EXECUTIVE SUMMIT & ROUNDTABLE 2009 - MIS Training
EXECUTIVE SUMMIT & ROUNDTABLE 2009 - MIS Training
EXECUTIVE SUMMIT & ROUNDTABLE 2009 - MIS Training
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
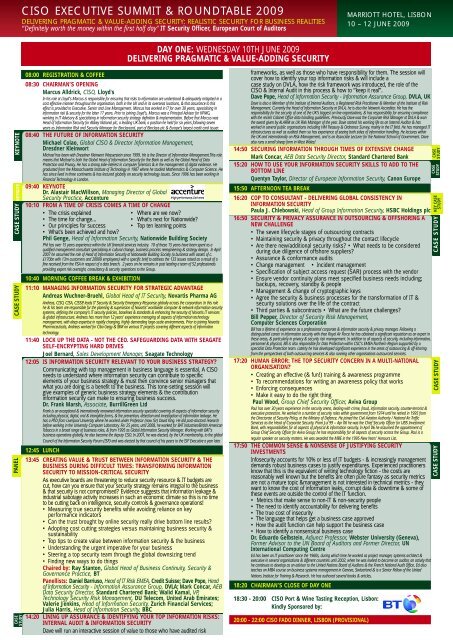
CISO <strong>EXECUTIVE</strong> <strong>SUMMIT</strong> & <strong>ROUNDTABLE</strong> <strong>2009</strong><br />
DELIVERING PRAGMATIC & VALUE-ADDING SECURITY: REALISTIC SECURITY FOR BUSINESS REALITIES<br />
“Definitely worth the money within the first half day" IT Security Officer, European Court of Auditors<br />
MARRIOTT HOTEL, LISBON<br />
10 – 12 JUNE <strong>2009</strong><br />
DAY ONE: WEDNESDAY 10TH JUNE <strong>2009</strong><br />
DELIVERING PRAGMATIC & VALUE-ADDING SECURITY<br />
KEYNOTE<br />
CASE STUDY KEYNOTE<br />
CASE STUDY<br />
PANEL<br />
CASE<br />
STUDY<br />
08:00 REGISTRATION & COFFEE<br />
08:30 CHAIRMAN’S OPENING<br />
Marcus Alldrick, CISO, Lloyd's<br />
In his role at Lloyd’s Marcus is responsible for ensuring that risks to information are understood & adequately mitigated in a<br />
cost effective manner throughout the organisation, both in the UK and in its overseas locations, & that assurance to this<br />
effect is provided to Executive, Senior and Line Management. Marcus has worked in IT for over 30 years, specialising in<br />
information risk & security for the latter 17 years. Prior to joining Lloyd’s, Marcus was a Principal Advisor for KPMG,<br />
working in IT Advisory & specialising in information security strategy definition & implementation. Before that Marcus was<br />
Head of Information Security for Abbey National plc, a leading UK bank, a position he held for six years following seven<br />
years as Information Risk and Security Manager for Barclaycard, part of Barclays plc & Europe’s largest credit card issuer.<br />
08:40 THE FUTURE OF INFORMATION SECURITY<br />
Michael Colao, Global CISO & Director Information Management,<br />
Dresdner Kleinwort<br />
Michael has been with Dresdner Kleinwort Wasserstein since 1999. He is the Director of Information Management.This role<br />
means that Michael is both the Global Head of Information Security for the Bank as well as the Global Head of Data<br />
Protection and Privacy. He has a strong side-interest in computer forensics & in the management of digital evidence. He<br />
graduated from the Massachusetts Institute of Technology in 1987 where he studied Mathematics & Computer Science. He<br />
has since lived in three continents & has lectured globally on security technology issues. Since 1996 has been working in<br />
Financial Technology in London.<br />
09:40 KEYNOTE<br />
Dr. Alastair MacWillson, Managing Director of Global<br />
Security Practice, Accenture<br />
10:10 FROM A TIME OF CRISIS COMES A TIME OF CHANGE<br />
• The crisis explained<br />
• Where are we now?<br />
• The time for change...<br />
• What's next for Nationwide?<br />
• Our principles for success • Top ten learning points<br />
• What's been achieved and how?<br />
Phil Genge, Head of Information Security, Nationwide Building Society<br />
Phil has over 15 years experience within the UK financial services industry. 10 of these 15 years have been spent as a<br />
qualified management consultant specialising in cultural change, business process reengineering & strategy design. In April<br />
2007 he assumed the role of Head of Information Security at Nationwide Building Society (a business with assets of c.<br />
£170bn with 13m customers and 20000 employees) with a specific brief to address the 133 issues raised as a result of a<br />
fine received from the FSA in respect of a data breach. 2 years on he remains in post leading a team of 52 professionals<br />
providing expert risk oversight, consultancy & security operations to the Group.<br />
10:40 MORNING COFFEE BREAK & EXHIBITION<br />
