Cryptanalysis of RSA Factorization - Library(ISI Kolkata) - Indian ...
Cryptanalysis of RSA Factorization - Library(ISI Kolkata) - Indian ...
Cryptanalysis of RSA Factorization - Library(ISI Kolkata) - Indian ...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
111 6.3 Exposing a Few MSBs <strong>of</strong> One Prime<br />
9864355429485398257581885621415132927137653573<br />
and<br />
5984825641870931585823382220962926344220670532554403933352105675571066<br />
6727036032597303235163473076823311343759215354840931554536631098033574<br />
6996932026050432396316389068925325234493940473852769406714934240353469<br />
4186411407834893900732303380146620012528421339.<br />
Note that, p 1 ,p 2 share middle 504 many bits (leaving 177 bits from the least<br />
significant side). Further, q 1 ,q 2 are 150-bit primes<br />
1038476608131498405684472704928794724111541861 and<br />
1281887704228770097092001008195142506836912053 respectively.<br />
Given N 1 ,N 2 , with only the implicit information, we can factorize both <strong>of</strong> them<br />
efficiently. We use lattice <strong>of</strong> dimension 70 (parameters m = 1,t 1 = 1,t 2 = 1) and<br />
the lattice reduction takes 175.83 seconds.<br />
Referring to Theorems 6.1,6.10 together, one may be tempted to consider the<br />
case that a few contiguous intervals <strong>of</strong> bits are same in p 1 ,p 2 . However, in such a<br />
scenario, the polynomials contain increased number <strong>of</strong> variables as well as monomials.<br />
Thus, encouraging results cannot be obtained in this method.<br />
6.3 Exposing a Few MSBs <strong>of</strong> One Prime<br />
In this section we study what actually happens when a few bits <strong>of</strong> q 1 or q 2 gets<br />
exposed. Without loss <strong>of</strong> generality, consider that a few MSBs <strong>of</strong> q 2 are available.<br />
In this case, q 2 can be written as q 20 + q 21 , where q 20 is known and it takes care<br />
<strong>of</strong> the higher order bits <strong>of</strong> q 2 . In such a case we can generalize Theorem 6.1 as<br />
follows. We do not write the pro<strong>of</strong> as it is similar to that <strong>of</strong> Theorem 6.1.<br />
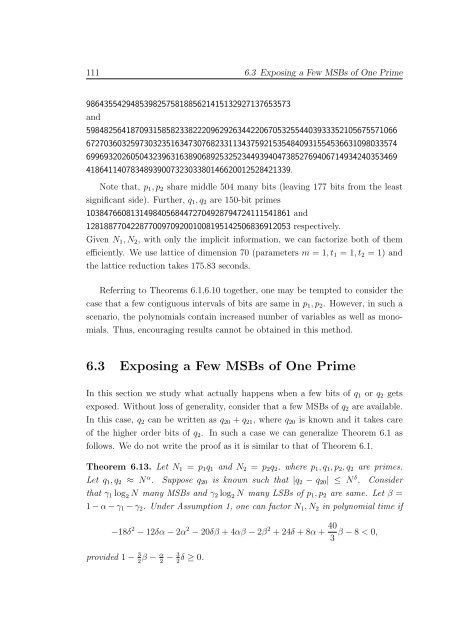
Theorem 6.13. Let N 1 = p 1 q 1 and N 2 = p 2 q 2 , where p 1 ,q 1 ,p 2 ,q 2 are primes.<br />
Let q 1 ,q 2 ≈ N α . Suppose q 20 is known such that |q 2 − q 20 | ≤ N δ . Consider<br />
that γ 1 log 2 N many MSBs and γ 2 log 2 N many LSBs <strong>of</strong> p 1 ,p 2 are same. Let β =<br />
1−α−γ 1 −γ 2 . Under Assumption 1, one can factor N 1 ,N 2 in polynomial time if<br />
−18δ 2 −12δα−2α 2 −20δβ +4αβ −2β 2 +24δ +8α+ 40 β −8 < 0,<br />
3<br />
provided 1− 3 2 β − α 2 − 3 2 δ ≥ 0.