eTrust CA-Top Secret Security for z/OS and OS ... - SupportConnect
eTrust CA-Top Secret Security for z/OS and OS ... - SupportConnect eTrust CA-Top Secret Security for z/OS and OS ... - SupportConnect
NFS (Network File System)Define the string c1c2c3c4c5c6c7cc8 as the encryption key value for SMBpassword support:TSS ADD(SDT) KEYSMSTR(DCE.PASSWORD.KEY) DCENCRY(C1C2C3C4C5C6C7C8)To delete the KEYSMSTR record for the SDT:TSS DEL(SDT) KEYSMSTR(DCE.PASSWORD.KEY)To replace the encryption key and use the DES encryption to mask:TSS REP(SDT) KEYSMSTR(DCE.PASSWORD.KEY) DCENCRY(0123456701234567)To list the current encryption value:TSS LIST(SDT) KEYSMSTR(DCE.PASSWORD.KEY)Important: To use the DFS SMB support and the SMB Encrypted Password Supportyou must be running eTrust CA-Top Secret 5.1, genlevel SP04 or eTrust CA-Top Secret5.2, genlevel SP01 with maintenance as required.NFS (Network File System)z/OS and OS/390 NFS enables remote access to z/OS and OS/390 data sets andUNIX System Services HFS files and directories. NFS provides the ability toprotect file systems on MVS through four protection schemes. This setting isdefined within the NFS 'Site Attributes' attribute 'Security'.Four possible SECURITY settings include:NONE Do restrict access No MVS userID requiredEXPORTS Restrict access by client IP address No SAF checkSAFSAFEXPUse SAF to control access to datasetsUse SAF and EXPORTS to controlaccessSAF check executedSAF check (most secure)Both SAF and SAFEXP require the user to use the 'mvslogin' process to validateaccess through a SAF call. For this reason we recommend a minimum of security(SAF). Users who attempt to access HFS data must have a valid OMVS segmentassigned to their MVS acid. Access to HFS files will then be done by validatingthe client's UID and group against the file UNIX permission bits. Under normalcircumstances access to MVS data sets requires both the z/OS or OS/390 NFSserver and client user to pass a security check for the resource. The exception tothis is when 'DataCaching' is enabled. DataCaching causes data to be stored onthe z/OS or OS/390 NFS client system.1–92 Cookbook
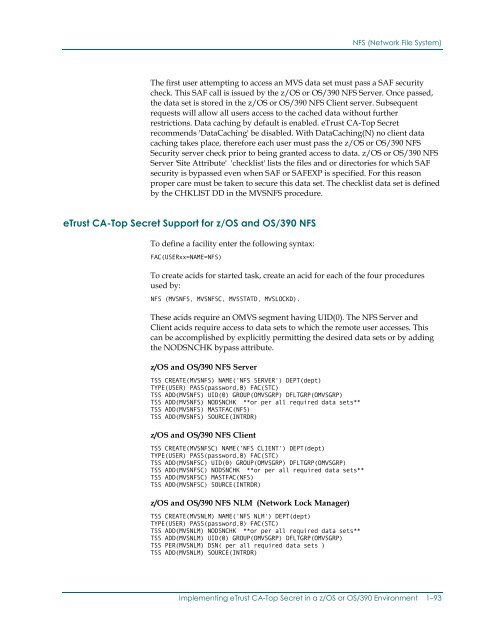
NFS (Network File System)The first user attempting to access an MVS data set must pass a SAF securitycheck. This SAF call is issued by the z/OS or OS/390 NFS Server. Once passed,the data set is stored in the z/OS or OS/390 NFS Client server. Subsequentrequests will allow all users access to the cached data without furtherrestrictions. Data caching by default is enabled. eTrust CA-Top Secretrecommends 'DataCaching' be disabled. With DataCaching(N) no client datacaching takes place, therefore each user must pass the z/OS or OS/390 NFSSecurity server check prior to being granted access to data. z/OS or OS/390 NFSServer 'Site Attribute' 'checklist' lists the files and or directories for which SAFsecurity is bypassed even when SAF or SAFEXP is specified. For this reasonproper care must be taken to secure this data set. The checklist data set is definedby the CHKLIST DD in the MVSNFS procedure.eTrust CA-Top Secret Support for z/OS and OS/390 NFSTo define a facility enter the following syntax:FAC(USERxx=NAME=NFS)To create acids for started task, create an acid for each of the four proceduresused by:NFS (MVSNFS, MVSNFSC, MVSSTATD, MVSLOCKD).These acids require an OMVS segment having UID(0). The NFS Server andClient acids require access to data sets