Download File - Computer Networks & Information Security
Download File - Computer Networks & Information Security Download File - Computer Networks & Information Security
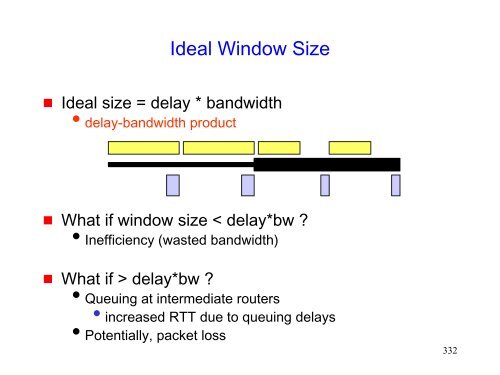
Ideal Window Size Ideal size = delay * bandwidth delay-bandwidth product What if window size < delay*bw ? Inefficiency (wasted bandwidth) What if > delay*bw ? Queuing at intermediate routers • increased RTT due to queuing delays Potentially, packet loss 332
How does TCP detect a packet loss? Retransmission timeout (RTO) Duplicate acknowledgements 333
- Page 281 and 282: Fairness Issue Assume that initial
- Page 283 and 284: MACAW Solution for Fairness When a
- Page 285 and 286: Distributed Fair Scheduling (DFS) [
- Page 287 and 288: Impact of Collisions After collisi
- Page 289 and 290: Distributed Fair Scheduling DFS us
- Page 291 and 292: Fairness in Multi-Hop Networks Not
- Page 293 and 294: Balanced MAC degree of node j p_ij
- Page 295 and 296: Balanced MAC Results show that it
- Page 297 and 298: Estimation-Based Fair MAC Fair sha
- Page 299 and 300: Proportional Fair Contention Resolu
- Page 301 and 302: Sender-Initiated Protocols The pro
- Page 303 and 304: Using Receiver’s Help in a Sender
- Page 305 and 306: Receiver-Based Adaptive Rate Contro
- Page 307 and 308: Capacity and MAC Protocols The MAC
- Page 309 and 310: Energy Conserving MAC Since many m
- Page 311 and 312: A Power Aware Multi-Access Protocol
- Page 313 and 314: PAMAS PAMAS uses a control channel
- Page 315 and 316: Another Proposal in PAMAS To avoid
- Page 317 and 318: UDP on Mobile Ad Hoc Networks 317
- Page 319 and 320: UDP Performance Several relevant s
- Page 321 and 322: UDP Performance Difficult to ident
- Page 323 and 324: Overview of Transmission Control Pr
- Page 325 and 326: Transmission Control Protocol (TCP)
- Page 327 and 328: Cumulative Acknowledgements A new
- Page 329 and 330: Window Based Flow Control Sliding
- Page 331: Window Based Flow Control Congesti
- Page 335 and 336: Retransmission Timeout (RTO) calcul
- Page 337 and 338: Fast Retransmission Timeouts can t
- Page 339 and 340: Congestion Avoidance and Control S
- Page 341 and 342: Congestion Control On detecting a
- Page 343 and 344: Congestion window (segments) 25 20
- Page 345 and 346: ssthresh = Fast Recovery min(cwnd,
- Page 347 and 348: Slow-start Congestion avoidance F
- Page 349 and 350: Performance of TCP Several factors
- Page 351 and 352: Random Errors May Cause Fast Retran
- Page 353 and 354: Random Errors May Cause Fast Retran
- Page 355 and 356: Random Errors May Cause Fast Retran
- Page 357 and 358: Sometimes Congestion Response May b
- Page 359 and 360: Burst Errors May Cause Timeouts If
- Page 361 and 362: Impact of Transmission Errors TCP
- Page 363 and 364: This Tutorial This tutorial consid
- Page 365 and 366: Mobile Ad Hoc Networks Mobility ca
- Page 367 and 368: Impact of Multi-Hop Wireless Paths
- Page 369 and 370: Ideal Throughput f(i) = fraction o
- Page 371 and 372: Impact of Mobility 20 m/s 30 m/s Id
- Page 373 and 374: Actual throughput But not always
- Page 375 and 376: mobility causes link breakage, resu
- Page 377 and 378: B C A Why Does Throughput Improve?
- Page 379 and 380: Network feedback How to Improve Thr
- Page 381 and 382: Actual throughput Performance Impro
Ideal Window Size<br />
Ideal size = delay * bandwidth<br />
delay-bandwidth product<br />
What if window size < delay*bw ?<br />
Inefficiency (wasted bandwidth)<br />
What if > delay*bw ?<br />
Queuing at intermediate routers<br />
• increased RTT due to queuing delays<br />
Potentially, packet loss<br />
332