computing lives - FTP Directory Listing
computing lives - FTP Directory Listing
computing lives - FTP Directory Listing
Create successful ePaper yourself
Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software.
›± ¨ª ¨ § ±± § ±± ±´¨ ⁄±Æ ø ø¨ ± ¨Æ´ ¨ ± ¥ªø ª ¥ µ ªÆª ÕªøÆ ´ª § “ª®¨ –ø ª<br />
¨¨ ÊÒÒ©©©Ú ± ´¨ªÆÚ±Æ<br />
ÀÃäŒ ›ÿfl—ÕÙ –Ú Í<br />
fl“fl‘« “Ÿ fl“<br />
fl“› ¤“à ՛Œ –ÃÙ –Ú ÈÍ<br />
œÀ¤Õà —“ “Ÿ<br />
“ Õ fi ‘ ë٠–Ú ËÏ<br />
›± ¨ª ¨ § ±± § ±± ±´¨ ⁄±Æ ø ø¨ ± ¨Æ´ ¨ ± ¥ªø ª ¥ µ ªÆª<br />
ÕªøÆ ´ª § “ª®¨ –ø ª
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
Editor in Chief<br />
Carl K. Chang<br />
Iowa State University<br />
____________<br />
chang@cs.iastate.edu<br />
Associate Editor<br />
in Chief<br />
Sumi Helal<br />
University of Florida<br />
__________<br />
helal@cise.ufl.edu<br />
Area Editors<br />
Computer Architectures<br />
Steven K. Reinhardt<br />
AMD<br />
Databases and Information<br />
Retrieval<br />
Erich Neuhold<br />
University of Vienna<br />
Distributed Systems<br />
Jean Bacon<br />
University of Cambridge<br />
Graphics and Multimedia<br />
Oliver Bimber<br />
Johannes Kepler University Linz<br />
High-Performance Computing<br />
Vladimir Getov<br />
University of Westminster<br />
Information and<br />
Data Management<br />
Naren Ramakrishnan<br />
Virginia Tech<br />
Multimedia<br />
Savitha Srinivasan<br />
IBM Almaden Research Center<br />
Networking<br />
Ahmed Helmy<br />
University of Florida<br />
Software<br />
Robert B. France<br />
Colorado State University<br />
David M. Weiss<br />
Iowa State University<br />
Editorial Staff<br />
Scott Hamilton<br />
Senior Acquisitions Editor<br />
_____________<br />
shamilton@computer.org<br />
Judith Prow<br />
Managing Editor<br />
___________<br />
jprow@computer.org<br />
Chris Nelson<br />
Senior Editor<br />
James Sanders<br />
Senior Editor<br />
COMPUTER<br />
Associate Editor in Chief,<br />
Research Features<br />
Kathleen Swigger<br />
University of North Texas<br />
__________<br />
kathy@cs.unt.edu<br />
Associate Editor in Chief,<br />
Special Issues<br />
Bill N. Schilit<br />
Google<br />
schilit@computer.org<br />
____________<br />
Column Editors<br />
AI Redux<br />
Naren Ramakrishnan<br />
Virginia Tech<br />
Education<br />
Ann E.K. Sobel<br />
Miami University<br />
Embedded Computing<br />
Tom Conte<br />
Georgia Tech<br />
Green IT<br />
Kirk W. Cameron<br />
Virginia Tech<br />
Industry Perspective<br />
Sumi Helal<br />
University of Florida<br />
IT Systems Perspectives<br />
Richard G. Mathieu<br />
James Madison University<br />
Invisible Computing<br />
Albrecht Schmidt<br />
University of Duisburg-Essen<br />
The Known World<br />
David A. Grier<br />
George Washington University<br />
The Profession<br />
Neville Holmes<br />
University of Tasmania<br />
Security<br />
Jeffrey M. Voas<br />
NIST<br />
Contributing Editors<br />
Lee Garber<br />
Bob Ward<br />
Design and Production<br />
Larry Bauer<br />
Design<br />
Olga D’Astoli<br />
Cover Design<br />
Kate Wojogbe<br />
Computing Practices<br />
Rohit Kapur<br />
rohit.kapur@synopsys.com<br />
________________<br />
Perspectives<br />
Bob Colwell<br />
bob.colwell@comcast.net<br />
_____________<br />
Web Editor<br />
Ron Vetter<br />
vetterr@uncw.edu<br />
___________<br />
Software Technologies<br />
Mike Hinchey<br />
Lero—the Irish Software<br />
Engineering Research Centre<br />
Web Technologies<br />
