Firewall Enterprise 8.2.0 Release Notes - McAfee
Firewall Enterprise 8.2.0 Release Notes - McAfee Firewall Enterprise 8.2.0 Release Notes - McAfee
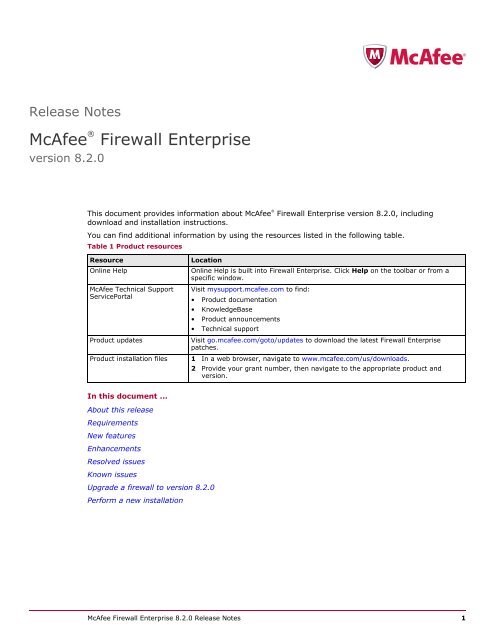
Release Notes McAfee ® Firewall Enterprise version 8.2.0 This document provides information about McAfee ® Firewall Enterprise version 8.2.0, including download and installation instructions. You can find additional information by using the resources listed in the following table. Table 1 Product resources Resource Online Help Location Online Help is built into Firewall Enterprise. Click Help on the toolbar or from a specific window. McAfee Technical Support Visit mysupport.mcafee.com to find: ServicePortal • Product documentation • KnowledgeBase • Product announcements • Technical support Product updates Visit go.mcafee.com/goto/updates to download the latest Firewall Enterprise patches. Product installation files 1 In a web browser, navigate to www.mcafee.com/us/downloads. 2 Provide your grant number, then navigate to the appropriate product and version. In this document ... About this release Requirements New features Enhancements Resolved issues Known issues Upgrade a firewall to version 8.2.0 Perform a new installation McAfee Firewall Enterprise 8.2.0 Release Notes 1
- Page 2 and 3: About this release About this relea
- Page 4 and 5: Requirements Firewall Enterprise re
- Page 6 and 7: Enhancements Enhancements The follo
- Page 8 and 9: Resolved issues High Availability
- Page 10 and 11: Known issues System • Improves de
- Page 12 and 13: Upgrade a firewall to version 8.2.0
- Page 14 and 15: Upgrade a firewall to version 8.2.0
- Page 16 and 17: Perform a new installation Download
- Page 18 and 19: Perform a new installation Firewall
- Page 20: Perform a new installation For supp
<strong>Release</strong> <strong>Notes</strong><br />
<strong>McAfee</strong> ®<br />
<strong>Firewall</strong> <strong>Enterprise</strong><br />
version <strong>8.2.0</strong><br />
This document provides information about <strong>McAfee</strong> ®<br />
<strong>Firewall</strong> <strong>Enterprise</strong> version <strong>8.2.0</strong>, including<br />
download and installation instructions.<br />
You can find additional information by using the resources listed in the following table.<br />
Table 1 Product resources<br />
Resource<br />
Online Help<br />
Location<br />
Online Help is built into <strong>Firewall</strong> <strong>Enterprise</strong>. Click Help on the toolbar or from a<br />
specific window.<br />
<strong>McAfee</strong> Technical Support Visit mysupport.mcafee.com to find:<br />
ServicePortal<br />
• Product documentation<br />
• KnowledgeBase<br />
• Product announcements<br />
• Technical support<br />
Product updates<br />
Visit go.mcafee.com/goto/updates to download the latest <strong>Firewall</strong> <strong>Enterprise</strong><br />
patches.<br />
Product installation files 1 In a web browser, navigate to www.mcafee.com/us/downloads.<br />
2 Provide your grant number, then navigate to the appropriate product and<br />
version.<br />
In this document ...<br />
About this release<br />
Requirements<br />
New features<br />
Enhancements<br />
Resolved issues<br />
Known issues<br />
Upgrade a firewall to version <strong>8.2.0</strong><br />
Perform a new installation<br />
<strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> <strong>8.2.0</strong> <strong>Release</strong> <strong>Notes</strong> 1
About this release<br />
About this release<br />
<strong>Firewall</strong> <strong>Enterprise</strong> version <strong>8.2.0</strong> introduces new features for <strong>Firewall</strong> <strong>Enterprise</strong> S model appliances.<br />
This release also resolves issues present in the previous release.<br />
<strong>Firewall</strong> <strong>Enterprise</strong> version <strong>8.2.0</strong> will be end of life (EOL) one year after certification is complete for the<br />
next Common Criteria and FIPS certified releases.<br />
Supported firewall types<br />
<strong>Firewall</strong> <strong>Enterprise</strong>, version <strong>8.2.0</strong> supports:<br />
• <strong>McAfee</strong> ® <strong>Firewall</strong> <strong>Enterprise</strong> appliances<br />
• <strong>McAfee</strong> ® <strong>Firewall</strong> <strong>Enterprise</strong>, Virtual Appliance<br />
• <strong>McAfee</strong> ® <strong>Firewall</strong> <strong>Enterprise</strong> on Riverbed Services Platform<br />
Note: This release does not support <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> on Crossbeam X-Series Platform. However,<br />
<strong>McAfee</strong> intends to support this platform in the future.<br />
Installation options<br />
The following installation options are available for version <strong>8.2.0</strong>:<br />
• Upgrade — Upgrade a firewall from version 8.1.2 to version <strong>8.2.0</strong>.<br />
For upgrade instructions, see Upgrade a firewall to version <strong>8.2.0</strong> in this document.<br />
• New installation — Re-image a firewall using version <strong>8.2.0</strong> installation media.<br />
Compatible <strong>McAfee</strong> products<br />
<strong>Firewall</strong> <strong>Enterprise</strong> version <strong>8.2.0</strong> is compatible with the following <strong>McAfee</strong> products:<br />
• <strong>McAfee</strong> ® <strong>Firewall</strong> <strong>Enterprise</strong> ePolicy Orchestrator ® Extension<br />
• <strong>McAfee</strong> ® <strong>Firewall</strong> <strong>Enterprise</strong> Control Center<br />
• <strong>McAfee</strong> ® <strong>Firewall</strong> Profiler<br />
