IRIS Authentication Accuracy – PoC Report - uidai
IRIS Authentication Accuracy – PoC Report - uidai
IRIS Authentication Accuracy – PoC Report - uidai
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
UIDAI<br />
h<br />
Unique Identification Authority of India<br />
Planning Commission, Govt. of India (GoI),<br />
3rd Floor, Tower II,<br />
Jeevan Bharati Building,<br />
Connaught Circus,<br />
New Delhi 110001<br />
Role of Biometric<br />
Technology in Aadhaar<br />
<strong>Authentication</strong><br />
<strong>IRIS</strong> <strong>Authentication</strong> <strong>Accuracy</strong> – <strong>PoC</strong> <strong>Report</strong><br />
Date: 14 September 2012
Executive Summary<br />
UIDAI has collected iris images of residents during enrollment, and<br />
successfully leveraged iris modality for de-duplication. A Proof of<br />
Concept (<strong>PoC</strong>) study was carried out to assess the feasibility of using<br />
iris for on-line biometric authentication in the Indian context. The<br />
findings of this study are presented in this report.<br />
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
This report covers the design framework, field implementation, data<br />
collection and analysis. It interprets empirical results to assess Figure 1 Young resident at POC<br />
effectiveness of iris technology, authentication processes and devices. It concludes with a set of<br />
observations and findings for iris authentication process and device ecosystem.<br />
Assessment of iris feasibility can be further divided into<br />
1. Coverage: Can residents use iris efficiently and conveniently for Aadhaar authentication?<br />
2. <strong>Accuracy</strong>: How accurately can iris authenticate a resident?<br />
3. Device readiness: Are there commercially available devices capable of performing<br />
authentication?<br />
4. System readiness: Is the entire authentication system ready for performing iris<br />
authentication?<br />
Study Process: <strong>PoC</strong> was conducted in a manner similar to the previous study [UIDAI, FP, 2012].<br />
Residents with Aadhaar number were asked to participate in the test. In the first part, scenario test,<br />
each resident was authenticated on-line on one of the eight cameras. In the second part, technology<br />
test, the resident’s iris images were captured on all eight cameras. In both parts, extensive logs<br />
were generated for off-line analysis. During the analysis, the data was first reviewed and cleansed of<br />
Feasibility of Iris based on-line <strong>Authentication</strong><br />
The empirical results clearly demonstrate iris authentication to be viable in<br />
Indian context.<br />
Findings<br />
% of Residents<br />
Single-eye cameras Dual-eye cameras<br />
Authenticated in first try 95.89 99.29<br />
Authenticated in multiple tries 99.21 99.40<br />
Failed authentication<br />
(FRR+FTC)<br />
0.79 0.60<br />
Device Readiness: Six different devices with a variety of form and function are<br />
available to form competitive vendor eco-system.<br />
System Readiness: Median time for end-to-end authentication was less than one<br />
minute over GPRS mobile network in semi-rural setting.<br />
© UIDAI, 2009-2012 Page 2 of 36
exceptions and anomalies.<br />
Set-up: The <strong>PoC</strong> was conducted in semi urban setting at<br />
centers in Nanjagud taluk in Mysore district of Karnataka<br />
between May 27 th and July 30 th 2012. The <strong>PoC</strong> centers<br />
were designed to resemble expected ground reality. No<br />
attempt was made to create an ideal situation. In online<br />
(scenario) testing, 17,990 online authentication<br />
transactions were performed by 5,747 residents. The<br />
online authentications were performed on a GPRS based<br />
mobile network. In the off-line (technology) study,<br />
5,833 residents went through 40,148 capture sessions<br />
on 8 authentication cameras. All the cameras used in<br />
the POC studies were obtained through an Expression of<br />
Interest (EOI). In all, 215,342 iris images were captured<br />
during this process.<br />
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
Iris <strong>PoC</strong> was carried out using the Aadhaar authentication system described in an earlier report<br />
[UIDAI, FP, 2012].<br />
Results:<br />
The <strong>PoC</strong> was conducted to obtain sample that demographically represents Indian population. At the<br />
end, the sample used has a slight over representation of women and seniors (over 65 years) and<br />
under-representation of children (below 15 years) as compared to Aadhaar enrollment data.<br />
Coverage: The coverage achieved by iris authentication was high, demonstrating the potential of iris<br />
to be an inclusive modality. Out of 5,833 residents, only one resident was not able to use any of<br />
the eight cameras, and 18 additional residents (0.31%) could not use four or more cameras.<br />
Thus, there is no inherent technical or physiological limitation to using iris for authentication. It<br />
should be possible for 99.67% of population to conveniently attempt iris authentication. In<br />
other words, failure to capture (FTC) rate is in the range of 0.33% with current capture software.<br />
The study has identified the root cause and suggested methods to improve vendor’s capture<br />
algorithm to achieve even higher coverage through this report.<br />
<strong>Accuracy</strong>: Table 1 shows the True Accept Rate (TAR) for different authentication modes with two<br />
attempts averaged over six “good” cameras. The data shows that high accuracy can be obtained<br />
using both single and dual eye cameras. In summary, False Reject Rate (FRR) of less than 0.5% is<br />
achievable whenever two irises are matched on single or dual eye cameras.<br />
<strong>Authentication</strong> Mode Single eye camera Dual eye camera<br />
One iris authentication 96.21% Not Applicable<br />
Two irises authentication 99.54% 99.73%<br />
Table 1: True Accept Rate at FAR = 1e -6<br />
<strong>Accuracy</strong> insight and conclusions:<br />
a) Manual inspection of iris images provided insight into the root cause of failure to capture<br />
and false rejects cases. Over two-third residents in question had eye deformity arising from<br />
certain types of surgeries or eye conditions and hence some cameras were unable to<br />
capture the image which resulted in FTC. Others cameras were more lenient in capturing<br />
© UIDAI, 2009-2012 Page 3 of 36
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
the image but authentication failed. These residents with special eye condition will not be<br />
able to authenticate using irises because either the cameras will be unable to capture or<br />
even when captured, they may fail to authenticate successfully as the current capture and<br />
matcher software are unable to process them. With this situation clearly identified and<br />
communication with vendors in progress, future devices and matching algorithms could be<br />
enhanced to accommodate some of these condition further increasing iris accuracy.<br />
Additional study may be also needed to more accurately estimate and analyse eye surgery<br />
cases (particularly, cataract surgeries) across India.<br />
b) Fingerprints of these individuals with special eye conditions were reviewed. For most of the<br />
residents, it was estimated that their fingerprints are of sufficient quality to enable<br />
fingerprint based biometric authentication.<br />
c) It was observed that DET curve for iris is flat implying little deterioration in FRR rate with<br />
stringent FAR. This binary behaviour – either a good match or not a match – could be<br />
uniquely useful in situations requiring high level of assurance such as money transfer or<br />
secure access control. Conversely, running iris authentication at less stringent FAR (such as 1<br />
in 10,000) will not improve the FRR.<br />
d) Two iris authentication shows material improvement over one iris authentication. It is<br />
estimated that additional 3% residents could be reliably authenticated by expanding<br />
authentication to include two irises. For all age categories, accuracy continues to be higher<br />
than 98.94%. Among those children have performed best, followed by adults. Some of the<br />
seniors could not be authenticated due to special eye conditions. This indicates the need to<br />
tune the capture and matcher algorithms specifically for seniors to accommodate for special<br />
eye conditions.<br />
Device readiness: Six of the iris cameras participating in this study performed at required accuracy<br />
level. This will assure competitive vendor eco-system to the service providers willing to use iris<br />
authentication. Key variables determining effectiveness of a camera are<br />
a. Single eye and dual eye capture: Four cameras each of single eye and dual eye were tested.<br />
Both single eye and dual eye devices were found suitable for iris authentication.<br />
b. Capture aid: Various physical and optical aids were utilized by different cameras. Cameras<br />
with visual indications on the camera for capture process, eye alignment, actionable<br />
feedback and capture completion were materially easier to use.<br />
c. High Capture quality – In addition to quality algorithms being in the device to capture high<br />
quality images, vendors could incorporate specific suggestions made in this document to<br />
further enhance image quality.<br />
All participating camera vendors were asked to supply <strong>IRIS</strong> segmentation SDK which produces<br />
image in formats KIND 1, 2, 3 and 7 (also known as Uncropped, VGA, Cropped and Cropped &<br />
Masked respectively) compliant to ISO 19794-6 standard [ISO 19794-6, 2011]. The camera<br />
vendors provided predominantly only two formats, KIND 1 and KIND 2. The image size is a<br />
dominant factor in network latency for mobile networks. While this <strong>PoC</strong> used KIND 2<br />
compressed image of size 15 KB, use of KIND 7 would have reduced it to 2 KB resulting in<br />
speedier authentication.<br />
As a result of factors mentioned above, there was a difference in performance of different<br />
cameras. In each category of single and dual eye cameras, one camera was an outlier compared<br />
to median performance of the group. For example, one camera demonstrated a failure to<br />
© UIDAI, 2009-2012 Page 4 of 36
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
capture (FTC) rate of about 10% when the median of peer cameras was below 0.5%. Some of<br />
the outliers were also judged to be more difficult to use in the field and were not considered in<br />
accuracy analysis. Suggestions made in this report would improve performance of cameras,<br />
especially these outlier cameras.<br />
System readiness: The overall system behaved reliably and conveniently for both resident and<br />
