web server - Borland Technical Publications
web server - Borland Technical Publications web server - Borland Technical Publications
Connection management Configuring connection properties The following connection pool properties can be set: Property Value type Description Default wait-timeout Integer The number of seconds to wait for a free connection when maximumcapacity connections are already opened. When using the maximumcapacity property and the pool is at its max and can't serve any more connections, the threads looking for connections end up waiting for the connection(s) to become available for a long time if the wait time is unbounded (set to 0 seconds). You can set the wait-timeout period to suit your needs. 30 busy-timeout Integer The number of seconds to wait before a busy connection is released. If a connection is busy for a long time, the application using it may have hung and be unable to release the connection. This timeout will ensure that connections will be timed out when they have been busy for much longer than necessary. idle-timeout Integer A pooled connection remaining in an idle state for a period of time longer than this timeout value should be closed to conserve resources. All idle connections are checked for idle-timeout expiration every 60 seconds. The value of the idletimeout is given in seconds. A value of 0 (zero) indicates that connection cleanup is disabled. maximum-capacity Integer Identifies the maximum number of managed connections which VisiConnect will allow. Throws ResourceAllocationException when requests for newly allocated managed connections go beyond this limit. The following properties are no longer used and are now ignored by VisiConnect. They are replaced in BES 6.5 by the pool properties busy-timeout, idle-timeout, and waittimeout, listed in the table above. You do not have to delete the old-style properties from ra-borland.xml, but they will no longer have any effect. Unused Pool properties 600 (ten minutes) 600 (ten minutes) 10 Table 27.1 Unused pool properties Property Default Description initial-capacity 1 Identifies the initial number of managed connections which VisiConnect will attempt to obtain during deployment. capacity-delta 1 Identifies the number of additional managed connections which the VisiConnect will attempt to obtain during resizing of the maintained connection pool. Chapter 27: Using VisiConnect 259
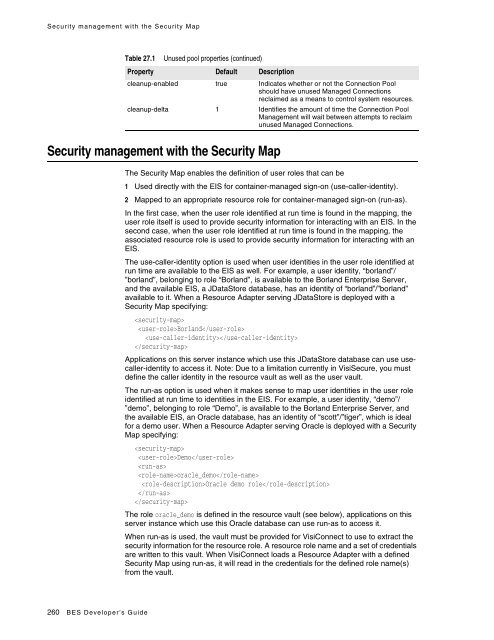
Security management with the Security Map Table 27.1 Unused pool properties (continued) Property Default Description cleanup-enabled true Indicates whether or not the Connection Pool should have unused Managed Connections reclaimed as a means to control system resources. cleanup-delta 1 Identifies the amount of time the Connection Pool Management will wait between attempts to reclaim unused Managed Connections. Security management with the Security Map The Security Map enables the definition of user roles that can be 1 Used directly with the EIS for container-managed sign-on (use-caller-identity). 2 Mapped to an appropriate resource role for container-managed sign-on (run-as). In the first case, when the user role identified at run time is found in the mapping, the user role itself is used to provide security information for interacting with an EIS. In the second case, when the user role identified at run time is found in the mapping, the associated resource role is used to provide security information for interacting with an EIS. The use-caller-identity option is used when user identities in the user role identified at run time are available to the EIS as well. For example, a user identity, “borland”/ ”borland”, belonging to role “Borland”, is available to the Borland Enterprise Server, and the available EIS, a JDataStore database, has an identity of “borland”/”borland” available to it. When a Resource Adapter serving JDataStore is deployed with a Security Map specifying: Borland Applications on this server instance which use this JDataStore database can use usecaller-identity to access it. Note: Due to a limitation currently in VisiSecure, you must define the caller identity in the resource vault as well as the user vault. The run-as option is used when it makes sense to map user identities in the user role identified at run time to identities in the EIS. For example, a user identity, “demo”/ ”demo”, belonging to role “Demo”, is available to the Borland Enterprise Server, and the available EIS, an Oracle database, has an identity of “scott”/”tiger”, which is ideal for a demo user. When a Resource Adapter serving Oracle is deployed with a Security Map specifying: Demo oracle_demo Oracle demo role The role oracle_demo is defined in the resource vault (see below), applications on this server instance which use this Oracle database can use run-as to access it. When run-as is used, the vault must be provided for VisiConnect to use to extract the security information for the resource role. A resource role name and a set of credentials are written to this vault. When VisiConnect loads a Resource Adapter with a defined Security Map using run-as, it will read in the credentials for the defined role name(s) from the vault. 260 BES Developer’s Guide
- Page 219 and 220: Connecting to JDBC Resources from J
- Page 221 and 222: Configuring JMS Connection Factorie
- Page 223 and 224: Defining Connection Pool Properties
- Page 225 and 226: Obtaining JMS Connection Factories
- Page 227 and 228: JMS and Transactions and its accomp
- Page 229 and 230: JMS and Transactions For instance:
- Page 231 and 232: 220 BES Developer’s Guide
- Page 233 and 234: Configuring JMS administered object
- Page 235 and 236: Tibco Creating Clustered JMS Servic
- Page 237 and 238: Sonic serverUrl String localhost:72
- Page 239 and 240: Sonic Creating Clustered JMS Servic
- Page 241 and 242: OpenJMS Even though OpenJMS can be
- Page 243 and 244: OpenJMS Important If you use OpenJM
- Page 245 and 246: OpenJMS openjms.clean_messages_on_s
- Page 247 and 248: OpenJMS Table 24.1 Property Name De
- Page 249 and 250: Other JMS providers The following a
- Page 251 and 252: 240 BES Developer’s Guide
- Page 253 and 254: Creating the Interceptor Class For
- Page 255 and 256: Creating the JAR file Creating the
- Page 257 and 258: Components Components The Connector
- Page 259 and 260: System Contracts Connection Managem
- Page 261 and 262: System Contracts Security Managemen
- Page 263 and 264: Common Client Interface (CCI) Conne
- Page 265 and 266: Packaging and Deployment Figure 26.
