Cryptanalysis of RSA Factorization - Library(ISI Kolkata) - Indian ...
Cryptanalysis of RSA Factorization - Library(ISI Kolkata) - Indian ...
Cryptanalysis of RSA Factorization - Library(ISI Kolkata) - Indian ...
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
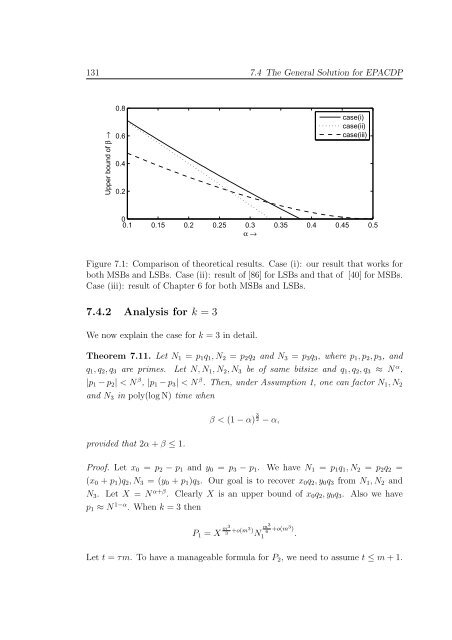
131 7.4 The General Solution for EPACDP<br />
Upper bound <strong>of</strong> β →<br />
0.8<br />
0.6<br />
0.4<br />
0.2<br />
case(i)<br />
case(ii)<br />
case(iii)<br />
0<br />
0.1 0.15 0.2 0.25 0.3 0.35 0.4 0.45 0.5<br />
α →<br />
Figure 7.1: Comparison <strong>of</strong> theoretical results. Case (i): our result that works for<br />
both MSBs and LSBs. Case (ii): result <strong>of</strong> [86] for LSBs and that <strong>of</strong> [40] for MSBs.<br />
Case (iii): result <strong>of</strong> Chapter 6 for both MSBs and LSBs.<br />
7.4.2 Analysis for k = 3<br />
We now explain the case for k = 3 in detail.<br />
Theorem 7.11. Let N 1 = p 1 q 1 ,N 2 = p 2 q 2 and N 3 = p 3 q 3 , where p 1 ,p 2 ,p 3 , and<br />
q 1 ,q 2 ,q 3 are primes. Let N,N 1 ,N 2 ,N 3 be <strong>of</strong> same bitsize and q 1 ,q 2 ,q 3 ≈ N α ,<br />
|p 1 −p 2 | < N β , |p 1 −p 3 | < N β . Then, under Assumption 1, one can factor N 1 ,N 2<br />
and N 3 in poly(logN) time when<br />
provided that 2α+β ≤ 1.<br />
β < (1−α) 3 2 −α,<br />
Pro<strong>of</strong>. Let x 0 = p 2 − p 1 and y 0 = p 3 − p 1 . We have N 1 = p 1 q 1 ,N 2 = p 2 q 2 =<br />
(x 0 + p 1 )q 2 ,N 3 = (y 0 + p 1 )q 3 . Our goal is to recover x 0 q 2 ,y 0 q 3 from N 1 ,N 2 and<br />
N 3 . Let X = N α+β . Clearly X is an upper bound <strong>of</strong> x 0 q 2 ,y 0 q 3 . Also we have<br />
p 1 ≈ N 1−α . When k = 3 then<br />
P 1 = X m3<br />
3 +o(m3) N m3<br />
6 +o(m3 )<br />
1 .<br />
Let t = τm. To have a manageable formula for P 2 , we need to assume t ≤ m+1.