Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
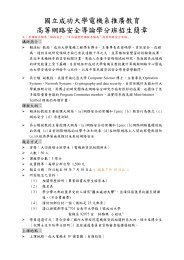
<strong>安全性機制及工具</strong><br />
主講人:曾龍 助理教授<br />
興國管理學院資訊科學系 助理教授<br />
TEL:(06)2870549<br />
E-mail: drbt@pchome.com.tw<br />
btseng@mail.hku.edu.tw<br />
1
OVERVIEW<br />
� O.S Level Security Tools<br />
--Windows XP,2000,2003/LINUX/*BSD/Solaris/…<br />
� Application Security Tools<br />
--SQL server: Oracle,DB2, MS SQL, MySQL, Postgresql<br />
--Mail Server: Exchange server, Sendmail, Qmail,….<br />
--Web/Application server: IIS, Apache, IBM websphere, Tomcat<br />
� Auditing &Trapping Tools<br />
-- Syslog-ng, Honeypot/Honeynet/HoneyWorld<br />
� Enhanced Security Tools(Main Focus)<br />
-- Firewall/IDS/VPN<br />
� Enterprise Security Testing<br />
--Vulnerability Scanner/ Penetration Test<br />
� Digital Forensic<br />
2
1.網路世界上的系統<br />
3
Auditing &Trapping Tools:Syslog-ng<br />
4
Auditing &Trapping Tools:<br />
Honeypot/Honeynet/HoneyWorld<br />
5
Enhanced Security Tools: Firewall<br />
� 1.What is Firewall ?<br />
� 2.Firewall 技術<br />
� 3.著名防火牆介紹<br />
� 4.Firewall 佈署架構<br />
� 5.IPTable 介紹<br />
� 6.Firewall 測試<br />
� 7.Firewall Extend<br />
6
1. What Is an Internet Firewall?<br />
� 防火牆是一種雙向的安全管理機制<br />
� 它只允許一些特定的資料通過,且必須經過一些事先設定<br />
的安全規則和政策才能放行。<br />
� 防火牆能有效地記錄網路傳輸的資料量與種類<br />
� 防火牆不能防護不經過它的連接<br />
� 防火牆不能防止新的威脅且不能完全防止病毒<br />
7
2. Firewall 技術<br />
� 封包過濾式防火牆 (Packet Filter)<br />
� 應用層閘道式防火牆 (Application-Level<br />
Gateway)<br />
� 電路層閘道式防火牆 (Circuit-Level Gateway)<br />
8
2.1 封包過濾式防火牆 (Packet Filter)<br />
9
� 封包過濾是在OSI七層架<br />
構中第三層以下的網路中<br />
運作。封包過濾器的功能<br />
主要是檢查過往的每一個<br />
IP資料封包,如果其表頭<br />
中所含的資料內容符合事<br />
先設定的安全規則和政策<br />
就放行通過。<br />
� 最常見的的封包過濾器就<br />
是(高階)路由器(Router)<br />
10
封包過濾的優點<br />
封包過濾式防火牆的最大優點是速度快(在任何時<br />
候都可以使封包通過)、容易建置、設置成本較低<br />
並具有完全通透性(Transparency)<br />
11
封包過濾的缺點<br />
封包過濾式防火牆的作用層次比較低,一些屬<br />
於OSI 模式中上幾層的功能無法在此類防火牆中<br />
做到,所以無法對所經過的資料流提供較詳細及<br />
較高層的稽核能力,有時也由於必須預先開放某<br />
些埠口,而造成了安全上的大漏洞。<br />
12
2.2 應用層閘道式防火牆<br />
(Application-Level Gateway)<br />
13
2.2 應用層閘道式防火牆<br />
(Application-Level Gateway)<br />
� Application-Level Gateway作<br />
用於OSI模組的應用層,它針<br />
對不同的應用程式如FTP、<br />
HTTP、Telnet等來分別進行<br />
安全的稽核工作。它是利用<br />
閘道或代理器(Proxy)—將內<br />
部網路與外部網路區隔開<br />
來,而存儲轉發(Store-and<br />
Forward) 。<br />
14
2.2 應用層閘道式防火牆<br />
(Application-Level Gateway)<br />
� 防火牆內的Clinet端實際是連接到防火牆之內的FTP伺<br />
服器,再由防火牆之內的FTP伺服器以Client端的身分<br />
去網際網路上真正的FTP伺服器上擷取檔案。<br />
� 應用層閘道器會先將欲通過它的傳輸連接切斷,再建<br />
立另一個連接,它會從這個連接的過程之中獲得一些<br />
必要的資訊,並依照各個應用程式之中所設定的一些<br />
規則,來決定誰可以進出防火牆的內外、誰可以擷取<br />
那些資料。<br />
15
2.2 應用層閘道式防火牆<br />
(Application-Level Gateway)<br />
� 作用在OSI 模式的最高層, Application-Level<br />
Gateway可以了解所有通過封包的資訊。<br />
� 目的端的伺服器無法知道Clinet端主機的實際位址,使<br />
得內部的網路位址可不為外界所知,如此以達到防火<br />
牆的功用。<br />
� 在功能上來說, Application-Level Gateway在各類型<br />
的防火牆技術之中算是最優良的。但它的價格較昂<br />
貴。<br />
� 它不完全具有透通性,有些程式應用很可能會莫名其<br />
妙地被阻檔在門外。<br />
16
2.3 電路層閘道式防火牆<br />
(Circuit-Level Gateway)<br />
17
2.3 電路層閘道式防火牆<br />
(Circuit-Level Gateway)<br />
� Circuit-Level Gateway是作<br />
用於OSI模式中的傳輸層,<br />
是介於封包過濾器和應用層<br />
閘道器之間的防火牆型式。<br />
� 它與應用層閘道器同樣是透<br />
過代理程式來進行安全控<br />
制,但作用於比較低的層<br />
次,並沒有專門針對每一個<br />
應用程式特別設定組態。<br />
� 當一個核可的服務接通之<br />
後,防火牆會建立一個交談<br />
(Session),而且馬上將埠口<br />
關閉。<br />
18
2.3 電路層閘道式防火牆<br />
(Circuit-Level Gateway)<br />
� 有些電路層閘道器具有動態地檢查資料封包狀態的功能,稱之為<br />
狀態檢驗(Statefull Inspection)技術。<br />
� 在閘道器的內部設置了一個連結狀態表,在查驗高層通信協定的<br />
同時,順便將過往交通的狀態記錄下來。<br />
� Circuit-Level Gateway的優點是比Packet Filtering還要安全又可<br />
掌握連線的資訊 ,且網路流量的效能較Application-Level<br />
Gateway更佳。<br />
� Circuit-Level Gateway缺點則為無法監督交談層(session-level)的<br />
活動,且封包流量比 packet filtering 慢。<br />
19
比較 : 運作方式與特色<br />
封包過濾式 應用層閘道式 電路層閘道式<br />
運作層次(OSI) 第三層(網路層) 第七層(應用層) 第四層(傳輸層)<br />
運作機制 路由器 代理程式 代理程式<br />
運作效率 最高 最低<br />
建置價格 最便宜 最昂貴<br />
建置容易度 最容易 最難<br />
通透性 完全通透 不完全通透 完全透通<br />
安全管控能力 最弱 最強<br />
20
3. 著名防火牆介紹<br />
� 3.1 軟體防火牆<br />
� WINDOWS XP/2003 ,<br />
� MS Internet Security Acceleration Server<br />
2000/2004 ,<br />
� IPtables,<br />
� Checkpoint<br />
� 3.2 硬體防火牆<br />
� Netscreen ,<br />
� Cisco Pix Firewall<br />
� Nokia(Checkpoint ,ISS…)<br />
21
3.1.1 軟體防火牆 – Windows XP<br />
22<br />
Mouse右鍵內容
設定規則<br />
23
記錄所有通過或禁止的封包,<br />
以便近一步的分析<br />
24
3.1.2 軟體防火牆 –ISA Server<br />
� ISA Server 是一套可擴充的企業用防火牆與網路快取伺服器軟體<br />
� 與 Windows 2000 整合之後,則可提供以原則 (Policy) 為基礎的<br />
安全性、網路的加速、以及網際網路管理等功能。<br />
� ISA Server 提供了兩種緊密整合的模式:<br />
� 多重層級 (Multilayer) 防火牆<br />
� 高效能的網路快取伺服器。<br />
可提供對封包層、電路層、及應用程式層的過濾功能;並提供狀<br />
態檢查功能來檢查通過防火牆的資料;還可控制存取原則並執<br />
行流量的路由工作。快取則可將使用者常要求的網路內容儲存<br />
,以提高網路效能以及使用者的使用經驗。<br />
26
小型、中型、大型 ISA Server 硬體規格<br />
每部伺服<br />
器安裝的<br />
Xeon CPU<br />
數量<br />
每部伺服<br />
器的記憶<br />
體大小<br />
27<br />
每部伺服<br />
器的 URL<br />
