Professional Certification - tabpi
Professional Certification - tabpi
Professional Certification - tabpi
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
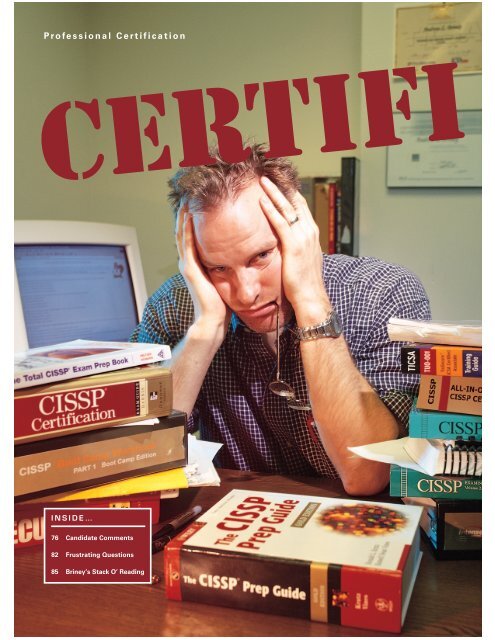
<strong>Professional</strong> <strong>Certification</strong><br />
Certifi<br />
INSIDE…<br />
76 Candidate Comments<br />
82 Frustrating Questions<br />
85 Briney’s Stack O’ Reading
able<br />
A newly minted CISSP gives you the<br />
inside scoop on infosecurity’s most<br />
coveted—and controversial—certification.<br />
by ANDREW BRINEY<br />
Ijust took the CISSP exam, and I’m here to testify: Everything<br />
you’ve heard about it is true. It’s both disarmingly easy and bewilderingly<br />
difficult. It’s both legitimately challenging and totally<br />
unfair. It’s both incredibly rewarding and pull-out-your-hair-andscream-to-the-heavens<br />
aggravating. It’s a mystery wrapped in riddle<br />
inside an enigma.<br />
And here’s the punch line: The exam is a metaphor for the CISSP<br />
credential itself. The CISSP is the undisputed heavyweight champion<br />
of infosec certifications, the gold standard, the pièce de résistance. Yet<br />
it’s routinely ridiculed as a “paper certification,” lacking depth or practical<br />
application. Even those who proudly use it like a third name—<br />
“Hi, I’d like to order a pizza; name’s John Doe, CISSP”—privately<br />
acknowledge that the cert isn’t all that it’s cracked up to be.<br />
Did I pass? Yeah, I passed. And oh, what a relief. After I finished, I<br />
had absolutely no idea how I did. OK, everybody says that, but for some<br />
reason I thought I’d be different. I walked out with this feeling like I’d<br />
simultaneously way overprepared and yet…somehow…failed anyway.<br />
I still haven’t decided if that’s a good thing. It’s all part of the general<br />
weirdness surrounding this exam and certification.<br />
photographs by DANA SMITH/BLACK STAR<br />
www.infosecuritymag.com 73
<strong>Professional</strong> <strong>Certification</strong><br />
10 FAQs RE:CISSP<br />
1. What is the CISSP?. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 74<br />
2. What are the requirements for obtaining a CISSP? . . . . . . . 74<br />
3. Why get a CISSP? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 75<br />
4. What’s the exam like? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 75<br />
5. What subjects does the exam cover?. . . . . . . . . . . . . . . . . . . 76<br />
6. How hard is the exam? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 78<br />
7. What should I study? . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 84<br />
8. Do I need to take one of the CISSP exam-cram classes?. . . 84<br />
9. What other security certifications are available?<br />
And which one is “best” for me? . . . . . . . . . . . . . . . . . . . . . . 86<br />
10. Does the CISSP deserve its reputation? . . . . . . . . . . . . . . . . 88<br />
74 Information Security June 2003<br />
This article is an attempt to explore, expose<br />
and possibly resolve some of these issues. Over<br />
the past eight months, I took the “full immersion”<br />
route to preparing for the CISSP exam. I<br />
read a half-dozen CISSP prep books, including<br />
two 1,000-page tomes. I attended two week-long<br />
exam cram classes, including one offered by the<br />
(ISC) 2 Institute. I completed thousands of sample<br />
test questions from a variety of print and online<br />
sources. And I interviewed dozens of current and<br />
would-be CISSPs about the exam and credential.<br />
For comparative purposes, I also studied for and<br />
obtained another IT security certification—the<br />
TICSA.<br />
What I learned along the way should help the<br />
thousands of would-be test-takers gear up for this<br />
exam. Perhaps more importantly, the process has<br />
taught me a little about what’s right and wrong<br />
about the CISSP—both the exam and the certification<br />
itself.<br />
1. What is the CISSP?<br />
CISSP stands for Certified Information Systems<br />
Security <strong>Professional</strong>. The credential was created<br />
in 1991 by the International Information Systems<br />
Security <strong>Certification</strong> Consortium (ISC) 2 (www.isc2.<br />
org), a nonprofit organization that is the sole caretaker<br />
and credentialing body for the CISSP.<br />
(ISC) 2 is very specific about the purpose and<br />
scope of the CISSP. It’s not intended to certify<br />
hands-on expertise in any infosecurity technology.<br />
Nor does it certify practical expertise in any<br />
one of the 10 domains covered under its Common<br />
Body of Knowledge (or CBK—more on this later).<br />
In fact, it doesn’t certify expertise in anything,<br />
other than, perhaps, mastering the material in<br />
the CBK.<br />
(ISC) 2 officials are quite vocal about this focus—<br />
in part, one assumes, to deflect criticism of the<br />
CISSP. “Its ultimate purpose is to be able to provide<br />
an independent benchmark of your knowledge<br />
of the fundamentals of information security,”<br />
says (ISC) 2 president Jim Duffy. “It proves minimal<br />
competency. CISSPs do not walk on water,<br />
but they certainly do understand the information<br />
security profession.”<br />
One of the things that gives the certification<br />
weight in the industry is the sheer size of the<br />
CISSP community. We’re definitely not talking<br />
Augusta National here. By the time you read this,<br />
nearly 20,000 people will hold a CISSP. By the<br />
end of 2003, that number will climb to 25,000.<br />
That’s up from just 6,900 in 2001.<br />
The jury’s out on whether this growth enhances<br />
or detracts from the credibility of the certification<br />
and those who hold it. Some say it reinforces<br />
the CISSP’s image as infosec’s de facto credential.<br />
Others say it only proves that the exam and certification<br />
process aren’t stringent enough.<br />
Either way, the CISSP has become its own selfpromoting<br />
marketing vehicle. Perception is reality.<br />
The more people who obtain it, the wider<br />
exposure it gets. The wider the exposure, the<br />
stronger the perception that you’ve gotta have<br />
it. Run through this cycle a few times, and it’s<br />
not surprising that even those who ridicule the<br />
CISSP are now lining up to get one.<br />
2. What are the requirements<br />
for obtaining a CISSP?<br />
There are basically three steps. I won’t dwell<br />
on these, since they’re explained in detail on the<br />
(ISC) 2 Web site and elsewhere.<br />
First, you have to apply for certification. To<br />
qualify, you have to have at least four years of professional<br />
experience across the 10 CBK domains.<br />
Alternatively, you must have three years experience<br />
plus a college degree. You also have to agree<br />
to the (ISC) 2 Code of Ethics and provide background<br />
information on things like felony convictions<br />
and involvement with “hackers.”<br />
The second step is to pass the exam, which<br />
costs $450 a sitting. If you fail the first time, you<br />
can retake it as soon (and often) as you want,<br />
though you have to pay $450 each time.<br />
Third, if you pass, you’re required to obtain<br />
written endorsement from someone who is “familiar<br />
with your professional experience,” preferably<br />
another CISSP.<br />
The certification is valid for three years, during<br />
which time you have to accumulate 120 continuing<br />
professional education (CPE) units through<br />
activities such as serving on industry boards, delivering<br />
presentations or publishing security articles<br />
or books.