11:10 MANAGING INFORMATION SECURITY FOR STRATEGIC ADVANTAGE<br />
Andreas Wuchner-Bruehl, Global Head of IT Security, Novartis Pharma AG<br />
Andreas, CISO, CISA, CISSP, leads IT Security & Security Emergency Response globally across the corporation. In this role<br />
he & his team are responsible for the planning & supervision of Novartis’ worldwide computer & network information security<br />
systems, defining the company’s IT security policies, baselines & standards & enhancing the security of Novartis IT services<br />
& global infrastructure. Andreas has more than 12 years’ experience managing all aspects of information technology<br />
management, with deep expertise in rapidly changing, highly demanding large-scale environments. Prior to joining Novartis<br />
Pharmaceuticals, Andreas worked for Ciba Geigy & IBM on various IT projects covering different aspects of information<br />
technology.<br />
11:40 LOCK UP THE DATA - NOT THE CEO. SAFEGUARDING DATA WITH SEAGATE<br />
SELF-ENCRYPTING HARD DRIVES<br />
Joel Bernard, Sales Development Manager, Seagate Technology<br />
12:05 IS INFORMATION SECURITY RELEVANT TO YOUR BUSINESS STRATEGY?<br />
Communicating with top management in business language is essential. A CISO<br />
needs to understand where information security can contribute to specific<br />
elements of your business strategy & must then convince senior managers that<br />
what you are doing is a benefit to the business. This tone-setting session will<br />
give examples of generic business strategy elements & the contribution<br />
information security can make to ensuring business success.<br />
Dr. Frank Marsh, Associate, BurrillGreen Ltd<br />
Frank is an exceptional & internationally renowned information security specialist covering all aspects of information security<br />
including physical, digital, oral & intangible forms, & the prevention, detection and investigation of information leakage. He<br />
has a PhD from Liverpool University where he worked under Professor (now Sir) David King. He did post-doctoral research<br />
before working in the University Computer Laboratory. For 25 years, until 2008, he worked for BAT Industries/British American<br />
Tobacco in a broad range of business roles, & from 1995 as Global Information Security Manager. Working with BAT‘s<br />
business operations globally, he also became the deputy CSO. In 2001, he was elected, by the UK membership, to the global<br />
Council of the Information Security Forum (ISF) and was elected by that council of his peers to the ISF Executive a year later.<br />
12:45 LUNCH<br />
13:45 CREATING VALUE & TRUST BETWEEN INFORMATION SECURITY & THE<br />
BUSINESS DURING DIFFICULT TIMES: TRANSFORMING INFORMATION<br />
SECURITY TO <strong>MIS</strong>SION-CRITICAL SECURITY<br />
As executive boards are threatening to reduce security resource & IT budgets are<br />
cut, how can you ensure that your security strategy remains integral to the business<br />
& that security is not compromised? Evidence suggests that information leakage &<br />
industrial sabotage activity increases in such an economic climate so this is no time<br />
to be cutting back on intelligence, security controls & governance operations!<br />
• Measuring true security benefits while avoiding reliance on key<br />
performance indicators<br />
• Can the trust brought by online security really drive bottom line results?<br />
• Adopting cost cutting strategies versus maintaining business security &<br />
sustainability<br />
• Top tips to create value between information security & the business<br />
• Understanding the urgent imperative for your business<br />
• Steering a top security team through the global downsizing trend<br />
• Finding new ways to do things<br />
Chaired by: Ray Stanton, Global Head of Business Continuity, Security &<br />
