Information Security Report 2010 - Nec
Information Security Report 2010 - Nec
Information Security Report 2010 - Nec
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
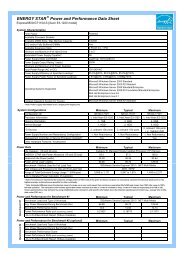
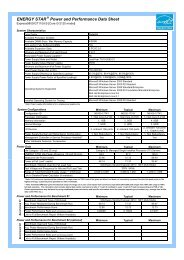
Reinforcement of <strong>Information</strong> Leak Prevention Measures<br />
Since fiscal 2009, the NEC Group has worked to implement<br />
measures aimed specifically at eradicating information<br />
leak incidents. That year we achieved our goal of<br />
reducing by half the number of leaks compared with<br />
those in the previous fiscal year. In fiscal <strong>2010</strong>, we<br />
focused on following measures to reduce further the<br />
number of incidents.<br />
Specifically, management measures included:<br />
1) management of confidential information for suppliers<br />
2) measures to prevent the loss or theft of USB flash<br />
drives and other removable storage media 3) use of thin<br />
client terminals, etc. as an enhanced security measure for<br />
work outside the company and 4) inventory and management<br />
of personal information. Other technology measures<br />
included: 1) System to Prevent <strong>Information</strong> Leak<br />
2) Secure Email Distribution System and 3) Secure <strong>Information</strong><br />
Exchange Site.<br />
<strong>Information</strong> <strong>Security</strong> Assessment<br />
The NEC Group conducts information security assessment<br />
for ensuring that information security measures partner companies.<br />
management involved in an outsourcing business with<br />
have been strictly implemented within each organization. (2) Method for Conducting <strong>Information</strong> <strong>Security</strong><br />
We have conducted assessments twice a year since<br />
Assessment<br />
fiscal 2006, and established a PDCA cycle for security The information security assessment was conducted from<br />
improvement activities.<br />
the management (organizational assessment) and implementation<br />
(individual assessment) point of view. Then by<br />
Aiming to eliminate the occurrence of any security<br />
incidents that could be prevented if the information security<br />
assessment was implemented strictly, the fiscal <strong>2010</strong> problems on both management and implementation<br />
reviewing the results of the gap analysis, we clarified the<br />
assessment was conducted targeting 98 domestic companies<br />
and 87 overseas companies, 185 Group Compa-<br />
PDCA cycle between the <strong>Information</strong> <strong>Security</strong> Promoters<br />
sides. To cope with these problems, we established a<br />
nies in total (an increase in the companies subject to and the individual staff members in each organization, and<br />
assessment compared with those in the previous year). between supervisors and their subordinates in pursuit of<br />
(1) Description of <strong>Information</strong> <strong>Security</strong> Assessment improved management activity at the working level.<br />
Five priority measures were defined specifically aimed at (3) Improvements Made Through Utilization of<br />
eradicating information security incidents related to information<br />
leaks. As a result of incident analysis, these mea-<br />
As a result of the assessment, each organization<br />
Assessment Results<br />
sures were determined as those reducing or eliminating worked to understand the causes of an inadequately<br />
the primary cause of the incidents. The measures<br />
implemented security measure, make an action plan to<br />
include: 1) security measures for use of USB flash drives improve the security level and carry out the plan. The<br />
and other removable storage media 2) security measures organization made the <strong>Information</strong> <strong>Security</strong> Promotion<br />
for the work outside the Company 3) assessment of Plan for fiscal 2011. And the plan included the insufficient<br />
security measures for fiscal <strong>2010</strong> and new secu-<br />
personal information relating to priority measures 4) security<br />
measures for entry passes 5) confidential information rity measures for fiscal 2011. As a result, the<br />
organization can keep following<br />
the PDCA cycle.<br />
■ PDCA Cycle via <strong>Information</strong> <strong>Security</strong> Assessment<br />
In fiscal 2011 the NEC Group<br />
Improvements<br />
plans to conduct the assessment<br />
Assessment System Enhancements<br />
Act<br />
by each employee role.<br />
Check<br />
PDCA<br />
Cycle<br />
Plan<br />
Assessment<br />
Do<br />
06<br />
NEC CORPORATION<br />
<strong>Information</strong> <strong>Security</strong> <strong>Report</strong> <strong>2010</strong>