operators. A few cases of system failure were observed. Two important metrics measure user<br />
friendliness of the iris based authentication.<br />
a. <strong>Authentication</strong> time. Using a GPRS based semi-rural network, median time across all devices<br />
was less than one minute. <strong>Authentication</strong> time is defined as time taken to complete full<br />
transaction including capture of two irises, local image quality check, operator review,<br />
transmission, backend processing and authentication response.<br />
b. Round trip time. Less than a quarter of the authentication cycle was transmission and<br />
backend matching time. Median round trip was less than 10 seconds, while only 7.8% of<br />
transactions took more than 15 seconds.<br />
Previous <strong>PoC</strong> demonstrated that the current setup is capable of supporting sustained fingerprint<br />
authentication speeds of one million per hour. It has been demonstrated repeatedly in the<br />
literature that iris matcher is more efficient than fingerprint matcher. Therefore no independent<br />
tests were performed using iris matcher. Based on published data, it is safe to state that Aadhaar is<br />
capable of sustaining iris authentication rate of over one million per hour. However UIDAI will do<br />
benchmarking of t its backend system to validate the peak load scenarios for iris authentication also.<br />
Findings and Next Steps<br />
The empirical results clearly demonstrate iris authentication to be viable in Indian context. With<br />
current level of device readiness for iris capture, it is capable of providing coverage for 99.67% of<br />
population with authentication accuracy of above 99.5% using two irises and up to two attempts.<br />
Suggestions made in this document for the vendors, once implemented, will improve the rates<br />
further. The overall systems – network and software - have shown to meet desired requirements in<br />
real life condition. Finally, six different devices with variety of form and function are available to<br />
provide competitive vendor eco-system.<br />
The <strong>PoC</strong> also provided a number of insights that could further improve performance of device and<br />
system. Three key improvements are<br />
a. Improvement in matcher algorithm and device capture software to handle residents with<br />
special eye conditions.<br />
b. Support for KIND 7 image format by device vendor to help reduce image size during<br />
transmission to about 2 KB from the current 15KB.<br />
Several ergonomic improvements in device design to aid in easier and more accurate<br />
capture. These cover visual aids for proper placement of camera and appropriate visible<br />
light source inside certain types of camera.<br />
UIDAI would be working with the biometric ecosystem to implement the findings mentioned in this<br />
document and take up further field studies to fine-tune iris authentication technology. These studies<br />
would also lead to formulation of iris device specifications which will be used for certification by<br />
STQC.<br />
© UIDAI, 2009-2012 Page 5 of 36
Abbreviations<br />
API Application Programming Interface<br />
ASA <strong>Authentication</strong> Service Agency<br />
AUA <strong>Authentication</strong> User Agency<br />
EOI Expression of Interest<br />
CIDR Central Identity Data Repository<br />
DET Detection Error Tradeoff<br />
NIST National Institute of Standards and Technologies<br />
IREX Iris Exchange<br />
FAR False Accept Rate<br />
FRR False Reject Rate<br />
FTC Failure To Capture<br />
IEC Information, Education and Communication<br />
KYC Know Your Customer<br />
PDS Public Distribution System<br />
<strong>PoC</strong> Proof of Concept<br />
SDK Software Development Kit<br />
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
STQC Standardisation Testing and Quality Certification Directorate<br />
TAR True Accept Rate (1 – FAR)<br />
UIDAI Unique Identification Authority of India<br />
© UIDAI, 2009-2012 Page 6 of 36
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
Contents<br />
Executive Summary ................................................................................................................................. 2<br />
Abbreviations .......................................................................................................................................... 6<br />
1 Aadhaar <strong>Authentication</strong> ................................................................................................................ 10<br />
2 Objective ....................................................................................................................................... 11<br />
3 Design and Field Implementation ................................................................................................. 12<br />
3.1 Introduction to <strong>PoC</strong> studies .................................................................................................. 12<br />
3.2 Iris <strong>Authentication</strong> Concepts ................................................................................................. 12<br />
3.3 Test Methodology ................................................................................................................. 13<br />
3.4 Resident and operator communication and training............................................................ 17<br />
3.5 Data Quality & Data Analysis ................................................................................................ 18<br />
4 Feasibility of using iris for authentication ..................................................................................... 19<br />
4.1 Demographic Profile ............................................................................................................. 19<br />
4.2 Coverage ............................................................................................................................... 20<br />
4.3 <strong>Accuracy</strong> results from technology test ................................................................................. 21<br />
4.4 System findings ..................................................................................................................... 24<br />
4.5 Devices Findings .................................................................................................................... 25<br />
4.6 Other findings ....................................................................................................................... 27<br />
5 Observations & Findings ............................................................................................................... 28<br />
5.1 Coverage ............................................................................................................................... 28<br />
5.2 <strong>Accuracy</strong> ................................................................................................................................ 28<br />
5.3 Device Readiness .................................................................................................................. 28<br />
5.4 System Readiness .................................................................................................................. 29<br />
5.5 Findings ................................................................................................................................. 29<br />
5.6 Way Forward ......................................................................................................................... 30<br />
6 References .................................................................................................................................... 31<br />
7 Appendix – Camera related findings ............................................................................................. 32<br />
7.1 Capture distance and Capture Volumes ............................................................................... 32<br />
7.2 Image Capture and Output ................................................................................................... 32<br />
7.3 Capture aids .......................................................................................................................... 33<br />
7.4 Detection and Capture of iris ................................................................................................ 34<br />
7.5 Dual eye vs. single eye cameras ............................................................................................ 35<br />
7.6 Capture Distance ................................................................................................................... 36<br />
© UIDAI, 2009-2012 Page 7 of 36
Figures<br />
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
Figure 1 Young resident at POC .............................................................................................................. 2<br />
Figure 2 POC Center at Nanjangud ....................................................................................................... 12<br />
Figure 3 Residents waiting for their turn .............................................................................................. 12<br />
Figure 4 Resident at POC site ................................................................................................................ 15<br />
Figure 5 Screen shot of Client UI ........................................................................................................... 16<br />
Figure 7: IEC material used during POC ................................................................................................ 17<br />
Figure 6: Announcer .............................................................................................................................. 17<br />
Figure 8: Age distribution of participants in study compared to Aadhaar enrolment ......................... 19<br />
Figure 9: Gender distribution of participants in study compared to Aadhaar enrolment ................... 20<br />
Figure 10: ICCE Cataract surgery ........................................................................................................... 20<br />
Figure 11: Occlusion .............................................................................................................................. 21<br />
Figure 13 DET Curve - Single and Dual Iris <strong>Authentication</strong> ................................................................... 23<br />
Figure 12 FRR by matchers.................................................................................................................... 23<br />
Figure 14: Resident authentication time .............................................................................................. 24<br />