3. Why get a CISSP?<br />
Most current and would-be CISSPs say the primary<br />
reason they want a CISSP is to increase their<br />
marketability. “The reason I put the effort into<br />
getting the certification in the first place was to<br />
advance my career,” says Brian Taylor, a network<br />
analyst with New England Research Institutes<br />
(NERI). “The job postings out there frequently require<br />
or mention the certification as an advantage.”<br />
Other motivations include filling in knowledge<br />
gaps, earning peer recognition, expanding one’s<br />
professional network and contributing to the development<br />
and maturation of the profession.<br />
“It’s worth the effort if it keeps one marketable<br />
in a down-turned economy,” says George Johnson,<br />
a software engineer at EMC. “As for my current<br />
job, I’m not sure that it matters a great deal or<br />
means anything to my immediate line of management<br />
in the short term, but there is another<br />
process at work that is raising the security awareness<br />
of management.”<br />
One benefit of CISSP certification—for me, the<br />
largest benefit—is that in preparing for the exam,<br />
you’re going to learn a lot about subjects you<br />
didn’t know about before, and probably<br />
wouldn’t have an excuse or occasion to<br />
learn about otherwise. I’ve always wanted<br />
to learn about how Kerberos works under<br />
the hood, but it wasn’t until I started studying<br />
for the CISSP that I was compelled to<br />
do so. The same thing applies to hundreds<br />
of subjects covered in the CBK.<br />
Sure, some of this material is boring and<br />
impractical. But if you’re genuinely interested<br />
in information security, studying for<br />
the CISSP exam will give you a very strong<br />
knowledgebase. The exam covers maybe<br />
1 percent of what you study. But no matter<br />
what you think about the exam or the credential<br />
itself, the important thing is that<br />
you’ve learned the material anyway—provided<br />
you’ve done your homework, of<br />
course. And that, I think, is what sets the<br />
CISSP apart from other security certifications.<br />
You’re simply not going to get as<br />
broad an overview of all-things security<br />
from other certifications.<br />
4. What’s the exam like?<br />
The exam is 250 multiple-choice questions.<br />
Only 225 of these questions are used<br />
in computing your score; the other 25 are<br />
“experimental” questions that (ISC) 2 might<br />
use as actual questions on future tests.<br />
However, you won’t know which 25 are<br />
experimental, so give your best effort on<br />
all 250. Also, don’t leave any questions<br />
blank; there’s no penalty for guessing.<br />
The questions are weighted differently, adding<br />
up to 1,000 points. To pass, you have to get 700<br />
out of 1,000. Approximately 70 percent of candidates<br />
pass on their first try.<br />
(ISC) 2 reveals your numerical score only if you<br />
fail the exam. Candidates who pass the exam<br />
aren’t told their scores for two reasons, says Lee<br />
Schroeder, president of Schroeder Measurement<br />
Technologies, the CISSP exam contractor.<br />
“The primary reason is that we don’t intend<br />
this exam to be used to differentiate between<br />
passing candidates for things such as hiring or<br />
promotion,” he says. “We don’t want to facilitate<br />
a setting where an employer is looking at two<br />
CISSPs, and uses their scores to differentiate<br />
between them.”<br />
The other reason, Schroeder says, has to do<br />
with the exam’s scoring system, a complex mathematical<br />
model called “item response theory.”<br />
Questions are constantly cycled in and out of the<br />
CISSP exam, creating different exam forms. The<br />
objective with each form is to create a consistent<br />
range of difficulty. But since no two forms have<br />
exactly the same difficulty level, the number of<br />
www.infosecuritymag.com 75
<strong>Professional</strong> <strong>Certification</strong><br />
questions constituting a passing score varies from<br />
test to test.<br />
It’s a valid scoring system, but one in which two<br />
candidates with the exact same scaled score (say,<br />
750 points) may have answered a different number<br />
of questions correctly. Rather than try to explain<br />
all this to successful candidates, (ISC) 2 opts<br />
to simply reveal that they “passed.”<br />
5. What subjects does the exam cover?<br />
Before I tell you about the exam, I’ll tell you what<br />
I can’t tell you. Before you sit for the exam, you<br />
have to agree not to discuss the exam’s content or<br />
questions with anyone during or after the test. By<br />
breaking the seal on the exam booklet, you agree<br />
to abide by these rules.<br />
So, while I can’t tell you about the exam content<br />
“I attended [the Intense School boot<br />
camp] class and studied for two hours<br />
before the test. I didn’t study outside<br />
of class or take any of the practice tests.<br />
I did take almost six hours to complete<br />
the test, as I considered each question<br />
in the context of my own career of 15<br />
years in computer security.”<br />
–RANDY CROLLEY, Senior Computer<br />
Security Engineer, Department of<br />
Energy’s Savannah River Site<br />
“ ”<br />
CANDIDATE COMMENTS<br />
“I came out of the exam feeling<br />
like I had underprepared. I was<br />
fairly confident that I had<br />
passed, but not confident<br />
enough to tell people I<br />
passed. I knew that if I failed<br />
it would be very close.<br />
“I felt and continue to feel<br />
that the worst enemy you<br />
can have in that exam is to over-think the questions. The<br />
(ISC) 2 [boot camp] class was very good at making you get<br />
in the mind-set of thinking in a manner that would allow<br />
you know what (ISC) 2 was looking for.”<br />
–DAVE DRAPER, Director of Engineering Services, GeoTrust<br />
Here’s what other recent CISSP<br />
candidates had to say about the exam,<br />
their study plan and the certification itself.<br />
“Here are some tips when taking the<br />
exam. First, don’t jump ahead. The test<br />
seems to have a lot of double negatives,<br />
so it’s critical to read the whole question<br />
before answering. I brought a magnifying<br />
ruler to the exam. I used it to force<br />
myself to read line by line. It helped immensely.<br />
Second, if I knew the answer<br />
with 90 percent certainty, I chose the<br />
answer and never looked back. Third, if<br />
I didn’t with 90 percent certainty know<br />
the answer, I circled the test question<br />
in the booklet and moved on. Fourth,<br />
I went back through the circled test<br />
questions and eliminated<br />
answers I knew with 90<br />
percent certainty were<br />
wrong. Fifth, I worked the<br />
unanswered questions one<br />
at a time and then erased<br />
the circle around the<br />