- Page 267 and 268: Resource Adapters Resource Adapters
- Page 269: Connection management Connection ma
- Page 273 and 274: Security management with the Securi
- Page 275 and 276: Resource Adapter overview Note Reso
- Page 277 and 278: Deployment Descriptors for the Reso
- Page 279 and 280: Developing the Resource Adapter Con
- Page 281 and 282: Deploying the Resource Adapter Pack
- Page 283 and 284: Application development overview 8
- Page 285 and 286: Application development overview //
- Page 287 and 288: Application development overview
- Page 289 and 290: Other Considerations Other Consider
- Page 291 and 292: Other Considerations To illustrate,
- Page 293 and 294: Other Considerations } } { cf = new
- Page 295 and 296: General syntax and usage General sy
- Page 297 and 298: Syntax and usage for iastool Table
- Page 299 and 300: Syntax and usage for java2iiop Exam
- Page 301 and 302: Syntax and usage for appclient Tabl
- Page 303 and 304: Building and running the BES exampl
- Page 305 and 306: Using the iastool command-line tool
- Page 307 and 308: Using the iastool command-line tool
- Page 309 and 310: Using the iastool command-line tool
- Page 311 and 312: Using the iastool command-line tool
- Page 313 and 314: Using the iastool command-line tool
- Page 315 and 316: Using the iastool command-line tool
- Page 317 and 318: Using the iastool command-line tool
- Page 319 and 320: Using the iastool command-line tool
Security management with the Security Map<br />
Table 27.1<br />
Unused pool properties (continued)<br />
Property Default Description<br />
cleanup-enabled true Indicates whether or not the Connection Pool<br />
should have unused Managed Connections<br />
reclaimed as a means to control system resources.<br />
cleanup-delta 1 Identifies the amount of time the Connection Pool<br />
Management will wait between attempts to reclaim<br />
unused Managed Connections.<br />
Security management with the Security Map<br />
The Security Map enables the definition of user roles that can be<br />
1 Used directly with the EIS for container-managed sign-on (use-caller-identity).<br />
2 Mapped to an appropriate resource role for container-managed sign-on (run-as).<br />
In the first case, when the user role identified at run time is found in the mapping, the<br />
user role itself is used to provide security information for interacting with an EIS. In the<br />
second case, when the user role identified at run time is found in the mapping, the<br />
associated resource role is used to provide security information for interacting with an<br />
EIS.<br />
The use-caller-identity option is used when user identities in the user role identified at<br />
run time are available to the EIS as well. For example, a user identity, “borland”/<br />
”borland”, belonging to role “<strong>Borland</strong>”, is available to the <strong>Borland</strong> Enterprise Server,<br />
and the available EIS, a JDataStore database, has an identity of “borland”/”borland”<br />
available to it. When a Resource Adapter serving JDataStore is deployed with a<br />
Security Map specifying:<br />
<br />
<strong>Borland</strong><br />
<br />
<br />
Applications on this <strong>server</strong> instance which use this JDataStore database can use usecaller-identity<br />
to access it. Note: Due to a limitation currently in VisiSecure, you must<br />
define the caller identity in the resource vault as well as the user vault.<br />
The run-as option is used when it makes sense to map user identities in the user role<br />
identified at run time to identities in the EIS. For example, a user identity, “demo”/<br />
”demo”, belonging to role “Demo”, is available to the <strong>Borland</strong> Enterprise Server, and<br />
the available EIS, an Oracle database, has an identity of “scott”/”tiger”, which is ideal<br />
for a demo user. When a Resource Adapter serving Oracle is deployed with a Security<br />
Map specifying:<br />
<br />
Demo<br />
<br />
oracle_demo<br />
Oracle demo role<br />
<br />
<br />
The role oracle_demo is defined in the resource vault (see below), applications on this<br />
<strong>server</strong> instance which use this Oracle database can use run-as to access it.<br />
When run-as is used, the vault must be provided for VisiConnect to use to extract the<br />
security information for the resource role. A resource role name and a set of credentials<br />
are written to this vault. When VisiConnect loads a Resource Adapter with a defined<br />
Security Map using run-as, it will read in the credentials for the defined role name(s)<br />
from the vault.<br />
260 BES Developer’s Guide