快取專用<br />
的磁碟空<br />
間<br />
每一陣列<br />
同一時間<br />
的使用者<br />
數<br />
小型 2 128M 36G 1,500 2<br />
中型 2 128M 54G 5,000 4<br />
大型 4 256M 63G 4,0000 9<br />
每個陣列<br />
的伺服器<br />
數量
3.1.3 軟體防火牆<br />
– Checkpoint Firewall-1<br />
� Checkpoint ,它是目前業界唯一一款具有開<br />
放、整合、能夠相容各平臺的網路安全綜合基<br />
礎設施。<br />
� Checkpoint Firewall-1在全球軟體防火牆產品<br />
中位居第一。<br />
� Checkpoint Firewall-1是一個綜合的、模組化<br />
的安全套件,它是一個基於策略的解決方案,提<br />
供集中管理、訪問控制、授權、加密、網路地<br />
址傳輸、內容顯示服務和服務器負載平衡等功<br />
能。<br />
28
3.1.3 軟體防火牆<br />
– Checkpoint Firewall-1<br />
� CP Firewall-1由3個交互操作的組件構成:控制<br />
組件、加強組件和可選組件。<br />
� 這些組件既可以運行在單機上,也可以部署在跨<br />
平台系統上。<br />
� 控制組件包括Firewall-1管理服務器和圖形化的客戶<br />
端<br />
� 加強組件包含Firewall-1檢測模塊和Firewall-1防火<br />
牆模塊<br />
� 可選組件包括Firewall-1 Encryption Module(主要用<br />
於保護VPN)、Firewall-1 Connect Control<br />
Module(執行服務器負載平衡)和Router Security<br />
Module(管理路由器訪問控制列表)。<br />
29
3.2.1 硬體防火牆 - NetScreen<br />
� NetScreen Technologies Inc.<br />
NetScreen於1997年成立,是整合型網路安全解決方<br />
案的領導者,根據Gartner Dataquest的2001防火牆軟<br />
硬體市場統計報告顯示,NetScreen擁有最大的市場佔<br />
有率。NetScreen提供一系列廣泛的網路安全解決方<br />
案,包括VPN、阻斷攻擊保護(denial of service<br />
protection)、防火牆(firewall)、入侵防護<br />
(intrusion prevention)等,<br />
30
3.2.2 硬體防火牆 –Cisco Pix Firewall<br />
� Cisco Systems的防火牆系列產品,提供了對網路重要<br />
資訊反偷竊、反破壞的優異保護功能;同時 對於一般<br />
駭客的拒絕服務(Denial of Service)攻擊做有效的了<br />
預防。您可以在網路上的不同節點應用不同的安全策<br />
略,以提供公司的網際網路(lnternet)、私有虛擬網路<br />
(Virtual Private Networks)及遠距私有網路(Extranet)<br />
的連結。<br />
� Cisco Systems的防火牆提供的重要安全功能包括<br />
(Perimeter Policy Enforcement)、私有虛擬網路<br />
(VPN)、內容過濾(Content Filtering)以及拒絕服務偵及<br />
保護(Denial of Service Detection And Prevention)。<br />
31
3.2.3 硬體防火牆 - Nokia IP40<br />
� 將人性化的設計帶進防火牆世界<br />
� 四種版本,選擇性更多<br />
� 精簡化的管理介面<br />
32
3.2.3 硬體防火牆 - Nokia IP40<br />
� Nokia 無線虛擬網路 Mobile VPN 解決方案 (包括<br />
Nokia Security Service Manager 和 Nokia Mobile<br />
VPN Client) 能與現有企業基礎架構整合,將<br />
IPSec VPN 的使用範圍延伸到行動通訊裝置。<br />
Nokia 9500 Communicator 也支援其它安全功<br />
能,例如裝置鎖定與網路應用系統 SSL 加密。<br />
33
小結<br />
� 軟體防火牆的主要優點,就是可清楚了解您使用系統<br />
的方式,且更能調整其設定以符合您的需求。<br />
� 但以一般而言,硬體防火牆仍較軟體防火牆效能高。<br />
主要原因是因為硬體防火牆為專職的防火牆,所有的<br />
資源(如CPU、記憶體等)均專門為防火牆設計、使<br />
用。而軟體防火牆則架設於開放作業平台之上(NT或<br />
UNIX),防火牆伺服器中相當多的資源已被作業平台佔<br />
用;所以防火牆軟體真正能使用的資源並不如預期的<br />
多,運作起來便力有未殆了。<br />
34
4. Firewall 佈署架構<br />
� 網路防火牆雖然大多以上述三種技術為基本的<br />
運作基礎,但其實務應用配置的種類及型式十<br />
分繁多。<br />
� 雙介面主機 (Dual-Homed Host)<br />
� 單一路由器防火牆 (screening router )<br />
� 屏障式閘道器防火牆 (Screened Host Gateway)<br />
� 屏障式子網防火牆 (Screened Subnet)<br />
� 雙屏障式子網防火牆 (Belt & Suspenders )<br />
35
4.1雙介面主機<br />
- Dual-Homed Host architecture<br />
36
4.2 單一路由器防火牆配置圖<br />
37
Using a screening router to do<br />
packet filtering<br />
38
4.2 單一路由器防火牆<br />
� 防火牆網路外部的使用者在透過單一路由器的封包過<br />
濾之後,才能接觸到網路內部的網際網路伺服器。<br />
� 通常這種配置下的防火牆管制工作一定要非常嚴格,<br />
只讓那些對擷取有嚴格限制的服務如電子郵件傳遞等<br />
進入內部的網路系統,而一些危險性較高的服務如遠<br />
端載入、檔案傳輸等皆阻檔在外。<br />
39
屏障式閘道器<br />
(Screened Host Gateway)防火牆配置圖<br />
一般小型的網路中,會使用單一防火牆中同時提供封包過濾與代<br />
理程式的雙重功能,它通常是利用內建封包過濾功能的路由器堵<br />
在第一線,而在內部網路另取一個主機作為應用層閘道器,此種<br />
配置方式可稱為屏障式閘道器。如此,位於代理程式前端的路由<br />
器就可以不必先經過複雜的組態設定來過濾封包。此為防火牆產<br />
品的最基本的型態。<br />
40
4.4 屏障式子網防火牆配置圖<br />
41
4.4 屏障式子網防火牆<br />
� 中型網路的保護架構可以採用上述的屏障式閘道器,<br />
一樣是由將單一閘道的防火牆擴展成數部主機,形成<br />
一個屏障式子網(Screened Subnet),提供內外界的各<br />
式服務,可以將風險及效能的負擔分散至數部主機。<br />
� 外來者須經由封包過濾器到公司的代理程式中,而內<br />
部的使用者則可先進到代理程式,再經由封包過濾<br />
器,或選擇直接經由封包過濾器入網際網路。<br />
42
4.5 雙屏障式子網防火牆配置圖<br />
43
4.5 雙屏障式子網防火牆<br />
� 較大型的網路,則可採用具有更高的安全管制的雙屏<br />
障式子網(Belt & Suspenders),在此模式中,利用一<br />
對封包過濾器形成一個非軍事區(DMZ,或稱會客<br />
區),而在內放置代理伺服器與Web伺服器等網路設<br />
備,此區的保護程度較內部網路為低,但一些較安全<br />
顧慮較低的服務可在此區中進行,而它與內部網路還<br />
以另一個封包過濾器相隔,因此能提供更進一步的保<br />
護。<br />
44
5. Linux/IPTable 介紹<br />
� 5.1 預設的原則表與鏈<br />
� 5.2 封包過濾原理<br />
� 5.3 Iptables語法結構<br />
45
Netfilter Architecture<br />
- A Packet Traversing the Netfilter System<br />
� Netfilter is merely a series of hooks in various points in a<br />
protocol stack (at this stage, IPv4, IPv6 and DECnet). The<br />
(idealized) IPv4 traversal diagram looks like the following:<br />
46
5.1 預設的原則表與鏈<br />
47
5.2 封包過濾原理<br />
48
5.3 Iptables語法結構<br />
� Iptables [-t table] command [match] [-j<br />
target/jump]<br />
� 5.3.1 Table 類型<br />
� [-t table]是指目前核心使用的原則表類型<br />
� EX � -t nat , -t mangle , -t filter (預設)<br />
� 5.3.2 Command 命令<br />
� 5.3.3 Match 比對<br />
� 5.3.4 Target 目標<br />
49
5.3.2 Command 命令<br />
� 表示要求iptables程式執行的工作,但只允許一個命令。<br />
除了「help」之外,所有的命令都必須以大寫來表示。<br />
� -A或--append 附加 iptables –A INPUT –I lo –j ACCEPT<br />
� -D或--delete 刪除<br />
� -E或--rename-chain 更名<br />
� -h或--help 說明<br />
� -F或--flush 清除<br />
� -P或--policy 設定原則鏈的目標<br />
� -N或--new-chain 新增使用者定義<br />
50
5.3.3 Match 比對<br />
� 若比對選項加入!則表示否定的意思。<br />
� -c或--set-counters<br />