• <strong>McAfee</strong> ® Logon Collector<br />
• <strong>McAfee</strong> ® <strong>Firewall</strong> Reporter<br />
For more information, see the following resources:<br />
• To find the latest information on <strong>McAfee</strong> firewall products and versions that <strong>Firewall</strong> <strong>Enterprise</strong><br />
supports, refer to KnowledgeBase article KB67462.<br />
• To learn about these products and how they interoperate with <strong>Firewall</strong> <strong>Enterprise</strong>, refer to the Using<br />
<strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> with Other <strong>McAfee</strong> Products application note.<br />
2 <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> <strong>8.2.0</strong> <strong>Release</strong> <strong>Notes</strong>
Requirements<br />
Requirements<br />
Before you install version <strong>8.2.0</strong>, make sure the Admin Console and <strong>Firewall</strong> <strong>Enterprise</strong> requirements are<br />
met.<br />
Admin Console requirements<br />
The computer that hosts the Admin Console must meet these requirements.<br />
Table 2 Admin Console minimum requirements<br />
Component<br />
Requirements<br />
Operating system One of the following Microsoft operating systems:<br />
• Windows Server 2008<br />
• Windows XP Professional<br />
• Windows Vista<br />
• Windows 7<br />
Web browser<br />
One of the following:<br />
• Microsoft Internet Explorer, version 7 or later<br />
• Mozilla Firefox, version 3.0 or later<br />
Hardware • 2 GHz x86-compatible processor<br />
• 2 GB of system memory<br />
• 300 MB of available disk space<br />
• CD-ROM drive<br />
• 1024 x 768 display<br />
• Network card (to connect to your firewall)<br />
• USB port<br />
<strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> <strong>8.2.0</strong> <strong>Release</strong> <strong>Notes</strong> 3
Requirements<br />
<strong>Firewall</strong> <strong>Enterprise</strong> requirements<br />
The firewall must meet these requirements.<br />
Table 3 Minimum requirements by <strong>Firewall</strong> <strong>Enterprise</strong> type<br />
<strong>Firewall</strong> type<br />
<strong>Firewall</strong> <strong>Enterprise</strong> appliance<br />
<strong>Firewall</strong> <strong>Enterprise</strong>, Virtual Appliance<br />
Platform requirements<br />
D model appliance or later with a valid support contract<br />
Virtualization server that meets the following requirements:<br />
• Hypervisor operating system — VMware ESX/ESXi version 4.0 or<br />
later<br />
Note: <strong>Firewall</strong> <strong>Enterprise</strong>, Virtual Appliance is installed in 64-bit mode<br />
by default. Your system must support Intel VT technology (or<br />
equivalent) for it to run properly in a virtual environment. Before<br />
starting the virtual appliance, verify that VT is enabled in your<br />
computer BIOS.<br />
• Hardware resources:<br />
• Two virtual processors<br />
• 512 MB of memory<br />
Note: If you plan to use features such as virus scanning or<br />
sendmail, increase the allocated memory to 1024 MB.<br />
<strong>Firewall</strong> <strong>Enterprise</strong> on Riverbed<br />
Services Platform<br />
• 28 GB of free disk space<br />
• Internet connectivity — The firewall requires a persistent Internet<br />
connection to maintain an active license and full functionality.<br />
Riverbed Steelhead appliance that meets the following requirements:<br />
• RiOS version 6.0 or later<br />
• RSP version 6.0 or later installed and licensed<br />
• Available RSP slot<br />
• 512 MB of free memory<br />
• 28 GB of free disk space<br />
Note: <strong>Firewall</strong> <strong>Enterprise</strong> on Riverbed Services Platform is installed in<br />
32-bit mode by default.<br />
4 <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> <strong>8.2.0</strong> <strong>Release</strong> <strong>Notes</strong>
New features<br />
New features<br />
The following new features are included in this release.<br />
IPv6 support<br />
This release introduces IPv6 support for the following configurations:<br />
• Failover High Availability (HA) — Supports IPv6 in peer-to-peer and primary/standby HA cluster<br />
configurations<br />
• Domain name system (DNS) — Supports split DNS with IPv6 configurations<br />
• Border Gateway Protocol (BGP) — Allows exchange of IPv4 and IPv6 routes<br />
Note: IPv6 is enabled by default in <strong>8.2.0</strong>.<br />
IPv6 support for failover HA<br />
Failover HA supports IPv6 addresses for all cluster interfaces except heartbeat and backup heartbeat<br />
interfaces. These cluster interfaces support IPv4 addresses, IPv6 addresses, or both.<br />
Note: The heartbeat and backup heartbeat must use IPv4 addresses. IPv6 addresses are not supported.<br />
The following restrictions apply:<br />
• For each shared IPv6 address, cluster firewalls must be assigned an individual IPv6 address in the<br />
same scope.<br />
• Load sharing HA does not support IPv6.<br />
IPv6 support for DNS<br />
Both split server DNS and single server DNS configurations are supported with IPv6 enabled. You can<br />
also have IPv4 and IPv6 DNS resolution over IPv4 or IPv6 addresses.<br />
IPv6 support for BGP<br />
BGP peers can exchange IPv4 and IPv6 routes. The following configurations are supported:<br />
• BGP IPv4 — BGP IPv4 route distribution over IPv4 or IPv6 network transport<br />
• BGP IPv6 — BGP IPv6 route distribution over IPv6 or IPv4 network transport<br />
<strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> <strong>8.2.0</strong> <strong>Release</strong> <strong>Notes</strong> 5
Enhancements<br />
Enhancements<br />
The following enhancements are included in this release.<br />
FIPS 140-2 compliance<br />
<strong>Firewall</strong> <strong>Enterprise</strong> can be configured to comply with Federal Information Processing Standard (FIPS)<br />
140-2. Use the FIPS window to enable or disable FIPS 140-2 processing on the firewall.<br />
Common Criteria<br />
A <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> network environment can be configured to comply with Common Criteria<br />
evaluation standards.<br />
Usability improvements<br />
This release includes the following usability enhancements.<br />
• Admin Console — From the Access Control Rules window, select the Application Defense groups and<br />
<strong>McAfee</strong> ®<br />
Global Threat Intelligence reputation options while defining access control rules.<br />
• Documentation — The product guide has been streamlined to clarify topics and optimize Admin<br />
Console option definitions.<br />
6 <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> <strong>8.2.0</strong> <strong>Release</strong> <strong>Notes</strong>
Resolved issues<br />
Resolved issues<br />
This release resolves the following issues.<br />
Admin Console<br />
• Improves the stability of the graphical user interface BGP editor<br />
• Improves the performance of dashboard when viewing data from firewall with a significant number of<br />
blackholed IP addresses<br />
• Improves parsing of DNS configuration files during DNS interface modification<br />
• Enhances Application defense usability<br />
• Allows choosing of user_name as a column in the graphical user interface Audit Viewer<br />
• Allows use of 0 as a netmask in VPN security associations<br />
• Resolves the failed to connect to SSL issue when the audit viewer is launched in a new application<br />
window<br />
• Resolves an issue with managing DNS configurations when non-resolvable NS or MX records are<br />
present<br />
• Supports policies that use deprecated applications on the Rule Interactions tab<br />
• Makes the Rule Interactions tab consistent with <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> Control Center<br />
• Fixes the port display for the Deny All rule on the Rule Interactions tab<br />
• Fixes an issue on the Rule Interactions tab with unsaved data on the Access Control Rules window<br />
• Fixes the save issue for the Auto-recover on Reconnect checkbox on the High Availability window<br />
• Fixes a dashboard timeout issue on the primary firewall<br />
• Addresses issues with handling of SmartFilter custom sites<br />
Command line interface<br />
• Allows implied entry type on cf interface add_addresses operations<br />
• Corrects display of policy out of cf policy showtables to display redirections and REDIR flag<br />
Crypto<br />
• Resolves incorrect UNIX permissions on fetched Certificate Revocation List (CRL) files<br />
• Fixes NAT-T support for password-based dynamic VPNs<br />
• Updates Trusted Internet CAs with the new list from Mozilla<br />
• Removes DigiNotar from the list of Trusted Internet CAs<br />
<strong>Firewall</strong> Policy Report<br />
• Includes AppPrism and IPS signature versions in the <strong>Firewall</strong> Policy Report<br />
• Displays ports configured for the rules in the policy<br />
<strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> <strong>8.2.0</strong> <strong>Release</strong> <strong>Notes</strong> 7
Resolved issues<br />
High Availability<br />
• Improves failover processing when an interface failure occurs<br />
• Resolves a startup issue that occurs during simultaneous booting of nodes in a peer-to-peer cluster<br />
• Resolves an issue with a down interface on a load sharing primary<br />
• Shares last application cache with secondary nodes<br />
Policy<br />
• Allows UDP proxy rules that pass IPv4 and IPv6 with redirection to pass both address families<br />
• Improves memory use during activation of large complex rule sets<br />
• Improves validation of IPv4 addresses in configuration<br />
• Improves validation of upstream proxy validation in the HTTP Application Defense<br />
• Improves error checking when including generic Application Defense in an Application Defense group<br />
• Improves usability with changes to policy validation and compilation<br />
• Improves usability with better defaults for SSL rules<br />
• Ensures that traffic is proxied if the policy requests it<br />
• Resolves an issue with netgroups containing too many host objects<br />
• Resolves a validation issue when using an application with multiple capabilities in a policy<br />
• Resolves a traceback issue when using time periods with IPv6 enabled<br />
• Fixes a timing issue in acld that causes Bad file descriptor traceback in audit<br />
• Fixes an issue with netmaps when handling IPv6 traffic<br />
• Fixes an error when using Geo-Location objects as endpoints in SSL rules<br />
• Fixes a validation issue when adding a zone with an index of 63<br />
• Cleans up the posting of listens so that proxies listen to interfaces that are specified only in the policy<br />
Proxies<br />
• Resolves the broken SmartFilter logo issue in block pages when Remote SmartFilter Administration<br />
Console is enabled<br />
• Resolves an issue with truncation of group names when passing user information from Passport to<br />
SmartFilter<br />
• Resolves an interface issue with DHCP Relay<br />