question once I had answered. Sixth—when all else failed—<br />
I guessed! One last thing: Save enough time to transfer<br />
the answers from the work booklets to the answer sheet.<br />
It takes about 30 minutes.”<br />
–TOM MADDEN, CISO, Centers for Disease Control<br />
“The CISSP certification is widely recognized as being the<br />
security certification to have. [The exam is] more difficult<br />
than the Microsoft certifications.”<br />
–DAVID BURNS, British Petroleum<br />
“It reminded me of taking a Navy promotion exam—the<br />
same format, but an additional 100 questions. Because I<br />
don’t use most of the information in daily [activities], the<br />
depth of the exam questions took me by surprise. I was<br />
confused by some of the questions.”<br />
–LT. GEORGE KONEN, Naval War College<br />
“A lot of the questions were kind of misleading. And a<br />
lot were just plain common sense. I felt you either knew<br />
the answer or you didn’t. The exam should only take<br />
three hours at the max.”<br />
–JOHN MILLS<br />
76 Information Security June 2003<br />
“Looking back, [the exam] seemed easy. I only did CCCure<br />
tests for a few days after [the (ISC) 2 exam-cram] course.<br />
Got a passing grade on most of them (“hard” level, not<br />
“pro” level). So that gave me confidence as well. I never<br />
opened the two books I bought. I thought the (ISC) 2 class<br />
should have put more emphasis on crypto and access<br />
control.”<br />
–VENKAT PERUMAL, CFO, AGCS Inc.<br />
“I could have studied until I was blue in the face. However,<br />
nothing could have prepared me for this examination. I<br />
would say that [number omitted] of the questions don’t<br />
require too much guesswork, [number omitted] are good<br />
for interpretation, and the last [number omitted], you<br />
should bring a coin and flip it.”<br />
—VINCENT JETTE,<br />
Senior Network Engineer, BIC International<br />
photograph by CREATAS/PICTUREQUEST
<strong>Professional</strong> <strong>Certification</strong><br />
itself, I can tell you about the scope and<br />
type of content, at least in general terms.<br />
This may not seem like much, but the<br />
CISSP test is like no other I’ve ever<br />
taken, at any level. Simply knowing what<br />
types of questions to expect when you<br />
walk in that room will definitely give you<br />
a leg up.<br />
The company line is that the CISSP<br />
exam tests the candidate’s knowledge of<br />
subjects covered in the 10 CBK domains.<br />
Dozens of books and online resources<br />
dive into these domains in great detail,<br />
so I’ll merely list them here:<br />
• Access Control Systems and<br />
Methodology<br />
• Application and Systems<br />
Development Security<br />
• Business Continuity and<br />
Disaster Recovery Planning<br />
• Cryptography<br />
• Law, Investigations and Ethics<br />
• Operations Security<br />
• Physical Security<br />
• Security Architecture and Models<br />
• Security Management Practices<br />
• Telecommunications and<br />
Networking Security<br />
Some of these domains cover a lot<br />
more material (and in greater depth)<br />
than others. For instance, Telecommunications/Network<br />
Security and Cryptography<br />
are both huge domains, while<br />
Physical Security and Law, Investigations<br />
and Ethics are comparatively small.<br />
The quantity of topics and depth of<br />
detail can be deceiving. Many candidates<br />
score poorly on the Physical Security and<br />
Law sections because they overprepare<br />
on the big domains and underprepare<br />
on the small ones. It’s unlikely that the<br />
exam will present you with an equal distribution<br />
of questions across all 10 domains.<br />
But even if I could tell you which<br />
domains were hit hardest on my exam,<br />
it wouldn’t matter, because the exam<br />
constantly changes. The only safe bet is<br />
to study each domain thoroughly, and<br />
don’t be surprised when the exam seems<br />
weighted toward a handful of domains or<br />
subjects.<br />
Another common mistake is to adopt<br />
a single, uniform approach to learning<br />
the material. The domains are very different,<br />
requiring different learning techniques.<br />
Let me explain what I mean.<br />
In some domains—for example, Crypto,<br />
Architectures/Models and Telcom/<br />
Networking—the topics are fact-oriented<br />
and black and white. You either know<br />
the bit size of an MD5 message digest or<br />
you don’t; you either know what Bell-<br />
LaPadula’s star-property rule is or you<br />
don’t; you either know what OSI layer<br />
IPSec operates at or you don’t. Learning<br />
this material requires a lot of rote memorization.<br />
You may know some of this<br />
material from your daily work, but you<br />
won’t know most of it.<br />
While memorizing a bunch of facts<br />
and details is an effective strategy for<br />
some domains, it won’t work as well for<br />
others, such as Security Management,<br />
BC/DR, Physical Security or Law/Ethics.<br />
The material in these sections is more<br />
contextual and interpretative, focusing<br />
more on standards, principles or best<br />
practices. Here, you should focus on the<br />
application of the facts, not the facts<br />
themselves.<br />
For example, there are eight steps to<br />
perform in a business impact analysis.<br />
The exam is unlikely to ask you to identify<br />
what happens in a particular step—<br />
that much is intuitive. Rather, it would<br />
ask you to identify the appropriate order<br />
of the steps, or to determine the most<br />
or least important step within a given<br />
scenario.<br />
These are oversimplified examples,<br />
and, of course, each domain contains a<br />
mix of factual and interpretive material.<br />
The point is that the CISSP exam has<br />
a way of exposing flaws in your study<br />
habits. If you haven’t memorized enough<br />
in the “black and white” domains—or if<br />
you can’t apply your knowledge in others—you<br />
might struggle on the exam.<br />
6. How hard is the exam?<br />
This is probably the most frequently<br />
asked question about the CISSP exam.<br />
It’s also the hardest to answer.<br />
The exam is best characterized as an<br />
“inch deep and a mile wide.” Whether<br />
this makes it easy or difficult is a matter<br />
of perspective.<br />
On the one hand, the exam is easy<br />
because it’s multiple choice, with four<br />
possible answers per question. Out of<br />
the 250 questions, the slight majority are<br />
fact-oriented questions. (I’m prohibited<br />
from revealing the approximate number<br />
of questions, and I probably wouldn’t<br />
anyway, since the distribution of question<br />
78 Information Security June 2003
<strong>Professional</strong> <strong>Certification</strong><br />
types changes constantly). These questions are<br />
straightforward, well-written questions with clearly<br />