� -d或--destination或--dst 指定套用原則的目的地主機<br />
� iptables –A INPUT –d 192.168.2.1<br />
� -i或--interface 指定封包進入的網路介面名稱<br />
� iptables –A INPUT –i eth0<br />
� -j或--jump 指定原則的目標與處理動作<br />
� iptables –A INPUT –i eth0 –p tcp –dport 20 –j ACCEPT<br />
� -o,--out-interface,-p,--protocol,-s,--source…etc<br />
51
5.3.4 Target 目標<br />
� 若少了這個選項,此原則就形成虛設,且必須使用大寫來<br />
指定原則的目標。<br />
� ACCEPT 允許<br />
� iptables –I INPUT 1 –dport 80 –j ACCEPT<br />
� DROP 丟棄<br />
� iptables –D INPUT –dport 80 –j DROP<br />
� RETURN 跳離目前的鏈<br />
� iptables –t nat –A PREROUTING –I eth0 –p icmp –j<br />
RETURN<br />
� QUEUE 重導至本機的佇列中<br />
� iptables –t nat –A OUTPUT –j QUEUE<br />
52
6. Firewall 測試<br />
� 6.1 White Box Test設計的角度<br />
� 6.2 Black Box Test使用的角度<br />
� 6.3 實務測試<br />
53
6.1 White Box Test<br />
� 以設計為主要觀點的白盒子測試,通常強調防火牆系<br />
統的整體設計,且具有其一定的假設情況和設計時的<br />
基準網路環境。<br />
� 從設計的角度測試防火牆系統,得要先知道防火牆的<br />
設計原理和設計時的假設等因素,才能做到比較實際<br />
的測試工作。<br />
54
6.2 Black Box Test<br />
� 黑盒子測試則是不管防火牆內部系統是如何設計的,<br />
只要試圖從外面闖入防火牆,看看是否可以將這非法<br />
闖入的測試阻檔在門外,也就是說它從使用者的角度<br />
著手去測試,不管它是如何建造的,只要能防火就<br />
好。<br />
� 黑盒子測試的進行通常會先列出測試的工作清單,如<br />
所有已知的安全漏洞,然後根據清單一項一項地去執<br />
行安全的測試工作。<br />
� 這種黑盒子的測試工作,可以確認防火牆系統或產品<br />
安裝和組態設定的正確性,並偵測出防火牆是否可以<br />
防禦已知的安全漏洞。<br />
55
6.3 實務測試:<br />
� TEST 1:防火牆建置與檢視基本規則<br />
56
6.3 實務測試:<br />
� TEST 2:IPtable防火牆自定規則、指令測試<br />
57
6.3 實務測試:<br />
� TEST 3:使用webmin設定IPtable防火牆<br />
58
6.3 實務測試:<br />
� TEST 4:IPtable防火牆port scan<br />
59
實務測試:[作業]<br />
60
實務測試:[作業]<br />
作業1:解決eMule/eDonkey傳檔過慢的問題<br />
一般NAT後面的eMule/eDonkey使用時,會因伺服器<br />
無法連到區域網路內用戶端的TCP4662及UDP4672埠<br />
(預設),會導致用戶端顯示低-ID,而導致下載速度變慢<br />
作業2:解決VNC與pcAnywhere無法連線的問題<br />
由於被遙控的遠端電腦位於私有IP裡,造成無法使用<br />
VNC(port 5900 預設)、pcAnywhere(port 5631、5632 預設)<br />
61
實務測試:[作業]<br />
作業3:解決外面查詢不到DNS伺服器的問題<br />
一般使用NAT架設DNS伺服器常會遇到的問題<br />
作業4:阻擋即時通訊軟體<br />
公司裡,老闆不希望員工上班時間聊天或洩漏公<br />
司商業機密,因此將MSN阻擋。<br />
作業5:阻擋P2P軟體<br />
62
7. 研伸閱讀與進階研究:<br />
� FIREWALLS AND INTERNET SECURITY:REPELLING THE WILY<br />
HACKER,2nd Edition, William R. Cheswick, Steven M. Bellovin, Aviel D.<br />
Rubin<br />
� A Quantitative Study of Firewall Configuration Errors<br />
Wool, A.; Computer , Volume: 37 , Issue: 6 , June 2004 Pages:62 - 67<br />
� Firewalls: an outdated defense<br />
Arbaugh, W.A.; Computer , Volume: 36 , Issue: 6 , June 2003 Pages:112 –<br />
113<br />
� Compiling policy descriptions into reconfigurable firewall processors<br />
Lee, T.K.; Yusuf, S.; Luk, W.; Sloman, M.; Lupu, E.; Dulay, N.;<br />
Field-Programmable Custom Computing Machines, 2003. FCCM 2003.<br />
11th Annual IEEE Symposium on , 9-11 April 2003 Pages:39 – 48<br />
� Implementation of a content-scanning module for an Internet firewall<br />
Moscola, J.; Lockwood, J.; Loui, R.P.; Pachos, M.;<br />
Field-Programmable Custom Computing Machines, 2003. FCCM 2003.<br />
11th Annual IEEE Symposium on , 9-11 April 2003 Pages:31 - 38<br />
63
Enhanced Security Tools: IDS<br />
� What is Intrusion Detection System<br />
� Model and Architecture<br />
� Data Source<br />
� Core technology<br />
� 產品介紹<br />
� Metric and Testing methodology<br />
� Testing Environment and Test reports<br />
� Development methodology: A software-engineering<br />
viewpoint<br />
� Other topics<br />
64
IDS in a Network: NIDS, HIDS, A-IDS<br />
65
Host Intrusion detection system (HIDS)<br />
66
Portsentry/Linux<br />
67
Intrusion Detection System: History<br />
資料來源:http://www.securityfocus.com/infocus/1514<br />
68
Model & Architecture<br />
DENNING’S IDS Model:<br />
Denning, D. E., "An Intrusion-Detection Model,"IEEE Transactions on<br />
Software Engineering, vol. 13, pp. 222-232, 1987.<br />
Hypothesis::<br />
exploitation of a system's vulnerabilities involves abnormal use of<br />
the system; therefore, security violations could be detected from<br />
abnormal patterns of system usage.<br />
The model is independent of any particular system, application<br />
environment, system vulnerability, or type of intrusion, thereby<br />
providing a framework for a general-purpose intrusion-detection<br />
expert system.<br />
69
Six main components<br />
� Subjects: Initiators of activity on a target system- normally users.<br />
� Objects: Resources managed by the system-files, commands,<br />
devices, etc.<br />
� Audit records: Generated by the target system in response to<br />
actions performed or attempted by subjects on objects-user login,<br />
command execution, file access, etc.<br />
� Profiles: Structures that characterize the behavior of subjects with<br />
respect to objects in terms of statistical metrics and models of<br />
observed activity. Profiles are automatically generated and initialized<br />
from templates.<br />
� Anomaly records: Generated when abnormal behavior is detected.<br />
