Elektronika 2009-11.pdf - Instytut Systemów Elektronicznych
Elektronika 2009-11.pdf - Instytut Systemów Elektronicznych
Elektronika 2009-11.pdf - Instytut Systemów Elektronicznych
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
a) will be or could be broken, or<br />
b) a public key certificate of a time stamping authority will be<br />
expired soon or is revoked.<br />
Prior to such an event, the trust to existing time stamps<br />
has to be reassured by means of new time stamping of the<br />
previous archive timestamp. Two types of the time stamp renewal<br />
are used (see details in Section 5):<br />
a) time stamp renewal: the new archive timestamp is generated,<br />
which is related to the previous one; subsequent<br />
timestamps obtained in this renewal procedure form the<br />
archive timestamp chain for a data object or a group of<br />
data objects;<br />
b) hash value renewal: the new time stamp for the archival<br />
form is generated; it is related to previous timestamps and<br />
to data objects stamped with the initial archive timestamp<br />
for the archival form as well; the new set of the archive<br />
timestamp chain is created; the set of one or more archive<br />
timestamp chains forms the archive timestamp sequence.<br />
5. Some technical examples<br />
of the timestamp and hash value renewal<br />
Two standards are presented below (ETSI TS 101 733 [7] and<br />
RFC 4998 [15]). Each of them can be used both for the timestamp<br />
and the hash value renewal. However, while the first<br />
standard is applied mainly to a single data object (an electronic<br />
document or signature), the second one can cover a group of<br />
data objects. In both cases the evidence records are generated<br />
(CAdES-A and EvidenceRecord structures, respectively)<br />
and thent available on each request of the authorized entities.<br />
5.1 ETSI TS 101 733 (CAdES) standard<br />
To keep the probative value of an electronic document the<br />
specification of the archival form CAdES [7] is used. The<br />
archive timestamp is related to each of the SignerInfo data<br />
element that is included into the SignedData. The value of<br />
the messageImprint field of the TimeStampToken (3) structure<br />
contains the hash value returned by the hash algorithm applied<br />
to an input argument being the concatenation of the following<br />
elements:<br />
a) the encapContentInfo field of the SignedData sequence;<br />
when the field is absent, the content is stored outside of<br />
this field, but its value is protected by the signature value located<br />
in the SignedData sequence;<br />
b) the Certificates and crls fields of the SignedData sequence,<br />
if these fields are present in this sequence,<br />
c) all data elements of the SignerInfo sequence, which should<br />
be protected by the generated timestamp token, including<br />
all signed and unsigned attributes.<br />
The SignerInfo can contain more then one instance of<br />
archive-time-stamp attributes. Furthermore, each successive<br />
timestamp protects all timestamps made previously. It means<br />
that the CAdES archival form allows to renew the archive<br />
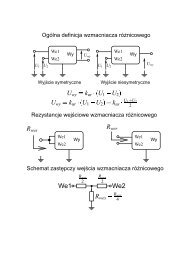
timestamp using mechanism like this presented on Fig. 1.<br />
Fig. 1. The idea of renewal of an archival timestamps form (CAdES<br />
[7])<br />
Rys. 1. Idea odnawiania znaczników czasu archiwum (CAdES [7])<br />
Each subsequent archive timestamp covers all existing<br />
timestamps, so the archive-time-stamp attribute can be used<br />
also to build the new hash value: it is sufficient to choose the<br />
new stronger hash function, calculate the new hash values<br />
and obtain the new archive timestamps.<br />
5.2 RFC 4998 de facto standard<br />
The proposal published in RFC 4998 [15] contains the following<br />
structure of the evidence record syntax (ERS):<br />
EvidenceRecord ::= SEQUENCE {<br />
version INTEGER { v1(1) },<br />
digestAlgorithms SEQUENCE OF AlgorithmIdentifier,<br />
cryptoInfos [0] CryptoInfos OPTIONAL,<br />
encryptionInfo [1] EncryptionInfo OPTIONAL,<br />
archiveTimeStampSequence ArchiveTimeStampSequence<br />
}<br />
This structure can be treated as an unsigned attribute and<br />
appears only once in each SignerInfo element of the Signed-<br />
Data structure (see the specification of archival form CAdES-A).<br />
The evidence record contains the ArchiveTimeStampSequence<br />
field, which is a sequence of archive timestamp chains:<br />
ArchiveTimeStampSequence ::= SEQUENCE OF<br />
ArchiveTimeStampChain<br />
ArchiveTimeStampChain ::= SEQUENCE OF<br />
ArchiveTimeStamp<br />
The ArchiveTimeStampChain structure contains the<br />
archive timestamps generated as the result of the timestamp<br />
renewal, while the ArchiveTimeStampSequence structure- as<br />
the result of the hash value renewal. The archive timestamp<br />
ArchiveTimestamp includes the timestamp and a set of lists of<br />
hash values and its verification must give a point of time when<br />
a given data object or a group of data objects has existed.<br />
The evidence record EvidenceRecord allows the implementation<br />
of timestamp and hash renewal procedures. The<br />
Fig. 2 is some example of the timestamp renewal used to the<br />
electronic documents divided into groups. Various methods<br />
can be applied to aggregate the group of documents (data objects).<br />
The most effective are this based on an authenticated<br />
dictionary [18], i.e. on data structures viewed simultaneously<br />
as the structured aggregate of all protected information and<br />
the proof of the authenticity and validity of these information.<br />
The initial archive timestamp generated for such aggregated<br />
groups of data is related to lists of hash values, which<br />
allow the verification of the existence of a data object or a<br />
group of data objects at a certain time. The lists of hash values<br />
are generated usually by reduction of an ordered Merkle<br />
hash tree (RFC 4998 [15], M. T. Goodrich, et al. [18]).<br />
7. Conclusions<br />
In order to model a long-term electronic signature scheme LT-<br />
CESS (as defined by Section 3) there is necessary to create<br />
so-called Virtual Signed Electronic Document (V-SED) and introduce<br />
an electronic signature verification algorithm as given<br />
in Equation (6). If there can be found an effective signature<br />
verification algorithm of the form (6), then for a given point in<br />
time it is always possible to assert the authenticity of an electronic<br />
document related to this V-SED and its existence before<br />
a certain moment in the past (in Section 3 a document<br />
ELEKTRONIKA 11/<strong>2009</strong> 33