Host Intrusion Prevention 7.0.0 for ePO 4.0 Product Guide - McAfee
Host Intrusion Prevention 7.0.0 for ePO 4.0 Product Guide - McAfee Host Intrusion Prevention 7.0.0 for ePO 4.0 Product Guide - McAfee
Configuring Application Blocking Policies Working with Application Blocking Rules policies Select this option... Allow application to hook other applications To do this... Allow the application to bind to other applications. 5 Select Matching Options: Select this option... Fingerprint only To do this... Match against the fingerprint. only if the client's application is the same version of the application referenced on the server. Path when matched first, then the fingerprint When the application is launched for the first time, it will be matched based on the path specified by the user. If it matches, the fingerprint will be calculated at the client. From that point on, the rule will match based only on the fingerprint of the application. Path only When the application is launched, it will be matched based only on the path specified by the user. 6 Enter a note, if desired. 7 Click OK to save changes. Managing Application Blocking client rules Use this task to analyze Application Blocking client rules created automatically in adaptive mode or manually for a group of clients, then determine which if any client rules to move to an Application Blocking policy. NOTE: Access to Application Blocking Client Rules on the Host IPS tab under Reporting requires additional permissions other than that for Host Intrusion Prevention Application Blocking, including view permissions for Event Log, Systems, and System Tree access. Task For option definitions, click ? on the page displaying the options. 1 Go to Reporting | Host IPS | Application Blocking Client Rules. Figure 29: Application Blocking Client Rules 74 McAfee Host Intrusion Prevention 7.0 Product Guide for use with ePolicy Orchestrator 4.0
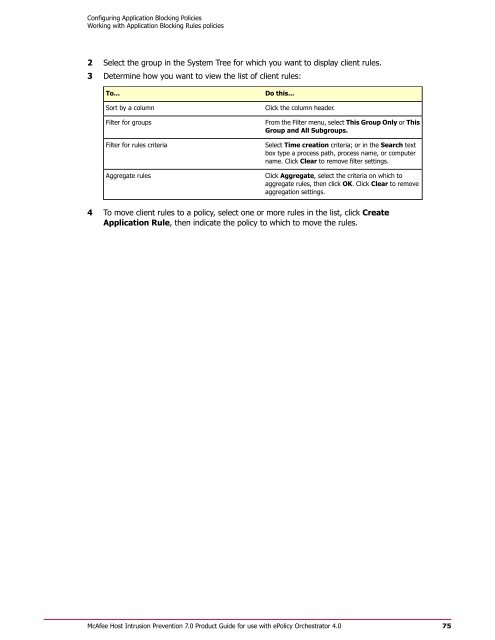
Configuring Application Blocking Policies Working with Application Blocking Rules policies 2 Select the group in the System Tree for which you want to display client rules. 3 Determine how you want to view the list of client rules: To... Sort by a column Filter for groups Filter for rules criteria Aggregate rules Do this... Click the column header. From the Filter menu, select This Group Only or This Group and All Subgroups. Select Time creation criteria; or in the Search text box type a process path, process name, or computer name. Click Clear to remove filter settings. Click Aggregate, select the criteria on which to aggregate rules, then click OK. Click Clear to remove aggregation settings. 4 To move client rules to a policy, select one or more rules in the list, click Create Application Rule, then indicate the policy to which to move the rules. McAfee Host Intrusion Prevention 7.0 Product Guide for use with ePolicy Orchestrator 4.0 75
- Page 23 and 24: Managing Your Protection Management
- Page 25 and 26: Configuring IPS Policies Overview o
- Page 27 and 28: Configuring IPS Policies Working wi
- Page 29 and 30: Configuring IPS Policies Working wi
- Page 31 and 32: Configuring IPS Policies Working wi
- Page 33 and 34: Configuring IPS Policies Working wi
- Page 35 and 36: Configuring IPS Policies Working wi
- Page 37 and 38: Configuring IPS Policies Working wi
- Page 39 and 40: Configuring IPS Policies Working wi
- Page 41 and 42: Configuring IPS Policies Working wi
- Page 43 and 44: Configuring IPS Policies Working wi
- Page 45 and 46: Configuring Firewall Policies The F
- Page 47 and 48: Configuring Firewall Policies Overv
- Page 49 and 50: Configuring Firewall Policies Overv
- Page 51 and 52: Configuring Firewall Policies Overv
- Page 53 and 54: Configuring Firewall Policies Overv
- Page 55 and 56: Configuring Firewall Policies Overv
- Page 57 and 58: Configuring Firewall Policies Worki
- Page 59 and 60: Configuring Firewall Policies Worki
- Page 61 and 62: Configuring Firewall Policies Worki
- Page 63 and 64: Configuring Firewall Policies Worki
- Page 65 and 66: Configuring Firewall Policies Worki
- Page 67 and 68: Configuring Firewall Policies Worki
- Page 69 and 70: Configuring Application Blocking Po
- Page 71 and 72: Configuring Application Blocking Po
- Page 73: Configuring Application Blocking Po
- Page 77 and 78: Configuring General Policies Workin
- Page 79 and 80: Configuring General Policies Workin
- Page 81 and 82: Configuring General Policies Workin
- Page 83 and 84: Configuring General Policies Workin
- Page 85 and 86: Configuring General Policies Workin
- Page 87 and 88: Working with Host Intrusion Prevent
- Page 89 and 90: Working with Host Intrusion Prevent
- Page 91 and 92: Working with Host Intrusion Prevent
- Page 93 and 94: Working with Host Intrusion Prevent
- Page 95 and 96: Working with Host Intrusion Prevent
- Page 97 and 98: Working with Host Intrusion Prevent
- Page 99 and 100: Working with Host Intrusion Prevent
- Page 101 and 102: Working with Host Intrusion Prevent
- Page 103 and 104: Working with Host Intrusion Prevent
- Page 105 and 106: Working with Host Intrusion Prevent
- Page 107 and 108: Index clients (continued) updating
- Page 109 and 110: Index McAfee Default policy (contin
- Page 111 and 112: Index T troubleshooting, Host IPS C
Configuring Application Blocking Policies<br />
Working with Application Blocking Rules policies<br />
2 Select the group in the System Tree <strong>for</strong> which you want to display client rules.<br />
3 Determine how you want to view the list of client rules:<br />
To...<br />
Sort by a column<br />
Filter <strong>for</strong> groups<br />
Filter <strong>for</strong> rules criteria<br />
Aggregate rules<br />
Do this...<br />
Click the column header.<br />
From the Filter menu, select This Group Only or This<br />
Group and All Subgroups.<br />
Select Time creation criteria; or in the Search text<br />
box type a process path, process name, or computer<br />
name. Click Clear to remove filter settings.<br />
Click Aggregate, select the criteria on which to<br />
aggregate rules, then click OK. Click Clear to remove<br />
aggregation settings.<br />
4 To move client rules to a policy, select one or more rules in the list, click Create<br />
Application Rule, then indicate the policy to which to move the rules.<br />
<strong>McAfee</strong> <strong>Host</strong> <strong>Intrusion</strong> <strong>Prevention</strong> 7.0 <strong>Product</strong> <strong>Guide</strong> <strong>for</strong> use with ePolicy Orchestrator <strong>4.0</strong><br />
75