� Activity rules: Actions taken when some condition is satisfied, which<br />
update profiles, detect abnormal behavior, relate anomalies to<br />
suspected intrusions, and produce reports.<br />
70
IDS 的標準化<br />
� Common Intrusion Detection Framework<br />
(CIDF)<br />
� Intrusion Detection Working Group<br />
(IDWG)<br />
� 隸屬於IETF (Internet Engineering Task Force)<br />
� The Intrusion Detection Message<br />
Exchange Format<br />
� draft-ietf-idwg-idmef-xml-14(January 27, 2005 )<br />
71
Intrusion Detection Working Group<br />
(IDWG) http://www.ietf.org/html.charters/idwg-charter.html<br />
72
IDWG<br />
1.A requirements document, which describes the high-level<br />
functional requirements for communication between<br />
intrusion detection systems and requirements for<br />
communication between intrusion detection systems and<br />
with management systems, including the rationale for those<br />
requirements. Scenarios will be used to illustrate the<br />
requirements.<br />
2. A common intrusion language specification, which<br />
describes data formats that satisfy the requirements.<br />
3. A framework document, which identifies existing protocols<br />
best used for communication between intrusion detection<br />
systems, and describes how the devised data formats<br />
relate to them.<br />
73
IDWG Documents<br />
74
The Intrusion Detection Message<br />
Exchange Format<br />
� The purpose of the Intrusion Detection<br />
Message Exchange Format (IDMEF) is<br />
to define data formats and exchange<br />
procedures for sharing information of<br />
interest to intrusion detection and<br />
response systems, and to the<br />
management systems which may need<br />
to interact with them.<br />
75
The Intrusion Detection<br />
Exchange Protocol (IDXP)<br />
� IDXP is specified, in part, as a Blocks Extensible Exchange<br />
Protocol (BEEP) "profile". BEEP is a generic application protocol<br />
framework for connection-oriented, asynchronous interactions.<br />
Features such as authentication and confidentiality are provided<br />
through the use of other BEEP profiles. Accordingly, many<br />
aspects of IDXP (e.g., confidentiality) are provided within the<br />
BEEP framework.<br />
� IDXP provides for the exchange of IDMEF messages,<br />
unstructured text, and binary data between intrusion detection<br />
entities. Addressing the security-sensitive nature of exchanges<br />
between intrusion detection entities, underlying BEEP security<br />
profiles should be used to offer IDXP the required set of security<br />
properties.<br />
� The Intrusion Detection Exchange Protocol (IDXP)<br />
� draft-ietf-idwg-beep-idxp-07(October 22, 2002)<br />
76
Data Source<br />
1.Audit log::<br />
SUN Solaris/BSM(Basic security Module)<br />
WINDOWS/Event log<br />
System log� Linux/*BSD::syslog<br />
App. Log� too many,…..<br />
2.Network packet flow<br />
3.Windows registry:only for Windows<br />
Frank Apap, Andrew Honig, Shlomo Hershkop, Eleazar Eskin, and Sal<br />
Stolfo<br />
(Columbia University), RAID 2002, LNCS 2516, pp. 36–53, 2002.<br />
……<br />
77
Data source(1): WINDOWS/Event Log<br />
78
Data source(2): NETWORK Packets<br />
79
Data source(3): Windows registry<br />
80
Core technology:Anomaly detection vs<br />
Misuse detection<br />
Anomaly detectors:<br />
(1)identify abnormal unusual behavior (anomalies) on a host<br />
or network.<br />
(2)Assumption:attacks are different from “normal” (legitimate)<br />
activity and can therefore be detected by systems that<br />
identify these differences.<br />
(3)Anomaly detectors construct profiles representing normal<br />
behavior of users, hosts, or network connections. These<br />
profiles are constructed from historical data collected over<br />
a period of normal operation. The detectors then collect<br />
event data and use a variety of measures to determine<br />
when monitored activity deviates from the norm.<br />
82
Anomaly detection<br />
� statistical methods::(NIDES,…)<br />
� Rule induction::(ASAX,..)<br />
� (artificial) neural networks::(many,…C.S.Laih)<br />
� fuzzy set theory::(T.Y.Lin1994)<br />
� machine learning algorithms(Lane, Brodley1997,)<br />
� artificial immune systems::(Forrest, Hofmeyr,..)<br />
� signal processing methods<br />
� temporal sequence learning::(Lane, Brodley1999)<br />
� Data mining::(W.Lee..)……..<br />
83
Misuse detectors<br />
(1)analyze system activity, looking for events or sets of events<br />
that match a predefined pattern of events that describe a<br />
known attack.<br />
(2)“signature-based detection.”<br />
The most common form of misuse detection used in<br />
commercial products specifies each pattern of events<br />
corresponding to an attack as a separate signature.<br />
(3)Technique:<br />
� Expert System::<br />
