eTrust CA-Top Secret Security for z/OS and OS ... - SupportConnect
eTrust CA-Top Secret Security for z/OS and OS ... - SupportConnect eTrust CA-Top Secret Security for z/OS and OS ... - SupportConnect
z/OS and OS/390 Security Server SupportDCE Security ServerThe DCE Security Server is a separate security product that providesauthentication services for users and servers running DCE applications.In a DCE environment, one DCE Security Server must exist. A DCE securityserver provides a central hub for system entry validation and single-sign onauthentication for all DCE platforms within a connected DCE environment. Akey concept of a DCE security server is that it provides an independent orso-called third-party platform in which to validate and authenticate securityrequests. This concept provides obvious security advantages.For example, when a user passes from one DCE platform to another, the targetplatform passes information about the user (so-called user credentials) alongwith other information to the DCE security server for authentication andauthorization. The DCE security server authenticates such requests by checkingthe supplied user credentials against those stored in the DCE security server'ssecurity repository and/or security registry. In performing this authentication,the DCE security server follows an authentication algorithm, which involves notonly the user credentials but also involves encryption keys known for eachplatform. The algorithm is standards-based and is platform independent. As aresult, multiple vendors and platforms offer a DCE security server.IBM's z/OS and OS/390 OE/DCE Security Server product allows an IBMmainframe to perform these functions.With z/OS and OS/390 O/E DCE security server, eTrust CA-Top Secret isutilized mainly to act as a repository for information needed to support the DCEauthentication process. In particular, the eTrust CA-Top Secret is used to holdDCE-specific userid information and encryption keys. Most notably, a 'DCEsegment' can now be defined for any userid. The DCE userid segment allows sixDCE-specific fields to be maintained for any userid. For example, one fieldnamed DCEKEY identifies each user's DCE password. During authentication, theDCE security server retrieves this and other information from eTrust CA-TopSecret following formal SAF interfaces. This information is then used separatelyto authenticate and authorize the DCE security server request. As stated, eTrustCA-Top Secret acts mainly as a repository for DCE information.eTrust CA-Top Secret provides for the following functions:■■■■support for the DCE segment for any userid;support for the KEYSMSTR resource class used to hold keys for DCEpassword encryption;support for the DCEUUIDS resclass used to track the correspondencebetween z/OS or OS/390 userids and DCE UIDs;support for four new callable services used to exchange information betweenthe ESM and the DCE security server.1–96 Cookbook
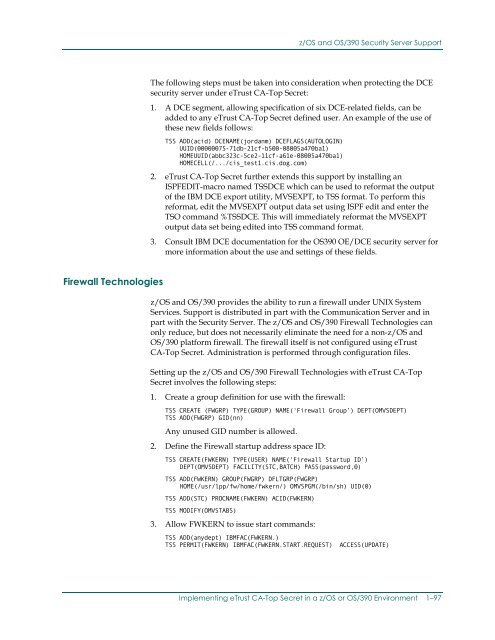
z/OS and OS/390 Security Server SupportThe following steps must be taken into consideration when protecting the DCEsecurity server under eTrust CA-Top Secret:1. A DCE segment, allowing specification of six DCE-related fields, can beadded to any eTrust CA-Top Secret defined user. An example of the use ofthese new fields follows:TSS ADD(acid) DCENAME(jordanm) DCEFLAGS(AUTOLOGIN)UUID(00000075-71db-21cf-b500-08005a470ba1)HOMEUUID(abbc323c-5ce2-11cf-a61e-08005a470ba1)HOMECELL(/.../cis_test1.cis.dog.com)2. eTrust CA-Top Secret further extends this support by installing anISPFEDIT-macro named TSSDCE which can be used to reformat the outputof the IBM DCE export utility, MVSEXPT, to TSS format. To perform thisreformat, edit the MVSEXPT output data set using ISPF edit and enter theTSO command %TSSDCE. This will immediately reformat the MVSEXPToutput data set being edited into TSS command format.3. Consult IBM DCE documentation for the OS390 OE/DCE security server formore information about the use and settings of these fields.Firewall Technologiesz/OS and OS/390 provides the ability to run a firewall under UNIX SystemServices. Support is distributed in part with the Communication Server and inpart with the Security Server. The z/OS and OS/390 Firewall Technologies canonly reduce, but does not necessarily eliminate the need for a non-z/OS andOS/390 platform firewall. The firewall itself is not configured using eTrustCA-Top Secret. Administration is performed through configuration files.Setting up the z/OS and OS/390 Firewall Technologies with eTrust CA-TopSecret involves the following steps:1. Create a group definition for use with the firewall:TSS CREATE (FWGRP) TYPE(GROUP) NAME(‘Firewall Group’) DEPT(OMVSDEPT)TSS ADD(FWGRP) GID(nn)Any unused GID number is allowed.2. Define the Firewall startup address space ID:TSS CREATE(FWKERN) TYPE(USER) NAME(‘Firewall Startup ID’)DEPT(OMVSDEPT) FACILITY(STC,BATCH) PASS(password,0)TSS ADD(FWKERN) GROUP(FWGRP) DFLTGRP(FWGRP)HOME(/usr/lpp/fw/home/fwkern/) OMVSPGM(/bin/sh) UID(0)TSS ADD(STC) PROCNAME(FWKERN) ACID(FWKERN)TSS MODIFY(OMVSTABS)3. Allow FWKERN to issue start commands:TSS ADD(anydept) IBMFAC(FWKERN.)TSS PERMIT(FWKERN) IBMFAC(FWKERN.START.REQUEST) ACCESS(UPDATE)Implementing eTrust CA-Top Secret in a z/OS or OS/390 Environment 1–97
- Page 55 and 56: WebSphere Application Server for z/
- Page 57 and 58: Lotus Domino Go Webserver/* PERMITT
- Page 59 and 60: Lotus Domino Go WebserverTo disable
- Page 61 and 62: Lotus Notes and Novell Directory Se
- Page 63 and 64: Digital Certificate SupportGeneral
- Page 65 and 66: Digital Certificate SupportFOR|UNTI
- Page 67 and 68: Digital Certificate SupportDCDSN(re
- Page 69 and 70: Digital Certificate SupportNote: In
- Page 71 and 72: Digital Certificate SupportYou can
- Page 73 and 74: Digital Certificate SupportCase #2.
- Page 75 and 76: Digital Certificate SupportImportan
- Page 77 and 78: Digital Certificate SupportAdding a
- Page 79 and 80: Digital Certificate SupportReconnec
- Page 81 and 82: Digital Certificate SupportTSS LIST
- Page 83 and 84: Certificate Name Filtering SupportT
- Page 85 and 86: Certificate Name Filtering SupportI
- Page 87 and 88: Certificate Name Filtering SupportD
- Page 89 and 90: Certificate Name Filtering SupportL
- Page 91 and 92: KerberosKerberosetrust CA-Top Secre
- Page 93 and 94: KerberosThe command syntax for this
- Page 95 and 96: KerberosThe following command creat
- Page 97 and 98: Mapping of Foreign EnvironmentsMapp
- Page 99 and 100: Mapping of Foreign EnvironmentsMapp
- Page 101 and 102: Distributed File Server SMB SUPPORT
- Page 103 and 104: NFS (Network File System)The first
- Page 105: z/OS and OS/390 Security Server Sup
- Page 109 and 110: z/OS and OS/390 Security Server Sup
- Page 111 and 112: Chapter2Controlling Access to theHi
- Page 113 and 114: Controlling HFS Using the Native UN
- Page 115 and 116: Controlling HFS Using CA SAF HFS Se
- Page 117 and 118: Securing HFS FunctionsKeywordALLCON
- Page 119 and 120: Securing HFS FunctionsFile Function
- Page 121 and 122: Implementing CA SAF HFS SecurityImp
- Page 123 and 124: HFSSEC Control Option+12—The addr
- Page 125 and 126: HFSSEC Control OptionDiagnosticsThe
- Page 127 and 128: HFSSEC Control OptionUNIX CMDCHMOD(
- Page 129 and 130: HFSSEC Control OptionTSSSUTIL EQUIV
- Page 131 and 132: HFSSEC Control OptionUNIX CMDS ACCE
- Page 133 and 134: HFSSEC Control OptionExample 1// JO
- Page 135 and 136: HFSSEC Control OptionExample 2// JO
- Page 137 and 138: MessagesMessagesCAS2301EEVENT PROCE
- Page 139 and 140: MessagesCAS2306Wxxxxxxxxxxxxxxx EVE