delineated answers. If you do your homework,<br />
you’ll answer most of these questions without any<br />
problem.<br />
Another large chunk of questions are straightforward<br />
interpretive questions. They set up a scenario<br />
in which you have to determine the best<br />
course of action. Again, the answers are usually<br />
clear if you’ve studied.<br />
One of the things that makes some of the questions<br />
easy (or at least straightforward) is that the<br />
exam is almost totally devoid of platform-, deviceor<br />
application-specific material. For example, you<br />
won’t be asked to create a Group Policy Object in<br />
Win2K Active Directory, convert Unix file permissions<br />
from alpha to octal characters or create<br />
FireWall-1 ACLs. You might be tested on the difference<br />
between block and stream ciphers, or between<br />
asymmetric and symmetric encryption, but<br />
you won’t be required to analyze algorithms or<br />
perform mathematical computations of any sort.<br />
You might be asked to explain the difference between<br />
code assemblers, compilers and interpreters,<br />
but you won’t be asked to assemble, compile or<br />
interpret code.<br />
The remaining questions are difficult, but for<br />
different reasons. Half of these are legitimate<br />
questions about obscure facts, or legitimate interpretative<br />
questions where the answer just isn’t<br />
clear. These are good, tough questions. You just<br />
have to know the answer or be able to dope it out.<br />
However, there’s a chunk of questions that are<br />
difficult for all the wrong reasons. They’re poorly<br />
worded, misleading or simply evasive (see “Frustrating<br />
Questions,” p. 82). Evasive: that’s the word that<br />
first came to mind when I walked out of the exam.<br />
It just seems like these questions serve no purpose<br />
other than to confuse and frustrate you.<br />
It’s because of these questions that you won’t<br />
have an intuitive sense if you passed the exam.<br />
And it’s because of these questions that the CISSP<br />
exam often gets a bad rap. Even though these<br />
questions comprise a comparatively small part of<br />
the exam, they’re the ones that stick in your craw<br />
as you walk out the door.<br />
“I felt the questions themselves were short and<br />
CONTINUED ON PAGE 82<br />
80 Information Security June 2003
<strong>Professional</strong> <strong>Certification</strong><br />
Frustrating Questions<br />
Anybody who says the CISSP exam is easy isn’t telling the whole story.<br />
There are plenty of difficult questions—some legitimate, some goofy.<br />
When taking the CISSP exam, expect to<br />
encounter at least a couple dozen questions<br />
that will frustrate the hell out of you. (ISC) 2<br />
exam designers claim these (and all) questions<br />
are psychometrically valid. Annoying or not, they’re<br />
a useful mechanism for separating qualified candidates<br />
(infosecurity professionals who have mastered the CBK to<br />
an acceptable level) from unqualified professionals (those<br />
without mastery of the material who are simply good at<br />
taking multiple-choice exams).<br />
Whether you buy this line of reasoning or not, these<br />
questions will drive you nuts if you’re not expecting them.<br />
For discussion purposes, I’ve divided these questions into<br />
four categories, comprising both the “factual” and “interpretive”<br />
question types. With each of these categories, I’ll<br />
try to explain what makes the question difficult, and offer<br />
an example. These examples may be a bit exaggerated to<br />
illustrate a point. That said, they’re not far from the truth,<br />
either.<br />
1. Obscure facts. Several questions require you<br />
to recall very specific details from the CBK. These are<br />
absolutely legitimate, fact-oriented questions that don’t<br />
require a lot of interpretation. The problem is that you<br />
just don’t know or can’t remember the answer unless you<br />
happened to study it recently, have hands-on experience<br />
with it, or have a photographic memory.<br />
Here’s an example:<br />
1. Which of the following characterizes the Data Encryption<br />
Standard (DES) Electronic Code Book (ECB) mode?<br />
a. “Stream mode” cipher, first ciphertext block is<br />
XORed with next text block.<br />
b. “Block mode” cipher, 64-bit plaintext blocks loaded<br />
sequentially.<br />
c. “Block mode” cipher, 64-bit data blocks processed<br />
individually one at a time.<br />
d. “Stream mode” cipher, keystream is XORed with<br />
message stream; simulates one-time pad.<br />
The answer is “C,” but it’s a really hard question because<br />
it’s very detailed and technical. Moreover, the options<br />
include both legitimate DES modes that aren’t ECB (answer<br />
B is cipher block chaining (CBC); answer D is output feedback<br />
mode (OFB)) and a made-up answer (answer “A”<br />
also describes CBC, except CBC is a block mode cipher).<br />
You either know the answer here or you don’t. It’s<br />
impossible to dope it out if you didn’t study it.<br />
2. Misleading interpretive questions. A chunk of<br />
questions ask you to pinpoint the “best” answer or course<br />
of action given a scenario or context. Granted, by their very<br />
nature, these questions are very difficult to craft, but the<br />
CISSP exam seems to have more than its share of doozies.<br />
Selecting the best answer to these questions is problematic<br />
because (a) what you would consider “best” isn’t one<br />
of the options; or (b) you need more context to determine<br />
what the exam-creators would consider best. Here’s an<br />
example question that captures both of these problems:<br />
2. Which of the following is usually considered to be<br />
the best type of firewall:<br />
a. Static packet filter<br />
b. Application-layer proxy<br />
c. Circuit-level firewall<br />
d. PC firewall<br />
Many people would consider a dynamic/stateful-inspection<br />
firewall to be the “best” general-purpose firewall<br />
available today. But that’s not one of the answers. So<br />
you’re left to determine what’s best from the list of four<br />
“next-best-but-not-really-best” alternatives.<br />
Compounding the problem, you’re not given any context<br />
in which to make an educated decision. “Best” under what<br />
circumstances? What type of access control or traffic filtering<br />
are you trying to enforce? What type of network or<br />
hosts is the firewall intended to protect?<br />
Moreover, the answers are not “equal” in the sense that<br />
82 Information Security June 2003<br />
CONTINUED FROM PAGE 80<br />
easy to read,” says Ty Whitten, a security engineer<br />
at Guardent Corp. “But I felt sometimes that the<br />
answers didn’t represent the questions well at all.<br />
Either the answers were way off base, or I would be<br />
left with two answers in which both could have<br />
