NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
NIST 800-44 Version 2 Guidelines on Securing Public Web Servers
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
GUIDELINES ON SECURING PUBLIC WEB SERVERS<br />
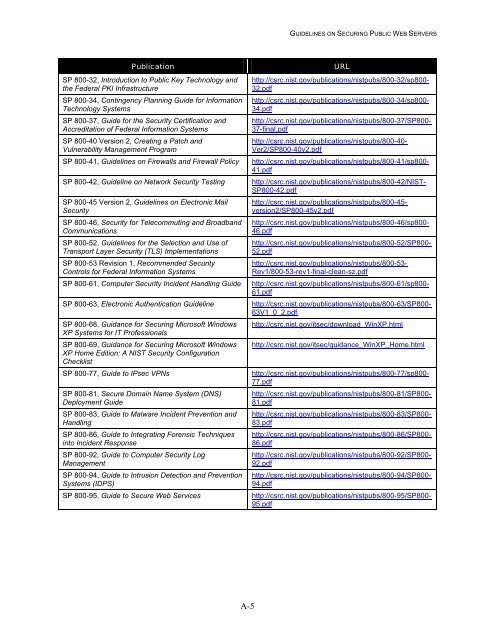
<strong>Public</strong>ati<strong>on</strong><br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-32, Introducti<strong>on</strong> to <strong>Public</strong> Key Technology and<br />
the Federal PKI Infrastructure<br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-34, C<strong>on</strong>tingency Planning Guide for Informati<strong>on</strong><br />
Technology Systems<br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-37, Guide for the Security Certificati<strong>on</strong> and<br />
Accreditati<strong>on</strong> of Federal Informati<strong>on</strong> Systems<br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-40 <str<strong>on</strong>g>Versi<strong>on</strong></str<strong>on</strong>g> 2, Creating a Patch and<br />
Vulnerability Management Program<br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-41, <str<strong>on</strong>g>Guidelines</str<strong>on</strong>g> <strong>on</strong> Firewalls and Firewall Policy<br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-42, Guideline <strong>on</strong> Network Security Testing<br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-45 <str<strong>on</strong>g>Versi<strong>on</strong></str<strong>on</strong>g> 2, <str<strong>on</strong>g>Guidelines</str<strong>on</strong>g> <strong>on</strong> Electr<strong>on</strong>ic Mail<br />
Security<br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-46, Security for Telecommuting and Broadband<br />
Communicati<strong>on</strong>s<br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-52, <str<strong>on</strong>g>Guidelines</str<strong>on</strong>g> for the Selecti<strong>on</strong> and Use of<br />
Transport Layer Security (TLS) Implementati<strong>on</strong>s<br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-53 Revisi<strong>on</strong> 1, Recommended Security<br />
C<strong>on</strong>trols for Federal Informati<strong>on</strong> Systems<br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-61, Computer Security Incident Handling Guide<br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-63, Electr<strong>on</strong>ic Authenticati<strong>on</strong> Guideline<br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-68, Guidance for <strong>Securing</strong> Microsoft Windows<br />
XP Systems for IT Professi<strong>on</strong>als<br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-69, Guidance for <strong>Securing</strong> Microsoft Windows<br />
XP Home Editi<strong>on</strong>: A <str<strong>on</strong>g>NIST</str<strong>on</strong>g> Security C<strong>on</strong>figurati<strong>on</strong><br />
Checklist<br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-77, Guide to IPsec VPNs<br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-81, Secure Domain Name System (DNS)<br />
Deployment Guide<br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-83, Guide to Malware Incident Preventi<strong>on</strong> and<br />
Handling<br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-86, Guide to Integrating Forensic Techniques<br />
into Incident Resp<strong>on</strong>se<br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-92, Guide to Computer Security Log<br />
Management<br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-94, Guide to Intrusi<strong>on</strong> Detecti<strong>on</strong> and Preventi<strong>on</strong><br />
Systems (IDPS)<br />
SP <str<strong>on</strong>g>800</str<strong>on</strong>g>-95, Guide to Secure <strong>Web</strong> Services<br />
URL<br />
http://csrc.nist.gov/publicati<strong>on</strong>s/nistpubs/<str<strong>on</strong>g>800</str<strong>on</strong>g>-32/sp<str<strong>on</strong>g>800</str<strong>on</strong>g>-<br />