• Resolves an issue with authenticated redirections<br />
• Fixes handling of pings on a secondary node in a load sharing HA cluster to clean up attack audits<br />
• Fixes a problem with the SmartFilter URL when using a non-default port<br />
• Fixes Passport authentication handling when using Web login with active session mode<br />
• Addresses UDP session hang on secondary nodes in a load sharing HA cluster<br />
• Citrix — Improves error handling in the UDP Citrix proxy<br />
• FTP — Adds support for QUOTE command in the FTP proxy<br />
8 <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> <strong>8.2.0</strong> <strong>Release</strong> <strong>Notes</strong>
Resolved issues<br />
• HTTP<br />
• Resolves an issue with the HTTP proxy to perform IPS scanning in URLs<br />
• Corrects logging of HTTPS sites in SF.log when using remote SmartFilter console<br />
• Prevents accidental HTTP protocol enforcement for non-HTTP protocols<br />
• Provides stability fixes for the HTTP proxy<br />
• Resolves an issue of denied headers in HTTP and blocked headers in the SMTP proxy<br />
• Resolves session hang in the HTTP proxy when using SmartFilter<br />
• Re-enables in-band authentication for non-transparent HTTPS<br />
• Restores special case handling of in-band Passport authentication handling for non-transparent<br />
HTTP<br />
• Adds attack detection and mitigation for slow header attacks on HTTP protocol<br />
• Allows non-transparent HTTP to use minimal inspection<br />
• Allows timeout invalid DNS responses to do subsequent re-querying<br />
• H.323 — Addresses H.323 handling of unregistration request messages without call signal addresses<br />
• SMTP<br />
• Improves the SMTP proxy debugging audits<br />
• Resolves hang in the SMTP proxy during configuration changes under some circumstances<br />
• Allows use of the BDAT verb in the SMTP proxy<br />
• SNMP — Improves the stability of the SNMP proxy<br />
• SSH — Relaxes validation of the X11 forwarding originator address field in the SSH proxy<br />
• Sun RPC — Improves error handling when passing Sun RPC through a proxy<br />
<strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> <strong>8.2.0</strong> <strong>Release</strong> <strong>Notes</strong> 9
Known issues<br />
System<br />
• Improves debugging support on large memory systems<br />
• Improves handling of DHCP addresses when modifying interfaces<br />
• Improves error handling when processing audit files with corrupted data<br />
• Allows passing of multicast traffic through the firewall when using transparent bridged interface and<br />
Link aggregation (LAGG)<br />
• Supports the configuration of more than two interfaces on a bridge<br />
• Adds AAAA records to BIND's root cache for the D and I root servers<br />
• Rejoins multicast groups for IP filter rules when interfaces change<br />
• Resolves a problem that dropped routing tables when zone modes are changed on a transparent<br />
firewall<br />
• Resolves a problem that restarts a device when installing multiple packages before all packages are<br />
completely installed<br />
• Resolves an issue with hostd performance<br />
• Resolves a Type Enforcement error when exiting from emergency maintenance mode<br />
• Fixes a Type Enforcement error when reconfigure mail is run when existing mail messages are queued<br />
in /var/spool/mqueue.c<br />
• Fixes the kernel stability issues<br />
• Corrects data returned by UCD-SNMP-MIB::ssCpuIdle.0 and<br />
HOST-RESOURCES-MIB::hrProcessorLoad SNMP OIDs<br />
• Cleans up the extraneous debug audits from hostd<br />
Security updates<br />
• Resolves CVE-2011-1910 and CVE-2011-2464 for BIND<br />
• Resolves CVE-2010-1674 and CVE-2010-1675 for Quagga BGP<br />
Known issues<br />
For information about known issues for <strong>Firewall</strong> <strong>Enterprise</strong> version <strong>8.2.0</strong>:<br />
1 Visit mysupport.mcafee.com.<br />
2 Log on with your user ID and password. The ServicePortal homepage appears with a welcome<br />
message at the top.<br />
• If you do not have an account but have received a grant number:<br />
• In the User Login section, click New User.<br />
• Complete the information and follow the prompts to set up your account.<br />
• If you do not have an account or grant number, contact Customer Service.<br />
3 In the Self Service section, click Search the KnowledgeBase. The KnowledgeBase welcome page<br />
appears.<br />
4 In the Ask a Question section, type KB72785, then click Ask. The KnowledgeBase article appears with<br />
any known issues.<br />
10 <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> <strong>8.2.0</strong> <strong>Release</strong> <strong>Notes</strong>
Upgrade a firewall to version <strong>8.2.0</strong><br />
Upgrade a firewall to version <strong>8.2.0</strong><br />
Select the upgrade method that is appropriate for your firewall type.<br />
• Upgrade a standalone firewall or HA cluster<br />
• Upgrade a Control Center-managed firewall or HA cluster<br />
Note: Your firewall must be at version 8.1.2 to upgrade to version <strong>8.2.0</strong> as described in this section. Refer to<br />
the <strong>Firewall</strong> <strong>Enterprise</strong> <strong>Release</strong> <strong>Notes</strong>, version 8.1.2 for details.<br />
Upgrade a standalone firewall or HA cluster<br />
Use the Admin Console to upgrade a standalone firewall or HA cluster to version <strong>8.2.0</strong>. Perform these<br />
tasks in order:<br />
1 Create a configuration backup<br />