Figure 15: Network Latency histogram ................................................................................................. 24<br />
Figure 16: Image Formats ..................................................................................................................... 25<br />
Figure 17: Sample images of residents providing samples during POC ................................................ 26<br />
Figure 18: Age wise DET chart .............................................................................................................. 27<br />
Figure 19 Resident with special condition Eyes .................................................................................... 35<br />
© UIDAI, 2009-2012 Page 8 of 36
List of Tables<br />
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
Table 1: True Accept Rate at FAR = 1e -6 .................................................................................................. 3<br />
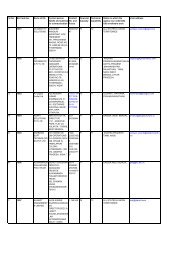
Table 2: Vendor Participation ............................................................................................................... 16<br />
Table 3: Failure to Capture ................................................................................................................... 20<br />
Table 4: Camera-wise FTC ..................................................................................................................... 21<br />
Table 5: Resident wise <strong>Accuracy</strong> ........................................................................................................... 22<br />
Table 6: Camera wise Reject Rates (2 irises with 2 attempts) .............................................................. 22<br />
Table 7: Single Eye Camera - Good and all single eye camera TAR ...................................................... 22<br />
Table 8: Dual eye camera - Good and all Dual eye camera TAR ........................................................... 23<br />
Table 9: True Accept Rate at FAR = 1e-6. ............................................................................................. 28<br />
Table 10 Camera Capture distance and capture volume information ................................................. 32<br />
© UIDAI, 2009-2012 Page 9 of 36
1 Aadhaar <strong>Authentication</strong><br />
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
The Unique Identification Authority of India (UIDAI) has been created with the mandate of providing<br />
a Unique Identity (Aadhaar) to all residents of India. The CIDR processes these enrolments by deduplicating<br />
them to ensure uniqueness and then issues Aadhaar numbers. As of August 2012, nearly<br />
200 million residents have been enrolled in Aadhaar and over 195 million of them have been issued<br />
with Aadhaar numbers<br />
One of the mandates given to UIDAI is to define usages and applicability of Aadhaar for delivery of<br />
benefit services. The Aadhaar number, which uniquely identifies a resident, will give individuals<br />
means to clearly establish their identity to public and private agencies across the country for service<br />
delivery. UIDAI provides online authentication using the resident’s demographic and biometric<br />
information to support Aadhaar-enabled delivery of services.<br />
Aadhaar <strong>Authentication</strong> is the process wherein, Aadhaar number along with the Aadhaar holder’s<br />
personal identity data is securely submitted to the CIDR for matching, following which the CIDR<br />
verifies the correctness thereof on the basis of the match with the Aadhaar holder’s identity<br />
information available with it. To protect resident’s privacy, Aadhaar <strong>Authentication</strong> service responds<br />
only with a “Yes/No” and no Personal Identity Information (PII) is returned as part of the response.<br />
Aadhaar <strong>Authentication</strong> supports several different types of authentication through a combination of<br />
demographic fields, biometric fields as well as other methods such as one-time-password (OTP). In<br />
case of iris, the CIDR server supports authentication of iris images compliant with ISO standard that<br />
ensures vendor neutral, open format.<br />
For further information on Aadhaar authentication system, please refer to www.<strong>uidai</strong>.gov.in.<br />
This study analyzes the feasibility of using iris as a modality for authentication.<br />
© UIDAI, 2009-2012 Page 10 of 36
2 Objective<br />
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
The objective of the <strong>PoC</strong> was to determine the feasibility of using iris modality for on-line<br />
authentication.<br />
UIDAI has successfully leveraged iris modality in enrollment and has collected iris images of the<br />
resident during enrollment. Iris is used for biometric de-duplication. This study was aimed at<br />
assessing its use for biometric authentication in the Indian context.<br />
Iris as a biometric modality promises certain unique characteristics in Indian environment. Iris<br />
technology literature lists several benefits.<br />
1. The iris does not get worn out with age, or with use. In addition, iris authentication is not<br />
impacted by changes in the weather.<br />
2. Iris image capture does not require physical contact. Capturing iris image is physically similar to<br />
familiar practice of taking photographs.<br />
3. Iris capture requires simple instructions such as ‘look at the camera, keep your eyes wide open’.<br />
4. Fake iris is difficult to synthesize making it harder to impersonate.<br />
5. Iris image cannot be captured without resident cooperation.<br />
6. Cost and manufacturing of iris cameras have been positively affected by the spread of low cost<br />
consumer cameras.<br />
Few global initiatives have empirically published results on iris based online authentication in a<br />
context similar to Aadhaar. Therefore the goal for the study was also to<br />
Characterize & propose optimal authentication setups (server & device level) for online<br />
biometric authentication of residents using iris authentication device.<br />
To achieve the goal, it is necessary to conduct rigorous field tests on sample population and to<br />
measure feasibility in four areas:<br />
A. Coverage indicates the percentage of the population that is able to conveniently and efficiently<br />
utilize iris authentication. For any system to be utilized for large scale benefit delivery, ease of<br />
use and speed of verification are also key measure of the overall coverage.<br />
B. <strong>Accuracy</strong> measure percentage of time system is able to authenticate genuine resident while<br />
rejecting attempt by imposter.<br />
C. System readiness covers overall response time with particular emphasis on network latency,<br />
reliability, stability and ease of deployment<br />
D. Device readiness measures individual device’s ability to perform above three factors reliably.<br />
Particular attention was given to understand different device characteristics and develop<br />
recommendation for enhancing device performance.<br />
© UIDAI, 2009-2012 Page 11 of 36
3 Design and Field Implementation<br />
3.1 Introduction to <strong>PoC</strong> studies<br />
There have been few studies regarding biometric<br />
authentication in the Indian field context and it was<br />
important to conduct rigorous <strong>PoC</strong> studies in order to<br />
design and configure the UIDAI authentication system. A<br />
number of such <strong>PoC</strong> studies have been carried out, each<br />
building on the learning from the previous ones. This<br />
chapter describes the design and setup for this study.<br />
Continuing the methodology used in the previous study<br />
[UIDAI, FP, 2012], the iris <strong>PoC</strong> tests various parameters<br />
using [ISO 19795-2, 2007], which provides the following definitions:<br />
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
Figure 2 POC Center at Nanjangud<br />
Scenario evaluation is an online evaluation of end-to-end system performance in a prototype or<br />
simulated application. The utility of scenario testing stems from the inclusion of human-sensor<br />
acquisition interaction in conjunction with the enrolment and recognition processes, whose<br />
benefits include the following:<br />
� Ability to gauge impact of additional attempts and transactions.<br />
� Ability to collect throughput results for resident authentication.<br />
and<br />
Technology evaluation is the offline evaluation of one or more devices and algorithms for the<br />
same biometric modality using a corpus of samples. The utility of technology testing stems from<br />
its separation of the human-sensor acquisition interaction and the recognition process. It allows<br />
for varying different parameters to re-run the same sample image [ISO 19795-2, 2007].<br />
The tests in the iris <strong>PoC</strong> have been instrumented to collect sufficient data to conduct both a specific<br />
scenario evaluation and follow on technology evaluation.<br />
3.2 Iris <strong>Authentication</strong> Concepts<br />
Prior to presenting the authentication accuracy results, terms used in this document are defined<br />
below.<br />
1. Session: Visit. This <strong>PoC</strong> uses only one session.<br />
2. Sample: User’s biometric measures as output by the data capture subsystem. For e.g., face<br />
image, fingerprint image and iris image are samples.<br />
3. Presentation: Submission of a single biometric sample on the part of a user. It may also be<br />
referred to as impression. On single eye camera, each presentation may generate one image.<br />
One presentation of two eye iris camera generates two images.<br />
4. Attempt: Submission of one (or a sequence of) biometric<br />
samples to the system after it has passed quality check.<br />
NOTE: An attempt results in a template and can be used<br />
to generate a matching score. There is a difference<br />
between the definition of attempt by ISO and this <strong>PoC</strong><br />
attempt. This <strong>PoC</strong> attempt is after quality check. A<br />
failure to acquire due to missing fingers/iris or inability to<br />
© UIDAI, 2009-2012 Page 12 of 36<br />
Figure 3 Residents waiting for their turn
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
even register image on scanner does not result in an attempt.<br />
5. False reject rate (FRR): Proportion of verification transactions with truthful claims of identity that<br />
are incorrectly denied. All data collected from the field included an operator-set flag for the<br />
expected response (the Ground Truth). Based on this, all ‘true’ authentication transactions were<br />
rerun in the lab and the matching scores recorded. This allowed capture of the false reject rate<br />
for a particular threshold.<br />
6. False accept rate (FAR): Proportion of verification transactions with wrongful claims of identity<br />