been correct. I also felt the material I studied was<br />
way more detailed than the vague questions and<br />
answers that were on the test.”<br />
(ISC) 2 officials contend that the CISSP exam<br />
doesn’t receive an unusual number of complaints<br />
relative to other certification exams. They point<br />
to the fact that candidates are encouraged to<br />
comment on questions when taking the exam—<br />
comments that are carefully evaluated when examining<br />
test incongruities and deciding which<br />
questions should be retired.<br />
Moreover, (ISC) 2 and its test developers say<br />
that the degree to which a question is annoying is
they’re not all of the same type or quality. Is this on<br />
purpose or by accident? Again, you can only guess.<br />
OK, you probably wouldn’t select “D,” because a<br />
PC firewall is a specific example of a host application<br />
filter. The other three options are core technologies,<br />
not form-factor examples of those technologies.<br />
Option A, static packet filter, is a “first-generation”<br />
network-layer firewall that does basic IP address and port<br />
filtering. It’s probably the widest deployed firewall today,<br />
so if “best” means “most accepted,” option A would be<br />
your answer.<br />
However, if by “best” they mean “most able to filter<br />
traffic at a granular application header or payload level,”<br />
then “application-layer proxy” is your answer. But wait:<br />
Circuit-level firewalls are “better” than static packet filters<br />
because they filter on Transport layer headers as well as<br />
IP headers; and they’re “better” than application proxies<br />
because they can filter on a wider variety of protocols and<br />
are easier to maintain. But do two “betters” add up to one<br />
“best”?<br />
You get the point. You have to determine what “best”<br />
means before you can select the “best” (er, “next-best”)<br />
answer. This question is aggravating because it doesn’t test<br />
your knowledge of firewalls—how they work, how they<br />
compare, which one’s most applicable to a given scenario—but<br />
rather your ability to guess how the exam creators<br />
would define “best.”<br />
3. Questions where more than one answer is<br />
correct. In some questions, more than one answer seems<br />
correct. And, indeed, more than one is correct, depending<br />
on your perspective.<br />
3. Which OSI layer(s) does SSL operate at?<br />
a. Layer 4<br />
b. Layer 5<br />
c. Layers 4 and 5<br />
d. Layers 5 and 7<br />
Each of these is correct under different scenarios. In preparing<br />
for the exam, I came across different sources that actually<br />
gave these answers. Which one is correct? More to the point:<br />
Which answer would (ISC) 2 consider correct? Guess!<br />
With questions like these, it’s clearly a matter of interpretation<br />
and context, and one would hope the CISSP exam<br />
would steer away from them. Unfortunately, it doesn’t.<br />
4. Confusing wording in the question itself.<br />
Perhaps the most frustrating questions on the CISSP exam<br />
are ones that force you to guess at exactly what the question<br />
is trying to ask. A sloppily written phrase forces you to<br />
interpret the meaning of the question—do they mean this,<br />
or do they mean that?—which in turn affects your interpretation<br />
of the answers.<br />
4. Which of the following best describes a “protective<br />
profile”?<br />
a. Implementation-dependent statement of security<br />
needs for a set of general IT products.<br />
b. Management-level description of resources necessary<br />
to protect a security domain.<br />
c. General framework of physical security requirements<br />
for a data center.<br />
d. Includes the “Target of Evaluation” description of<br />
an IT product and its purpose, but not necessarily<br />
from a security perspective.<br />
If you studied the Common Criteria security evaluation<br />
standard, you know that the “protection profile” is an<br />
implementation-independent statement of security requirements<br />
within the CC. Ah, but the question says protective<br />
profile—and what’s worse, it puts the phrase in quotes.<br />
Is this a simple spelling or usage mistake? Or are the exam<br />
developers specifically trying to bait you into answering<br />
the question as though it specifies “protection profile,”<br />
when in fact they mean something more generic and<br />
completely unrelated to the Common Criteria?<br />
It may seem like I’m picking on (ISC) 2 and the exam creators<br />
by going into this level of detail. But to be forewarned<br />
is to be forearmed, and no book, study guide or boot camp<br />
prepared me for these types of questions, and no sample<br />
test I came across quite captured the essence of these<br />
questions. Everybody talks about how some CISSP exam<br />
questions are frustrating. Hopefully, I’ve illustrated why<br />
they can be frustrating. ◗<br />
–ANDREW BRINEY<br />
of little significance in determining its statistical<br />
validity. The goal with the exam and exam questions<br />
is to show an acceptable level of discrimination<br />
between high-scoring candidates and lowscoring<br />
candidates. If the cluster of high-scoring<br />
candidates—those who have adequately mastered<br />
the CBK—consistently answer a question correctly<br />
while the low-scoring candidates answer it incorrectly,<br />
then the degree to which the question is<br />
subjectively “vague” or “evasive” to either group<br />
is inconsequential.<br />
“We want questions such that high-scoring candidates<br />
tend to get them right, and low-scoring candidates<br />
tend to get them wrong,” says Lee Schroeder.<br />
One other thing: the CISSP exam is long—gruelingly<br />
long, in my opinion. You’re allotted six<br />
hours to complete it, and most people take at<br />
least three. It took me about five hours.<br />
www.infosecuritymag.com 83
<strong>Professional</strong> <strong>Certification</strong><br />
84 Information Security June 2003<br />
7. What should I study?<br />
No one book covers everything you need to know<br />
to prepare for the CISSP exam. There are at least<br />
three 1,000-page “all-in-one” prep guides out<br />
there. I’ve read two of these, and as comprehensive<br />
as they are, neither is sufficient in and of itself.<br />
On the other hand, you shouldn’t feel compelled<br />
to dive into everything in (ISC) 2 ’s study<br />
guide. Accept the fact that you’ll never have<br />
enough time to study the CBK in depth, nor<br />
should you attempt to. There’s just too much<br />
information.<br />
The first thing you should do is review the<br />
main topics in each domain. This will reveal your<br />
strengths and weaknesses. Then, take the plunge<br />
and buy at least one of the “all-in-one” books (see<br />
“Briney’s Stack O’ Reading,” opposite). As you read<br />
each chapter/domain, take the practice exams in<br />