� “state-based” analysis techniques<br />
� Genetic algorithm::(GASSATA1998,..)<br />
� …………………………..<br />
84
IDS Product<br />
� AXENT (acquired by Symantec): Enterprise Security Manager(HVAT),<br />
NetRecon(NVAT); Intruder Alert(HIDS), NetProwler(NIDS)<br />
� CyberSafe: Centrax(Hybrid-IDS with basic VAT)<br />
� Cisco Systems: Cisco Secure Scanner(NVAT, formerly NetSonar); Cisco Secure<br />
IDS(NIDS, formerly Netranger)<br />
� Intrusion.com: SecureNet Pro(NIDS), Kane Security Enterprise(HIDS);<br />
SecurityAnalyst(Hybrid VAT)<br />
� Internet Security Systems(ISS): RealSecure(Hybrid IDS); Internet<br />
Scanner(NVAT), System Scanner(HVAT)<br />
� Network ICE; BlackICE Defender(HIDS)<br />
� Network Flight Recorder; NFR(NIDS)<br />
� Network Security Wizards (acquired by Enterasys Networks): Dragon<br />
Sensor(NIDS), Dragon Squire(HIDS), Dragon Server(Management)<br />
� PGP Security (acquired by Network Associates): CyberCop Scanner(HVAT);<br />
CyberCop Monitor(Hybrid IDS); CyberCop Sting(Honeypot),<br />
� Tripwire: TripWire(Host-based File Integrity Assessment Tool)<br />
85
Testing Environment and Test reports<br />
� Mitre(1997):Netranger, Realsecure, ASIM<br />
� Information Warfare Conf.(1998):<br />
Realsecure, NFR<br />
� MIT/Lincoln Labs(1998/1999): DARPA-funded<br />
� SANS 2000 ID-NET(2000.3):Intrusiondetection-focused<br />
conf.<br />
� ……………………………..<br />
86
•1998 DARPA Intrusion Detection Evaluation<br />
•1999 DARPA Intrusion Detection Evaluation<br />
87
1998 DARPA Intrusion Detection Evaluation<br />
Simulation Network for Off-line Off line Evaluation<br />
Ultra Ultra<br />
486 Sparc<br />
P2 Sparc<br />
P2<br />
P2<br />
Solaris 2.5.1<br />
Simulation<br />
Linux 2.0.27 SunOS 4.1.4 Solaris 2.5.1<br />
Status Target Machines<br />
Locke<br />
172.16.112.10<br />
dm: last modified 3/24/98<br />
= Pentium II pcs running modified Linux kernel (based on 2.0.32)<br />
which allows these machines to spoof many different ip addresses<br />
Marx<br />
172.16.114.50<br />
“Inside Inside”<br />
172.16 => eyrie.af.mil<br />
Zeno<br />
172.16.113.50<br />
Pascal<br />
172.16.112.50<br />
Inside<br />
Traffic<br />
Generator<br />
Hobbes<br />
172.16.112.20<br />
Ethernet Hub Info<br />
A: AsanteHub 1012 (no ip)<br />
B: HP EtherTwist Hub PLUS (ip = 192.168.1.5)<br />
hub hub<br />
Router<br />
Cisco<br />
A AGS+ B<br />
88<br />
SunOS 5.6<br />
Sniffer<br />
Solomon<br />
192.168.1.90<br />
Router Interface Info<br />
A: 172.16.112.1<br />
B: 198.168.1.1<br />
“Outside Outside”<br />
192.168.1 => world.net<br />
194.27.251 => plum.net<br />
197.218.177 => grape.mil<br />
(plus all other domains used)<br />
Outside<br />
Traffic<br />
Generator<br />
Calvin<br />
192.168.1.10<br />
MIT Lincoln Laboratory<br />
Web<br />
Server<br />
Aesop<br />
192.168.1.20
�<br />
89
1998 Training Data Attack<br />
90
1998 Anomaly Training Data<br />
The simulation featured<br />
6 users whose activity<br />
can be used to test<br />
anomaly detection systems.<br />
91
Test the following types of misuse<br />
1. Denial of service<br />
2. Unauthorized access from a remote machine<br />
3. Unauthorized transition to root by an<br />
unprivileged user<br />
4. Surveillance and probing<br />
5. Anomalous user behavior<br />
92
aesop<br />
192.168.1.20<br />
Web Server<br />
Linux Linux<br />
attacker<br />
1999 DARPA Intrusion Detection<br />
Evaluation::Simulation Network 99<br />
calvin<br />
192.168.1.10<br />
Gateway<br />
attacker<br />
solomon<br />
192.168.1.90<br />
Sniffer<br />
Linux Linux NT<br />
Cisco 2514<br />
Router<br />
CISCO<br />
192.168.1.1 172.16.0.1<br />
HP HP<br />
locke<br />
172.16.112.10<br />
Sniffer<br />
plato<br />
SunOS MacOS 192.168.1.2 172.16.112.5 SunOS Linux Solaris SunOS Linux NT Win98<br />
NT<br />
attacker<br />
monitor<br />
192.168.1.30<br />
SNMP Monitor<br />
Virtual Outside<br />
Hosts<br />
. . .<br />
attacker<br />
hobbes<br />
172.16.112.20<br />
Gateway<br />
attacker<br />
pascal<br />
172.16.112.50<br />
Victim<br />
zeno<br />
172.16.113.50<br />
Victim<br />
. . .<br />
Virtual Inside<br />
Hosts<br />
marx<br />
172.16.114.50<br />
Victim<br />
NT 98<br />
hume<br />
172.16.112.100<br />
Victim<br />
Ethernet Hub<br />
Router<br />
kant<br />
172.16.112.110<br />
Victim
批判性文章:<br />
DARPA Intrusion Detection Evaluation<br />
� John McHugh:(2000)ACM TISSEC會議<br />
發表厚達33頁的批判性文章<br />
� Philip K. Chan(Florida Institute of Technology)<br />
and Matthew V. Mahoney<br />
An Analysis of the 1999 DARPA/Lincoln Laboratory Evaluation<br />
Data for Network Anomaly Detection<br />
RAID2003<br />
96
研伸閱讀與進階研究:IDS/IDP<br />
� A fast pattern matching algorithm for network processor-based intrusion<br />
detection system<br />
Rong-Tai Liu; Nen-Fu Huang; Chia-Nan Kao; Chih-Hao Chen;<br />