32.pdf<br />
http://csrc.nist.gov/publicati<strong>on</strong>s/nistpubs/<str<strong>on</strong>g>800</str<strong>on</strong>g>-34/sp<str<strong>on</strong>g>800</str<strong>on</strong>g>-<br />
34.pdf<br />
http://csrc.nist.gov/publicati<strong>on</strong>s/nistpubs/<str<strong>on</strong>g>800</str<strong>on</strong>g>-37/SP<str<strong>on</strong>g>800</str<strong>on</strong>g>-<br />
37-final.pdf<br />
http://csrc.nist.gov/publicati<strong>on</strong>s/nistpubs/<str<strong>on</strong>g>800</str<strong>on</strong>g>-40-<br />
Ver2/SP<str<strong>on</strong>g>800</str<strong>on</strong>g>-40v2.pdf<br />
http://csrc.nist.gov/publicati<strong>on</strong>s/nistpubs/<str<strong>on</strong>g>800</str<strong>on</strong>g>-41/sp<str<strong>on</strong>g>800</str<strong>on</strong>g>-<br />
41.pdf<br />
http://csrc.nist.gov/publicati<strong>on</strong>s/nistpubs/<str<strong>on</strong>g>800</str<strong>on</strong>g>-42/<str<strong>on</strong>g>NIST</str<strong>on</strong>g>-<br />
SP<str<strong>on</strong>g>800</str<strong>on</strong>g>-42.pdf<br />
http://csrc.nist.gov/publicati<strong>on</strong>s/nistpubs/<str<strong>on</strong>g>800</str<strong>on</strong>g>-45-<br />
versi<strong>on</strong>2/SP<str<strong>on</strong>g>800</str<strong>on</strong>g>-45v2.pdf<br />
http://csrc.nist.gov/publicati<strong>on</strong>s/nistpubs/<str<strong>on</strong>g>800</str<strong>on</strong>g>-46/sp<str<strong>on</strong>g>800</str<strong>on</strong>g>-<br />
46.pdf<br />
http://csrc.nist.gov/publicati<strong>on</strong>s/nistpubs/<str<strong>on</strong>g>800</str<strong>on</strong>g>-52/SP<str<strong>on</strong>g>800</str<strong>on</strong>g>-<br />
52.pdf<br />
http://csrc.nist.gov/publicati<strong>on</strong>s/nistpubs/<str<strong>on</strong>g>800</str<strong>on</strong>g>-53-<br />
Rev1/<str<strong>on</strong>g>800</str<strong>on</strong>g>-53-rev1-final-clean-sz.pdf<br />
http://csrc.nist.gov/publicati<strong>on</strong>s/nistpubs/<str<strong>on</strong>g>800</str<strong>on</strong>g>-61/sp<str<strong>on</strong>g>800</str<strong>on</strong>g>-<br />
61.pdf<br />
http://csrc.nist.gov/publicati<strong>on</strong>s/nistpubs/<str<strong>on</strong>g>800</str<strong>on</strong>g>-63/SP<str<strong>on</strong>g>800</str<strong>on</strong>g>-<br />
63V1_0_2.pdf<br />
http://csrc.nist.gov/itsec/download_WinXP.html<br />
http://csrc.nist.gov/itsec/guidance_WinXP_Home.html<br />
http://csrc.nist.gov/publicati<strong>on</strong>s/nistpubs/<str<strong>on</strong>g>800</str<strong>on</strong>g>-77/sp<str<strong>on</strong>g>800</str<strong>on</strong>g>-<br />
77.pdf<br />
http://csrc.nist.gov/publicati<strong>on</strong>s/nistpubs/<str<strong>on</strong>g>800</str<strong>on</strong>g>-81/SP<str<strong>on</strong>g>800</str<strong>on</strong>g>-<br />
81.pdf<br />
http://csrc.nist.gov/publicati<strong>on</strong>s/nistpubs/<str<strong>on</strong>g>800</str<strong>on</strong>g>-83/SP<str<strong>on</strong>g>800</str<strong>on</strong>g>-<br />
83.pdf<br />
http://csrc.nist.gov/publicati<strong>on</strong>s/nistpubs/<str<strong>on</strong>g>800</str<strong>on</strong>g>-86/SP<str<strong>on</strong>g>800</str<strong>on</strong>g>-<br />
86.pdf<br />
http://csrc.nist.gov/publicati<strong>on</strong>s/nistpubs/<str<strong>on</strong>g>800</str<strong>on</strong>g>-92/SP<str<strong>on</strong>g>800</str<strong>on</strong>g>-<br />
92.pdf<br />
http://csrc.nist.gov/publicati<strong>on</strong>s/nistpubs/<str<strong>on</strong>g>800</str<strong>on</strong>g>-94/SP<str<strong>on</strong>g>800</str<strong>on</strong>g>-<br />
94.pdf<br />
http://csrc.nist.gov/publicati<strong>on</strong>s/nistpubs/<str<strong>on</strong>g>800</str<strong>on</strong>g>-95/SP<str<strong>on</strong>g>800</str<strong>on</strong>g>-<br />
95.pdf<br />
A-5