NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
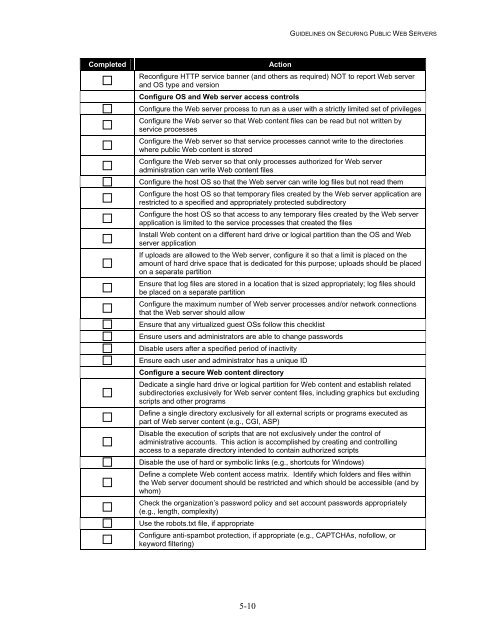
GUIDELINES ON SECURING PUBLIC WEB SERVERS<br />
Completed<br />
Acti<strong>on</strong><br />
Rec<strong>on</strong>figure HTTP service banner (and others as required) NOT to report <strong>Web</strong> server<br />
and OS type and versi<strong>on</strong><br />
C<strong>on</strong>figure OS and <strong>Web</strong> server access c<strong>on</strong>trols<br />
C<strong>on</strong>figure the <strong>Web</strong> server process to run as a user with a strictly limited set of privileges<br />
C<strong>on</strong>figure the <strong>Web</strong> server so that <strong>Web</strong> c<strong>on</strong>tent files can be read but not written by<br />
service processes<br />
C<strong>on</strong>figure the <strong>Web</strong> server so that service processes cannot write to the directories<br />
where public <strong>Web</strong> c<strong>on</strong>tent is stored<br />
C<strong>on</strong>figure the <strong>Web</strong> server so that <strong>on</strong>ly processes authorized for <strong>Web</strong> server<br />
administrati<strong>on</strong> can write <strong>Web</strong> c<strong>on</strong>tent files<br />
C<strong>on</strong>figure the host OS so that the <strong>Web</strong> server can write log files but not read them<br />
C<strong>on</strong>figure the host OS so that temporary files created by the <strong>Web</strong> server applicati<strong>on</strong> are<br />
restricted to a specified and appropriately protected subdirectory<br />
C<strong>on</strong>figure the host OS so that access to any temporary files created by the <strong>Web</strong> server<br />
applicati<strong>on</strong> is limited to the service processes that created the files<br />
Install <strong>Web</strong> c<strong>on</strong>tent <strong>on</strong> a different hard drive or logical partiti<strong>on</strong> than the OS and <strong>Web</strong><br />
server applicati<strong>on</strong><br />
If uploads are allowed to the <strong>Web</strong> server, c<strong>on</strong>figure it so that a limit is placed <strong>on</strong> the<br />
amount of hard drive space that is dedicated for this purpose; uploads should be placed<br />
<strong>on</strong> a separate partiti<strong>on</strong><br />
Ensure that log files are stored in a locati<strong>on</strong> that is sized appropriately; log files should<br />
be placed <strong>on</strong> a separate partiti<strong>on</strong><br />
C<strong>on</strong>figure the maximum number of <strong>Web</strong> server processes and/or network c<strong>on</strong>necti<strong>on</strong>s<br />
that the <strong>Web</strong> server should allow<br />
Ensure that any virtualized guest OSs follow this checklist<br />
Ensure users and administrators are able to change passwords<br />
Disable users after a specified period of inactivity<br />
Ensure each user and administrator has a unique ID<br />
C<strong>on</strong>figure a secure <strong>Web</strong> c<strong>on</strong>tent directory<br />
Dedicate a single hard drive or logical partiti<strong>on</strong> for <strong>Web</strong> c<strong>on</strong>tent and establish related<br />
subdirectories exclusively for <strong>Web</strong> server c<strong>on</strong>tent files, including graphics but excluding<br />
scripts and other programs<br />
Define a single directory exclusively for all external scripts or programs executed as<br />
part of <strong>Web</strong> server c<strong>on</strong>tent (e.g., CGI, ASP)<br />
Disable the executi<strong>on</strong> of scripts that are not exclusively under the c<strong>on</strong>trol of<br />
administrative accounts. This acti<strong>on</strong> is accomplished by creating and c<strong>on</strong>trolling<br />
access to a separate directory intended to c<strong>on</strong>tain authorized scripts<br />
Disable the use of hard or symbolic links (e.g., shortcuts for Windows)<br />
Define a complete <strong>Web</strong> c<strong>on</strong>tent access matrix. Identify which folders and files within<br />
the <strong>Web</strong> server document should be restricted and which should be accessible (and by<br />
whom)<br />
Check the organizati<strong>on</strong>’s password policy and set account passwords appropriately<br />
(e.g., length, complexity)<br />
Use the robots.txt file, if appropriate<br />
C<strong>on</strong>figure anti-spambot protecti<strong>on</strong>, if appropriate (e.g., CAPTCHAs, nofollow, or<br />
keyword filtering)<br />
5-10