Information Security Report 2010 - Nec
Information Security Report 2010 - Nec
Information Security Report 2010 - Nec
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
NEC’s Initiatives to Build a Secure IT-Driven Society<br />
<strong>Information</strong> <strong>Security</strong> Human Resources Development<br />
The NEC Group develops human resources with expert knowledge and skills<br />
relating to information security to meet the expectations of customers, business<br />
partners, the general public and the market.<br />
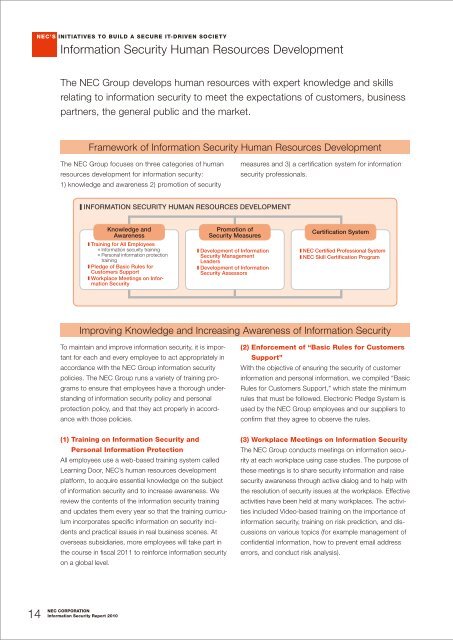
Framework of <strong>Information</strong> <strong>Security</strong> Human Resources Development<br />
The NEC Group focuses on three categories of human<br />
resources development for information security:<br />
1) knowledge and awareness 2) promotion of security<br />
measures and 3) a certification system for information<br />
security professionals.<br />
■ <strong>Information</strong> <strong>Security</strong> Human Resources Development<br />
Knowledge and<br />
Awareness<br />
■ Training for All Employees<br />
■ <strong>Information</strong> security training<br />
■ Personal information protection<br />
training<br />
■ Pledge of Basic Rules for<br />
Customers Support<br />
■ Workplace Meetings on <strong>Information</strong><br />
<strong>Security</strong><br />
Promotion of<br />
<strong>Security</strong> Measures<br />
■ Development of <strong>Information</strong><br />
<strong>Security</strong> Management<br />
Leaders<br />
■ Development of <strong>Information</strong><br />
<strong>Security</strong> Assessors<br />
Certification System<br />
■ NEC Certified Professional System<br />
■ NEC Skill Certification Program<br />
Improving Knowledge and Increasing Awareness of <strong>Information</strong> <strong>Security</strong><br />
To maintain and improve information security, it is important<br />
for each and every employee to act appropriately in<br />
accordance with the NEC Group information security<br />
policies. The NEC Group runs a variety of training programs<br />
to ensure that employees have a thorough understanding<br />
of information security policy and personal<br />
protection policy, and that they act properly in accordance<br />
with those policies.<br />
(2) Enforcement of “Basic Rules for Customers<br />
Support”<br />
With the objective of ensuring the security of customer<br />
information and personal information, we compiled “Basic<br />
Rules for Customers Support,” which state the minimum<br />
rules that must be followed. Electronic Pledge System is<br />
used by the NEC Group employees and our suppliers to<br />
confirm that they agree to observe the rules.<br />
(1) Training on <strong>Information</strong> <strong>Security</strong> and<br />
Personal <strong>Information</strong> Protection<br />
All employees use a web-based training system called<br />
Learning Door, NEC’s human resources development<br />
platform, to acquire essential knowledge on the subject<br />
of information security and to increase awareness. We<br />
review the contents of the information security training<br />
and updates them every year so that the training curriculum<br />
incorporates specific information on security incidents<br />
and practical issues in real business scenes. At<br />
overseas subsidiaries, more employees will take part in<br />
the course in fiscal 2011 to reinforce information security<br />
on a global level.<br />
(3) Workplace Meetings on <strong>Information</strong> <strong>Security</strong><br />
The NEC Group conducts meetings on information security<br />
at each workplace using case studies. The purpose of<br />
these meetings is to share security information and raise<br />
security awareness through active dialog and to help with<br />
the resolution of security issues at the workplace. Effective<br />
activities have been held at many workplaces. The activities<br />
included Video-based training on the importance of<br />
information security, training on risk prediction, and discussions<br />
on various topics (for example management of<br />
confidential information, how to prevent email address<br />
errors, and conduct risk analysis).<br />
14<br />
NEC CORPORATION<br />
<strong>Information</strong> <strong>Security</strong> <strong>Report</strong> <strong>2010</strong>