that are incorrectly confirmed. Expected false requests were created by pairing biometric data<br />
collected from the field with an Aadhaar number other than the original Aadhaar holder<br />
(imposter requests). A large number of these requests were rerun and matching scores<br />
recorded. This allowed capture of the false accept rate for several thresholds. As many false<br />
requests as necessary were created to provide statistically significant results.<br />
7. Failure-to-capture (FTC) includes:<br />
� Attempts where the biometric characteristic cannot be captured;<br />
� Attempts in which the extracted features do not meet the quality control thresholds;<br />
� Attempts for which the segmentation or feature extraction fail; and<br />
� Attempts where the raw sample was not acquired or did not meet quality thresholds are<br />
not processed by the matching algorithm, and do not generate matching scores.<br />
8. Transaction: Entire on-line process of capturing biometric sample, packaging it for on-line<br />
submission, communicating to the backend server (CIDR), backend server matching and<br />
receiving of the response. It began when the resident provided his/her Aadhaar number and<br />
ended when the response was received.<br />
9. True Accept Rate (TAR): TAR = 1 – FRR.<br />
3.3 Test Methodology<br />
Since collection of biometric data from the residents is an expensive process, the multi-modal<br />
authentication <strong>PoC</strong> covered both scenario and technology testing in one session. The complete<br />
process that included several more steps took about 15 minutes per resident and consisted of<br />
1. One Best Finger Detection procedure (UIDAI, 2011) (UIDAI, 2012)<br />
2. Two online fingerprint authentications (scenario test)<br />
3. One face picture<br />
4. One online iris authentication on one of the iris authentication cameras (scenario test)<br />
5. 2 “best” images on each of 8 iris authentication cameras (technology test)<br />
6. 2 “best” images on each of 6 iris enrolment camera (technology test)<br />
This report covers results of iris authentication only (steps 4 and 5).<br />
The session setup consisted of two parts. The resident went through both two parts. Part 1 covered<br />
scenario testing and part 2 covered technology testing.<br />
Part 1: Scenario Testing. The scenario testing utilized Aadhaar’s<br />
production environment. It was performed on-line and in real<br />
time. The authentication frontend was connected with the CIDR<br />
through mobile network. The resident was authenticated in real<br />
time against the enrolment data.<br />
Figure 4 Resident at POC site<br />
© UIDAI, 2009-2012 Page 13 of 36
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
Part 2: Technology Testing. The test collected a number of presentations (images) of iris for use in<br />
off-line analysis.<br />
Iris authentication devices come in a variety of forms and designs. Available models were tested to<br />
determine readiness of iris authentication including suitability, usability, interoperability and<br />
performance of the camera.<br />
In scenario testing, it is important to measure process parameters such as end to end transaction<br />
time and number of attempts. <strong>Accuracy</strong> results were obtained from technology test. Technology<br />
test also provided device level performance. Technology tests were done using offline data<br />
collection. Raw uncompressed images were captured. Images were compressed using JPEG 2000<br />
lossy compression during off line analysis.<br />
3.3.1 Iris Capture attempts under scenario testing<br />
Iris images were captured using maximum of 3 attempts of up to 3 presentations. All images were<br />
captured automatically by the device, without operator forcing the capture.<br />
1. Each successful presentation resulted in image capture. Unsuccessful presentation, where<br />
the camera was unable to capture image was still counted as presentation.<br />
2. Each captured presentation was checked for quality using SDK’s quality algorithm. If the<br />
quality was below acceptable threshold, the image was captured again (i.e., second<br />
presentation). The final image was either the first image meeting quality threshold or best<br />
image among the three presentations, whichever comes first. Final image was sent to the<br />
back end for authentication using the chosen mode of communication.<br />
3. If the authentication failed, the resident was asked to undergo step 1 & 2 again up to two<br />
additional attempts.<br />
4. FTC condition would occur if no image was captured after three attempts as mentioned in<br />
step 1.<br />
Single eye camera: Each presentation was defined as image of one eye. Second attempt used<br />
different eye from the first. In other words, the recommended multiple attempt sequence was right<br />
eye, left eye, right eye. The switching of eyes effectively provides “best finger” strategy for two<br />
eyes.<br />
Dual eye camera: Each presentation was defined as one image of each eye (two iris images). While<br />
other aspect of process was same (3 attempts of 3 presentations each), the maximum number of<br />
images captured would be twice that of single eye camera. Dual eye camera is effectively equivalent<br />
to using two fingers for authentication in previous studies.<br />
3.3.2 Iris Capture attempts under technology testing<br />
Maximum of two images of each eye were captured using up to 5 attempts. All images were<br />
captured automatically by the device, without operator forcing the capture.<br />
� Each successful presentation would result in image capture. Unsuccessful presentation,<br />
where the camera was unable to capture image, was skipped.<br />
© UIDAI, 2009-2012 Page 14 of 36
� Each captured presentation was checked for quality using SDK’s<br />
quality algorithm. If the quality is below acceptable threshold,<br />
the image was captured again. The process continued until two<br />
quality images are captured or maximum of five attempts,<br />
whichever comes first. If the process did not generate two<br />
quality images, two best quality images of each eye were<br />
selected from available images.<br />
� In case of single eye camera, above steps were repeated for<br />
each eye. In case of dual eye camera, even when two eyes are<br />
captured, the above process was repeated until two images of<br />
each eye is collected. In other words, regardless of camera<br />
type, two “best” quality images of each eye are collected.<br />
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
� FTC condition was recorded if no image could be captured in five attempts.<br />
Figure 4 Resident at POC site<br />
3.3.3 Iris Stations for scenario testing<br />
The resident was authenticated at only one of the iris stations. In other words, with eight iris<br />
camera stations, each station received approximately 1/8 th of the residents. The distribution of<br />
residents to the iris station was not controlled.<br />
1. Iris authentication during scenario testing.<br />
a. All the cameras were handled by the operator during the test.<br />
b. Attempts: Section 3.3.1 details process to be used for multiple attempts.<br />
c. Quality check: UIDAI’s quality check SDK was used whenever the device vendor did not<br />
supply it.<br />
d. Image format: Vendor supplied software to generate ISO image (VGA) was used. Images<br />
were compressed using JPEG 2000 lossy compression.<br />
e. Image selection: In case of one eye camera, best image was the first image that passed<br />
quality check or the best image of the attempt. In case of two eye camera the images<br />
within an attempt would be buffered and best image of each eye was sent.<br />
2. The operator recorded eye position (left or right) using provided UI.<br />
3. Matching: The resident is authenticated when match occurs in any attempt. No further<br />
biometric capture is done at the station for the resident.<br />
4. If a resident is unable to authenticate at the station, the resident is not excluded from going to<br />
technology testing section.<br />
3.3.4 Iris Stations for technology testing<br />
1. The resident authenticated using iris through the following steps.<br />
a. All cameras were handled by the operator.<br />
b. Auto capture function captured iris image(s). If one-eye camera was used, one image<br />
was captured. If two-eye camera was used, two images were captured.<br />
c. Eye: The default first attempt was right eye unless operator determined that the<br />
resident’s right eye was not ideal. This was not relevant for two eye cameras.<br />
d. The operator was required to note the eye position in the software for single eye<br />
camera using the interface provided.<br />
e. Attempts: See Section 3.3.2.<br />
f. Quality check- SDK quality check used in enrolment was used.<br />
© UIDAI, 2009-2012 Page 15 of 36
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
g. On-line authentication. It was not necessary to perform on-line authentication. All iris<br />
stations were off-line.<br />
h. Raw images were stored.<br />
Figure 5 Screen shot of Client UI<br />
2. If a resident was unable to provide iris image at one station, the resident was not excluded from<br />
going to subsequent stations. For such residents, FTC (Failure to capture) event is recorded.<br />
3.3.5 <strong>PoC</strong> Client Application and Data Collection<br />
As part of the <strong>PoC</strong> client application, to measure different variables and compare/fine-tune<br />
performance of various SDKs, detailed logs were captured for further analysis. At the UIDAI<br />
Technology Centre, all logs were analyzed and authentication requests were replayed on multiple<br />
SDKs to understand the impact of various biometric matching algorithmic changes and other<br />
backend interventions that could be used to improve the authentication accuracy. POC application<br />
prominently displayed quality parameters along with captured iris.<br />
3.3.6 Vendor Participation<br />
In this study, Iris camera vendors were invited to participate based on an EOI (EOI No. K-<br />
1102/16/2012-UIDAI dated 7 th March, 2012). Following an initial evaluation, vendors selected for<br />
the study, as summarized below:<br />
Measure Number<br />
EOI responses received 11<br />
Number of models ready with H/W and S/W by due date 8<br />
Number of models participated in <strong>PoC</strong> 8<br />
Number of OEM participated 6<br />
Number of devices which were made ready post POC and<br />
hence could not participate in <strong>PoC</strong><br />
1<br />
Table 2: Vendor Participation<br />
© UIDAI, 2009-2012 Page 16 of 36
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
3.3.7 Field Setup<br />
<strong>Authentication</strong> <strong>PoC</strong> centers were designed to resemble expected ground reality. No attempt was<br />