2 Download the <strong>8.2.0</strong> package<br />
3 Install the <strong>8.2.0</strong> package<br />
4 Update the Admin Console<br />
5 Verify that version <strong>8.2.0</strong> is installed<br />
Note: To upgrade a High Availability cluster, upgrade the secondary/standby firewall first, then upgrade the<br />
primary firewall.<br />
Create a configuration backup<br />
<strong>McAfee</strong> recommends that you create a configuration backup before upgrading. Backing up the<br />
configuration files lets you quickly restore a firewall.<br />
For instructions on creating a configuration backup, refer to the <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> Product<br />
Guide.<br />
Download the <strong>8.2.0</strong> package<br />
Perform the appropriate procedure to download the <strong>8.2.0</strong> package.<br />
• If your firewall has Internet connectivity, follow the steps under Download the package using the<br />
Admin Console.<br />
• If your firewall does not have Internet connectivity, follow the steps under Manually load the package.<br />
Download the package using the Admin Console<br />
Downloading the patch moves it from the <strong>McAfee</strong> FTP site to the firewall but does not install it.<br />
To download the patch from the network:<br />
1 Select Maintenance | Software Management.<br />
2 Click the Manage Packages tab.<br />
3 Display the available packages.<br />
a<br />
b<br />
Click Check for Updates. When the operation is complete, a pop-up window appears.<br />
Click OK. Packages appear in the table with a status of Available. These packages are available for<br />
downloading from the <strong>McAfee</strong> FTP site.<br />
Tip: To configure this action to occur automatically, use the Download Packages tab.<br />
4 Select the <strong>8.2.0</strong> package, then click Download. Click Yes to confirm.<br />
A “successfully loaded” message appears, and the package status changes to Loaded.<br />
<strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> <strong>8.2.0</strong> <strong>Release</strong> <strong>Notes</strong> 11
Upgrade a firewall to version <strong>8.2.0</strong><br />
Manually load the package<br />
If your firewall is not connected to the Internet, use a web browser to download the package, then<br />
manually load the package on the firewall.<br />
1 Use a web browser to download the <strong>8.2.0</strong> package.<br />
a<br />
b<br />
c<br />
Go to go.mcafee.com/goto/updates.<br />
Scroll down to the <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> Upgrades and Patches entry for version <strong>8.2.0</strong>, then<br />
click Download.<br />
Enter a valid <strong>Firewall</strong> <strong>Enterprise</strong> serial number, then click Submit.<br />
d Click Download Patch for version <strong>8.2.0</strong>.<br />
2 Place the <strong>8.2.0</strong> file where the firewall can access it. Choose one of these options:<br />
• Local FTP site — Place the package on an FTP site that the firewall has access to.<br />
• HTTPS website — Place the package on an HTTPS website that the firewall has access to.<br />
• CD — Place the package in a /packages directory on a CD, then insert the CD into the firewall<br />
CD-ROM drive.<br />
• Directory on the firewall — Use SCP to copy the package to the /home directory of your firewall<br />
administrator account.<br />
Note: To transfer files to the firewall using SCP, SSH access must be enabled on the firewall.<br />
3 In the Admin Console, go to Maintenance | Software Management, then click the Download<br />
Packages tab. The Download Packages tab appears.<br />
Tip: For option descriptions, click Help.<br />
4 Click Perform Manual Load Now. The Manual Load window appears.<br />
5 Specify where the <strong>8.2.0</strong> package is stored.<br />
a<br />
From the Load packages from drop-down list, select the appropriate method to load the package.<br />
• FTP — Select if you placed the package on a local FTP site<br />
• HTTPS — Select if you placed the package on an HTTPS website<br />
• CDROM — Select if you created a CD that contains the package<br />
• File — Select if you copied the package to your home directory on the firewall<br />
b In the Packages field, type <strong>8.2.0</strong>.<br />
c<br />
d<br />
Complete the remaining fields as appropriate.<br />
Click OK. A confirmation message appears.<br />
6 Click Yes. The firewall loads the package from the specified location. When the operation is complete,<br />
a message appears.<br />
7 Click OK.<br />
8 Verify that <strong>8.2.0</strong> is loaded on your firewall.<br />
a<br />
b<br />
Click the Manage Packages tab.<br />
Verify that the Status of the <strong>8.2.0</strong> package is Loaded on .<br />
12 <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> <strong>8.2.0</strong> <strong>Release</strong> <strong>Notes</strong>
Upgrade a firewall to version <strong>8.2.0</strong><br />
Install the <strong>8.2.0</strong> package<br />
Perform this procedure to install the <strong>8.2.0</strong> package on your firewall. This package also includes a<br />
separate Admin Console update.<br />
Note: The firewall will restart during the patch installation.<br />
To install this patch on your firewall from the Admin Console:<br />
1 Select Maintenance | Software Management.<br />
2 Click the Manage Packages tab.<br />
3 Select <strong>8.2.0</strong> from the list of packages, then click Install.<br />
4 Select Install now, then click OK.<br />
A warning appears stating that the firewall will restart after the patch is installed.<br />
