Policy Framework Configuration Guide - Juniper Networks
Policy Framework Configuration Guide - Juniper Networks
Policy Framework Configuration Guide - Juniper Networks
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
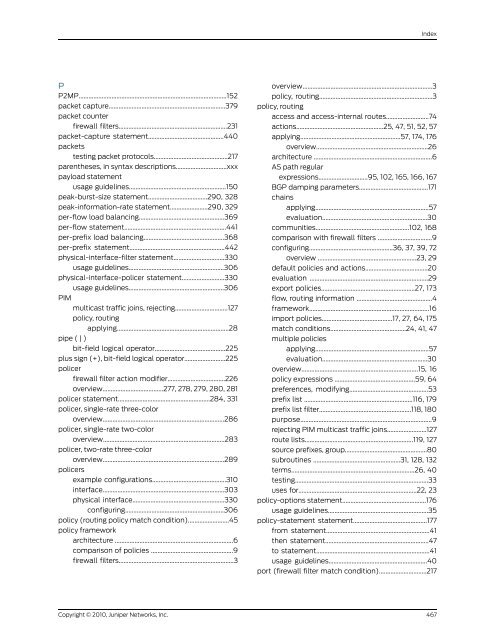
Index<br />
P<br />
P2MP..........................................................................................152<br />
packet capture.......................................................................379<br />
packet counter<br />
firewall filters..................................................................231<br />
packet-capture statement..............................................440<br />
packets<br />
testing packet protocols.............................................217<br />
parentheses, in syntax descriptions...............................xxx<br />
payload statement<br />
usage guidelines...........................................................150<br />
peak-burst-size statement....................................290, 328<br />
peak-information-rate statement.......................290, 329<br />
per-flow load balancing....................................................369<br />
per-flow statement..............................................................441<br />
per-prefix load balancing.................................................368<br />
per-prefix statement..........................................................442<br />
physical-interface-filter statement...............................330<br />
usage guidelines..........................................................306<br />
physical-interface-policer statement..........................330<br />
PIM<br />
pipe ( | )<br />
usage guidelines..........................................................306<br />
multicast traffic joins, rejecting................................127<br />
policy, routing<br />
applying....................................................................28<br />
bit-field logical operator...........................................225<br />
plus sign (+), bit-field logical operator.........................225<br />
policer<br />
firewall filter action modifier...................................226<br />
overview.....................................277, 278, 279, 280, 281<br />
policer statement........................................................284, 331<br />
policer, single-rate three-color<br />
overview..........................................................................286<br />
policer, single-rate two-color<br />
overview..........................................................................283<br />
policer, two-rate three-color<br />
policers<br />
overview..........................................................................289<br />
example configurations.............................................310<br />
interface..........................................................................303<br />
physical interface........................................................330<br />
configuring............................................................306<br />
policy (routing policy match condition).........................45<br />
policy framework<br />
architecture ........................................................................6<br />
comparison of policies ..................................................9<br />
firewall filters......................................................................3<br />
overview...............................................................................3<br />
policy, routing.....................................................................3<br />
policy, routing<br />
access and access-internal routes..........................74<br />
actions.....................................................25, 47, 51, 52, 57<br />
applying.............................................................57, 174, 176<br />
overview....................................................................26<br />
architecture ........................................................................6<br />
AS path regular<br />
expressions..............................95, 102, 165, 166, 167<br />
BGP damping parameters..........................................171<br />
chains<br />
applying.....................................................................57<br />
evaluation................................................................30<br />
communities.........................................................102, 168<br />
comparison with firewall filters .................................9<br />
configuring...................................................36, 37, 39, 72<br />
overview ............................................................23, 29<br />
default policies and actions......................................20<br />
evaluation ........................................................................29<br />
export policies.........................................................27, 173<br />
flow, routing information ..............................................4<br />
framework.........................................................................16<br />
import policies...........................................17, 27, 64, 175<br />
match conditions..............................................24, 41, 47<br />
multiple policies<br />
applying.....................................................................57<br />
evaluation................................................................30<br />
overview.......................................................................15, 16<br />
policy expressions .................................................59, 64<br />
preferences, modifying................................................53<br />
prefix list ..................................................................116, 179<br />
prefix list filter........................................................118, 180<br />
purpose................................................................................9<br />
rejecting PIM multicast traffic joins........................127<br />
route lists..................................................................119, 127<br />
source prefixes, group..................................................80<br />
subroutines .....................................................31, 128, 132<br />
terms...........................................................................26, 40<br />
testing.................................................................................33<br />
uses for........................................................................22, 23<br />
policy-options statement...................................................176<br />
usage guidelines.............................................................35<br />
policy-statement statement.............................................177<br />
from statement...............................................................41<br />
then statement...............................................................47<br />
to statement.....................................................................41<br />
usage guidelines............................................................40<br />
port (firewall filter match condition).............................217<br />
Copyright © 2010, <strong>Juniper</strong> <strong>Networks</strong>, Inc.<br />
467