Performance, Computing, and Communications, 2004 IEEE International<br />
Conference on , April 15-17, 2004 Pages:271 – 276<br />
� Intrusion detection in wireless ad hoc networks<br />
Mishra, A.; Nadkarni, K.; Patcha, A.;<br />
Wireless Communications, IEEE [see also IEEE Personal<br />
Communications] , Volume: 11 , Issue: 1 , Feb. 2004 Pages:48 - 60<br />
� Intrusion sensor data fusion in an intelligent intrusion detection system<br />
architecture<br />
Siraj, A.; Vaughn, R.B.; Bridges, S.M.;<br />
System Sciences, 2004. Proceedings of the 37th Annual Hawaii International<br />
Conference on , 5-8 Jan. 2004 Pages:279 - 288<br />
� Indra: a peer-to-peer approach to network intrusion detection and prevention<br />
Janakiraman, R.; Waldvogel, M.; Qi Zhang;<br />
Enabling Technologies: Infrastructure for Collaborative Enterprises, 2003. WET<br />
ICE 2003. Proceedings. Twelfth IEEE International Workshops on , 9-11 June<br />
2003<br />
97<br />
Pages:226 - 231
Snort介紹<br />
� Network-Based IDS<br />
� Three main modes<br />
1) Sniffer Mode<br />
2) Packet Logger Mode<br />
3) Network Intrusion Detection Mode<br />
� NIDS Mode : snort.conf<br />
1) Set the network variables for your network<br />
2) Configure preprocessors<br />
3) Configure output plugins<br />
4) Customize your rule set<br />
Command: snort -c snort.conf<br />
98
NIDS Mode運作流程<br />
99
Snort架構<br />
100
IDS測試<br />
� TEST 1: SNORT安裝與基本執行測試<br />
Sniffer Mode 、 Packet Logger Mode 、<br />
Network Intrusion Detection Mode<br />
� TEST 2: Scanning Attack偵測測試<br />
Nmap Scan<br />
� TEST 3: Buffer Overflow Attack偵測測試<br />
微軟安全性公告MS04011:LSASS服務存在<br />
Buffer Overflow漏洞<br />
� TEST 4: Snort rule新增與實測<br />
針對HTTP存取設計一規則<br />
101
TEST 2:<br />
IDS測試<br />
10.0.0.1<br />
192.168.24.1 192.168.25.1<br />
192.168.24.2<br />
TEST 3:<br />
TEST 4:<br />
10.0.0.2<br />
102<br />
192.168.25.2
Enhanced Security Tools: VPN<br />
� What Is VPN?<br />
� VPN 應用<br />
� VPN 技術<br />
� VPN 產品介紹<br />
� VPN 建置實例<br />
103
Virtual Private Networks<br />
� Virtual Private Networks可以實現將不同<br />
網域的電腦設為相同網域,使之間相互<br />
連接。<br />
� 構建加密通道,並提供與專用網路一樣<br />
的虛擬專用網路能夠利用Internet或其它<br />
安全和功能保障。<br />
104
何謂VPN(Virtual Private Networks)?<br />
傳統與現今私有網路的比較<br />
傳統的私有網路方式是使用P-to-P網路連線<br />
VPNs (虛擬私有網路)<br />
A企業 T3 專線<br />
B企業<br />
VPN連線<br />
105<br />
Internet<br />
C企業 D企業
VPN的成長<br />
106
VPN 應用:<br />
通過Internet達到遠端訪問<br />
107
通過Internet達到遠端內部主機訪問<br />
108
通過區域網路與伺服器達到私有<br />
連線<br />
109
通過區域網路進行內部VPN<br />
110
VPN 技術:通道技術<br />
� CPE (Customer Premises Equipment) -<br />
Based VPN協定可分為<br />
� 通道技術<br />
� Layer 2: PPTP、L2TP<br />
� Layer 3: IPsec<br />
� Layer 5: SOCKS v5<br />
� 安全技術<br />
� Network-based VPN<br />
111
驗證方式<br />
� PAP<br />
� PAP是一種簡單的公開驗證方式。要求用戶提供用戶名稱和密碼,<br />
PAP以公開方式回覆用戶資訊。<br />
� CHAP<br />
� CHAP 通過使用 MD5(文件的數字簽名) 來協商的一種加密身份驗證<br />
之安全形式<br />
� MS-CHAP<br />
� 由微軟開發,為了對遠端 Windows 工作站進行身份驗證<br />
� MS-CHAP v2<br />
� 第二版的質詢握手身份驗證協議,支援在用戶端和伺服器之間進行<br />
相互驗證 。<br />
� EAP<br />
� 由IETF所提出可延伸驗證通訊協定,允許連接使用任意方式對PPP連<br />
接的有效性進行驗證。<br />
� SSL<br />
� Secure Sockets Layer Protocol,是基於公開金鑰和對稱金鑰加密,<br />
以及數位簽名和認證的技術。<br />
112
點到點通道協議 –PPTP(Point-to-<br />
Point Tunneling Protocol )<br />
� 內建的通道通訊協定<br />
� LAN-to-LAN以及遠端存取的VPN<br />
� 採用PPP協議(PAP、 CHAP、 MS-<br />
CHAP )<br />
� EAP(可延伸驗證通訊協定 )憑證(可有可<br />
無)<br />
� 相容性問題<br />
113
PPTP 封包<br />
資料連結標頭<br />
GRE 標頭<br />
PPP 標頭<br />
IP 標頭<br />
加密的 PPP 資料(IP、IPX、NetBEUI)<br />
114
第二層通道協議 -L2TP(Layer<br />
Two Tunneling Protocol )<br />
� L2TP是國際標準隧道協議,它結合了PPTP協議<br />
� 第二層轉發L2F協議的優點,能以隧道模式使PPP<br />
� L2TP沒有任何加密措施<br />
� 趨勢是將L2TP和IPSec結合起來: 用L2TP部分VPN採用這<br />
類技術<br />
115
L2TP Message Header<br />
116
IPSec協議<br />
� 在Layer 3網路層<br />
� 將二台電腦之間傳送的所有資料加密,提供訊息的機密性<br />
� 提供二台電腦之間訊息的完整性 (不加密資料)<br />
� 提供二台電腦之間的相互驗證<br />
� 限制能夠相互通信的電腦<br />
� IPsec的封裝機制<br />
� Transport mode:host-to-host<br />
� Tunnel mode:gateway-to-[host/gateway]<br />
117
IPSec Between Host<br />
118
Tunnel Mode<br />
119
SOCKS v5<br />
� 工作在OSI(Open System Internet)模型中<br />
的第五層<br />
� 優勢在於訪問控制<br />
� 能同低層協議<br />
� 必須制定更複雜的安全管理策略<br />
120
四種通道技術在OSI七層模型的位置<br />
121
VPN標準<br />
� 目前VPN標準是以IETF制定的IPSec(Internet<br />
Protocol Security)為主,它是將密碼學的技術應用在<br />
網路層IPv4及IPv6上的一種標準,可保護IP資料封包<br />
的安全,並達到網路層(Network Layer)中的安全通<br />
訊。IPSec協定主要包括以下三種:<br />
� AH(Authentication Header):可為IP封包提供資料完整<br />
性、資料原始身分認證和抗重送攻擊(Anti-replay)等安全服<br />
務。<br />
� ESP(Encapsulation Security Payload):可為IP封包提供<br />
機密性、資料來源身分認證、抗重送攻擊以及資料完整性等<br />
安全服務。<br />
� IKE(Internet Key Exchange):可協商程序為IPSec產生金<br />
鑰。IKE是在IPSec通信雙方之間,建立起SA,並維護更新<br />
SAD(Security Association Database)。<br />
122
VPN 產品介紹<br />
� 硬體式的VPN VS. 軟體式的VPN<br />
� 昱德科技股份有限公司<br />
� RideWay Station / MCT<br />
