2014 Digital Yearbook of Homeland Security Awards
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
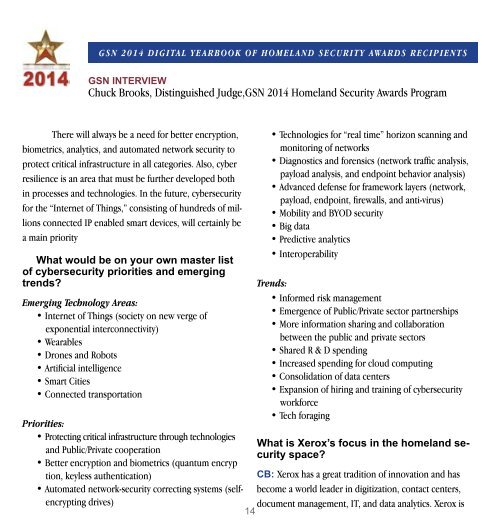
GSN <strong>2014</strong> <strong>Digital</strong> <strong>Yearbook</strong> <strong>of</strong> <strong>Homeland</strong> <strong>Security</strong> <strong>Awards</strong> Recipients<br />
GSN INTERVIEW<br />
Chuck Brooks, Distinguished Judge,GSN <strong>2014</strong> <strong>Homeland</strong> <strong>Security</strong> <strong>Awards</strong> Program<br />
There will always be a need for better encryption,<br />
biometrics, analytics, and automated network security to<br />
protect critical infrastructure in all categories. Also, cyber<br />
resilience is an area that must be further developed both<br />
in processes and technologies. In the future, cybersecurity<br />
for the “Internet <strong>of</strong> Things,” consisting <strong>of</strong> hundreds <strong>of</strong> millions<br />
connected IP enabled smart devices, will certainly be<br />
a main priority<br />
What would be on your own master list<br />
<strong>of</strong> cybersecurity priorities and emerging<br />
trends?<br />
Emerging Technology Areas:<br />
• Internet <strong>of</strong> Things (society on new verge <strong>of</strong><br />
exponential interconnectivity)<br />
• Wearables<br />
• Drones and Robots<br />
• Artificial intelligence<br />
• Smart Cities<br />
• Connected transportation<br />
Priorities:<br />
• Protecting critical infrastructure through technologies<br />
and Public/Private cooperation<br />
• Better encryption and biometrics (quantum encryp<br />
tion, keyless authentication)<br />
• Automated network-security correcting systems (selfencrypting<br />
drives)<br />
14<br />
• Technologies for “real time” horizon scanning and<br />
monitoring <strong>of</strong> networks<br />
• Diagnostics and forensics (network traffic analysis,<br />
payload analysis, and endpoint behavior analysis)<br />
• Advanced defense for framework layers (network,<br />
payload, endpoint, firewalls, and anti-virus)<br />
• Mobility and BYOD security<br />
• Big data<br />
• Predictive analytics<br />
• Interoperability<br />
Trends:<br />
• Informed risk management<br />
• Emergence <strong>of</strong> Public/Private sector partnerships<br />
• More information sharing and collaboration<br />
between the public and private sectors<br />
• Shared R & D spending<br />
• Increased spending for cloud computing<br />
• Consolidation <strong>of</strong> data centers<br />
• Expansion <strong>of</strong> hiring and training <strong>of</strong> cybersecurity<br />
workforce<br />
• Tech foraging<br />
What is Xerox’s focus in the homeland security<br />
space?<br />
CB: Xerox has a great tradition <strong>of</strong> innovation and has<br />
become a world leader in digitization, contact centers,<br />
document management, IT, and data analytics. Xerox is