made to create an ideal situation. Some key considerations for setting up and managing the<br />
authentication stations were as follows:<br />
� UIDAI procured all the components and standardized them across all authentication <strong>PoC</strong><br />
stations – such as laptops, network connectivity, power backup, etc. EOI participants<br />
provided cameras and capture software. UIDAI performed final software integration with<br />
<strong>PoC</strong> UI.<br />
� Commercially available telecom data card (GPRS) used for network connection in order to<br />
send authentication requests to CIDR.<br />
� Regular electrical supply available at the <strong>PoC</strong> location, backed up with UPS/ generators was<br />
used for the <strong>PoC</strong> exercise. Disruptions in the main power supply were noticed during the<br />
course of the <strong>PoC</strong>.<br />
� Sensors were deployed across various stations to provide equal opportunity to all<br />
participating device technologies / OEMs, constrained by USB port availability.<br />
� The key consideration was to get each resident to authenticate using all the authentication<br />
devices.<br />
� For resident mobilization, residents were requested to participate in<br />
the Proof of Concept studies through announcements by local<br />
administration. Announcer was made to move into surrounding<br />
villages and to draw the resident population for the studies.<br />
During the field operation, some of the deployed devices intermittently<br />
failed causing system hang-ups or freeze. Considering the larger <strong>PoC</strong><br />
objectives & crowd management issues, the devices had to be disconnected<br />
temporarily. As a result not every resident went through every device.<br />
3.4 Resident and operator communication and training<br />
Detailed communication material was developed to educate the operators<br />
Figure 6: Announcer<br />
and residents to conduct the process as well do’s and don’ts. Banners and<br />
Standees were placed in and around the <strong>PoC</strong> site. Laminated sheets containing these instructions<br />
were handed over to residents as they entered the <strong>PoC</strong> site in order for them to acquaint<br />
themselves with the process to follow during the capture. Operators were also trained using the<br />
same instructions.<br />
Figure 7: IEC material used during POC<br />
© UIDAI, 2009-2012 Page 17 of 36
3.5 Data Quality & Data Analysis<br />
Data analysis consisted of the following steps:<br />
� Analyzing the logs from field<br />
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
� Replaying the images captured from the field against the authentication server<br />
� Visually reviewing images to eliminate errors. Several types of errors were identified and<br />
rectified<br />
o Labeling errors. Wrong demographical information, wrong label of right or left eye<br />
o Enrollment errors. Residents whose authentication images could not be matched<br />
because the corresponding enrolment data consisted of extremely low quality<br />
images, etc. These residents (8 residents) were identified and not considered in the<br />
accuracy analysis.<br />
© UIDAI, 2009-2012 Page 18 of 36
4 Feasibility of using iris for authentication<br />
This section summarizes the following areas from the iris study:<br />
� Demographics of the study participants (scenario test)<br />
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
� Coverage - Resident population who were able to have their iris captured for authentication<br />
(technology test)<br />
� <strong>Accuracy</strong> - Matching accuracy using various matchers (technology test)<br />
� System readiness - Capture time, Network time related characteristics (scenario test)<br />
� Devices readiness and related findings (technology test)<br />
In scenario testing, 17,990 online authentication transactions were performed by 5,747 residents on<br />
available GPRS mobile network. The 5,833 residents participated in the iris technology test resulting<br />
in 40,148 capture sessions on 8 authentication cameras. In all, 215,342 iris images were capture<br />
during this process.<br />
4.1 Demographic Profile<br />
The demographic profile of participants in the iris study was compared with the profile of residents<br />
enrolled in Aadhaar – both nationally as well as within Mysore district. The comparison was done on<br />
the basis of participant age bands, as well as gender.<br />
It was found that children in 5-15 years range were under represented in the sample compared to<br />
overall Aadhaar enrolment statistics, while senior residents (66+ years) were over represented.<br />
Similarly, females were over represented in the study.<br />
The following charts show the age and gender distribution of all Aadhaar holders nationwide, in<br />
Mysore district and participants in the iris <strong>PoC</strong>.<br />
Poc<br />
Mysore<br />
India<br />
9<br />
18<br />
18<br />
83<br />
0% 20% 40% 60% 80% 100%<br />
77<br />
78<br />
Figure 8: Age distribution of participants in study compared to Aadhaar enrolment<br />
© UIDAI, 2009-2012 Page 19 of 36<br />
8<br />
5<br />
4<br />
6-15 years<br />
16-65 years<br />
66 and above
Poc<br />
Mysore<br />
India<br />
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
Figure 9: Gender distribution of participants in study compared to Aadhaar enrolment<br />
4.2 Coverage<br />
Coverage is primarily measured by failure to capture (FTC) rate. Since devices with different<br />
characteristics and quality were utilized, FTC rate over all devices does not accurately measure<br />
maturity of iris technology. A new metric that measures inherent technology limitation in capturing<br />
iris images in Indian context was also introduced. This measured the number of residents who could<br />
not use any device and could not use several devices.<br />
4.2.1 Resident coverage across multiple devices<br />
Two conclusions can be drawn from the statistics:<br />
45<br />
50<br />
52<br />
0% 20% 40% 60% 80% 100%<br />
Table 3: Failure to Capture<br />
� The coverage achieved by iris authentication was high, demonstrating the potential of iris to be<br />
an inclusive modality. There is no inherent technical or physiological limitation to using iris for<br />
authentication.<br />
� The observed FTC rate of 0.33% (based on failure across 4 or more cameras) indicates that it<br />
should be possible for most of the residents to conveniently authenticate using iris.<br />
Since the resident’s iris image capture was attempted on different cameras in one session, it was<br />
possible to manually review cases where image capture failed on one camera but succeeded on<br />
another. While the FTC rate was very small, the most frequent cause for those failed was due to eye<br />
conditions such as deformed pupil/iris (mostly result of surgeries), antiquated cataract surgery or<br />
other types of eye abnormalities. Majority of the cases were from non-circular pupil shape caused<br />
due to cataract operations using Intra Capsular Cataract Extraction (ICCE) cryo-surgery technique<br />
used prior to 1990.<br />
© UIDAI, 2009-2012 Page 20 of 36<br />
55<br />
50<br />
48<br />
Male<br />
Female<br />
Resident coverage across 8 cameras Number of residents % failure<br />
Total no. of Residents who participated 5833<br />
Neither eye could be captured in all cameras 1 0.017%<br />
Only left eye was captured (right eye not captured) 3 0.051%<br />
Only right eye was captured (left eye not captured) 9 0.154%<br />
Failed iris capture (either eye) on 4 or more cameras 18 0.308%<br />
Figure 10: ICCE Cataract surgery
Other causes observed were from:<br />
Figure 11: Occlusion<br />
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
� Residents with squint eyes often suffered from FTC especially on dual eye camera. Single eye<br />
cameras are able to capture one eye with less difficulty.<br />
� Some residents could not open their eyes sufficiently leading to FTC or false rejects (Figure 11).<br />
� Some residents suffered from involuntary movement of the eye-ball (Nystagmus) and hence had<br />
an unstable iris resulting in FTC.<br />
In the analysis, failure due to segmentation, if any, was included in FTC. Failure in template<br />
generation, if any, was included in false reject statistics.<br />
4.2.2 Failure to Capture (FTC) by Camera<br />
FTC rates are computed by device and can provide another perspective on the capture failure.<br />
Single Eye Camera FTC Dual Eye Camera FTC<br />
A 0.12% E 0.61%<br />
B 2.01% F 2.13%<br />
C 0.30% G 9.84%<br />
D 0.10% H 0.31%<br />
Table 4: Camera-wise FTC<br />
The failure to capture (FTC) of individual iris cameras varies widely by camera as shown in Table 4.<br />
When compared to median performance of peer devices, camera “G” performed poorly and was<br />
judged to be an outlier.<br />
Improvements in capture software and ergonomics can enhance camera performance. These issues<br />
are discussed in detailed as part of device recommendations under Section 4.5 and in Annexure<br />
4.3 <strong>Accuracy</strong> results from technology test<br />
The most common measure of accuracy is True Accept Rate (TAR) and False Accept Rate (FAR). Just<br />
like coverage it is instructive to use additional measure, called resident accuracy, to understand<br />
behavior of iris technology across cameras.<br />
All biometric matchers require FAR threshold as input to calculate matching score which is used to<br />
determine FRR. <strong>Accuracy</strong> calculations shown below are done at FAR of 1e -6 or 1 in 1,000,000.<br />
4.3.1 Resident <strong>Accuracy</strong><br />
Of the 5833 residents who participated, 5793 residents were able to successfully authenticate using<br />
at least one authentication camera using either their left or right eye. Of remaining residents, 8<br />
could not be authenticated due to incorrect enrolments (i.e. issues with enrollment gallery), while 13<br />
residents (0.22%) could not be successfully authenticated using either the left or right iris on all<br />
© UIDAI, 2009-2012 Page 21 of 36
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
cameras. It is indicative of issues inherent to the image and not capture or matching algorithm. 19<br />
residents were FTC in at least four cameras.<br />
<strong>Accuracy</strong> centric statistics<br />
Table 5: Resident wise <strong>Accuracy</strong><br />
4.3.2 Device <strong>Accuracy</strong><br />
The accuracy of individual iris cameras varied widely. The FRR achieved using up to 2 attempts of<br />
both left and right iris (FAR of 1e-6) is shown in Table 6 for single eye and dual eye camera.<br />
Compared to median performance of peer groups, two cameras – C and G – were considered to be<br />
outlier. Others are referred to as “good” cameras. Further analysis on the cameras can be found in<br />