� RideWay Station / SOHO10<br />
� 友冠資訊<br />
� NetScreen Secure Access SSL VPN<br />
� Cisco<br />
� IPSEC IOS & IOS FIREWALL<br />
� Cisco VPN 3000 Concentrator<br />
� CISCO PIX 500 SERIES FIREWALLS<br />
� ASI<br />
� Filanet InterJak200<br />
123
軟體式的VPN產品<br />
� 賽門鐵克Enterprise VPN<br />
� Cisco Security & VPN Software<br />
� FreeSwan<br />
� CIPE<br />
� OpenVPN<br />
� 宏碁 UU100<br />
� SonicWALL Global VPN Client<br />
� 美國趨勢科技 VPN-1 SecureClient<br />
124
產品說明<br />
� Cisco VPN 3000 Concentrator<br />
� 提供的VPN連接技術包括 IPSec、 PPTP、結合IPSec的L2TP和Cisco的<br />
WebVPN。<br />
� CISCO PIX 500 SERIES FIREWALLS<br />
� 支援各式各樣的遠程訪問VPN Client,包括Cisco軟體VPN Client(關於很多<br />
政綱包括微軟公司Window、 Linux、Solaris 和Apple OS X) 、 Cisco硬體<br />
VPN Client,在Microsoft Windows. 系統裡提供Point-to-Point Tunneling<br />
Protocol 與 Layer 2 Tunneling Protocol clients。<br />
� NetScreen Secure Access SSL VPN<br />
� 產品的應用層安全閘道具有新的存取管理功能,包括以表單(forms)與標頭<br />
(header)為基礎之網路單一簽入(single sign-on;SSO)、密碼管理整合<br />
以及跨企業線上會議的功能等。這也使得NetScreen除了在現有的遠端存取<br />
安全、IPSec VPN、防火牆、入侵偵測與防護系統市場外,進一步開拓新業<br />
務範疇。<br />
� FreeSwan<br />
� FreeS/WAN是目前口碑最好的VPN軟體,支援IPSsec,可以設定多個<br />
tunnel,對不同的destination的packet 做不同的加密工作。<br />
� OpenVPN<br />
� 使用的是最先進的SLL技術,比其他IPsec的VPN更加安全<br />
125
VPN 建置與測試:環境配置<br />
126
VPN基本要求<br />
� 用戶驗證<br />
VPN必須能夠驗證用戶名稱,顯示何人在何時的身份並<br />
嚴格控制只有授權用戶才能訪問了何種資訊。<br />
� 地址管理<br />
VPN方案必須能夠為用戶分配專用網路上的位址並確保<br />
位址的安全性。<br />
� 數據加密<br />
對通過Internet傳遞的資料必須經過加密,確保網路其他<br />
未授權的用戶無法讀取該資訊。<br />
� 密鑰管理<br />
VPN必須建立並更新用戶端和伺服器的加密密碼。<br />
127
配置內容<br />
� 將內部網路分為三個網段<br />
� VPN Server同時具備Router、防火牆功能<br />
� DNZ 具備網域控制站、「網域名稱系統 (DNS)」<br />
伺服器、「動態主機設定通訊協定 (DHCP)」伺服<br />
器及憑證授權單位 (CA)、「遠端驗證撥入使用者<br />
服務 (RADIUS)」伺服器、Web 與檔案伺服器(IIS)<br />
� Client為企業內部網路的一台電腦<br />
128
實驗目的<br />
� 正常連線至企業時,能瀏覽企業網站(不<br />
能存取企業內部網路資源)。<br />
� 以VPN連線至企業時,不僅能瀏覽企業<br />
網站,更能夠存取企業內部網路資源。<br />
129
Route print<br />
130
實務測試:<br />
� TEST 1:<br />
路由對路由 PPTP VPN架設與連線測試<br />
� TEST 2:<br />
區域網路PPTP VPN架設與連線測試<br />
� TEST 3:<br />
NAT 與 PPTP 結合的VPN架設與連線測<br />
試(Point-to-Router )<br />
131
延伸閱讀與進階研究:VPN<br />
� Making the Gigabit IPsec VPN Architecture Secure<br />
Friend, R.;<br />
Computer , Volume: 37 , Issue: 6 , June 2004<br />
Pages:54 - 60<br />
� Virtual private network services: scenarios, requirements<br />
and architectural constructs from a standardization<br />
perspective<br />
Carugi, M.; De Clercq, J.;<br />
Communications Magazine, IEEE , Volume: 42 , Issue: 6 , June<br />
2004<br />
Pages:116 - 122<br />
� Kory Hamzeh、Gurdeep Singh Pall、William Verthein、Jeff<br />
Taarud、and W. Andrew Little,“Point-to-Point Tunneling<br />
Protocol (PPTP)”, IETF RFC 2637, July 1999.<br />
� RUN!PC 2004年2月號 特企專欄-2004資安研討會資安技術篇<br />
132
Enterprise Security Testing<br />
:Vulnerability Scanner(弱點掃描)<br />
� 網路安全的防護策略<br />
-防火牆(Firewall)、入侵偵測/防護(IDS/IDP)<br />
� 自行主動找出安全漏洞並修補<br />
-弱點掃描<br />
� 降低風險<br />
-進行漏洞修補<br />
駭客也會善用弱點掃描偵測系統<br />
133
Why:為何需要弱點掃描器<br />
What<br />
Security scanner=<br />
Integrate all available tools into a<br />
All_in_one supertools.<br />
Why:For What…<br />
to test your system/environment<br />
or<br />
to learn the attack technique<br />
134
弱點掃描分類<br />
� 主動掃描(Active Scanning)<br />
送出資料至目標機器,收集、分析回傳的訊息來取得目標資訊<br />
� 被動掃描(Passive Scanning)<br />
監看網路封包來取得訊息。<br />
主動掃描 1. 資訊收集快。<br />
2. 較精確。<br />
被動掃描 1. 資訊收集慢。<br />
被動掃描的遠景:<br />
優點 缺點<br />
2. 目標無網路流量時,<br />
便無法獲得訊息。<br />
135<br />
1. 很難掩蓋紀錄。<br />
2. 越來越多目標受到防火牆<br />
的保護。<br />
1. 隱密性高。<br />
發展新的演算法,提高被動掃描的速度和正確性。<br />
部分新演算法的發展,使用正常方式使目標產生流量。<br />
2. 不會受到防火牆的影響。
Commercial Vulnerability Scanning Tools<br />
產品 網站<br />
ISS Internet Scanner www.iss.net<br />
Retina www.eEye.com<br />
FoundScan www.foundstone.com<br />
QualysGuard Intranet<br />
Scanner<br />
136<br />
www.qualys.com<br />
Typhon II www.nextgenss.com
Retina security scanner<br />
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
N-Stealth: Web scanner<br />
158
159
160
161
162
163
164
165
Enterprise Security Testing<br />
:Penetration Test<br />
� Penetration Test:<br />
透過模擬駭客方式的入侵模式,測試你的資訊系<br />
統架構的安全強度。與駭客攻擊最大不同在於<br />
滲透測試在測試完後會產生一份報告說明安全<br />
程度,主機並不會遭受破壞,而駭客攻擊則相<br />
反。<br />
� Vulnerability Scanning:<br />
漏洞掃描是由內部去掃描內部主機的漏洞,與<br />
滲透測試的外部不同。<br />
166
OSSTMM<br />
167
Digital forensic analysis : the goal<br />
� is to identify digital evidence for an<br />
investigation. An investigation typically uses<br />
both physical and digital evidence with the<br />
scientific method to draw conclusions.<br />
Examples of investigations that use digital<br />
forensics include computer intrusion,<br />
unauthorized use of corporate computers,<br />
child pornography, and any physical crime<br />
whose suspect had a computer.<br />
168
What about “Forensics”?<br />
� “Relating to the use of science or<br />
