Windows Server 2003 Recommended Baseline Security
Windows Server 2003 Recommended Baseline Security
Windows Server 2003 Recommended Baseline Security
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
<strong>Windows</strong> <strong>Server</strong> <strong>2003</strong><br />
<strong>Recommended</strong> <strong>Baseline</strong> <strong>Security</strong> (ITSG-20)<br />
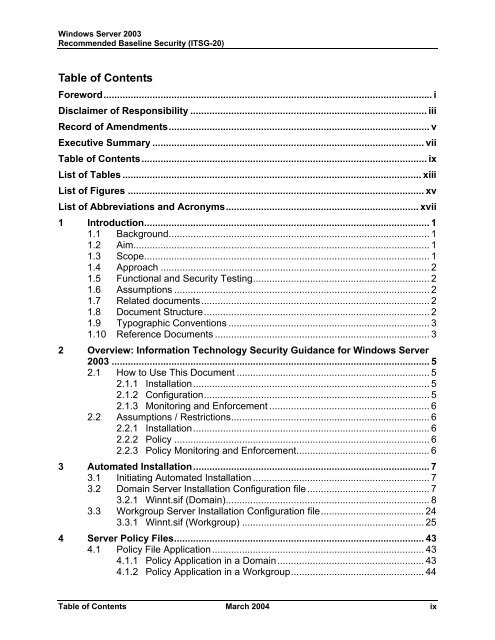
Table of Contents<br />
Foreword......................................................................................................................... i<br />
Disclaimer of Responsibility ....................................................................................... iii<br />
Record of Amendments................................................................................................ v<br />
Executive Summary .................................................................................................... vii<br />
Table of Contents......................................................................................................... ix<br />
List of Tables .............................................................................................................. xiii<br />
List of Figures ............................................................................................................. xv<br />
List of Abbreviations and Acronyms....................................................................... xvii<br />
1 Introduction......................................................................................................... 1<br />
1.1 Background................................................................................................ 1<br />
1.2 Aim............................................................................................................. 1<br />
1.3 Scope......................................................................................................... 1<br />
1.4 Approach ................................................................................................... 2<br />
1.5 Functional and <strong>Security</strong> Testing................................................................. 2<br />
1.6 Assumptions .............................................................................................. 2<br />
1.7 Related documents.................................................................................... 2<br />
1.8 Document Structure................................................................................... 2<br />
1.9 Typographic Conventions .......................................................................... 3<br />
1.10 Reference Documents ............................................................................... 3<br />
2 Overview: Information Technology <strong>Security</strong> Guidance for <strong>Windows</strong> <strong>Server</strong><br />
<strong>2003</strong> ..................................................................................................................... 5<br />
2.1 How to Use This Document ....................................................................... 5<br />
2.1.1 Installation....................................................................................... 5<br />
2.1.2 Configuration................................................................................... 5<br />
2.1.3 Monitoring and Enforcement ........................................................... 6<br />
2.2 Assumptions / Restrictions......................................................................... 6<br />
2.2.1 Installation....................................................................................... 6<br />
2.2.2 Policy .............................................................................................. 6<br />
2.2.3 Policy Monitoring and Enforcement................................................. 6<br />
3 Automated Installation....................................................................................... 7<br />
3.1 Initiating Automated Installation ................................................................. 7<br />
3.2 Domain <strong>Server</strong> Installation Configuration file ............................................. 7<br />
3.2.1 Winnt.sif (Domain)........................................................................... 8<br />
3.3 Workgroup <strong>Server</strong> Installation Configuration file...................................... 24<br />
3.3.1 Winnt.sif (Workgroup) ................................................................... 25<br />
4 <strong>Server</strong> Policy Files............................................................................................ 43<br />
4.1 Policy File Application.............................................................................. 43<br />
4.1.1 Policy Application in a Domain...................................................... 43<br />
4.1.2 Policy Application in a Workgroup................................................. 44<br />
Table of Contents March 2004 ix