the Annexure. Remaining six cameras are used for all further analysis unless noted otherwise.<br />
Single Eye Camera FRR Dual Eye Camera FRR<br />
A 0.52% E 0.21%<br />
B 0.43% F 0.31%<br />
C 0.91% G 0.85%<br />
D 0.41% H 0.28%<br />
Table 6: Camera wise Reject Rates (2 irises with 2 attempts)<br />
4.3.3 Impact of using two irises and multiple attempts<br />
Single eye camera captures one iris at time. The 3 “good” single eye cameras achieved a true accept<br />
rate (TAR) 96.21% in one attempt. This means that 96.21% residents can be authenticated using a<br />
single (left) iris capture. When the other (right) iris is added in matching the percentage of resident<br />
successfully authenticating improves to 99.23%, again in single attempt. Capturing both the left and<br />
right iris a second time (second attempt) improves the TAR to 99.54%.<br />
There is a significant improvement in the TAR rate, between a single (left) iris capture and both iris<br />
capture.<br />
Single Eye Camera Single Iris TAR<br />
Number of<br />
residents<br />
Both Iris<br />
1st Attempt TAR<br />
Both Iris<br />
2 Attempts TAR<br />
All Cameras (4) 93.77% 98.99% 99.43%<br />
Good Cameras (3) 96.21% 99.23% 99.54%<br />
Table 7: Single Eye Camera - Good and all single eye camera TAR<br />
% of residents<br />
Resident successfully with either their left or right eye (on<br />
at least one camera)<br />
5793 99.45%<br />
Resident did NOT authenticate successfully on any eye(right<br />
or left)<br />
13 0.22%<br />
Resident did NOT authenticate due to enrolment issues 8 0.14%<br />
FTC (image capture failed on four or more cameras) 19 0.33%<br />
Dual eye camera captures both irises at the same time. The “3” good dual iris cameras achieved a<br />
TAR of 99.62% in the first attempt. A second attempt of the dual iris capture improved the TAR to<br />
99.73%.<br />
© UIDAI, 2009-2012 Page 22 of 36
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
Dual Eye Camera Both Iris 1st Attempt TAR Both Iris 2 Attempts TAR<br />
All Cameras (4) 99.46% 99.62%<br />
Good Cameras (3) 99.62% 99.73%<br />
Table 8: Dual eye camera - Good and all Dual eye camera TAR<br />
The data shows that high accuracy can be obtained using both single eye and dual eye cameras.<br />
Performing a second attempt of capturing the iris slightly improves the TAR for both single and dual<br />
iris camera. It is estimated that third attempt may not further improve accuracy. Hence it is safe to<br />
specify maximum attempts at two in standard operating procedure.<br />
4.3.4 Matcher Performance<br />
The images captured were compared using two different backend<br />
matchers (SDK). The graph below illustrates the session wise (up to 2<br />
attempts of both irises) FRR achieved using the two SDK. Matcher 2<br />
had an FRR of 0.43% while matcher 1 had an FRR of 1.11%. Matcher 2<br />
has been used for all other comparisons in this report.<br />
When falsely rejected images were manually reviewed, it was noticed<br />
that Matcher 2 was able to match off axis (gaze), dilated, out of focus<br />
and motion blur images better than Matcher 1. This was a significant<br />
contributing factor in superior performance of Matcher 2.<br />
4.3.5 Iris DET Curve<br />
Figure 12 FRR by matchers<br />
Iris authentication has a flat DET curve, i.e., there is only a slight<br />
degradation in FRR for significant reduction in FAR. As shown in the DET curve in Figure 13, the<br />
single eye camera FRR (2 iris, 2 attempts) increases from 0.31% for an FAR of 1e-3 to an FRR of<br />
0.46% for an FAR of 1e-6.<br />
FRR<br />
1.00%<br />
0.80%<br />
0.60%<br />
0.40%<br />
0.20%<br />
0.00%<br />
0.46%<br />
Iris DET (2 Iris, 2 Attempts)<br />
Single <strong>IRIS</strong> Camera Dual <strong>IRIS</strong> Camera<br />
0.34% 0.33% 0.31%<br />
0.27% 0.23% 0.22% 0.21%<br />
1.00E-06 1.00E-05 1.00E-04 1.00E-03<br />
FAR<br />
Figure 13 DET Curve - Single and Dual Iris <strong>Authentication</strong><br />
As shown in the DET curve in Figure 13 the dual iris camera FRR (2 iris, 2 attempts) increases from<br />
0.21% for an FAR of 1e-3 to an FRR of 0.27% for an FAR of 1e-6.<br />
Hence, iris can be a particularly attractive option for high security applications such as financial<br />
transactions or secures access control. Iris authentication can operate at TAR > 99% with FAR = 1e-6.<br />
© UIDAI, 2009-2012 Page 23 of 36
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
4.4 System findings<br />
Besides accuracy and coverage, the third most important factor for feasibility of iris based<br />
authentication is system level factors. These factors consist of<br />
� Response time<br />
� Image size used in transmission.<br />
� Matcher speed<br />
The response is measured with two metrics: Resident authentication time and round trip time.<br />
Resident authentication time includes time to select the device, enter the Aadhaar number, guiding<br />
the resident for correct capture procedure, completing the capture of both eyes, submitting the<br />
transaction and receiving response. Round trip time measures the last two parameters of the<br />
authentication time during which the resident is waiting for system to respond.<br />
4.4.1 Resident <strong>Authentication</strong> Time<br />
Figure 14 is a histogram of authentication time<br />
separated by single and dual eye cameras.<br />
Median time in both cases is below one minute.<br />
In case of single eye devices, one iris is captured<br />
at a time whereas in case of dual eye device, both<br />
irises are captured at a time. Therefore, median<br />
time of dual eye camera is lower than that of<br />
single eye.<br />
This time distribution also includes the time<br />
taken for repeated impressions due to failed<br />
quality or failure to capture during the first<br />
attempt.<br />
4.4.2 Round trip time<br />
The histogram of round trip time under these<br />
conditions is shown in Figure 15. Median is below<br />
ten seconds. Over 62% of transactions returned in<br />
less than 10 seconds, while only 7.8% of<br />
transactions took more than 15 seconds.<br />
The network performance can be further improved<br />
by smaller image sizes as discussed in the next<br />
section.<br />
© UIDAI, 2009-2012 Page 24 of 36<br />
70%<br />
60%<br />
50%<br />
40%<br />
30%<br />
20%<br />
10%<br />
0%<br />
0.4%<br />
24.0%<br />
65.4%<br />
60.4%<br />
31.0%<br />
Single Eye device<br />
Dual Eye Device<br />
13.6%<br />
3.3%<br />
2.0%<br />
< 30 sec
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
The diagram below shows compression used in this <strong>PoC</strong> and the roadmap to get the device vendors<br />
to support kind 7 images which will reduce the iris image to 2KB. Refer [ISO 19794-6-2011] for<br />
further definitions of image types cited above.<br />
Figure 16: Image Formats<br />
4.4.4 Matcher Speed<br />
Previous <strong>PoC</strong> demonstrated that current setup is capable of supporting sustained fingerprint<br />
authentication speed of one million per hour. It has been demonstrated repeatedly in the literature<br />
that iris matcher is more efficient than fingerprint matcher. Therefore no independent tests were<br />
performed using iris matcher. Based on published data, it is safe to state that Aadhaar is capable of<br />
sustaining iris authentication rate of over one million per hour. Further tests could verify this<br />
assertion.<br />
4.5 Devices Findings<br />
During the <strong>PoC</strong>, four cameras were single eye cameras and four cameras were dual eye cameras.<br />
The cameras varied in form and function. Satisfactory performance of six cameras supplied by<br />
different OEMs indicates that cameras will be competitively available in different form and in desired<br />
quantities.<br />
All devices provided documentation on mode of capture and were easy to learn and operate from<br />
operator and resident point of view. Similarly 8 of 11 device vendors provided software in<br />
compliance to API specifications published for the purpose of POC. One vendor achieved<br />
compliance after POC process was completed and could not therefore be tested.<br />
All the devices used during the test, were supplied with rugged casing. No breakages and<br />
malfunctioning due to packaging were reported during the POC.<br />
© UIDAI, 2009-2012 Page 25 of 36
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
Devices supported auto capture feature. This enabled devices to automatically capture good quality<br />
iris pictures when operator held the device at the specified capture distance from the resident iris.<br />
Single eye devices captured single iris at a time. Dual eye devices captured both irises at the same<br />
time. There was one device which was capable of dual iris capture, but was configured to capture<br />
both irises, in a sequence, one iris at a time. When presented with residents who had one eye in<br />
good condition, single eye devices fared better than dual eye camera which looked for two good<br />
irises. Dual iris cameras could improve the capture algorithms in order to overcome this issue.<br />
Figure 17: Sample images of residents providing samples during POC<br />
From usage model point of view, capture distance and capture volume of iris devices used varied<br />
widely. Capture distance (distance between edge of device and eye) of less than10 mm to over<br />
300mm were tested during the POC. All but one device were expected to be handled by the<br />
operator and last device was mounted using tripod. As the capture volume supported by the device<br />
plays important role in ease of capture, devices with larger capture distance and small capture<br />
volume required additional training for both operators and residents.<br />
Similarly, actionable feedback and capture aids supported by the devices played key role in ensuring<br />
high quality and easier iris captures. Most devices were providing actionable feedback to the<br />
operator and capture was supported through various aids. Devices that provided no feedback and<br />
capture aids took more number of presentations to achieve high quality of iris capture.<br />
VGA images provided by devices were compressed and analyzed during the analysis. Iris images<br />
were compressed to 15KB for the analysis. However, devices supporting cropped/masked (Kind 7)<br />
images would help reduce the size of the iris further to order of 2KB. This reduction will help during<br />
iris online transactions. It has been shown by NIST report [Grother, P, 2009] that such reduction<br />
does not have accuracy related implications.<br />
© UIDAI, 2009-2012 Page 26 of 36
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
The annexure provides further information related to device readiness and areas of further<br />
improvements.<br />
4.6 Other findings<br />
4.6.1 Impact of Resident Age<br />