Governance Practice, BT<br />
Panellists: Daniel Barriuso, Head of IT Risk EMEA, Credit Suisse; Dave Pope, Head<br />
of Information Security - Information Assurance Group, DVLA; Mark Concar, AEB<br />
Data Security Director, Standard Chartered Bank; Walid Kamal, VP,<br />
Technology Security Risk Management, DU Telecom, United Arab Emirates;<br />
Valerie Jenkins, Head of Information Security, Zurich Financial Services;<br />
Julia Harris, Head of Information Security, BBC<br />
14:20 LINING UP ASSURANCE & IDENTIFYING YOUR TOP INFORMATION RISKS:<br />
INTERNAL AUDIT & INFORMATION SECURITY<br />
Dave will run an interactive session of value to those who have audited risk<br />
frameworks, as well as those who have responsibility for them. The session will<br />
cover how to identify your top information risks & will include a<br />
case study on DVLA, how the risk framework was introduced, the role of the<br />
CISO & Internal Audit in this process & how to “keep it real”.<br />
Dave Pope, Head of Information Security - Information Assurance Group, DVLA, UK<br />
Dave is also a Member of the Institute of Internal Auditors, a Registered Risk Practitioner & Member of the Institute of Risk<br />
Management. Currently the Head of Information Security at DVLA, he is also the Network Accreditor. He has the<br />
responsibility for the security of one of the UK’s biggest on line organisations, & has responsibility for ensuring compliance<br />
with the recent Cabinet Office data handling guidelines. Previously Dave was the Corporate Risk Manager at DVLA & won<br />
the award given by ALARM as UK Risk Manager of the year. Dave started his working life as an Internal Auditor & has<br />
worked in several public organisations including HM Treasury & Ordnance Survey, mainly in the IT field. He has managed IT<br />
infrastructures as well as audited them so has experience of seeing both sides of information handling. He lectures within<br />
the UK and internationally on Risk Management, and is an Associate Lecturer for the National School of Government. Dave<br />
also runs a small sheep farm in West Wales!<br />
14:50 SECURING INFORMATION THROUGH TIMES OF EXTENSIVE CHANGE<br />
Mark Concar, AEB Data Security Director, Standard Chartered Bank<br />
15:20 HOW TO USE YOUR INFORMATION SECURITY SKILLS TO ADD TO THE<br />
BOTTOM LINE<br />
Quentyn Taylor, Director of European Information Security, Canon Europe<br />
15:50 AFTERNOON TEA BREAK<br />
16:20 COP TO CONSULTANT - DELIVERING GLOBAL CONSISTENCY IN<br />
INFORMATION SECURITY<br />
Paula J. Chlebowski, Head of Group Information Security, HSBC Holdings plc<br />
16:50 SECURITY & PRIVACY ASSURANCE IN OUTSOURCING & OFFSHORING A<br />
NEW CHALLENGE<br />
• The seven lifecycle stages of outsourcing contracts<br />
• Maintaining security & privacy throughout the contact lifecycle<br />
• Are there new/additional security risks? • What needs to be considered<br />
during due diligence of offshore suppliers?<br />
• Assurance & conformance audits<br />
• Change management • Incident management<br />
• Specification of subject access request (SAR) process with the vendor<br />
• Ensure vendor continuity plans meet specified business needs including;<br />
backups, recovery, standby & people<br />
• Management & change of cryptographic keys<br />
• Agree the security & business processes for the transformation of IT &<br />
security solutions over the life of the contract<br />
• Third parties & subcontracts • What are the future challenges?<br />
Bill Pepper, Director of Security Risk Management,<br />
Computer Sciences Corporation<br />
Bill has a lifetime of experience as a professional corporate & information security & privacy manager. Following a<br />
distinguished career in information security with thee Royal Air Force he has obtained a significant reputation as an expert in<br />
