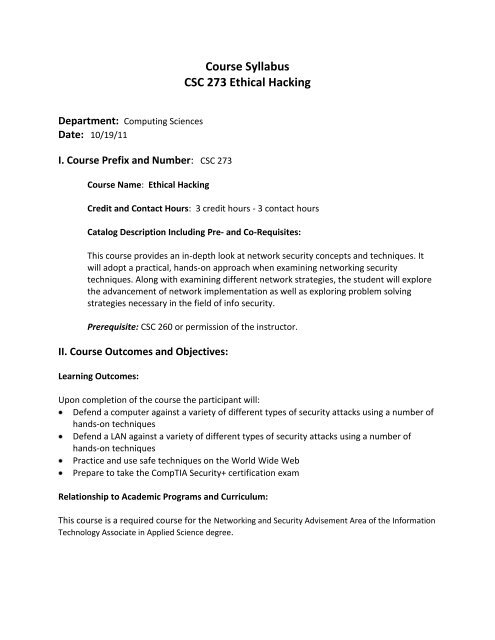
Course Syllabus CSC 273 Ethical Hacking
Course Syllabus CSC 273 Ethical Hacking
Course Syllabus CSC 273 Ethical Hacking
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
Department: Computing Sciences<br />
Date: 10/19/11<br />
I. <strong>Course</strong> Prefix and Number: <strong>CSC</strong> <strong>273</strong><br />
<strong>Course</strong> Name: <strong>Ethical</strong> <strong>Hacking</strong><br />
<strong>Course</strong> <strong>Syllabus</strong><br />
<strong>CSC</strong> <strong>273</strong> <strong>Ethical</strong> <strong>Hacking</strong><br />
Credit and Contact Hours: 3 credit hours - 3 contact hours<br />
Catalog Description Including Pre- and Co-Requisites:<br />
This course provides an in-depth look at network security concepts and techniques. It<br />
will adopt a practical, hands-on approach when examining networking security<br />
techniques. Along with examining different network strategies, the student will explore<br />
the advancement of network implementation as well as exploring problem solving<br />
strategies necessary in the field of info security.<br />
Prerequisite: <strong>CSC</strong> 260 or permission of the instructor.<br />
II. <strong>Course</strong> Outcomes and Objectives:<br />
Learning Outcomes:<br />
Upon completion of the course the participant will:<br />
Defend a computer against a variety of different types of security attacks using a number of<br />
hands-on techniques<br />
Defend a LAN against a variety of different types of security attacks using a number of<br />
hands-on techniques<br />
Practice and use safe techniques on the World Wide Web<br />
Prepare to take the CompTIA Security+ certification exam<br />
Relationship to Academic Programs and Curriculum:<br />
This course is a required course for the Networking and Security Advisement Area of the Information<br />
Technology Associate in Applied Science degree.
College Learning Outcomes Addressed by the <strong>Course</strong>:<br />
Writing ethics/values<br />
oral communications citizenship<br />
reading global concerns<br />
mathematics information resources<br />
problem-solving professional competency<br />
computer literacy<br />
III. Instructional Materials and Methods:<br />
Types of <strong>Course</strong> Materials:<br />
Textbooks, lab manuals, and other related materials developed by the instructor.<br />
Methods of Instruction (e.g. Lecture, Labs, Seminars …):<br />
Lecture<br />
Discussions<br />
Demonstrations<br />
Hands-on lab activities<br />
Group projects<br />
IV. Assessment Measures (Summarize how the College and student learning<br />
outcomes will be assessed):<br />
The demonstration of the satisfactory achievement of the above learning outcomes will be the<br />
responsibility of the student, facilitated by the instructor. The department maintains a very<br />
open attitude and believes each instructor should determine the grading system and evaluation<br />
methods that will be used in his/her sections of the course. It is highly recommended that these<br />
be communicated to the students the first week of the semester, preferable in writing.<br />
Among the evaluation methods that could be used are hands-on practical exams, and quizzes.<br />
Any grading system used must be consistent with the College Catalog and Middle States grading<br />
procedure. <strong>Course</strong> policies about attendance, late work, academic honesty, etc. are at the
discretion of the instructor. If such policies exist, they must be communicated to the students,<br />
preferably in writing.<br />
V. General Outline of Topics Covered:<br />
<strong>Ethical</strong> <strong>Hacking</strong> Overview<br />
TCP/IP Concepts Review<br />
Network and Computer Attacks<br />
Footprinting and Social Engineering<br />
Port Scanning<br />
Enumeration<br />
Programming for Security Professionals<br />
Microsoft Operating System Vulnerabilities<br />
Linux Operating System Vulnerabilities<br />
<strong>Hacking</strong> Web Servers<br />
<strong>Hacking</strong> Wireless Networks<br />
Cryptography<br />
Protecting Networks with Security Devices