On the Practicality of PIR - Radu Sion
On the Practicality of PIR - Radu Sion On the Practicality of PIR - Radu Sion
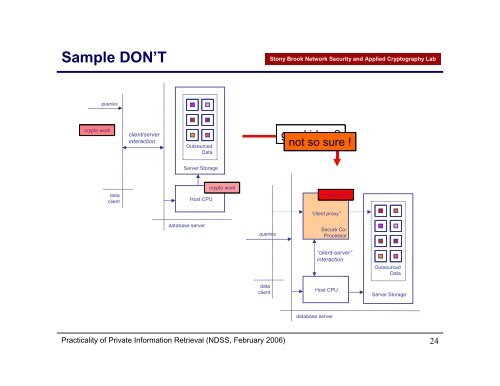
Sample DON’T Stony Brook Network Security and Applied Cryptography Lab queries crypto work client/server interaction Outsourced Data good idea ? not so sure ! Server Storage data client Host CPU crypto work crypto work “client proxy” database server queries Secure Co- Processor data client “client-server” interaction Host CPU Outsourced Data Server Storage database server Practicality of Private Information Retrieval (NDSS, February 2006) 24
in/yes > /dev/lunchtime Stony Brook Network Security and Applied Cryptography Lab wet !? Thank you ! Practicality of Private Information Retrieval (NDSS, February 2006) 25
- Page 1 and 2: Network Security and Applied Crypto
- Page 3 and 4: What is “practical” ? Stony Bro
- Page 5 and 6: Time to “illustrate” … Stony
- Page 7 and 8: Execution time analysis Stony Brook
- Page 9 and 10: Past: MIPS Schedule Stony Brook Net
- Page 11 and 12: Present: Hardware Stony Brook Netwo
- Page 13 and 14: Present: Low bandwidth conditions S
- Page 15 and 16: Future: CPU Speed follows Moore ! S
- Page 17 and 18: Future: 1 bit multiplication vs. tr
- Page 19 and 20: What do we do ? Stony Brook Network
- Page 21 and 22: IBM 4764 Stony Brook Network Securi
- Page 23: Comparison: Pentium 4 Stony Brook N
Sample DON’T<br />
Stony Brook Network Security and Applied Cryptography Lab<br />
queries<br />
crypto work<br />
client/server<br />
interaction<br />
Outsourced<br />
Data<br />
good idea ?<br />
not so sure !<br />
Server Storage<br />
data<br />
client<br />
Host CPU<br />
crypto work<br />
crypto work<br />
“client proxy”<br />
database server<br />
queries<br />
Secure Co-<br />
Processor<br />
data<br />
client<br />
“client-server”<br />
interaction<br />
Host CPU<br />
Outsourced<br />
Data<br />
Server Storage<br />
database server<br />
<strong>Practicality</strong> <strong>of</strong> Private Information Retrieval (NDSS, February 2006)<br />
24