- Page 141: MessagesCAS2319ITRACEID=aaaaaaaa US
- Page 144 and 145: The SYSPLEX XES FunctionThere are t
- Page 146 and 147: eTrust CA-Top Secret and the SYSPLE
- Page 148 and 149: Defining the Sysplex to eTrust CA-T
- Page 150 and 151: Managing the Coupling FacilityWhen
- Page 152 and 153: Defining SYSTEM LOGGER to eTrust CA
- Page 154 and 155: IMVSECUR/*=========================
z/<strong>OS</strong> <strong>and</strong> <strong>OS</strong>/390 <strong>Security</strong> Server SupportThe following steps must be taken into consideration when protecting the DCEsecurity server under <strong>eTrust</strong> <strong>CA</strong>-<strong>Top</strong> <strong>Secret</strong>:1. A DCE segment, allowing specification of six DCE-related fields, can beadded to any <strong>eTrust</strong> <strong>CA</strong>-<strong>Top</strong> <strong>Secret</strong> defined user. An example of the use ofthese new fields follows:TSS ADD(acid) DCENAME(jordanm) DCEFLAGS(AUTOLOGIN)UUID(00000075-71db-21cf-b500-08005a470ba1)HOMEUUID(abbc323c-5ce2-11cf-a61e-08005a470ba1)HOMECELL(/.../cis_test1.cis.dog.com)2. <strong>eTrust</strong> <strong>CA</strong>-<strong>Top</strong> <strong>Secret</strong> further extends this support by installing anISPFEDIT-macro named TSSDCE which can be used to re<strong>for</strong>mat the outputof the IBM DCE export utility, MVSEXPT, to TSS <strong>for</strong>mat. To per<strong>for</strong>m thisre<strong>for</strong>mat, edit the MVSEXPT output data set using ISPF edit <strong>and</strong> enter theTSO comm<strong>and</strong> %TSSDCE. This will immediately re<strong>for</strong>mat the MVSEXPToutput data set being edited into TSS comm<strong>and</strong> <strong>for</strong>mat.3. Consult IBM DCE documentation <strong>for</strong> the <strong>OS</strong>390 OE/DCE security server <strong>for</strong>more in<strong>for</strong>mation about the use <strong>and</strong> settings of these fields.Firewall Technologiesz/<strong>OS</strong> <strong>and</strong> <strong>OS</strong>/390 provides the ability to run a firewall under UNIX SystemServices. Support is distributed in part with the Communication Server <strong>and</strong> inpart with the <strong>Security</strong> Server. The z/<strong>OS</strong> <strong>and</strong> <strong>OS</strong>/390 Firewall Technologies canonly reduce, but does not necessarily eliminate the need <strong>for</strong> a non-z/<strong>OS</strong> <strong>and</strong><strong>OS</strong>/390 plat<strong>for</strong>m firewall. The firewall itself is not configured using <strong>eTrust</strong><strong>CA</strong>-<strong>Top</strong> <strong>Secret</strong>. Administration is per<strong>for</strong>med through configuration files.Setting up the z/<strong>OS</strong> <strong>and</strong> <strong>OS</strong>/390 Firewall Technologies with <strong>eTrust</strong> <strong>CA</strong>-<strong>Top</strong><strong>Secret</strong> involves the following steps:1. Create a group definition <strong>for</strong> use with the firewall:TSS CREATE (FWGRP) TYPE(GROUP) NAME(‘Firewall Group’) DEPT(OMVSDEPT)TSS ADD(FWGRP) GID(nn)Any unused GID number is allowed.2. Define the Firewall startup address space ID:TSS CREATE(FWKERN) TYPE(USER) NAME(‘Firewall Startup ID’)DEPT(OMVSDEPT) FACILITY(STC,BATCH) PASS(password,0)TSS ADD(FWKERN) GROUP(FWGRP) DFLTGRP(FWGRP)HOME(/usr/lpp/fw/home/fwkern/) OMVSPGM(/bin/sh) UID(0)TSS ADD(STC) PROCNAME(FWKERN) ACID(FWKERN)TSS MODIFY(OMVSTABS)3. Allow FWKERN to issue start comm<strong>and</strong>s:TSS ADD(anydept) IBMFAC(FWKERN.)TSS PERMIT(FWKERN) IBMFAC(FWKERN.START.REQUEST) ACCESS(UPDATE)Implementing <strong>eTrust</strong> <strong>CA</strong>-<strong>Top</strong> <strong>Secret</strong> in a z/<strong>OS</strong> or <strong>OS</strong>/390 Environment 1–97