technology in the investigation and<br />
establishment of facts or evidence in a<br />
court of law”<br />
� American Heritage Dictionary<br />
� Digital Investigation vs. Digital Forensic<br />
Investigation: The legal requirements<br />
169
Digital Forensic Investigation<br />
A process that uses science and<br />
technology to examine digital objects<br />
and that develops and tests theories,<br />
which can be entered into a court of law,<br />
to answer questions about events that<br />
occurred.<br />
170
Digital Forensic Science<br />
� The use of scientifically derived and proven<br />
methods toward the preservation, collection,<br />
validation, identification, analysis,<br />
interpretation, documentation and<br />
presentation of digital evidence derived from<br />
digital sources for the purpose of facilitating<br />
or furthering the reconstruction of events<br />
found to be criminal, or helping to anticipate<br />
unauthorized actions shown to be disruptive<br />
to planned operations.<br />
Gary Palmer, A Road Map for Digital Forensic Research. Technical<br />
Report DTR-T0010-01, DFRWS, November 2001. Report from the First<br />
Digital Forensic Research Workshop (DFRWS).<br />
171
http://www.e-evidence.info/b.html<br />
172
173
174
175
http://www.ijde.org/ [2002]<br />
176
Computer Forensics Tool Testing<br />
(CFTT) Project<br />
177
The Big Picture<br />
An Event-based Event based Digital Forensic Investigation<br />
Framework, Brian D. Carrier ,Eugene H. Spafford<br />
178
Digital Crime Scene<br />
Investigation<br />
� Goal: To determine what digital events<br />
occurred by recognizing digital evidence<br />
� Three Phases:<br />
� Crime Scene Preservation & Documentation<br />
� Evidence Search & Documentation<br />
� Event Reconstruction & Documentation<br />
179
Phase 1: Scene Preservation<br />
& Documentation<br />
� Goal: Preserve the state of as many<br />
digital objects as possible and<br />
document the crime scene.<br />
� Methods:<br />
� Shut system down and copy it<br />
� Unplug from network & kill processes<br />
� Do nothing<br />
180
Is it Necessary?<br />
� An investigation does not need preservation<br />
� A forensic investigation may need<br />
preservation<br />
� Are bitwise-images needed?<br />
� Do we take buildings as evidence?<br />
� Legal requirements dictate the technical<br />
requirements of this phase<br />
181
Phase 2:Digital Evidence<br />
Searching and Documentation<br />
� Need to find evidence of events<br />
� Goal: To recognize the digital objects<br />
that may contain information about the<br />
incident and document them.<br />
182
183
Existing Research (1)<br />
� Target definition<br />
� Stallard & Levitt - Automated Analysis for Digital<br />
Forensic Science: Semantic Integrity Checking<br />
� Carrier & Spafford - Defining Searches of Digital<br />
Crime Scenes<br />
� Manually - experience and training<br />
� Stego & malware signatures<br />
� Many others….<br />
184
Existing Research (2)<br />
� Extraction<br />
� All current “forensic” tools<br />
� Carrier - Defining Digital Forensic<br />
Examination and Analysis Tools<br />
� Comparison<br />
� Visual (most tools)<br />
� Equality (keyword searching)<br />
185
Phase 3:Digital Event Reconstruction and<br />
Documentation<br />
� Need to translate evidence into events<br />
� Goal: To determine and document the<br />
events for which evidence exists and<br />
has been collected<br />
� Not currently supported by many tools<br />
186
187
Evidence<br />
Examination<br />
188<br />
Role<br />
Classification
Event Construction Event Sequencing<br />
189
Existing Research<br />
� Carney & Rogers - The Trojan Made Me Do It: A First<br />
Step in Statistical Based Computer Forensics Event<br />
Reconstruction - IJDE<br />
� Carrier & Spafford - Defining Digital Crime Scene<br />
Event Reconstruction - JFS<br />
� Gladyshev & Patel - Finite State Machine Approach<br />
to Digital Event Reconstruction - JDI<br />
� Stephenson - Modeling of Post-Incident Root Cause<br />
Analysis - IJDE<br />
190
作業<br />
� digital forensic analysis of e-mails<br />
� digital forensic analysis of BT,P2P<br />
DIGITAL MUSIC DEVICE FORENSICS<br />
Automated Analysis for Digital Forensic Science<br />
digital forensic and honeypot<br />
Ryan C. Barnett<br />
Using SWATCH for Forensic Analysis of VMware & DD Images(2002)<br />
Monitoring VMware Honeypots<br />
191
延伸閱讀<br />
� Hacking Exposed Computer Forensics,<br />
Chris Davis, Aaron Philipp, David Cowen<br />
McGraw-Hill; (November, 2004)<br />
� Windows Forensics and Incident Recovery<br />
,Harlan Carvey, Addison-Wesley (July 21, 2004)<br />
� File System Forensic Analysis, Brian<br />
Carrier,Addison-Wesley (March 17, 2005)<br />
192