to which the remote user accesses. Thiscan be accomplished by explicitly permitting the desired data sets or by addingthe NODSNCHK bypass attribute.z/OS and OS/390 NFS ServerTSS CREATE(MVSNFS) NAME('NFS SERVER') DEPT(dept)TYPE(USER) PASS(password,0) FAC(STC)TSS ADD(MVSNFS) UID(0) GROUP(OMVSGRP) DFLTGRP(OMVSGRP)TSS ADD(MVSNFS) NODSNCHK **or per all required data sets**TSS ADD(MVSNFS) MASTFAC(NFS)TSS ADD(MVSNFS) SOURCE(INTRDR)z/OS and OS/390 NFS ClientTSS CREATE(MVSNFSC) NAME('NFS CLIENT') DEPT(dept)TYPE(USER) PASS(password,0) FAC(STC)TSS ADD(MVSNFSC) UID(0) GROUP(OMVSGRP) DFLTGRP(OMVSGRP)TSS ADD(MVSNFSC) NODSNCHK **or per all required data sets**TSS ADD(MVSNFSC) MASTFAC(NFS)TSS ADD(MVSNFSC) SOURCE(INTRDR)z/OS and OS/390 NFS NLM (Network Lock Manager)TSS CREATE(MVSNLM) NAME('NFS NLM') DEPT(dept)TYPE(USER) PASS(password,0) FAC(STC)TSS ADD(MVSNLM) NODSNCHK **or per all required data sets**TSS ADD(MVSNLM) UID(0) GROUP(OMVSGRP) DFLTGRP(OMVSGRP)TSS PER(MVSNLM) DSN( per all required data sets )TSS ADD(MVSNLM) SOURCE(INTRDR)Implementing eTrust CA-Top Secret in a z/OS or OS/390 Environment 1–93
- Page 51 and 52: WebSphere Application Server for z/
- Page 53 and 54: WebSphere Application Server for z/
- Page 55 and 56: WebSphere Application Server for z/
- Page 57 and 58: Lotus Domino Go Webserver/* PERMITT
- Page 59 and 60: Lotus Domino Go WebserverTo disable
- Page 61 and 62: Lotus Notes and Novell Directory Se
- Page 63 and 64: Digital Certificate SupportGeneral
- Page 65 and 66: Digital Certificate SupportFOR|UNTI
- Page 67 and 68: Digital Certificate SupportDCDSN(re
- Page 69 and 70: Digital Certificate SupportNote: In
- Page 71 and 72: Digital Certificate SupportYou can
- Page 73 and 74: Digital Certificate SupportCase #2.
- Page 75 and 76: Digital Certificate SupportImportan
- Page 77 and 78: Digital Certificate SupportAdding a
- Page 79 and 80: Digital Certificate SupportReconnec
- Page 81 and 82: Digital Certificate SupportTSS LIST
- Page 83 and 84: Certificate Name Filtering SupportT
- Page 85 and 86: Certificate Name Filtering SupportI
- Page 87 and 88: Certificate Name Filtering SupportD
- Page 89 and 90: Certificate Name Filtering SupportL
- Page 91 and 92: KerberosKerberosetrust CA-Top Secre
- Page 93 and 94: KerberosThe command syntax for this
- Page 95 and 96: KerberosThe following command creat
- Page 97 and 98: Mapping of Foreign EnvironmentsMapp
- Page 99 and 100: Mapping of Foreign EnvironmentsMapp
- Page 101: Distributed File Server SMB SUPPORT
- Page 105 and 106: z/OS and OS/390 Security Server Sup
- Page 107 and 108: z/OS and OS/390 Security Server Sup
- Page 109 and 110: z/OS and OS/390 Security Server Sup
- Page 111 and 112: Chapter2Controlling Access to theHi
- Page 113 and 114: Controlling HFS Using the Native UN
- Page 115 and 116: Controlling HFS Using CA SAF HFS Se
- Page 117 and 118: Securing HFS FunctionsKeywordALLCON
- Page 119 and 120: Securing HFS FunctionsFile Function
- Page 121 and 122: Implementing CA SAF HFS SecurityImp
- Page 123 and 124: HFSSEC Control Option+12—The addr
- Page 125 and 126: HFSSEC Control OptionDiagnosticsThe
- Page 127 and 128: HFSSEC Control OptionUNIX CMDCHMOD(
- Page 129 and 130: HFSSEC Control OptionTSSSUTIL EQUIV
- Page 131 and 132: HFSSEC Control OptionUNIX CMDS ACCE
- Page 133 and 134: HFSSEC Control OptionExample 1// JO
- Page 135 and 136: HFSSEC Control OptionExample 2// JO
- Page 137 and 138: MessagesMessagesCAS2301EEVENT PROCE
