Application of Behavior Change Theory to the Development
Application of Behavior Change Theory to the Development
Application of Behavior Change Theory to the Development
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
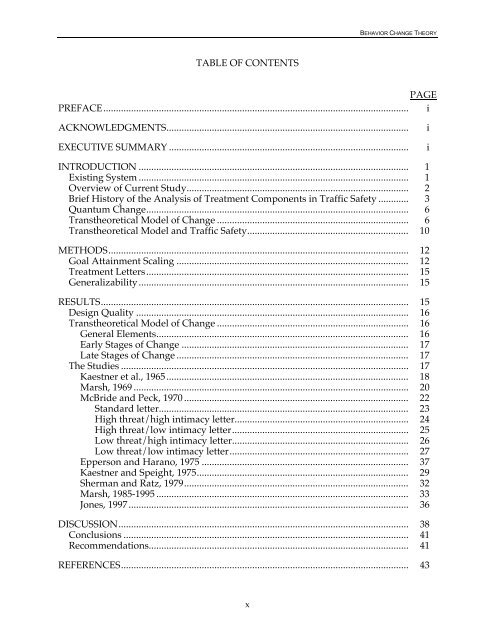
TABLE OF CONTENTS<br />
x<br />
BEHAVIOR CHANGE THEORY<br />
PAGE<br />
PREFACE......................................................................................................................... i<br />
ACKNOWLEDGMENTS................................................................................................ i<br />
EXECUTIVE SUMMARY ............................................................................................... i<br />
INTRODUCTION ........................................................................................................... 1<br />
Existing System ........................................................................................................... 1<br />
Overview <strong>of</strong> Current Study........................................................................................ 2<br />
Brief His<strong>to</strong>ry <strong>of</strong> <strong>the</strong> Analysis <strong>of</strong> Treatment Components in Traffic Safety ............ 3<br />
Quantum <strong>Change</strong>........................................................................................................ 6<br />
Trans<strong>the</strong>oretical Model <strong>of</strong> <strong>Change</strong> ............................................................................ 6<br />
Trans<strong>the</strong>oretical Model and Traffic Safety................................................................ 10<br />
METHODS....................................................................................................................... 12<br />
Goal Attainment Scaling ............................................................................................ 12<br />
Treatment Letters........................................................................................................ 15<br />
Generalizability........................................................................................................... 15<br />
RESULTS.......................................................................................................................... 15<br />
Design Quality ............................................................................................................ 16<br />
Trans<strong>the</strong>oretical Model <strong>of</strong> <strong>Change</strong> ............................................................................ 16<br />
General Elements.................................................................................................... 16<br />
Early Stages <strong>of</strong> <strong>Change</strong> .......................................................................................... 17<br />
Late Stages <strong>of</strong> <strong>Change</strong> ............................................................................................ 17<br />
The Studies .................................................................................................................. 17<br />
Kaestner et al., 1965 ................................................................................................ 18<br />
Marsh, 1969 ............................................................................................................. 20<br />
McBride and Peck, 1970 ......................................................................................... 22<br />
Standard letter................................................................................................... 23<br />
High threat/high intimacy letter..................................................................... 24<br />
High threat/low intimacy letter...................................................................... 25<br />
Low threat/high intimacy letter...................................................................... 26<br />
Low threat/low intimacy letter....................................................................... 27<br />
Epperson and Harano, 1975 .................................................................................. 37<br />
Kaestner and Speight, 1975.................................................................................... 29<br />
Sherman and Ratz, 1979......................................................................................... 32<br />
Marsh, 1985-1995 .................................................................................................... 33<br />
Jones, 1997............................................................................................................... 36<br />
DISCUSSION................................................................................................................... 38<br />
Conclusions ................................................................................................................. 41<br />
Recommendations....................................................................................................... 41<br />
REFERENCES.................................................................................................................. 43