Military Communications and Information Technology: A Trusted ...
Military Communications and Information Technology: A Trusted ... Military Communications and Information Technology: A Trusted ...
258 Military Communications and Information Technology... (a) P2P connectivity and RP subscriber forwarder (b) Subscription with resulting multicast tree (c) Another subscription (d) A publish Figure 2. Subscribe and publish in KadScribe The messages used in KadScribe are called subscribe, subscribe ack, unsubscribe, publish, publish ack and multicast. KadScribe in contrast to Scribe has no create message to create a topic. The functionality of this message is integrated in the subscribe message as a topic is created as soon as the first node subscribes to it. In contrast to Scribe, publish and multicast are realized in two separate messages to be able to acknowledge the publishing. This contributes to the resilience of the protocol. Multicast messages are not acknowledged not to overwhelm the sender with acknowledgements.
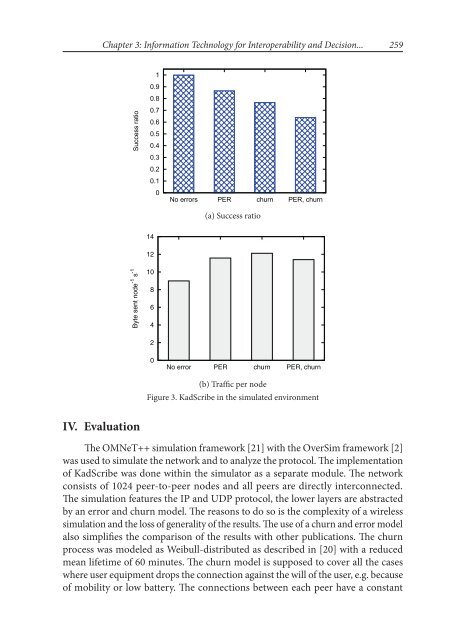
Chapter 3: Information Technology for Interoperability and Decision... 259 Success ratio 1 0.9 0.8 0.7 0.6 0.5 0.4 0.3 0.2 0.1 0 No errors PER churn PER, churn (a) Success ratio 14 Byte sent node -1 s -1 12 10 8 6 4 2 0 No error PER churn PER, churn (b) Traffic per node Figure 3. KadScribe in the simulated environment IV. Evaluation The OMNeT++ simulation framework [21] with the OverSim framework [2] was used to simulate the network and to analyze the protocol. The implementation of KadScribe was done within the simulator as a separate module. The network consists of 1024 peer-to-peer nodes and all peers are directly interconnected. The simulation features the IP and UDP protocol, the lower layers are abstracted by an error and churn model. The reasons to do so is the complexity of a wireless simulation and the loss of generality of the results. The use of a churn and error model also simplifies the comparison of the results with other publications. The churn process was modeled as Weibull-distributed as described in [20] with a reduced mean lifetime of 60 minutes. The churn model is supposed to cover all the cases where user equipment drops the connection against the will of the user, e.g. because of mobility or low battery. The connections between each peer have a constant
- Page 208 and 209: 208 Military Communications and Inf
- Page 210 and 211: 210 Military Communications and Inf
- Page 212 and 213: 212 Military Communications and Inf
- Page 214 and 215: 214 Military Communications and Inf
- Page 216 and 217: 216 Military Communications and Inf
- Page 218 and 219: 218 Military Communications and Inf
- Page 220 and 221: 220 Military Communications and Inf
- Page 222 and 223: 222 Military Communications and Inf
- Page 224 and 225: 224 Military Communications and Inf
- Page 226 and 227: 226 Military Communications and Inf
- Page 228 and 229: 228 Military Communications and Inf
- Page 230 and 231: 230 Military Communications and Inf
- Page 232 and 233: 232 Military Communications and Inf
- Page 234 and 235: 234 Military Communications and Inf
- Page 236 and 237: 236 Military Communications and Inf
- Page 239 and 240: Run-Time Ontology on the Basis of E
- Page 241 and 242: Chapter 3: Information Technology f
- Page 243 and 244: Chapter 3: Information Technology f
- Page 245 and 246: Chapter 3: Information Technology f
- Page 247 and 248: Chapter 3: Information Technology f
- Page 249 and 250: Chapter 3: Information Technology f
- Page 251 and 252: Chapter 3: Information Technology f
- Page 253 and 254: A Robust and Scalable Peer-to-Peer
- Page 255 and 256: Chapter 3: Information Technology f
- Page 257: Chapter 3: Information Technology f
- Page 261 and 262: Chapter 3: Information Technology f
- Page 263 and 264: Chapter 3: Information Technology f
- Page 265 and 266: Automatic Exploitation of Multiling
- Page 267 and 268: Chapter 3: Information Technology f
- Page 269 and 270: Chapter 3: Information Technology f
- Page 271 and 272: Chapter 3: Information Technology f
- Page 273 and 274: Chapter 3: Information Technology f
- Page 275 and 276: Chapter 3: Information Technology f
- Page 277 and 278: Chapter 3: Information Technology f
- Page 279 and 280: Chapter 3: Information Technology f
- Page 281 and 282: Information Fusion Under Network Co
- Page 283 and 284: Chapter 3: Information Technology f
- Page 285 and 286: Chapter 3: Information Technology f
- Page 287 and 288: Chapter 3: Information Technology f
- Page 289 and 290: Chapter 3: Information Technology f
- Page 291 and 292: Chapter 3: Information Technology f
- Page 293: Chapter 3: Information Technology f
- Page 296 and 297: 296 Military Communications and Inf
- Page 298 and 299: 298 Military Communications and Inf
- Page 300 and 301: 300 Military Communications and Inf
- Page 302 and 303: 302 Military Communications and Inf
- Page 305 and 306: Commanding Multi-Robot Systems with
- Page 307 and 308: Chapter 3: Information Technology f
Chapter 3: <strong>Information</strong> <strong>Technology</strong> for Interoperability <strong>and</strong> Decision...<br />
259<br />
Success ratio<br />
1<br />
0.9<br />
0.8<br />
0.7<br />
0.6<br />
0.5<br />
0.4<br />
0.3<br />
0.2<br />
0.1<br />
0<br />
No errors PER churn PER, churn<br />
(a) Success ratio<br />
14<br />
Byte sent node -1 s -1<br />
12<br />
10<br />
8<br />
6<br />
4<br />
2<br />
0<br />
No error PER churn PER, churn<br />
(b) Traffic per node<br />
Figure 3. KadScribe in the simulated environment<br />
IV. Evaluation<br />
The OMNeT++ simulation framework [21] with the OverSim framework [2]<br />
was used to simulate the network <strong>and</strong> to analyze the protocol. The implementation<br />
of KadScribe was done within the simulator as a separate module. The network<br />
consists of 1024 peer-to-peer nodes <strong>and</strong> all peers are directly interconnected.<br />
The simulation features the IP <strong>and</strong> UDP protocol, the lower layers are abstracted<br />
by an error <strong>and</strong> churn model. The reasons to do so is the complexity of a wireless<br />
simulation <strong>and</strong> the loss of generality of the results. The use of a churn <strong>and</strong> error model<br />
also simplifies the comparison of the results with other publications. The churn<br />
process was modeled as Weibull-distributed as described in [20] with a reduced<br />
mean lifetime of 60 minutes. The churn model is supposed to cover all the cases<br />
where user equipment drops the connection against the will of the user, e.g. because<br />
of mobility or low battery. The connections between each peer have a constant