Part 1: General - Computer Security Resource Center - National ...
Part 1: General - Computer Security Resource Center - National ...
Part 1: General - Computer Security Resource Center - National ...
You also want an ePaper? Increase the reach of your titles
YUMPU automatically turns print PDFs into web optimized ePapers that Google loves.
March, 2007<br />
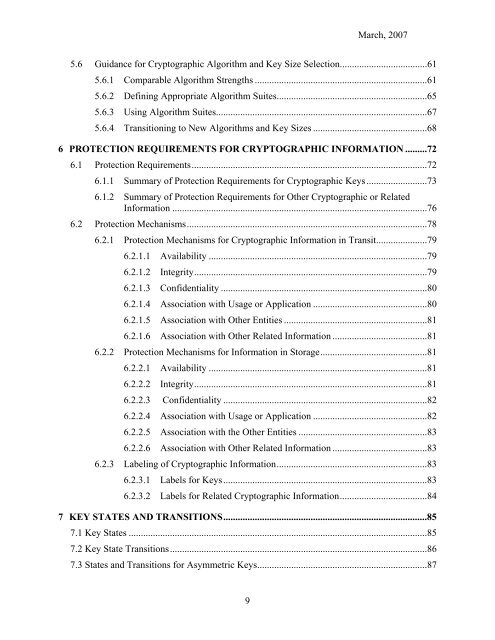
5.6 Guidance for Cryptographic Algorithm and Key Size Selection....................................61<br />
5.6.1 Comparable Algorithm Strengths .......................................................................61<br />
5.6.2 Defining Appropriate Algorithm Suites..............................................................65<br />
5.6.3 Using Algorithm Suites.......................................................................................67<br />
5.6.4 Transitioning to New Algorithms and Key Sizes ...............................................68<br />
6 PROTECTION REQUIREMENTS FOR CRYPTOGRAPHIC INFORMATION .........72<br />
6.1 Protection Requirements.................................................................................................72<br />
6.1.1 Summary of Protection Requirements for Cryptographic Keys.........................73<br />
6.1.2 Summary of Protection Requirements for Other Cryptographic or Related<br />
Information .........................................................................................................76<br />
6.2 Protection Mechanisms...................................................................................................78<br />
6.2.1 Protection Mechanisms for Cryptographic Information in Transit.....................79<br />
6.2.1.1 Availability ..........................................................................................79<br />
6.2.1.2 Integrity................................................................................................79<br />
6.2.1.3 Confidentiality .....................................................................................80<br />
6.2.1.4 Association with Usage or Application ...............................................80<br />
6.2.1.5 Association with Other Entities ...........................................................81<br />
6.2.1.6 Association with Other Related Information .......................................81<br />
6.2.2 Protection Mechanisms for Information in Storage............................................81<br />
6.2.2.1 Availability ..........................................................................................81<br />
6.2.2.2 Integrity................................................................................................81<br />
6.2.2.3 Confidentiality ....................................................................................82<br />
6.2.2.4 Association with Usage or Application ...............................................82<br />
6.2.2.5 Association with the Other Entities .....................................................83<br />
6.2.2.6 Association with Other Related Information .......................................83<br />
6.2.3 Labeling of Cryptographic Information..............................................................83<br />
6.2.3.1 Labels for Keys....................................................................................83<br />
6.2.3.2 Labels for Related Cryptographic Information....................................84<br />
7 KEY STATES AND TRANSITIONS....................................................................................85<br />
7.1 Key States ...........................................................................................................................85<br />
7.2 Key State Transitions..........................................................................................................86<br />
7.3 States and Transitions for Asymmetric Keys......................................................................87<br />
9