- Page 139 and 140: MessagesCAS2306Wxxxxxxxxxxxxxxx EVE
- Page 141: MessagesCAS2319ITRACEID=aaaaaaaa US
- Page 144 and 145: The SYSPLEX XES FunctionThere are t
- Page 146 and 147: eTrust CA-Top Secret and the SYSPLE
- Page 148 and 149: Defining the Sysplex to eTrust CA-T
- Page 150 and 151: Managing the Coupling FacilityWhen
NFS (Network File System)The first user attempting to access an MVS data set must pass a SAF securitycheck. This SAF call is issued by the z/<strong>OS</strong> or <strong>OS</strong>/390 NFS Server. Once passed,the data set is stored in the z/<strong>OS</strong> or <strong>OS</strong>/390 NFS Client server. Subsequentrequests will allow all users access to the cached data without furtherrestrictions. Data caching by default is enabled. <strong>eTrust</strong> <strong>CA</strong>-<strong>Top</strong> <strong>Secret</strong>recommends 'DataCaching' be disabled. With DataCaching(N) no client datacaching takes place, there<strong>for</strong>e each user must pass the z/<strong>OS</strong> or <strong>OS</strong>/390 NFS<strong>Security</strong> server check prior to being granted access to data. z/<strong>OS</strong> or <strong>OS</strong>/390 NFSServer 'Site Attribute' 'checklist' lists the files <strong>and</strong> or directories <strong>for</strong> which SAFsecurity is bypassed even when SAF or SAFEXP is specified. For this reasonproper care must be taken to secure this data set. The checklist data set is definedby the CHKLIST DD in the MVSNFS procedure.<strong>eTrust</strong> <strong>CA</strong>-<strong>Top</strong> <strong>Secret</strong> Support <strong>for</strong> z/<strong>OS</strong> <strong>and</strong> <strong>OS</strong>/390 NFSTo define a facility enter the following syntax:FAC(USERxx=NAME=NFS)To create acids <strong>for</strong> started task, create an acid <strong>for</strong> each of the four proceduresused by:NFS (MVSNFS, MVSNFSC, MVSSTATD, MVSLOCKD).These acids require an OMVS segment having UID(0). The NFS Server <strong>and</strong>Client acids require access to data sets to which the remote user accesses. Thiscan be accomplished by explicitly permitting the desired data sets or by addingthe NODSNCHK bypass attribute.z/<strong>OS</strong> <strong>and</strong> <strong>OS</strong>/390 NFS ServerTSS CREATE(MVSNFS) NAME('NFS SERVER') DEPT(dept)TYPE(USER) PASS(password,0) FAC(STC)TSS ADD(MVSNFS) UID(0) GROUP(OMVSGRP) DFLTGRP(OMVSGRP)TSS ADD(MVSNFS) NODSNCHK **or per all required data sets**TSS ADD(MVSNFS) MASTFAC(NFS)TSS ADD(MVSNFS) SOURCE(INTRDR)z/<strong>OS</strong> <strong>and</strong> <strong>OS</strong>/390 NFS ClientTSS CREATE(MVSNFSC) NAME('NFS CLIENT') DEPT(dept)TYPE(USER) PASS(password,0) FAC(STC)TSS ADD(MVSNFSC) UID(0) GROUP(OMVSGRP) DFLTGRP(OMVSGRP)TSS ADD(MVSNFSC) NODSNCHK **or per all required data sets**TSS ADD(MVSNFSC) MASTFAC(NFS)TSS ADD(MVSNFSC) SOURCE(INTRDR)z/<strong>OS</strong> <strong>and</strong> <strong>OS</strong>/390 NFS NLM (Network Lock Manager)TSS CREATE(MVSNLM) NAME('NFS NLM') DEPT(dept)TYPE(USER) PASS(password,0) FAC(STC)TSS ADD(MVSNLM) NODSNCHK **or per all required data sets**TSS ADD(MVSNLM) UID(0) GROUP(OMVSGRP) DFLTGRP(OMVSGRP)TSS PER(MVSNLM) DSN( per all required data sets )TSS ADD(MVSNLM) SOURCE(INTRDR)Implementing <strong>eTrust</strong> <strong>CA</strong>-<strong>Top</strong> <strong>Secret</strong> in a z/<strong>OS</strong> or <strong>OS</strong>/390 Environment 1–93