Elektronika 2009-11.pdf - Instytut Systemów Elektronicznych
Elektronika 2009-11.pdf - Instytut Systemów Elektronicznych
Elektronika 2009-11.pdf - Instytut Systemów Elektronicznych
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
As is it shown in Fig. 7, the decision-aid will analyse the<br />
ontology and generate the facts and rules. Actually, the ontology<br />
instances will be mapped to facts and the SWRL rules will<br />
be mapped to engine’s rules.<br />
In that manner, the tool will be facilitated with information<br />
that will allow to:<br />
• measure dynamically (the value will not be hard coded into<br />
ontology) the vulnerability likelihood,<br />
• dynamically rank the vulnerabilities,<br />
• inform the operator what may cause the fault in SCADA<br />
system,<br />
• what element of the network needs some attention and<br />
safeguards.<br />
By defining the additional (tool build-in) rules there will be<br />
possibility to realize the customized features of the aid tool:<br />
• proposing the action plans with information how to minimize<br />
the likelihood of the vulnerability,<br />
• apply some appropriate countermeasures to minimize the<br />
probability of most likely attack,<br />
• evaluate the SCADA system condition based on standards.<br />
Conclusions<br />
In this paper ontology-based approach for description of<br />
SCADA systems vulnerabilities has been presented. Functionalities<br />
of ontology applied to knowledge representation for<br />
security and protection of critical infrastructures have been<br />
shown. Our solution has been developed within research in<br />
the INSPIRE Project that aims to increase security and protection<br />
through infrastructure resilience. Presented ontology<br />
approach will be basis for Decision - aid tool which is a part of<br />
INSPIRE security framework.<br />
The research leading to these results has received funding from the<br />
European Community’s Seventh Framework Programme (FP7/2007-<br />
2013) under grant agreement no. 225553 (INSPIRE Project).<br />
References<br />
[1] Critical infrastructure: Understanding Its Component Parts, Vulnerabilities,<br />
Operating Risks, and Interdependencies, Tyson<br />
Macaulay, August 2008.<br />
[2] Lewis T. G.: Critical Infrastructure Protection in Homeland Security:<br />
Defending a Networked Nation, Wiley-Interscience,<br />
2006.<br />
[3] Ustawa z dnia 26 kwietnia 2007 r. o zarządzaniu kryzysowym,<br />
Opracowano na podstawie: Dz.U. z 2007 r. nr 89, poz. 590.<br />
[4] Homeland Security Presidential Directive/Hspd-7, December 17,<br />
2003.<br />
[5] European Parliament legislative resolution of 10 July 2007 on<br />
the proposal for a Council directive on the identification and designation<br />
of European Critical Infrastructure and the assessment<br />
of the need to improve their protection (COM(2006)0787 - C6-<br />
0053/2007 - 2006/0276(CNS)).<br />
[6] EU Critical Infrastructure Protection (CIP), Council of the European<br />
Union, Brussels, 28 October 2005.<br />
[7] McClanahan Robert H. :“The benefits of networked SCADA systems<br />
utilizing IP-enabled networks”, Arkansas Electric Cooperative<br />
Corporation, IEEE, 2002.<br />
[8] ISO/IEC 13335-1:2004, Information Technology - Security Techniques<br />
- Management of information and communications technology<br />
security - Part 1: Concepts and models for information<br />
and communications technology security management.<br />
[9] http://nvd.nist.gov/.<br />
[10] http://osvdb.org/.<br />
[11] Choraś M., Renk R., Flizikowski A., Hołubowicz W.: Ontologybased<br />
description of networks vulnerabilities, Polish Journal of<br />
Environmental Studies, vol. 5c, 2008.<br />
[12] SWRL: A Semantic Web Rule Language Combning OWL and<br />
RuleML. W3C Member Submission, http://www.w3.org/Submission/SWRL/.<br />
[13] Stamp J., Dillinger J., Young W.: Common vulnerabilities in critical<br />
infrastructure control systems. Networked Systems Survivability<br />
and Assurance Department, Jennifer DePoy, Information<br />
Operations Red Team & Assessments Department, Sandia National<br />
Laboratories, 22 May 2003.<br />
[14] “D2.2 - Identification of Vulnerabilities” , INSPIRE Project, July<br />
<strong>2009</strong>.<br />
Synthesis and management of system with<br />
parallel multiprocessors and fault tolerance<br />
(Synteza i zarządzanie komputerowych systemów z równoległymi wieloprocesorami<br />
i tolerowaniem uszkodzeń)<br />
dr MIECZYSŁAW DRABOWSKI<br />
Cracow University of Technology, Faculty of Electrical and Computer Engineering<br />
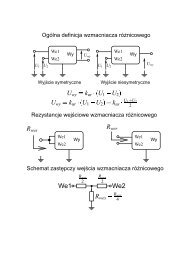
The management of computer systems [1,2] is an issue the<br />
basic objective of which is to find an optimum solution, satisfy<br />
the requirements and limitations enforced by the given specification<br />
of operations (tasks) and resources. The following criteria<br />
of optimality are usually considered: the costs of planning in<br />
execution of operations, its operating speed and reliability. The<br />
problems of operations and resources scheduling are one of<br />
the most significant issues occurring at the procedure planning<br />
of operating system responsible for controlling the distribution<br />
of tasks and resources in computer systems. The problem of<br />
control in resources requires the list of available hardware resources<br />
- the set describing resources - which can be used to<br />
realization of operations. The starting point for constructing our<br />
approach to the issues of fault tolerance system is the deterministic<br />
theory of task scheduling [3]. Accordingly, decomposition<br />
of the general task scheduling model is suggested,<br />
adequate to the problems of fault tolerance system [4]. We will<br />
discuss the system: ∑={R,T,C}, where: R - resources, T - tasks<br />
and C - optimality criteria. We assume that processor set<br />
P={P 1 ,P 2 ,…,P m } consists of m elements and additional resources<br />
set A = { A 1 ,A 2 ,…,A p } consist of p elements). We consider<br />
a set of n tasks to be processed with a set of resources<br />
38 ELEKTRONIKA 11/<strong>2009</strong>