these areas, & particularly in privacy & security risk management. In addition to all aspects of security, including information,<br />
personnel & physical, Bill is also responsible for Data Protection within CSC’s EMEA Northern Region supported by a<br />
specialist Data Protection team. Latterly he has developed significant experience in the areas of outsourcing & off-shoring<br />
from the perspectives of both outsourcing services & also running other organisations outsourced services.<br />
17:20 HUMAN ERROR: THE TOP SECURITY CONCERN IN A MULTI-NATIONAL<br />
ORGANISATION?<br />
• Creating an effective (& fun!) training & awareness programme<br />
• To recommendations for writing an awareness policy that works<br />
• Enforcing consequences<br />
• Make it easy to do the right thing<br />
Paul Wood, Group Chief Security Officer, Aviva Group<br />
Paul has over 30 years experience in the security arena, dealing with crime, fraud, information security, counter-terrorist &<br />
executive protection. He worked in a number of security roles within government from 1974 until he retired in 1995 from<br />
the Directorate of Security Policy, at the Ministry of Defence. He joined the Civil Aviation Authority / National Air Traffic<br />
Services as the Head of Corporate Security. From Jul 99 – Apr 06 he was the Chief Security Officer for UBS Investment<br />
Bank, with responsibilities for all aspects of physical & information security. In April 06 he assumed the appointment of<br />
Group Chief Security Officer for Aviva Group; he has responsibility for all aspects of security across the Group. Paul is a<br />
regular speaker on security matters. He was awarded the MBE in the 1995 New Years’ Honours List.<br />
17:50 THE COMMON SENSE & NONSENSE OF JUSTIFYING SECURITY<br />
INVESTMENTS<br />
Infosecurity accounts for 10% or less of IT budgets - & increasingly management<br />
demands robust business cases to justify expenditures. Experienced practitioners<br />
know that this is the equivalent of writing technology fiction - the costs are<br />
reasonably well known but the benefits are often pure fantasy as security metrics<br />
are not a mature topic &management is not interested in technical metrics - they<br />
want to know the cost of information leaks, corrupt data & downtime & some of<br />
these events are outside the control of the IT function.<br />
• Metrics that make sense to non-IT & non-security people<br />
• The need to identify accountability for delivering benefits<br />
• The true cost of insecurity<br />
• The language that helps get a business case approved<br />
• How the audit function can help support the business case<br />
• How to identify a nonsensical business case<br />
Dr. Eduardo Gelbstein, Adjunct Professor, Webster University (Geneva),<br />
Former Advisor to the UN Board of Auditors and Former Director, UN<br />
International Computing Centre<br />
Ed has been an IT practitioner since the 1960s, during which time he worked as project manager, systems architect &<br />
executive in several organisations & different countries until 2002, when he was invited to become an auditor, an activity that<br />
he continues to develop as an advisor to the United Nations Board of Auditors & the French National Audit Office. Ed also<br />
teaches an MBA course on business systems management in Geneva, Switzerland & is a Senior Fellow of the United<br />
Nations Institute for <strong>Training</strong> & Research. He has authored several books & articles.<br />
18:20 CHAIRMAN’S CLOSE OF DAY ONE<br />
18:30 - 20:00 CISO Port & Wine Tasting Reception, Lisbon:<br />
Kindly Sponsored by:<br />
20:00 - 22:00 CISO FADO DINNER, LISBON (PROVISIONAL)<br />
STUDY<br />
CASE STUDY<br />
CASE<br />
CASE STUDY<br />
CASE STUDY<br />
CASE<br />
STUDY<br />
KEY CASE<br />
STUDY