Lectures notes for 2010 - KTH
Lectures notes for 2010 - KTH Lectures notes for 2010 - KTH
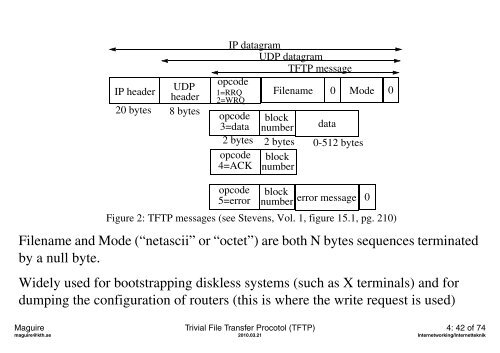
IP header UDP header 20 bytes 8 bytes IP datagram UDP datagram TFTP message opcode 1=RRQ 2=WRQ Filename opcode block 3=data number data 2 bytes 2 bytes 0-512 bytes opcode block 4=ACK number 0 Mode 0 opcode block 5=error number error message 0 Figure 2: TFTP messages (see Stevens, Vol. 1, figure 15.1, pg. 210) Filename and Mode (“netascii” or “octet”) are both N bytes sequences terminated by a null byte. Widely used for bootstrapping diskless systems (such as X terminals) and for dumping the configuration of routers (this is where the write request is used) Maguire Trivial File Transfer Procotol (TFTP) 4: 42 of 74 maguire@kth.se 2010.03.21 Internetworking/Internetteknik
Mapping names to IP addresses Host name: string “ccslab1.kth.se” Name Resolution: DNS IP address 32 bit 130.237.15.254 ARP RARP HW address: 48 bit Ethernet MAC address “08:00:2B:00:EE:0B” Figure 3: mapping between host names and IP address(es) Addr. Resolution Maguire Mapping names to IP addresses 4: 43 of 74 maguire@kth.se 2010.03.21 Internetworking/Internetteknik
- Page 223 and 224: ICMP Port Unreachable Error Example
- Page 225 and 226: PING: Packet InterNet Groper or son
- Page 227 and 228: On a HP-UX 11.0 machine: ping -ov w
- Page 229 and 230: Useful Tool: Traceroute Programs De
- Page 231 and 232: This lecture we have discussed: •
- Page 233 and 234: IK1550 Internetworking/Internettekn
- Page 235 and 236: Transport layer protocols The trans
- Page 237 and 238: User Datagram Protocol (UDP) • Da
- Page 239 and 240: UDP Checksum and Pseudo-Header •
- Page 241 and 242: Port numbers in three groups Range
- Page 243 and 244: Fragmentation Required If datagram
- Page 245 and 246: • on a BSDI system: • each of t
- Page 247 and 248: With an even larger UDP packet I re
- Page 249 and 250: Datagram truncation What if the app
- Page 251 and 252: Learning about Socket programming F
- Page 253 and 254: UDP server design Stevens, Vol, 1,
- Page 255 and 256: Changed the client Changing the fol
- Page 257 and 258: if (!(proto = getprotobyname("raw")
- Page 259 and 260: ICMP Source Quench Error Since UDP
- Page 261 and 262: No error control Since UDP has no e
- Page 263 and 264: BOOTP continued When a request is s
- Page 265 and 266: DHCP: Dynamic Host Configuration Pr
- Page 267 and 268: • Message - used by a server to p
- Page 269 and 270: DHCP’s importance • allows reus
- Page 271 and 272: Example of dhcpd.conf ### Managed b
- Page 273: Trivial File Transfer Procotol (TFT
- Page 277 and 278: Zones A zone is a subtree of the DN
- Page 279 and 280: (see Stevens, Vol. 1, figure 14.2,
- Page 281 and 282: Domain registrars Internet Corporat
- Page 283 and 284: Resource Records (RR) See Stevens,
- Page 285 and 286: Network names Conventions: • it.k
- Page 287 and 288: Example: $ORIGIN it.kth.se. @ 1D IN
- Page 289 and 290: How to give your host a name? Host
- Page 291 and 292: Configuring DNS • Configuring the
- Page 293 and 294: Load leveling [1] For example, f.ro
- Page 295 and 296: Where is f.root-servers.net ? trace
- Page 297 and 298: Dynamic Domain Name System (DDNS) R
- Page 299 and 300: Attacks upon DNS • Denial of serv
- Page 301 and 302: DNS performance - top 100 From www.
- Page 303 and 304: Web performance - continued Using P
- Page 305 and 306: This lecture we have discussed: •
- Page 307 and 308: IK1550 Internetworking/Internettekn
- Page 309 and 310: Transport layer protocols • User
- Page 311 and 312: Applications which use TCP Lots of
- Page 313 and 314: TCP header continued Reliability is
- Page 315 and 316: time client SYN, seq=x SYN, seq=y,
- Page 317 and 318: client active close ACKs from clien
- Page 319 and 320: Maximum Segment Size • The Maximu
- Page 321 and 322: Window size Increasing window size
- Page 323 and 324: Silly Window Syndrome If receiver a
IP header<br />
UDP<br />
header<br />
20 bytes 8 bytes<br />
IP datagram<br />
UDP datagram<br />
TFTP message<br />
opcode<br />
1=RRQ<br />
2=WRQ<br />
Filename<br />
opcode block<br />
3=data number data<br />
2 bytes 2 bytes 0-512 bytes<br />
opcode block<br />
4=ACK number<br />
0<br />
Mode<br />
0<br />
opcode block<br />
5=error number error message 0<br />
Figure 2: TFTP messages (see Stevens, Vol. 1, figure 15.1, pg. 210)<br />
Filename and Mode (“netascii” or “octet”) are both N bytes sequences terminated<br />
by a null byte.<br />
Widely used <strong>for</strong> bootstrapping diskless systems (such as X terminals) and <strong>for</strong><br />
dumping the configuration of routers (this is where the write request is used)<br />
Maguire Trivial File Transfer Procotol (TFTP) 4: 42 of 74<br />
maguire@kth.se <strong>2010</strong>.03.21 Internetworking/Internetteknik