Beginning SQL
Beginning SQL Beginning SQL
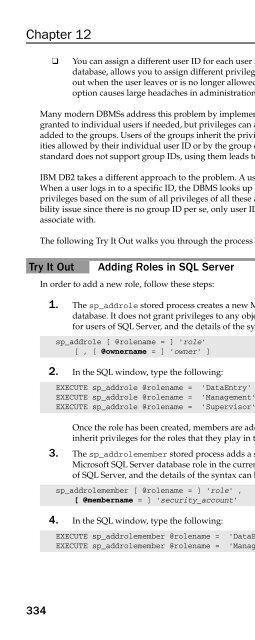
Chapter 12 ❑ You can assign a different user ID for each user in the group. This distinguishes the users in the database, allows you to assign different privileges as needed later, and allows locking that user out when the user leaves or is no longer allowed access to the database. Unfortunately, this option causes large headaches in administration when many users need access to the database. Many modern DBMSs address this problem by implementing the group or role concept. Privileges can be granted to individual users if needed, but privileges can also be granted to groups, and then users can be added to the groups. Users of the groups inherit the privileges of the group. Users can then perform activities allowed by their individual user ID or by the group or groups to which they belong. Because the SQL standard does not support group IDs, using them leads to non-portability between DBMS systems. IBM DB2 takes a different approach to the problem. A user ID can be associated with other user IDs. When a user logs in to a specific ID, the DBMS looks up all the associated IDs and builds a merged set of privileges based on the sum of all privileges of all these associated IDs. This neatly sidesteps the portability issue since there is no group ID per se, only user IDs with privileges that any other user ID can associate with. The following Try It Out walks you through the process of adding a new role to your database. Try It Out Adding Roles in SQL Server 334 In order to add a new role, follow these steps: 1. The sp_addrole stored process creates a new Microsoft SQL Server role in the current database. It does not grant privileges to any objects in the database. This syntax is useful only for users of SQL Server, and the details of the syntax can be found in Books Online. sp_addrole [ @rolename = ] ‘role’ [ , [ @ownername = ] ‘owner’ ] 2. In the SQL window, type the following: EXECUTE sp_addrole @rolename = ‘DataEntry’ EXECUTE sp_addrole @rolename = ‘Management’ EXECUTE sp_addrole @rolename = ‘Supervisor’ Once the role has been created, members are added to the role. This step allows members to inherit privileges for the roles that they play in the database. 3. The sp_addrolemember stored process adds a security account as a member of an existing Microsoft SQL Server database role in the current database. This syntax is useful only for users of SQL Server, and the details of the syntax can be found in Books Online. sp_addrolemember [ @rolename = ] ‘role’ , [ @membername = ] ‘security_account’ 4. In the SQL window, type the following: EXECUTE sp_addrolemember @rolename = ‘DataEntry’, @membername = ‘John’ EXECUTE sp_addrolemember @rolename = ‘Management’, @membername = ‘Lynn’
- Page 658: SAVE TRANSACTION Select Update Begi
- Page 662: Figure 11-5 Begin Transaction Delet
- Page 666: In spite of all of these performanc
- Page 670: Shared A shared lock essentially me
- Page 674: of record locks, the DBMS may decid
- Page 678: No updates, additions, or deletions
- Page 682: International Board Manufacturer ha
- Page 686: contention. You could wrap your new
- Page 690: Summary Transactions ensure that us
- Page 696: Chapter 12 328 SQL security is cent
- Page 700: Chapter 12 Creating User IDs Figure
- Page 704: Chapter 12 3. In the SQL window, ty
- Page 710: How It Works After you run this sta
- Page 714: check constraints can be used in a
- Page 718: You could then give SELECT privileg
- Page 722: Limitations on Views Views are by t
- Page 726: GRANT SELECT (NAME, SSN, SALARY) ON
- Page 730: Betsey also grants privileges to Ji
- Page 734: The CASCADE option tells the DBMS t
- Page 738: 13 Database Tuning SQL is a languag
- Page 742: Perhaps this doesn’t sound remote
- Page 746: When an application asks for data f
- Page 750: The point of all the discussion of
- Page 754: How Do You Do It? And herein lies t
Chapter 12<br />
❑ You can assign a different user ID for each user in the group. This distinguishes the users in the<br />
database, allows you to assign different privileges as needed later, and allows locking that user<br />
out when the user leaves or is no longer allowed access to the database. Unfortunately, this<br />
option causes large headaches in administration when many users need access to the database.<br />
Many modern DBMSs address this problem by implementing the group or role concept. Privileges can be<br />
granted to individual users if needed, but privileges can also be granted to groups, and then users can be<br />
added to the groups. Users of the groups inherit the privileges of the group. Users can then perform activities<br />
allowed by their individual user ID or by the group or groups to which they belong. Because the <strong>SQL</strong><br />
standard does not support group IDs, using them leads to non-portability between DBMS systems.<br />
IBM DB2 takes a different approach to the problem. A user ID can be associated with other user IDs.<br />
When a user logs in to a specific ID, the DBMS looks up all the associated IDs and builds a merged set of<br />
privileges based on the sum of all privileges of all these associated IDs. This neatly sidesteps the portability<br />
issue since there is no group ID per se, only user IDs with privileges that any other user ID can<br />
associate with.<br />
The following Try It Out walks you through the process of adding a new role to your database.<br />
Try It Out Adding Roles in <strong>SQL</strong> Server<br />
334<br />
In order to add a new role, follow these steps:<br />
1. The sp_addrole stored process creates a new Microsoft <strong>SQL</strong> Server role in the current<br />
database. It does not grant privileges to any objects in the database. This syntax is useful only<br />
for users of <strong>SQL</strong> Server, and the details of the syntax can be found in Books Online.<br />
sp_addrole [ @rolename = ] ‘role’<br />
[ , [ @ownername = ] ‘owner’ ]<br />
2. In the <strong>SQL</strong> window, type the following:<br />
EXECUTE sp_addrole @rolename = ‘DataEntry’<br />
EXECUTE sp_addrole @rolename = ‘Management’<br />
EXECUTE sp_addrole @rolename = ‘Supervisor’<br />
Once the role has been created, members are added to the role. This step allows members to<br />
inherit privileges for the roles that they play in the database.<br />
3. The sp_addrolemember stored process adds a security account as a member of an existing<br />
Microsoft <strong>SQL</strong> Server database role in the current database. This syntax is useful only for users<br />
of <strong>SQL</strong> Server, and the details of the syntax can be found in Books Online.<br />
sp_addrolemember [ @rolename = ] ‘role’ ,<br />
[ @membername = ] ‘security_account’<br />
4. In the <strong>SQL</strong> window, type the following:<br />
EXECUTE sp_addrolemember @rolename = ‘DataEntry’, @membername = ‘John’<br />
EXECUTE sp_addrolemember @rolename = ‘Management’, @membername = ‘Lynn’