ehr onc final certification - Department of Health Care Services
ehr onc final certification - Department of Health Care Services
ehr onc final certification - Department of Health Care Services
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
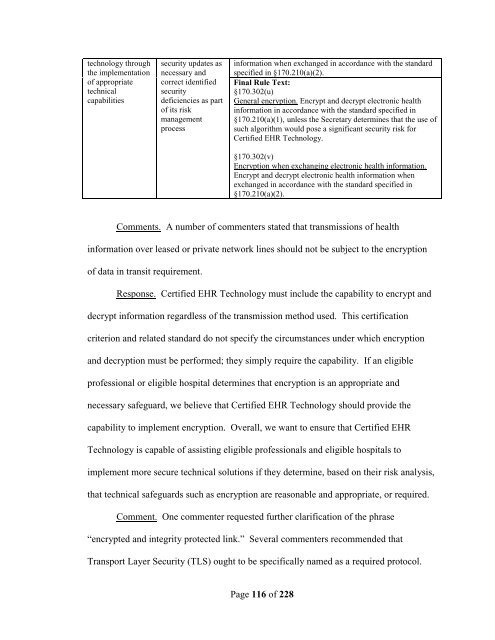
technology through<br />
the implementation<br />
<strong>of</strong> appropriate<br />
technical<br />
capabilities<br />
security updates as<br />
necessary and<br />
correct identified<br />
security<br />
deficiencies as part<br />
<strong>of</strong> its risk<br />
management<br />
process<br />
information when exchanged in accordance with the standard<br />
specified in §170.210(a)(2).<br />
Final Rule Text:<br />
§170.302(u)<br />
General encryption. Encrypt and decrypt electronic health<br />
information in accordance with the standard specified in<br />
§170.210(a)(1), unless the Secretary determines that the use <strong>of</strong><br />
such algorithm would pose a significant security risk for<br />
Certified EHR Technology.<br />
§170.302(v)<br />
Encryption when exchanging electronic health information.<br />
Encrypt and decrypt electronic health information when<br />
exchanged in accordance with the standard specified in<br />
§170.210(a)(2).<br />
Comments. A number <strong>of</strong> commenters stated that transmissions <strong>of</strong> health<br />
information over leased or private network lines should not be subject to the encryption<br />
<strong>of</strong> data in transit requirement.<br />
Response. Certified EHR Technology must include the capability to encrypt and<br />
decrypt information regardless <strong>of</strong> the transmission method used. This <strong>certification</strong><br />
criterion and related standard do not specify the circumstances under which encryption<br />
and decryption must be performed; they simply require the capability. If an eligible<br />
pr<strong>of</strong>essional or eligible hospital determines that encryption is an appropriate and<br />
necessary safeguard, we believe that Certified EHR Technology should provide the<br />
capability to implement encryption. Overall, we want to ensure that Certified EHR<br />
Technology is capable <strong>of</strong> assisting eligible pr<strong>of</strong>essionals and eligible hospitals to<br />
implement more secure technical solutions if they determine, based on their risk analysis,<br />
that technical safeguards such as encryption are reasonable and appropriate, or required.<br />
Comment. One commenter requested further clarification <strong>of</strong> the phrase<br />
“encrypted and integrity protected link.” Several commenters recommended that<br />
Transport Layer Security (TLS) ought to be specifically named as a required protocol.<br />
Page 116 <strong>of</strong> 228