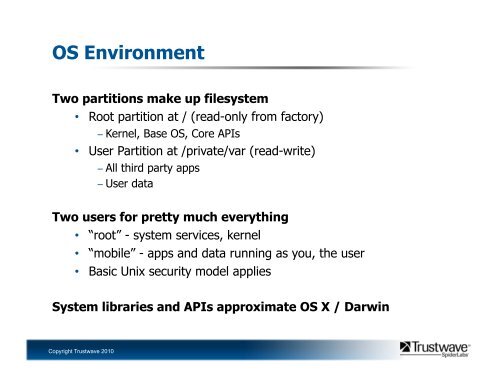
OS EnvironmentTwo partitions make up filesystem• Root partition at / (read-only from factory)− Kernel, Base OS, Core APIs• User Partition at /private/var (read-write)− All third party apps− User dataTwo users for pretty much everything• “root” - system services, kernel• “mobile” - apps and data running as you, the user• Basic Unix security model appliesSystem libraries and APIs approximate OS X / DarwinCopyright Trustwave 2010
Application SecurityCode signing• All exe’s from the AppStore must be signed by Apple• Signatures stored in mach-o header section• Check implemented in kernel as through an enhanced exec()system callSandbox• Applications run as user “mobile”• Chroot sandbox (ostensibly) restricts apps to their own data• Can’t access the OS or other apps’ data• Entitlements also restrict some functionality− Programs need special entitlements for things like debugging− Entitlements are trivial to add, but during exploitation this factors inCopyright Trustwave 2010
- Page 5 and 6: iPhone/iOS Security Overview
- Page 7: Architecture OverviewApplications P
- Page 11 and 12: Jailbreaking Overview
- Page 13 and 14: Jailbreakme.com A Thing to Behold
- Page 15 and 16: What it looks likeVisit h'p://jailb
- Page 17 and 18: Weaponizing
- Page 19 and 20: Patch PlanReversing the installui.d
- Page 21 and 22: My “Big Fat Rootkit”… so farC
- Page 23 and 24: Set-upA vanilla un-jailbroken iPhon
- Page 25 and 26: Hardware: Mic and AudioAudio record
- Page 27 and 28: Dumping Process DataSeveral interes
- Page 29 and 30: Targeting iOS ApplicationsiOS isn
- Page 31 and 32: Demo App Backdoor
- Page 33 and 34: Binary Reversing Prep (continued…
- Page 35 and 36: No More SecretsHint: find the LC
- Page 37 and 38: Mach Binary Encryption (continued
- Page 39 and 40: What’s your point?For starters…
- Page 41 and 42: Objective-C Method HookingIt’s ca
- Page 43 and 44: Objective-C Method Hook ExampleLets
- Page 45 and 46: Injecting Our LibraryConventionally
- Page 47 and 48: ConclusionsLots of security researc
- Page 49 and 50: Reversing Redux: The Binary “star
- Page 51 and 52: … continued: eggMalformed Times-
- Page 53 and 54: class-dump on installui.dylib (aka
OS EnvironmentTwo partitions make up filesystem• Root partition at / (read-only from factory)− Kernel, Base OS, Core APIs• User Partition at /private/var (read-write)− All third party apps− User dataTwo users <strong>for</strong> pretty much everything• “root” - system services, kernel• “mobile” - apps <strong>an</strong>d data running as you, the user• Basic Unix security model appliesSystem libraries <strong>an</strong>d APIs approximate OS X / DarwinCopyright Trustwave 2010