ehr onc final certification - Department of Health Care Services
ehr onc final certification - Department of Health Care Services
ehr onc final certification - Department of Health Care Services
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
it has not been altered when it has been electronically exchanged. We recognize that<br />
certain situations may not be conducive to the use <strong>of</strong> hashes, which is why, as we noted<br />
above, we do not specify the instances in which hashing must be used, just that Certified<br />
EHR Technology include these capabilities.<br />
Comment. One commenter stated that secure transmission requirements are<br />
“inappropriate” because they do not support any meaningful use requirements.<br />
Response. We disagree. Meaningful use requires the electronic exchange <strong>of</strong><br />
health information and the protection <strong>of</strong> such information. We believe that the only<br />
practical and effective way that electronic health information can be exchanged in a<br />
meaningful manner is if the integrity <strong>of</strong> the information can be maintained. Information<br />
“integrity” is also one <strong>of</strong> the three pillars <strong>of</strong> securing or “protecting” electronic<br />
information.<br />
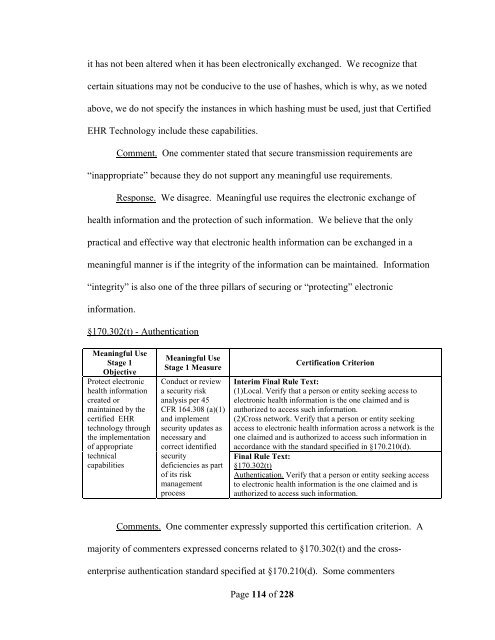
§170.302(t) - Authentication<br />
Meaningful Use<br />
Stage 1<br />
Objective<br />
Protect electronic<br />
health information<br />
created or<br />
maintained by the<br />
certified EHR<br />
technology through<br />
the implementation<br />
<strong>of</strong> appropriate<br />
technical<br />
capabilities<br />
Meaningful Use<br />
Stage 1 Measure<br />
Conduct or review<br />
a security risk<br />
analysis per 45<br />
CFR 164.308 (a)(1)<br />
and implement<br />
security updates as<br />
necessary and<br />
correct identified<br />
security<br />
deficiencies as part<br />
<strong>of</strong> its risk<br />
management<br />
process<br />
Page 114 <strong>of</strong> 228<br />
Certification Criterion<br />
Interim Final Rule Text:<br />
(1)Local. Verify that a person or entity seeking access to<br />
electronic health information is the one claimed and is<br />
authorized to access such information.<br />
(2)Cross network. Verify that a person or entity seeking<br />
access to electronic health information across a network is the<br />
one claimed and is authorized to access such information in<br />
accordance with the standard specified in §170.210(d).<br />
Final Rule Text:<br />
§170.302(t)<br />
Authentication. Verify that a person or entity seeking access<br />
to electronic health information is the one claimed and is<br />
authorized to access such information.<br />
Comments. One commenter expressly supported this <strong>certification</strong> criterion. A<br />
majority <strong>of</strong> commenters expressed c<strong>onc</strong>erns related to §170.302(t) and the cross-<br />
enterprise authentication standard specified at §170.210(d). Some commenters