Host Intrusion Prevention 7.0.0 for ePO 4.0 Product Guide - McAfee
Host Intrusion Prevention 7.0.0 for ePO 4.0 Product Guide - McAfee
Host Intrusion Prevention 7.0.0 for ePO 4.0 Product Guide - McAfee
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
Configuring Firewall Policies<br />
Working with Firewall Rules policies<br />
Change the policy’s assignment on the Policy Assignment page. For a group, go to Systems<br />
| System Tree, select a group, and then on the Policies tab click Edit Assignment. For a<br />
system go to Systems | System Tree, select a group that contains the system, and then on<br />
the System tab, select the system and select More Actions | Modify Policies on a Single<br />
System.<br />
Tasks<br />
Configuring the Firewall Options policy<br />
Configuring the Firewall Options policy<br />
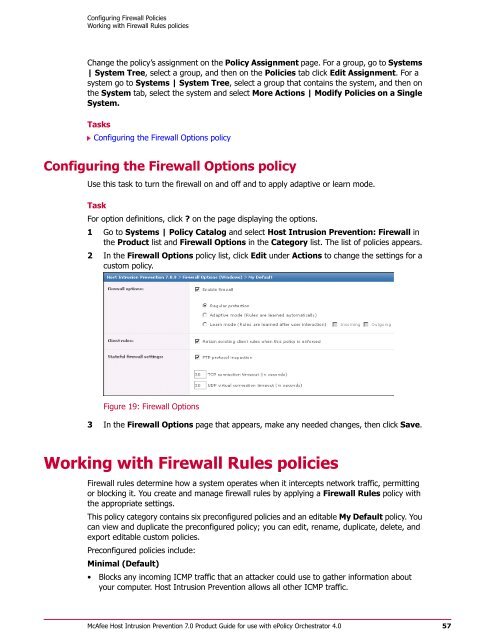
Use this task to turn the firewall on and off and to apply adaptive or learn mode.<br />
Task<br />
For option definitions, click ? on the page displaying the options.<br />
1 Go to Systems | Policy Catalog and select <strong>Host</strong> <strong>Intrusion</strong> <strong>Prevention</strong>: Firewall in<br />
the <strong>Product</strong> list and Firewall Options in the Category list. The list of policies appears.<br />
2 In the Firewall Options policy list, click Edit under Actions to change the settings <strong>for</strong> a<br />
custom policy.<br />
Figure 19: Firewall Options<br />
3 In the Firewall Options page that appears, make any needed changes, then click Save.<br />
Working with Firewall Rules policies<br />
Firewall rules determine how a system operates when it intercepts network traffic, permitting<br />
or blocking it. You create and manage firewall rules by applying a Firewall Rules policy with<br />
the appropriate settings.<br />
This policy category contains six preconfigured policies and an editable My Default policy. You<br />
can view and duplicate the preconfigured policy; you can edit, rename, duplicate, delete, and<br />
export editable custom policies.<br />
Preconfigured policies include:<br />
Minimal (Default)<br />
• Blocks any incoming ICMP traffic that an attacker could use to gather in<strong>for</strong>mation about<br />
your computer. <strong>Host</strong> <strong>Intrusion</strong> <strong>Prevention</strong> allows all other ICMP traffic.<br />
<strong>McAfee</strong> <strong>Host</strong> <strong>Intrusion</strong> <strong>Prevention</strong> 7.0 <strong>Product</strong> <strong>Guide</strong> <strong>for</strong> use with ePolicy Orchestrator <strong>4.0</strong><br />
57