the book and online. Among other sites, www.<br />
cccure.org allows you to develop practice quizzes<br />
targeting specified domains.<br />
Plan to take at least two full-length practice tests<br />
before sitting for the exam. However, keep in<br />
mind that these practice exams are intended to<br />
test your knowledge and understanding of the<br />
CBK. None of the practice tests I came across<br />
adequately prepared me for the “difficult-for-thewrong-reasons”<br />
questions.<br />
8. Do I need to take one of<br />
the CISSP exam-cram classes?<br />
It’s hard for me to say whether you need to sign up<br />
for one of these courses. What I can tell you is that<br />
I took two of them, and they were both very useful.<br />
The first one I took was Intense School’s sevenday<br />
1 CISSP Boot Camp (www.intenseschool.com).<br />
The instructor was Shon Harris, who wrote one of<br />
the popular all-in-one prep books and developed<br />
all the materials for the course, including more<br />
than 1,200 pages of PowerPoint slides, 30-40 practice<br />
questions per domain and a full-length practice<br />
exam.<br />
The Intense School course also provides you<br />
with a variety of supplemental materials, including<br />
RFC 2196: The Site Security Handbook, NIST’s<br />
Guidelines for Network Security Testing, an<br />
Internet Firewalls FAQ and a half-dozen other<br />
documents. Having all this stuff in one place saves<br />
a lot of time.<br />
The second boot camp was offered by the (ISC) 2<br />
Institute, the for-profit arm of the nonprofit (ISC) 2<br />
certification body. If you think that (ISC) 2 ’s ties to<br />
this course will give you an inside track on the<br />
exam, think again. By design, the instructors have<br />
no input into the exam itself, and they’re bound<br />
by the same restrictions that all CISSPs are: they<br />
can’t discuss exam content.<br />
The five-day (ISC) 2 boot camp was team-taught<br />
by Sandy Sherizen and John Glover, both of whom<br />
really knew their stuff. They traded off on domains,<br />
Sherizen focusing on the “soft” domains<br />
and Glover on the technical ones. This was mostly<br />
effective, though their different teaching styles<br />
sometimes clashed. The time devoted to each domain,<br />
the subjects covered and the depth of discussion<br />
was very similar to Intense School’s approach.<br />
However, there wasn’t 100 percent overlap. For<br />
instance, Intense devoted more time to remote<br />
authentication than (ISC) 2 , while (ISC) 2 devoted<br />
more time to wireless security than Intense.<br />
Intense School’s course materials were marginally<br />
superior to (ISC) 2 ’s. (ISC) 2 ’s consisted primarily<br />
of a two spiral-bound notebooks with printed<br />
reproductions of the PowerPoint slides covered in<br />
class. While Intense also took this approach, the<br />
material was backed up by written documentation<br />
on each page. This helped a lot when I went back to<br />
review the materials after the course wrapped up.<br />
After completing each domain, the (ISC) 2<br />
instructors reviewed 10 practice questions with<br />
the entire class. I preferred Intense’s approach,<br />
in which you had the questions in writing and<br />
answered them at your own pace—just like on the<br />
exam. (ISC) 2 also offered a practice exam at the<br />
end of the course, but it was only 100 questions<br />
long, compared to Intense’s full-length, 250-question<br />
exam. Then again, the (ISC) 2 class had the<br />
advantage of using retired questions from the<br />
actual exam, which to some candidates might be<br />
a real value-add.<br />
Exam-cram courses aren’t cheap. Intense’s selling<br />
price ranges between $2,600 and $2,900, while<br />
(ISC) 2 ’s list price is $2,400. You get a few more<br />
frills with Intense’s approach: most costs related to<br />
hotel and meals are included in the course fee.<br />
If you’re going to sign up for a boot camp, the<br />
natural question arises: Should I take it before I<br />
start studying, or after I’ve already done most of<br />
my homework? I did it both ways, and would suggest<br />
these courses work better as a primer, not a<br />
review. They set out a framework of topics and<br />
expose holes in your knowledge. Better to have<br />
plenty of time to fill in those holes before sitting<br />
for the exam.<br />
Both courses boast successful pass rates. Including<br />
myself, 15 out of the 16 people in Intense<br />
School’s boot camp passed the exam. Of the 11<br />
students I heard from after the (ISC) 2 class, nine<br />
passed. The standard pass rate for all CISSP<br />
candidates is 70 percent. You do the math.<br />
If you sign up for a five- or seven-day boot<br />
camp, be prepared for your mental buffer to run-<br />
1<br />
The typical Intense School CISSP Training Program is<br />
seven days, though the course I attended was five days. CONTINUED ON PAGE 86
Briney’s Stack O’ Reading<br />
No one resource can prepare you for the CISSP. At the same time, there are literally hundreds, perhaps thousands,<br />
of books and Web sites covering some aspect of the CBK. The goal is to read widely, if not necessarily deeply,<br />
in each domain. Remember, the exam is a mile-wide and an inch deep. Tailor your study plan accordingly.<br />
photograph by AMY HIGHT<br />
BOOKS<br />
An Amazon search reveals 15 books with<br />
“CISSP” in the title. There’s even a CISSP for<br />
Dummies! I read every page of two 1,000-page<br />
“all-in-one” guides plus a smattering of other<br />
books and online resources. I also dabbled<br />
around and skimmed a half-dozen other books.<br />
All-in-One CISSP <strong>Certification</strong><br />
By Shon Harris (McGraw Hill Osborne, 2002)<br />
971 pages + CD, $80<br />
This book is extremely comprehensive, and<br />
Harris has a knack for explaining complex<br />
technical topics in layman’s terms without talking<br />
down to the reader. Harris also teaches an<br />
exam-cram class for Intense School, and has sat for (and<br />
passed) the CISSP exam on two separate occasions—both<br />
of which lend an air of authority to this guide.<br />
While the text is good, the graphics in this book leave<br />
something to be desired. Some are too sketchy or generic<br />
to add anything to the textual discussion. Others are<br />
clearly space fillers, like the half-page photo of a fire<br />
extinguisher with the caption, “Portable extinguishers<br />
are marked indicating what type of fire they should be<br />
used on.” (Gee, tell me more).<br />
Each chapter/domain ends with a list of quick tips,<br />
which were very helpful. Harris also gives you 20-30<br />
practice questions at the end of each domain, along<br />
with a CD containing hundreds of additional questions<br />
(the new edition reportedly contains 1,300 total questions<br />
with explanations). While the practice questions were<br />
