magazine - Connect-World
magazine - Connect-World
magazine - Connect-World
- No tags were found...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
Mobile security<br />
Cutting mobile content risks<br />
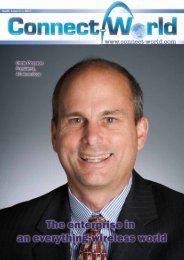
by Kees Van Veenendaal, VP and General Manager of EMEA, MobileIron<br />
The old model for content security - heavy containerization - protected data by separating it<br />
from other data and blocking unauthorized apps or users, but users did not like the experience.<br />
People that buy an iPhone or Android device do not want to flip between enterprise and<br />
personal screens and use third-party apps instead of the native experience they love. This<br />
compromises productivity and creates security risks as employees develop workarounds.<br />
Targeted containerization secures enterprise content within the native experience.<br />
Kees van Veenendaal is the VP and General Manager of EMEA at MobileIron; hebrings more than 25 years of experience throughout<br />
EMEA, the Americas and APAC to his role.<br />
Prior joining MobileIron, Mr van Veenendaal was Vice President <strong>World</strong>wide Sales for Trapeze Networks; Vice President of EMEA sales<br />
at Extreme Networks; and Managing Director of US Robotics Benelux. Mr van Veenendaal also held senior European management roles<br />
at Gandalf, Digital Communications Associates.<br />
Kees van Veenendaal has an MBA from Universiteit Nyenrode, the Netherlands.<br />
Mobile technology is driving a massive<br />
shift in the ability of IT departments to truly<br />
support the way people want to work. Across<br />
Europe, we see companies becoming Mobile<br />
First organizations, embracing mobility as<br />
a primary computing platform in order to<br />
transform their businesses and increase their<br />
competitiveness. A mobile deployment used<br />
to mean the company issued 200 BlackBerrys<br />
to executives. Now, it means that every<br />
employee in an organization is using mobile<br />
apps and accessing corporate content via a<br />
mobile device that may or may not be owned<br />
by the company.<br />
The result is that people expect to be able<br />
to access the corporate content they need on<br />
any device at any time. However, as soon as<br />
you put email on a mobile device you risk<br />
losing enterprise content. Email attachments<br />
can be forwarded or uploaded to a consumer<br />
cloud storage service. Content can be cut and<br />
pasted from one email account to another.<br />
Apps introduce additional security risks. Data<br />
moving between an app and the corporate<br />
network is vulnerable to man-in-the-middle<br />
attacks via rogue Wi-Fi hotspots. App data<br />
stored on the mobile device could be accessed<br />
by a malicious app a user inadvertently<br />
installed. Securing mobile content presents<br />
several distinct challenges.<br />
Mobile Content Security Challenges<br />
Mobile devices are consumer devices not<br />
corporate devices<br />
In the days of old mobile, everyone<br />
was issued BlackBerrys because the IT<br />
department could lock them down. That’s<br />
not possible with the new mobile operating<br />
systems. Now, mobile devices are no longer<br />
issued by IT. People who love using their<br />
smartphones and tablets in their personal<br />
lives bring them to work. Then the Mobile<br />
IT team needs to figure out how to secure<br />
corporate content without compromising the<br />
employee’s privacy in terms of their personal<br />
content. Regardless of whether the mobile<br />
device is owned by the employee or the<br />
company, most devices will be used for both<br />
personal and professional use.<br />
Mobile devices store large amounts of data in<br />
small, easy to lose packages<br />
Storage capacity is growing, and, in addition,<br />
most Android devices have removable SD<br />
cards. Content is stored in email attachments<br />
and in mobile apps. And all of it is in a small<br />
device that is easily lost or stolen. Enterprises<br />
need to be able to ensure the security of dataat-rest<br />
on the device.<br />
Mobile devices are hyper-connected<br />
Apple devices have iCloud and any device<br />
can connect to file-sharing services, such<br />
as Dropbox. This makes it very easy for an<br />
40 • EMEA 2013