The impact of age on authentication accuracy was studied. The computed DET curves compare the<br />
accuracy of matching for people in the age group 5-15, 15-60 and 60+ years.<br />
FRR<br />
1.20%<br />
1.00%<br />
0.80%<br />
0.60%<br />
0.40%<br />
0.20%<br />
0.00%<br />
Age wise DET Curves (2 Iris, 2 Attempts)<br />
1.06%<br />
0.29%<br />
0.19%<br />
0.87%<br />
0.84%<br />
0.22% 0.21% 0.20%<br />
0.14% 0.14% 0.14%<br />
Figure 18: Age wise DET chart<br />
0.81%<br />
1.00E-06 1.00E-05 1.00E-04 1.00E-03<br />
FAR<br />
For all age categories, overall accuracy continues to be higher than 98.94% at FAR of 1e-6. Among,<br />
those children have performed best (0.19% reject rate, statistically not significant), followed by<br />
adults (0.29%) and seniors (1.06%). Some of the seniors could not be authenticated due to special<br />
eye conditions.<br />
© UIDAI, 2009-2012 Page 27 of 36<br />
< 15<br />
15-60<br />
>60
5 Observations & Findings<br />
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
In conclusion, a set of observations and findings derived from the analysis of the <strong>PoC</strong> data is<br />
presented below.<br />
5.1 Coverage<br />
It is possible to achieve over 99.5% population coverage for on-line iris authentication. Most of<br />
those whose iris images could not be captured on four or more cameras suffered from special eye<br />
condition, mostly due to older generation of cataract or eye surgery that resulted in highly irregular<br />
shaped pupil or iris. With current devices and matcher algorithm, they cannot avail themselves to<br />
iris authentication. Alternate method such as fingerprint or OTP will be required. They could be<br />
easily identified using enrollment data or during first attempt to authenticate.<br />
Fingerprints of these individuals with special eye conditions were reviewed. It was found through<br />
best finger detection (BFD) and authentication that their fingerprints were of sufficient quality to<br />
enable fingerprint based biometric authentication.<br />
5.2 <strong>Accuracy</strong><br />
It is possible to attain true accept rate of over 99% on both single and dual eye cameras with<br />
stringent FAR of 1e-6.<br />
<strong>Authentication</strong> Mode Single eye camera Dual eye camera<br />
One eye authentication 96.21% Not Applicable<br />
Two eye authentication 99.54% 99.73%<br />
Table 9: True Accept Rate at FAR = 1e-6.<br />
Operating at false accept rate of one in million, Iris technology also lends itself for highly secure<br />
authentication against imposter attacks. Table 9 shows how high accuracy authentication may be<br />
achieved using various strategies.<br />
Use of second iris for authentication improves accuracy by 3% over single iris. However, second<br />
attempt of the same iris only marginally improves accuracy. Due to diminishing return, it is unlikely<br />
that third attempt would increase accuracy any further.<br />
For all age categories, overall accuracy continues to be higher than 98.94%. Among those children<br />
have performed best, followed by adults. Some of the seniors could not be authenticated due to<br />
special eye conditions. This indicates the need to tune the capture and matcher algorithms<br />
specifically for seniors to accommodate for special eye conditions.<br />
A smaller percentage of people (0.14%, not statistically valid) could not be authenticated because of<br />
enrollment data quality issues. They would be able to use iris authentication once their biometric<br />
data is updated.<br />
Anecdotally, blindness by itself was not perceived to be an issue and blind people without special<br />
eye conditions authenticated successfully.<br />
5.3 Device Readiness<br />
There is a variation in authentication accuracy cameras based on capture algorithms, ergonomics<br />
and related factors. In the study, it was observed that while most cameras performed well, there<br />
© UIDAI, 2009-2012 Page 28 of 36
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
were outliers with high FTC and FRR rates. Operator’s difficulty in using them correlated with their<br />
poor FTC and FRR rates. For example, one camera had FTC rate of about 10% while most others<br />
were operating below 1%. It is critical that only good cameras are selected for deployment in the<br />
field through a rigorous testing and certification process.<br />
Single eye camera was judged better with people with squint eye. Residents found dual eye camera<br />
easier to use resulting in slightly faster capture time. Dual eye camera that captures one eye at a<br />
time seems to offer best of both the worlds.<br />
Devices providing capture aids and actionable feedback help operator with faster and better quality<br />
capture. The devices which provided effective capture aids and feedback to operator regarding<br />
capture process and image quality was seen to achieve very high degree of accuracy.<br />
It is important to emphasize that the quality of image plays an important role in ensuring<br />
authentication accuracy. Devices have incorporated quality measurements within their capture<br />
algorithms to enable auto capture. In addition to the existing parameters, to further improve the<br />
quality of capture and minimize number of attempts, algorithms could check for gaze correctness,<br />
rotated device, upside down eyes, occlusion, focus, motion blur and special eye conditions.<br />
Vendor supplied software provided iris image in KIND 1 and KIND 2 formats. Resulting compressed<br />
image was 15 KB in size. KIND 3 and KIND 7 could bring this size down to 2 KB which would be<br />
beneficial in reducing network latency and improving network reliability.<br />
5.4 System Readiness<br />
The median time to perform end-to-end online authentication is less than one minute out of which<br />
about a quarter is for round trip transmission (& back end processing which is sub second). From<br />
resident’s view, the wait time after capture has occurred is less than 15 seconds which was judged<br />
acceptable.<br />
Faster network or smaller image size will reduce resident wait time. Device improvement<br />
recommendation mentioned in this report will also improve transaction time.<br />
5.5 Findings<br />
1. One eye vs. two eyes: Two irises authentication provides significant improvement in accuracy<br />
and coverage over one iris. In case of single eye camera, it is recommended to authenticate first<br />
with one eye, and only in case of failure, the second eye be used for authentication.<br />
2. Attempts: Two attempts are recommended. While the second attempt only marginally<br />
improved accuracy, it compensates for other forms of human error should they occur.<br />
3. Device Certification: Stringent authentication device testing and certification is recommended to<br />
ensure high quality authentication devices are deployed for Aadhaar authentication.<br />
4. Capture aids: Device vendors should provide better capture aid for operator and residents. The<br />
study categories three types of aid: actionable feedback, visual aid and “appropriate light source<br />
to improve quality of image and finally measures to block ambient light reflections. These<br />
improvements detailed in Annexure will reduce capture time, improve accuracy and offer better<br />
user experience.<br />
© UIDAI, 2009-2012 Page 29 of 36
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
5. Capture quality: It is important to emphasize that quality of image plays important role to ensure<br />
authentication accuracy. Devices should make attempt to incorporate specific areas of quality<br />
explained in the document along with what is being already being done within the devices to<br />
ensure quality.<br />
6. KIND 7 image formats: Device vendors need to implement KIND 7 format which is more efficient<br />
than the current standard used.<br />
7. Device Enhancement: The study has clearly identified a small number of residents (< 0.3%) with<br />
special eye conditions. Vendors would be provided with the images (suitably anonymized) and<br />
UIDAI would work with them to improve device capture and iris matching algorithms to handle<br />
such cases.<br />
8. Matcher SDKs: Since there was a variance in the performance of two matcher SDKs tested, the<br />
matcher SDK vendors need to enhance their algorithms to provide higher tolerance to problems<br />
arising out of incorrect gaze, dilation, focus, motion blur etc.<br />
9. Matcher Setting: Since FRR does not materially change when FAR is changed from 1e-4 to 1e-6,<br />
iris lends itself well to be operated at much lower FAR thus providing robust security against<br />
imposter attacks.<br />
5.6 Way Forward<br />
UIDAI would be working with the biometric ecosystem to implement the findings mentioned in this<br />
document and take up further field studies to fine-tune iris authentication technology. These studies<br />
would also lead to formulation of iris device specifications which will be used for certification by<br />
STQC.<br />
© UIDAI, 2009-2012 Page 30 of 36
6 References<br />
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
[Grother, P, 2009]: IREX Summary. By P. Grother, E. Tabassi, G. W. Quinn, W. Salamon: NIST.<br />
[ISO 19795-2, 2007]: Biometric performance testing and reporting—Testing methodologies for technology and<br />
scenario evaluation. By International Standards Organization.<br />
[ISO 19794-6, 2011]: Information technology -- Biometric data interchange formats -- Part 6: Iris image data.<br />
By International Standards Organization.<br />
[UIDAI, FP, 2012]: Role of Biometric Technology in Aadhaar Authentiation - Detailed <strong>Report</strong><br />
http://<strong>uidai</strong>.gov.in/images/role_of_biometric_technology_in_aadhaar_authentication_0<br />
20412.pdf<br />
© UIDAI, 2009-2012 Page 31 of 36
7 Appendix – Camera related findings<br />
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
This section is concerned with devices used in the field exercise. The section goes into detailed<br />
findings and observations including future areas of improvements to improve capture efficiency and<br />
ergonomic improvements.<br />
7.1 Capture distance and Capture Volumes<br />
During the proof of concept, four cameras were single eye cameras and four cameras were dual eye<br />
cameras. Most of the single cameras had capture distance of less than 3cm. One dual iris camera<br />
had a capture distance of about 33 centimeters. Camera distance and volume of cameras used in<br />
the POC is listed below.<br />
Camera Single or Dual Iris Capture Distance Capture Volume ( WxHxD)<br />
Camera 1 Dual 22.5 cm to 25.0 cm 15 cm x 11 cm x 4 cm depth.<br />
Camera 2 Dual 0 to 10 mm from forehead 42 x 24 x 30 mm for each eye<br />
Camera 3 Single 120mm 39x25x20mm<br />
Camera 4 Dual 315 to 345 mm 60 x 45 x 30 mm for each eye<br />
Camera 5 Single<br />