good, taken together they’re easier than many of the<br />
actual exam questions, which might give you a false<br />
sense of security.<br />
The CISSP Prep Guide (Gold Edition)<br />
By Ronald Krutz and Russell Vines (Wiley, 2003)<br />
945 pages + CD, $80<br />
The Krutz and Vines guide is also excellent. The Gold<br />
Edition is actually the combination of two other Wiley<br />
books by the same authors: the original CISSP Prep<br />
Guide and the Advanced CISSP Prep Guide. The Gold<br />
Edition also contains updated content based on reader<br />
suggestions.<br />
I’m glad I read this book after Harris’s book, because<br />
the presentation is tighter and more accelerated.<br />
There’s not as much detail as in Harris’s book, but<br />
the discussion moves along more quickly.<br />
The Krutz and Vines book has a lot of practice questions,<br />
660 in all, in addition to a CD-ROM containing two<br />
complete practice exams from Boson (see below).<br />
Most of the sample and bonus questions after each<br />
domain are about the same level as Harris’s questions—<br />
in some cases, they’re a little more advanced.<br />
Also included after each domain/chapter are several<br />
“advanced sample questions” that the authors claim<br />
“are at a level commensurate with that of the<br />
CISSP Examination.” Well, that’s not strictly<br />
true. They are more difficult than the sample<br />
and bonus questions, giving you a sense of<br />
the level of detail to which you need to study.<br />
However, they don’t capture the way in which<br />
the CISSP exam’s questions are difficult.<br />
Some of Krutz and Vines’s advanced questions<br />
are extremely verbose, which is definitely<br />
not the style of the CISSP exam. Others ask<br />
you to do computations or visual analysis—<br />
again, not the exam’s M.O.<br />
In any case, the authors provide long<br />
explanations to each answer, which helps.<br />
The Total CISSP Exam Prep Book<br />
By Thomas Peltier and Patrick Howard (Auerbach, 2002)<br />
286 pages, $60<br />
The title is misleading, because this is basically a<br />
book of sample test questions. Each chapter covers<br />
a domain, and each domain includes 25 practice study<br />
questions with explained answers. The good thing about<br />
this book is that it cites the sources from which the questions<br />
are drawn—down to the page number. This is a real<br />
bonus if you want to follow up. At the end of the book<br />
there’s a full-length practice exam, which also comes<br />
with answer explanations and citations.<br />
OTHER RESOURCES<br />
Boson<br />
www.boson.com/tests/secure.htm<br />
The Boson Web site offers three practice CISSP exams,<br />
250 questions each. (Two of these exams are included<br />
on the Krutz and Vines CD-ROM.) Each exam costs $40.<br />
Don’t take Boson Exam #1. Exams #2 and #3 have<br />
decent questions, though many candidates feel that<br />
CCCure’s are better.<br />
CCCure<br />
www.cccure.org<br />
An indispensable site for CISSP candidates. Contains<br />
tons of CBK resources and thousands of practice<br />
questions. The CISSP quiz page lets you specify the number<br />
of questions you want to take, the level of difficulty<br />
(from “novice” to “pro”), and the CBK domains you want<br />
to cover. Best of all, it’s free—all you have to do is register.<br />
CISSP Cramsessions<br />
www.cccure.org, click on “Downloads” and go to “<br />
CISSP Study Guides”<br />
One way of identifying weaknesses is to compare<br />
your study plan to that of other CISSPs. Michael<br />
Overly’s Cramsession, in particular, is excellent—<br />
concise yet thorough, hitting on all the high points. ◗<br />
–ANDREW BRINEY<br />
www.infosecuritymag.com 85
<strong>Professional</strong> <strong>Certification</strong><br />
CONTINUED FROM PAGE 84<br />
neth over. Both courses I took did a good job mixing<br />
up the material by alternating technical- and<br />
management-oriented domains, but there’s no<br />
way to get around the huge volume of information<br />
you have to absorb.<br />
While Intense School and (ISC) 2 courses may be<br />
the most recognized CISSP boot camps, several<br />
other CISSP classes are available, ranging from<br />
one to seven days in length. One of these is The<br />
Training Camp (www.trainingcamp.com), which<br />
(ISC) 2 recently contracted as a course “reseller.”<br />
So, to answer the initial question, if you can get<br />
your boss to pay for a boot camp, and can afford<br />
the time out of the office, do it! You won’t necessarily<br />
learn anything different from an equivalent<br />
course of independent study, but a boot camp will<br />
give you a lot more confidence that you’re on the<br />
right track. The instructors can help you grasp<br />
complex topics, and you can band together with<br />
fellow students to form study groups. All of these<br />
things help you get motivated to do your homework—and<br />
pass the exam.<br />
9. What other security certifications are<br />
available? Which one is “best” for me?<br />
The CISSP may be the most popular security certification,<br />
but it’s far from the only one. You might<br />
be surprised to learn that there are at least 45<br />
information security-related professional certifications,<br />
according to <strong>Certification</strong> magazine. Thirty of<br />
these of these are vendor-neutral, while 15 are<br />
vendor-specific.<br />
I won’t attempt to discuss all or even most of<br />
these. Instead, I’ll discuss the basic categories,<br />
and suggest which certifications are recognized as<br />
the “leaders” in each. This ranking is obviously<br />
subjective, though I think it generally reflects how<br />
most infosec professionals feel.<br />
Benchmarks. These certifications are widely<br />
recognized and respected by professionals on all<br />
levels and in all sectors in the infosecurity industry.<br />
What’s more, they’re increasingly a prerequisite<br />
for many jobs, an indication that they are also<br />
recognized and respected by non-security managers<br />
and HR.<br />
In addition to the CISSP, I’d put ISACA’s<br />
Certified Information Systems Auditor (CISA)<br />
and SANS’s GIAC Security Essentials <strong>Certification</strong><br />
(GSEC) in this group. The CISA is the CISSP for<br />
the IT audit community, plain and simple. The<br />
GSEC is kind of the “anti-CISSP.” It’s more technical<br />
in nature and, like most of the 11 GIAC<br />
certifications, it has gained the respect of the<br />
techy community that the CISSP lacks.<br />
“Foundation” certifications. There are at least<br />
a half-dozen introductory certifications for professionals<br />
with one to three years of experience. Leading<br />
certifications in this category include (ISC) 2 ’s<br />
own Systems Security Certified <strong>Professional</strong> (SSCP)<br />
and the CIW Security <strong>Professional</strong> (CIW-SP).<br />
