Policy Framework Configuration Guide - Juniper Networks
Policy Framework Configuration Guide - Juniper Networks
Policy Framework Configuration Guide - Juniper Networks
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
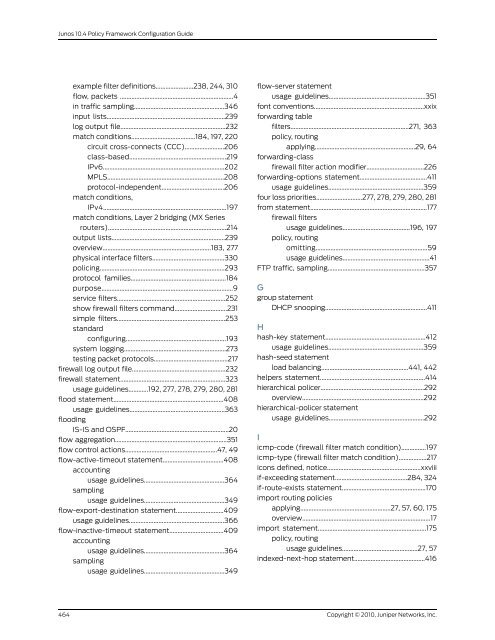
Junos 10.4 <strong>Policy</strong> <strong>Framework</strong> <strong>Configuration</strong> <strong>Guide</strong><br />
example filter definitions.......................238, 244, 310<br />
flow, packets .....................................................................4<br />
in traffic sampling.......................................................346<br />
input lists........................................................................239<br />
log output file................................................................232<br />
match conditions.......................................184, 197, 220<br />
circuit cross-connects (CCC)........................206<br />
class-based...........................................................219<br />
IPv6..........................................................................202<br />
MPLS.......................................................................208<br />
protocol-independent......................................206<br />
match conditions,<br />
IPv4...........................................................................197<br />
match conditions, Layer 2 bridging (MX Series<br />
routers)........................................................................214<br />
output lists.....................................................................239<br />
overview..................................................................183, 277<br />
physical interface filters............................................330<br />
policing............................................................................293<br />
protocol families..........................................................184<br />
purpose................................................................................9<br />
service filters..................................................................252<br />
show firewall filters command................................231<br />
simple filters..................................................................253<br />
standard<br />
configuring.............................................................193<br />
system logging..............................................................273<br />
testing packet protocols.............................................217<br />
firewall log output file.........................................................232<br />
firewall statement................................................................323<br />
usage guidelines............192, 277, 278, 279, 280, 281<br />
flood statement...................................................................408<br />
usage guidelines..........................................................363<br />
flooding<br />
IS-IS and OSPF...............................................................20<br />
flow aggregation....................................................................351<br />
flow control actions........................................................47, 49<br />
flow-active-timeout statement.....................................408<br />
accounting<br />
usage guidelines.................................................364<br />
sampling<br />
usage guidelines.................................................349<br />
flow-export-destination statement.............................409<br />
usage guidelines..........................................................366<br />
flow-inactive-timeout statement.................................409<br />
accounting<br />
usage guidelines.................................................364<br />
sampling<br />
usage guidelines.................................................349<br />
flow-server statement<br />
usage guidelines...........................................................351<br />
font conventions...................................................................xxix<br />
forwarding table<br />
filters........................................................................271, 363<br />
policy, routing<br />
forwarding-class<br />
applying.............................................................29, 64<br />
firewall filter action modifier...................................226<br />
forwarding-options statement.........................................411<br />
usage guidelines..........................................................359<br />
four loss priorities............................277, 278, 279, 280, 281<br />
from statement.......................................................................177<br />
firewall filters<br />
usage guidelines.........................................196, 197<br />
policy, routing<br />
omitting....................................................................59<br />
usage guidelines.....................................................41<br />
FTP traffic, sampling...........................................................357<br />
G<br />
group statement<br />
DHCP snooping..............................................................411<br />
H<br />
hash-key statement.............................................................412<br />
usage guidelines..........................................................359<br />
hash-seed statement<br />
load balancing.....................................................441, 442<br />
helpers statement................................................................414<br />
hierarchical policer...............................................................292<br />
overview..........................................................................292<br />
hierarchical-policer statement<br />
usage guidelines..........................................................292<br />
I<br />
icmp-code (firewall filter match condition)...............197<br />
icmp-type (firewall filter match condition).................217<br />
icons defined, notice.........................................................xxviii<br />
if-exceeding statement............................................284, 324<br />
if-route-exists statement...................................................170<br />
import routing policies<br />
applying.......................................................27, 57, 60, 175<br />
overview..............................................................................17<br />
import statement..................................................................175<br />
policy, routing<br />
usage guidelines..............................................27, 57<br />
indexed-next-hop statement...........................................416<br />
464<br />
Copyright © 2010, <strong>Juniper</strong> <strong>Networks</strong>, Inc.