5 Click Yes.<br />
The package is installed, then an Error message appears stating that the connection to the server<br />
has been lost.<br />
6 Click OK.<br />
The Admin Console is disconnected and the firewall restarts.<br />
Update the Admin Console<br />
After the firewalls, update the Admin Console by connecting to the firewall.<br />
1 Reconnect the Admin Console to the firewall.<br />
A message appears prompting you to install an Admin Console update.<br />
2 Click Yes.<br />
The Admin Console update downloads, then a message appears asking if you want to install the<br />
package now.<br />
3 Click Yes.<br />
The Admin Console closes and the InstallShield Wizard window appears.<br />
4 Click Next.<br />
A progress bar appears while the Admin Console update installs. When the installation completes,<br />
the Update Complete window appears.<br />
5 Click Finish. The Admin Console opens.<br />
Verify that version <strong>8.2.0</strong> is installed<br />
After the Admin Console update completes, verify that version <strong>8.2.0</strong> is installed on your firewall.<br />
1 Reconnect the Admin Console to the firewall.<br />
2 Select Maintenance | Software Management.<br />
3 On the Manage Packages tab, verify that the status for <strong>8.2.0</strong> is Installed.<br />
• If the patch status is still Loaded, call technical support.<br />
• You can also click View Package Details or View Log to see information about the installation.<br />
The patch is now installed.<br />
<strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> <strong>8.2.0</strong> <strong>Release</strong> <strong>Notes</strong> 13
Upgrade a firewall to version <strong>8.2.0</strong><br />
Patch rollback<br />
If the installed patch does not work to your satisfaction, you can use the Rollback feature to restore the<br />
firewall to a previous state.<br />
Caution: If you use the Rollback feature, any configuration changes made after the patch was installed are<br />
lost. Therefore, rolling back is a recommended recovery option for only a short time after a patch installation.<br />
Note: A rollback always requires a restart.<br />
To restore the firewall to a previous state:<br />
1 Select Maintenance | Software Management.<br />
2 Click the Rollback tab.<br />
3 Click Rollback Now, or select Schedule Rollback for to schedule a time for the rollback.<br />
Upgrade a Control Center-managed firewall or HA cluster<br />
Use Control Center to upgrade firewalls and clusters managed by Control Center.<br />
Caution: Do not use the <strong>Firewall</strong> <strong>Enterprise</strong> Admin Console to install a patch directly on a managed firewall.<br />
1 Upgrade your Control Center to version 5.2.0 or later. For instructions, see the <strong>McAfee</strong> <strong>Firewall</strong><br />
<strong>Enterprise</strong> Control Center <strong>Release</strong> <strong>Notes</strong>, version 5.2.0.<br />
2 Use Control Center to upgrade the managed firewall or cluster to version <strong>8.2.0</strong>. For instructions, see<br />
the <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> Control Center Product Guide.<br />
14 <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> <strong>8.2.0</strong> <strong>Release</strong> <strong>Notes</strong>
Perform a new installation<br />
Perform a new installation<br />
To install version <strong>8.2.0</strong>, use the appropriate procedure for your <strong>Firewall</strong> <strong>Enterprise</strong> platform:<br />
• <strong>Firewall</strong> <strong>Enterprise</strong> appliance<br />
• <strong>Firewall</strong> <strong>Enterprise</strong>, Virtual Appliance<br />
• <strong>Firewall</strong> <strong>Enterprise</strong> on Riverbed Services Platform<br />
Note: This release does not support <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> on Crossbeam X-Series Platform. However,<br />
<strong>McAfee</strong> intends to support this platform in the future.<br />
<strong>Firewall</strong> <strong>Enterprise</strong> appliance<br />
To re-image your firewall to version <strong>8.2.0</strong>, perform these tasks in order:<br />
1 Create a configuration backup<br />
2 Download <strong>Firewall</strong> <strong>Enterprise</strong> software<br />
3 Download the Product Guide<br />
4 Install the Management Tools<br />
5 Install <strong>Firewall</strong> <strong>Enterprise</strong><br />
6 Complete post-installation instructions<br />
Create a configuration backup<br />
When you perform a new installation on your firewall, all configuration and log information is removed.<br />
<strong>McAfee</strong> recommends that you create a configuration backup and save it off the firewall. Backing up the<br />
configuration files lets you quickly restore a firewall.<br />
For instructions on creating a configuration backup, refer to the <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> Product<br />
Guide.<br />
Download <strong>Firewall</strong> <strong>Enterprise</strong> software<br />
Perform this procedure to download the version <strong>8.2.0</strong> files.<br />
1 In a web browser, navigate to www.mcafee.com/us/downloads.<br />
2 Provide your grant number, then navigate to the appropriate product and version.<br />
3 Download the appropriate files.<br />
• Management Tools — Download the <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> Admin Console executable (.exe)<br />
file or CD image (.iso) file.<br />
Tip: Select the CD image file if you want to create a CD for use in installing the Management Tools.<br />