Vendor certifications. Many of the leading<br />
providers in the security space—Cisco, Symantec,<br />
Check Point, Tivoli and others—offer multiple<br />
certification levels, from baseline “administrator”<br />
to more advanced “expert” (some even offer<br />
“expert plus”).<br />
On a slightly more generic level is SANS’s vendor-agnostic<br />
GIAC Certified Firewall Analyst (GC<br />
FA) and GIAC Certified Intrusion Analyst (GCIA),<br />
both of which have an excellent reputation.<br />
<strong>Certification</strong>s for non-security professionals.<br />
As the visibility of IT security grows in the enterprise,<br />
so does the number of non-security professionals<br />
who have security-related responsibilities.<br />
Several certification programs have cropped up to<br />
fulfill this need, including SECURITY+, offered<br />
by CompTIA; and the TruSecure ICSA Certified<br />
Security Associate (TICSA). 2<br />
As I mentioned earlier, I sat for the TICSA exam<br />
to see how it compared to the CISSP. In a nutshell,<br />
if the CISSP is “an inch deep and a mile wide,” the<br />
TICSA is “two feet deep and 100 yards wide.”<br />
Obviously, the scope and breadth of topics covered<br />
pale by comparison to the CISSP. Then again, in<br />
places the TICSA content is actually deeper—more<br />
technical, more hands-on, more practical.<br />
(ISC) 2 could take a page from TruSecure’s book<br />
on question creation and exam delivery. To my<br />
recollection, few, if any, of the 75 questions on the<br />
TICSA exam were evasive or vague in the way that<br />
some CISSP questions are. Also, TruSecure partners<br />
with Thompson Prometric to deliver the<br />
exam. You can sit for the exam at any Thompson<br />
facility (there are 3,500 centers worldwide) whenever<br />
you want. And the TICSA exam is completely<br />
computer-based. As soon as I completed the exam,<br />
I was informed of my score and given a printout<br />
of how I did in each of 14 TICSA sections. See<br />
www.trusecure.com/solutions/certifications/ticsa.<br />
Advanced certifications. Several industry groups<br />
are jockeying to gain CISSP-like acceptance for<br />
their “advanced” certifications, which is one of the<br />
things the industry is sorely missing. In addition<br />
to the expert-level vendor certifications, advanced<br />
certs include SANS’s GIAC Security Engineer<br />
(GSE) and ASIS’s Certified Protection <strong>Professional</strong><br />
(CPP), a CISO-level certification covering human,<br />
physical and information security. Neither of these<br />
has achieved anywhere near the level of acceptance<br />
as the CISSP.<br />
To its credit, (ISC) 2 has recognized the need for<br />
more advanced (or targeted) certifications. As of<br />
May, it offers three certification “concentrations”<br />
that build upon the CISSP: the Information Sys-<br />
2<br />
TruSecure publishes Information Security.<br />
86 Information Security June 2003
<strong>Professional</strong> <strong>Certification</strong><br />
tems Security Engineering <strong>Professional</strong> (ISSEP), a<br />
certification developed in partnership with the<br />
National Security Agency; the Information Systems<br />
Security Management <strong>Professional</strong> (ISSMP),<br />
which validates advanced security management<br />
expertise; and the Information Systems Security<br />
Architecture <strong>Professional</strong> (ISSAP), which validates<br />
advanced technical knowledge and expertise.<br />
10. Does the CISSP<br />
deserve its reputation?<br />
There are really two questions here: Does the<br />
CISSP deserve to be the industry’s gold standard?<br />
And does the CISSP—and (ISC) 2 —deserve all the<br />
criticism it gets?<br />
The CISSP is frequently criticized because it<br />
doesn’t contain a lot of advanced material. People<br />
naturally assume that the “gold standard” should<br />
be the “best” in every way—not only the most popular<br />
or broadest in scope, but the most advanced<br />
and selective, too.<br />
“It’s not a certification that says, ‘I’m a damn<br />
good information security professional,” says Nan<br />
Smith, a newly minted CISSP and cyber security<br />
program manager for the Oak Ridge Institute<br />
for Science and Education. “To me, a certification<br />
should guarantee to the employer that you’ve<br />
made the effort to become good at what you’re<br />
doing, at what you know. To me, the CISSP doesn’t<br />
say that. It says, ‘Hey, I figured out what (ISC) 2<br />
wanted me to answer on the exam.’”<br />
In some ways, this is a legitimate critique. The<br />
CISSP is not and never will be equivalent to<br />
the “gold standard” in other fields—for example,<br />
the CPA for accountants. To obtain that level of<br />
respect, the CISSP would have to be sanctioned<br />
by regulatory and legal bodies, and recognized<br />
by communities outside of the infosecurity profession.<br />
But we’re really talking apples and oranges<br />
here. (ISC) 2 never intended the CISSP to be<br />
the CPA of infosecurity. Yes, the credential has<br />
acquired the reputation of pretending to be something<br />
it’s not. But that’s hardly (ISC) 2 ’s fault; it’s<br />
certainly not an image that was ever promoted by<br />
(ISC) 2 .<br />
Moreover, it’s unrealistic to expect (ISC) 2 to<br />
change the fundamental makeup of the exam to<br />
make it more “technical” or “advanced”—<br />
qualities that, in the minds of its critics,<br />
would make it truly representative of a<br />
gold standard. It is what it is. While you can<br />
alter the requirements and qualifications<br />
for sitting for the exam (which (ISC) 2 recently<br />
did), you can’t arbitrarily decide to<br />
change the basic charter or mission of the<br />
credential or character of the exam.<br />
With all this said, however, I think it’s<br />
fair to criticize the CISSP on two scores.<br />
First, the exam does have some problems.<br />
Whether or not the “evasive” questions are<br />
statistically and psychometrically valid,<br />
they are evasive. Yes, in the final analysis<br />
that’s my opinion, but it’s not as though<br />
I’m alone in feeling this way.<br />
The second problem is related to the<br />
first. Thanks in part to the exam, the first<br />
impression one gets of the CISSP is often<br />
negative. Whether you pass or not, nobody<br />
walks out of the test center feeling enthusiastic<br />
about the experience. It seems that<br />
the ramifications of this bad image are<br />
almost totally ignored by (ISC) 2 .<br />
Can either of these problems be fixed<br />
without making the test too accessible to<br />
“test-savvy” candidates who have no business<br />
holding the CISSP credential? Good<br />
question. ◗<br />
ANDREW BRINEY, CISSP, TICSA<br />
(abriney@infosecuritymag.com), is<br />
Information Security’s editor-in-chief.<br />
88 Information Security June 2003