Policy 7230A - Department of Administration
Policy 7230A - Department of Administration
Policy 7230A - Department of Administration
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
10 Physical Security<br />
Sections 10.1 and 10.2 constitute the State <strong>of</strong> Kansas’ Physical Security <strong>Policy</strong>. This policy is<br />
to be accompanied by defined Physical Security Non-Mandatory Procedures and Baselines<br />
that are distributed in a companion document.<br />
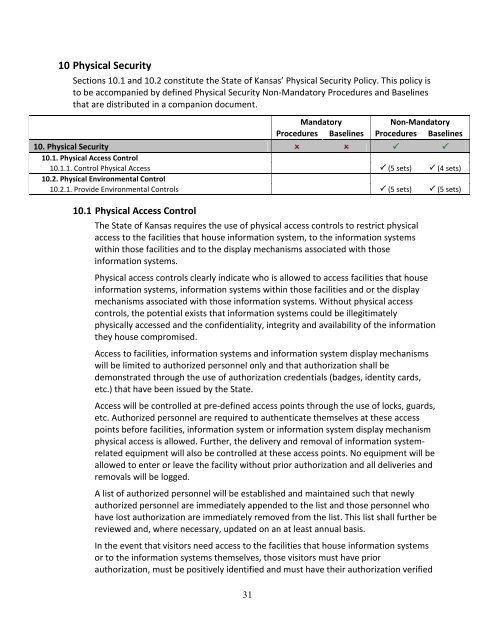
Mandatory<br />
Non-Mandatory<br />
Procedures Baselines Procedures Baselines<br />
10. Physical Security <br />
10.1. Physical Access Control<br />
10.1.1. Control Physical Access (5 sets) (4 sets)<br />
10.2. Physical Environmental Control<br />
10.2.1. Provide Environmental Controls (5 sets) (5 sets)<br />
10.1 Physical Access Control<br />
The State <strong>of</strong> Kansas requires the use <strong>of</strong> physical access controls to restrict physical<br />
access to the facilities that house information system, to the information systems<br />
within those facilities and to the display mechanisms associated with those<br />
information systems.<br />
Physical access controls clearly indicate who is allowed to access facilities that house<br />
information systems, information systems within those facilities and or the display<br />
mechanisms associated with those information systems. Without physical access<br />
controls, the potential exists that information systems could be illegitimately<br />
physically accessed and the confidentiality, integrity and availability <strong>of</strong> the information<br />
they house compromised.<br />
Access to facilities, information systems and information system display mechanisms<br />
will be limited to authorized personnel only and that authorization shall be<br />
demonstrated through the use <strong>of</strong> authorization credentials (badges, identity cards,<br />
etc.) that have been issued by the State.<br />
Access will be controlled at pre-defined access points through the use <strong>of</strong> locks, guards,<br />
etc. Authorized personnel are required to authenticate themselves at these access<br />
points before facilities, information system or information system display mechanism<br />
physical access is allowed. Further, the delivery and removal <strong>of</strong> information systemrelated<br />
equipment will also be controlled at these access points. No equipment will be<br />
allowed to enter or leave the facility without prior authorization and all deliveries and<br />
removals will be logged.<br />
A list <strong>of</strong> authorized personnel will be established and maintained such that newly<br />
authorized personnel are immediately appended to the list and those personnel who<br />
have lost authorization are immediately removed from the list. This list shall further be<br />
reviewed and, where necessary, updated on an at least annual basis.<br />
In the event that visitors need access to the facilities that house information systems<br />
or to the information systems themselves, those visitors must have prior<br />
authorization, must be positively identified and must have their authorization verified<br />
31