• Version <strong>8.2.0</strong> image — Download the installation CD image (.iso) file or USB image (.zip) file.<br />
Tip: Select the USB image file if your appliance does not have a CD-ROM drive.<br />
4 Create physical installation media using the downloaded installation files.<br />
• Write the .iso file(s) to a CD.<br />
Note: If you downloaded multiple .iso files, use a separate CD for each file.<br />
• If you downloaded the USB image file, write the image to a USB drive. Refer to KnowledgeBase<br />
article KB69115 for instructions.<br />
<strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> <strong>8.2.0</strong> <strong>Release</strong> <strong>Notes</strong> 15
Perform a new installation<br />
Download the Product Guide<br />
Download the <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> Product Guide so you have it available during the planning and<br />
setup process.<br />
1 Go to the <strong>McAfee</strong> Technical Support ServicePortal at mysupport.mcafee.com.<br />
2 Under Self Service, click Product Documentation.<br />
3 Select the appropriate product and version.<br />
4 Download the version <strong>8.2.0</strong> product guide.<br />
Install the Management Tools<br />
Perform this procedure to install the Management Tools on a Windows-based computer. The<br />
Management Tools include:<br />
• Quick Start Wizard — Creates the initial configuration for the firewall<br />
• Admin Console — Manages the firewall<br />
Note: <strong>Firewall</strong> <strong>Enterprise</strong> management tools are version-specific. You cannot connect to a version 8.x firewall<br />
using an older version of the Admin Console. However, you can have multiple management tools that co-exist<br />
on the same Windows-based computer.<br />
1 Launch the installation process:<br />
• If you downloaded the executable (.exe) file, locate the file on your computer, then double-click it.<br />
• If you downloaded the CD image (.iso) file and used it to create a CD, insert the CD into the<br />
appropriate drive.<br />
The welcome window appears.<br />
2 Follow the on-screen instructions to complete the setup program.<br />
Note: <strong>McAfee</strong> recommends using the default settings.<br />
Tip: Consider installing an SSH client on your computer. Use the SSH client to provide secure command line<br />
access to the firewall.<br />
Install <strong>Firewall</strong> <strong>Enterprise</strong><br />
Use this procedure to install version <strong>8.2.0</strong> on your appliance.<br />
1 Boot the firewall from the physical installation media that you created.<br />
• Installation USB drive:<br />
• If the firewall is on, insert the USB drive and restart.<br />
• If the firewall is off, insert the USB drive and turn on the firewall.<br />
• Installation CD:<br />
• If the firewall is on, insert the CD and restart.<br />
• If the firewall is off, turn it on and quickly insert the CD.<br />
The firewall starts and displays standard boot-up information.<br />
2 When the firewall starts, configure it to boot from the inserted installation media.<br />
• Models without a CD-ROM drive — Enter the boot menu, then select the installation USB drive.<br />
• Models with a CD-ROM drive — By default, the boot order is set to check the CD drive first. If<br />
the boot order has been altered and does not check the CD drive first, restart and enter the BIOS<br />
to adjust the boot order accordingly.<br />
The firewall boots from the installation media.<br />
16 <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> <strong>8.2.0</strong> <strong>Release</strong> <strong>Notes</strong>
Perform a new installation<br />
3 At the <strong>McAfee</strong> Inc. menu, accept the default, which is the Operational System. The welcome menu<br />
appears.<br />
4 At the Welcome to <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> menu, select a <strong>Firewall</strong> <strong>Enterprise</strong> boot option.<br />
• If you are using a locally attached terminal, press Enter to accept the default.<br />
• If you intend to use a serial console, type 4 and press Enter.<br />
5 When the installation complete message appears, remove the installation media from the firewall.<br />
6 Press R to restart the firewall, then press Enter. The firewall restarts and displays standard restart<br />
information.<br />
<strong>Firewall</strong> <strong>Enterprise</strong> version <strong>8.2.0</strong> is now installed on your appliance.<br />
Complete post-installation instructions<br />
Now that you have installed <strong>Firewall</strong> <strong>Enterprise</strong>, you are ready to configure and start up the firewall. For<br />
complete setup instructions, refer to the following chapters in the <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> Product<br />
Guide, version <strong>8.2.0</strong>:<br />
• Planning<br />
• Installation and configuration<br />
• Startup<br />
<strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> <strong>8.2.0</strong> <strong>Release</strong> <strong>Notes</strong> 17
Perform a new installation<br />
<strong>Firewall</strong> <strong>Enterprise</strong>, Virtual Appliance<br />
To install <strong>Firewall</strong> <strong>Enterprise</strong>, Virtual Appliance, version <strong>8.2.0</strong>, perform these tasks in order:<br />
1 Create a configuration backup<br />
2 Download <strong>Firewall</strong> <strong>Enterprise</strong>, Virtual Appliance software<br />
3 Download the Installation Guide<br />