50mm(from sensor)- 0-10mm<br />
from the eye guard<br />
33x24.5x8mm(D)<br />
Camera 6 Dual >58mm 20x15x12mm<br />
Camera 7 Single >58mm 20X15X12mm<br />
Camera 8 Single<br />
0 to 10 mm from the eye<br />
guard<br />
32 x 24 x 10 mm<br />
Table 10 Camera Capture distance and capture volume information<br />
Note: Cameras have been listed above in alphabetical order and are not to be correlated with other<br />
camera listing tables.<br />
7.2 Image Capture and Output<br />
All participating camera vendors were requested <strong>IRIS</strong> segmentation SDK which produces image in<br />
format Type 1, 2, 3 and 7 (also known as Uncropped, VGA, Cropped and Cropped & Masked<br />
respectively) compliant to ISO 19794-6 standard. It was observed the camera vendors support for<br />
Uncropped and VGA formats (Kind1 and 2 respectively as per ISO 19794-6 standard) (ISO, 2011) was<br />
complete and support for Kind3 (cropped) and kind7 (masked) was not complete.<br />
Support for Kind7 (Cropped & Masked) is key for iris authentication to be viable in the field due to<br />
size of the image. Crop/masked images allow for close to 2kb images which tends to be relatively<br />
easier on transmission during online authentication.<br />
All devices supported auto capture. Forced capture was not implemented across devices uniformly<br />
and hence was not used.<br />
Auto capture algorithms on few cameras failed to capture in instances where special eye conditions<br />
were presented (see section 8.4). It is very important for the auto capture algorithms be tuned to<br />
capture resident iris with special eye conditions in order to improve the coverage of iris<br />
authentication.<br />
© UIDAI, 2009-2012 Page 32 of 36
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
Cameras that seek to block ambient light provide visible light source inside the camera. Visible light<br />
source serves two purposes. It prevents dilation of pupil that would otherwise occur in a dark<br />
environment. It helps resident to maintain proper gaze. Residents complained about some light<br />
sources to be too bright to cause stress. When light source was not present, the residents had to be<br />
instructed to look straight. Providing resident focus points such as a mirror so resident can see<br />
his/her own eyes inside will also help retain gaze.<br />
Two single cameras supported eye flaps to help position the device close to eyes softly. These flaps<br />
could rotate 180 degrees to capture either of the eyes. Although this feature was innovative and<br />
helped operator and resident to capture easily, room for error due to non-rotation of flaps for each<br />
capture may cause bad quality images as flaps tend to obstruct movement of device close to eyes<br />
and nose, when not rotated.<br />
All the devices were connected to the PC through USB interface. Few cameras required independent<br />
power source while most drew power through USB. This makes certain cameras useful for mobile<br />
field requirements with handheld usage while others which require continuous power suitable for<br />
desk usage with continuous power availability.<br />
7.3 Capture aids<br />
7 Devices out of 8 implemented one or many capture aids during the capture process to provide<br />
support and actionable feedback to operator. Actionable Feedback provided to operator falls in one<br />
or more of the following categories.<br />
1. LCD display for operator to visually see the camera output. By moving device closer/farther<br />
the operator was able to get improve the focus and quality.<br />
2. Using small lights behind the camera to indicate capture start and end process. This helped<br />
operator to position the device at the right distance for the capture process to begin and<br />
also know when the process completed.<br />
3. Changing color of the light to indicate when the resident is too far or too close or at the right<br />
distance. For example, light color would change to blue when the resident moved too close<br />
or and turned to red when the resident moved too far and turn green when the resident is in<br />
the right range.<br />
4. Devices using visible light source also provided feedback in that when the source was turned<br />
on, by watching the eye socket being lit, operator could infer that capture process having<br />
started and similarly when it was turned off, infer that capture process was completed.<br />
However, if the room ambient light was high, then operator might not be able to notice the<br />
light source from the camera. Excess light source was seen to result in constriction (reduced<br />
pupil) affecting the ability of the matchers to segment iris.<br />
5. Provide operator feedback related to capture process on the PC. Messages such as resident<br />
being far, close and at the right distance etc. were provided to operator. However it<br />
required that the operator watch both PC and camera at the same time. Operator feedback<br />
should be incorporated in the camera.<br />
6. Alignment aids in terms of view finder for operator to align the camera to the resident eyes.<br />
This helped operator to align the device to the eye level.<br />
It was observed that providing capture aids and actionable feedback to the operator<br />
improves the capture process and enhances the quality of capture. Actionable feedback<br />
© UIDAI, 2009-2012 Page 33 of 36
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
becomes essential when the capture distance is high and capture volume is not big enough<br />
for quick and high quality capture. Lack of capture aids/effective operator feedback was<br />
seen to make the capture process harder.<br />
There is scope for providing further capture aids and more actionable feedback for the<br />
operator. These areas include<br />
1. Feedback related to quality of the image - devices could provide image quality feedback<br />
to the operator to enable him to take another impression. Quality areas such as focus,<br />
gaze, occlusion, presence of reflected objects covering iris etc. could be highlighted<br />
during the capture process by device (as actionable feedback). This will help operator to<br />
capture high quality images.<br />
2. Iris rotation – Device vendors could alert the operators when device is not held straight.<br />
Images are likely to rotate by certain angle when the devices are not held straight which<br />
may result in rejects during the matching process. Feedback to operator in this regard is<br />
likely to help the operator to hold the device straight. Similarly, devices could provide<br />
feedback when the device is held upside down.<br />
3. Cameras with mechanical aids - Alignment aid<br />
– Presence of alignment aids helps operator to position the device for capture.<br />
– Alignment aid helps to fix the camera on capture area to help position the camera<br />
correctly. Alignment aid will also help in placing the device at the right capture distance.<br />
– In the absence of alignment aids, display of live stream from camera will help operator<br />
to align the device.<br />
– Alignment aid design should take safety of eyes into account<br />
– Alignment aid / Enclosure help reduce ambient reflections. This may help accuracy.<br />
Cameras with Enclosure help reduce ambient reflections. This will also help when the<br />
capture is taking place in open areas or areas with excess ambient lighting conditions.<br />
In summary, Cameras with visual indications for capture process, eye alignment and capture<br />
completion were easiest to use. Cameras that offered backlit LCD display to the operator helped<br />
operator to capture very quickly. Conversely, cameras that offered no feedback to operator were<br />
relatively more difficult to use. Dual eye cameras would benefit from alignment visual indication for<br />
operator. Capture aids help operator and resident during the capture process.<br />
7.4 Detection and Capture of iris<br />
It was seen during the POC that certain cameras were able to detect and capture resident iris more<br />
effectively than others. It was observed that certain special eye conditions where resident had<br />
undergone possibly surgery (for cataract in most cases) due to which the pupil shape has changed<br />
had resulted in capture failures in certain authentication cameras whereas certain other<br />
authentication cameras were able to capture the same. Some of the resident’s iris images which<br />
were successfully captured on few cameras but failed to capture on others are shown below.<br />
© UIDAI, 2009-2012 Page 34 of 36
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
Improvements to detection and capture algorithms after taking note of the nature of iris images<br />
below is expected to improve the capture efficiency of failing devices.<br />
Figure 19 Resident with special condition Eyes<br />
7.5 Dual eye vs. single eye cameras<br />
During POC, of 8 cameras deployed, 4 cameras were dual iris and 4 were single eye cameras. Of the<br />
four dual iris cameras deployed, one camera implemented dual simultaneous capture, with left/right<br />
single-eye capture in succession.<br />
Dual iris cameras were seen to complete the dual eye capture overall faster than single eye cameras<br />
where the capture for each iris had to be initiated one eye at a time. Since single eye cameras had<br />
to capture one eye at a time, and dual eye cameras capture both eyes together. Consequently dual<br />
eye capture time is less for dual eye cameras.<br />
However when capturing iris of residents with special eyes, it is possible that one of the iris is good<br />
and can be captured with high quality. Dual iris devices which look for pair of iris in good conditions<br />
© UIDAI, 2009-2012 Page 35 of 36
Iris <strong>Authentication</strong> <strong>Accuracy</strong> - <strong>PoC</strong> <strong>Report</strong><br />
are likely to fail in these situations. Single eye devices have an advantage in these situations where<br />
resident’s only eye can be captured due to special eye conditions. Dual iris cameras can improve<br />
capture algorithms to capture resident iris when presented with resident with special eye<br />
conditions.<br />
In Summary, both single eye and dual eye devices were found suitable for iris authentication.<br />
7.6 Capture Distance<br />
Capture distance refers to distance at which the camera should be held in order to enable the<br />
capture of iris. As noted in the table above, in the field trial, cameras had capture distance ranging<br />
from 10mm to over 300mm.<br />
Higher capture distance in general has convenience and hygiene value as device need not be taken<br />
very close to eyes during the capture. As capture distance increase, capture depth has to be<br />
correspondingly increased to ensure ease of capture.<br />
© UIDAI, 2009-2012 Page 36 of 36