Policy 7230A - Department of Administration
Policy 7230A - Department of Administration
Policy 7230A - Department of Administration
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Mandatory Baselines<br />
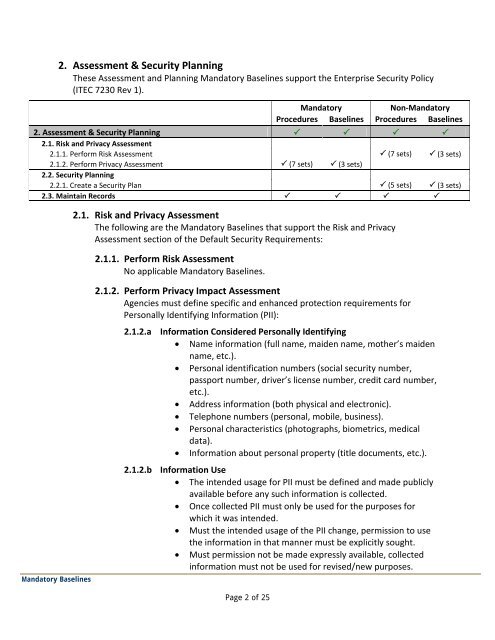
2. Assessment & Security Planning<br />
These Assessment and Planning Mandatory Baselines support the Enterprise Security <strong>Policy</strong><br />
(ITEC 7230 Rev 1).<br />
Page 2 <strong>of</strong> 25<br />
Mandatory<br />
Non-Mandatory<br />
Procedures Baselines Procedures Baselines<br />
2. Assessment & Security Planning <br />
2.1. Risk and Privacy Assessment<br />
2.1.1. Perform Risk Assessment (7 sets) (3 sets)<br />
2.1.2. Perform Privacy Assessment (7 sets) (3 sets)<br />
2.2. Security Planning<br />
2.2.1. Create a Security Plan (5 sets) (3 sets)<br />
2.3. Maintain Records <br />
2.1. Risk and Privacy Assessment<br />
The following are the Mandatory Baselines that support the Risk and Privacy<br />
Assessment section <strong>of</strong> the Default Security Requirements:<br />
2.1.1. Perform Risk Assessment<br />
No applicable Mandatory Baselines.<br />
2.1.2. Perform Privacy Impact Assessment<br />
Agencies must define specific and enhanced protection requirements for<br />
Personally Identifying Information (PII):<br />
2.1.2.a Information Considered Personally Identifying<br />
• Name information (full name, maiden name, mother’s maiden<br />
name, etc.).<br />
• Personal identification numbers (social security number,<br />
passport number, driver’s license number, credit card number,<br />
etc.).<br />
• Address information (both physical and electronic).<br />
• Telephone numbers (personal, mobile, business).<br />
• Personal characteristics (photographs, biometrics, medical<br />
data).<br />
• Information about personal property (title documents, etc.).<br />
2.1.2.b Information Use<br />
• The intended usage for PII must be defined and made publicly<br />
available before any such information is collected.<br />
• Once collected PII must only be used for the purposes for<br />
which it was intended.<br />
• Must the intended usage <strong>of</strong> the PII change, permission to use<br />
the information in that manner must be explicitly sought.<br />
• Must permission not be made expressly available, collected<br />
information must not be used for revised/new purposes.