4 Install the virtual firewall<br />
Create a configuration backup<br />
If you are replacing an existing <strong>Firewall</strong> <strong>Enterprise</strong>, Virtual Appliance, <strong>McAfee</strong> recommends that you<br />
create a configuration backup. Backing up the configuration files lets you quickly restore a firewall.<br />
For instructions on creating a configuration backup, refer to the <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> Product<br />
Guide.<br />
Download <strong>Firewall</strong> <strong>Enterprise</strong>, Virtual Appliance software<br />
Perform this procedure to download version <strong>8.2.0</strong> files.<br />
1 In a web browser, navigate to www.mcafee.com/us/downloads.<br />
2 Provide your grant number, then navigate to the appropriate product and version.<br />
3 Download the virtual image (.zip) file.<br />
Download the Installation Guide<br />
You will use the <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong>, Virtual Appliance Installation Guide during the planning and<br />
setup process.<br />
1 Go to the <strong>McAfee</strong> Technical Support ServicePortal at mysupport.mcafee.com.<br />
2 Under Self Service, click Product Documentation.<br />
3 Select the appropriate product and version.<br />
4 Download the version 8.x installation guide.<br />
Install the virtual firewall<br />
Refer to the <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong>, Virtual Appliance Installation Guide, version 8.x, to install the<br />
virtual firewall.<br />
The high-level installation steps include:<br />
1 Install the virtual firewall on a VMware ESXi server.<br />
a<br />
b<br />
c<br />
d<br />
On your ESXi server, create an isolated port group, and name it unconfigured.<br />
Import the firewall.<br />
Configure network mappings for the firewall.<br />
Perform initial firewall configuration.<br />
2 Install the Management Tools on a Windows-based computer.<br />
18 <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> <strong>8.2.0</strong> <strong>Release</strong> <strong>Notes</strong>
Perform a new installation<br />
<strong>Firewall</strong> <strong>Enterprise</strong> on Riverbed Services Platform<br />
To install <strong>Firewall</strong> <strong>Enterprise</strong> version <strong>8.2.0</strong> on Riverbed Services Platform, perform these tasks in order:<br />
1 Create a configuration backup<br />
2 Download the <strong>Firewall</strong> <strong>Enterprise</strong> for Riverbed package<br />
3 Download the Installation Guide<br />
4 Install <strong>Firewall</strong> <strong>Enterprise</strong> on your Riverbed Steelhead appliance<br />
Create a configuration backup<br />
If you are replacing an existing <strong>Firewall</strong> <strong>Enterprise</strong> on Riverbed Services Platform, <strong>McAfee</strong> recommends<br />
that you create a configuration backup. Backing up the configuration files lets you quickly restore a<br />
firewall.<br />
For instructions on creating a configuration backup, refer to the <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> Product<br />
Guide.<br />
Download the <strong>Firewall</strong> <strong>Enterprise</strong> for Riverbed package<br />
Perform this procedure to download the <strong>Firewall</strong> <strong>Enterprise</strong> RSP package and Admin Console.<br />
1 In a web browser, navigate to www.mcafee.com/us/downloads.<br />
2 Provide your grant number, then navigate to the appropriate product and version.<br />
3 Download the <strong>Firewall</strong> <strong>Enterprise</strong> package.<br />
Download the Installation Guide<br />
You will use the <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> on Riverbed Services Platform Installation Guide during the<br />
planning and setup process.<br />
1 Go to the <strong>McAfee</strong> Technical Support ServicePortal at mysupport.mcafee.com.<br />
2 Under Self Service, click Product Documentation.<br />
3 Select the appropriate product and version.<br />
4 Download the version 8.x installation guide.<br />
Install <strong>Firewall</strong> <strong>Enterprise</strong> on your Riverbed Steelhead appliance<br />
Refer to the <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> on Riverbed Services Platform Installation Guide, version 8.x, to<br />
install the firewall.<br />
The high-level installation steps include:<br />
1 Install the firewall on your Riverbed Steelhead appliance.<br />
a<br />
b<br />
c<br />
d<br />
Add the <strong>Firewall</strong> <strong>Enterprise</strong> package to RSP.<br />
Install the firewall in an available slot.<br />
Configure the RSP data flow to direct network traffic through the firewall.<br />
Perform initial firewall configuration.<br />
2 Install the Management Tools on a Windows-based computer.<br />
<strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> <strong>8.2.0</strong> <strong>Release</strong> <strong>Notes</strong> 19
Perform a new installation<br />
For support information, visit mysupport.mcafee.com.<br />
Copyright © 2011 <strong>McAfee</strong>, Inc. All Rights Reserved.<br />
No part of this publication may be reproduced, transmitted, transcribed, stored in a retrieval system, or translated into any language<br />
in any form or by any means without the written permission of <strong>McAfee</strong>, Inc., or its suppliers or affiliate companies.<br />
700-3493A00<br />
20 <strong>McAfee</strong> <strong>Firewall</strong> <strong>Enterprise</strong> <strong>8.2.0</strong> <strong>Release</strong> <strong>Notes</strong>