Simon S.Y. Shim<br />
San Jose State University<br />
Advisory Panel<br />
Thomas Cain<br />
University of Pittsburgh<br />
Doris L. Carver<br />
Louisiana State University<br />
Ralph Cavin<br />
Semiconductor Research Corp.<br />
Dan Cooke<br />
Texas Tech University<br />
Ron Hoelzeman<br />
University of Pittsburgh<br />
Naren Ramakrishnan<br />
Virginia Tech<br />
Ron Vetter<br />
University of North Carolina,<br />
Wilmington<br />
Alf Weaver<br />
University of Virginia<br />
Administrative<br />
Staff<br />
Products and<br />
Services Director<br />
Evan Butterfield<br />
Manager,<br />
Editorial Services<br />
Jennifer Stout<br />
2010 IEEE Computer<br />
Society President<br />
James D. Isaak<br />
cspresident2010@jimisaak.com<br />
__________________<br />
CS Publications Board<br />
David A. Grier (chair), David<br />
Bader, Angela R. Burgess, Jean-<br />
Luc Gaudiot, Phillip Laplante,<br />
Dejan Milojičić, Linda I. Shafer,<br />
Dorée Duncan Seligmann, Don<br />
Shafer, Steve Tanimoto, and<br />
Roy Want<br />
CS Magazine<br />
Operations Committee<br />
Dorée Duncan Seligmann<br />
(chair), David Albonesi, Isabel<br />
Beichl, Carl Chang, Krish<br />
Chakrabarty, Nigel Davies, Fred<br />
Douglis, Hakan Erdogmus, Carl<br />
E. Landwehr, Simon Liu, Dejan<br />
Milojičić, John Smith, Gabriel<br />
Taubin, Fei-Yue Wang, and<br />
Jeffrey R. Yost<br />
Senior Business<br />
Development Manager<br />
Sandy Brown<br />
Senior Advertising<br />
Coordinator<br />
Marian Anderson<br />
Circulation: Computer (ISSN 0018-9162) is published monthly by the IEEE Computer Society. IEEE Headquarters, Three Park Avenue, 17th Floor, New York, NY<br />
10016-5997; IEEE Computer Society Publications Office, 10662 Los Vaqueros Circle, PO Box 3014, Los Alamitos, CA 90720-1314; voice +1 714 821 8380; fax +1<br />
714 821 4010; IEEE Computer Society Headquarters, 2001 L Street NW, Suite 700, Washington, DC 20036. IEEE Computer Society membership includes $19 for<br />
a subscription to Computer magazine. Nonmember subscription rate available upon request. Single-copy prices: members $20.00; nonmembers $99.00.<br />
Postmaster: Send undelivered copies and address changes to Computer, IEEE Membership Processing Dept., 445 Hoes Lane, Piscataway, NJ 08855. Periodicals<br />
Postage Paid at New York, New York, and at additional mailing offices. Canadian GST #125634188. Canada Post Corporation (Canadian distribution) publications<br />
mail agreement number 40013885. Return undeliverable Canadian addresses to PO Box 122, Niagara Falls, ON L2E 6S8 Canada. Printed in USA.<br />
Editorial: Unless otherwise stated, bylined articles, as well as product and service descriptions, reflect the author’s or firm’s opinion. Inclusion in Computer<br />
does not necessarily constitute endorsement by the IEEE or the Computer Society. All submissions are subject to editing for style, clarity, and space.<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
Almost $90 million in server room<br />
research. Now yours is FREE!<br />
Implementing Energy<br />
Efficient Data Centers<br />
“ Implementing Energy<br />
Efficient Data Centers”<br />
White Paper #114<br />
$ 65 00 FREE!<br />
Power er and an and<br />
Cooling Coo oolin ling i g Ca Capacity Ca Capacity CThe pa pacity acityAdvantages<br />
of Row<br />
Management Ma for Data and Centers Rack-Oriented<br />
Five ve Basic Steps for Efficient<br />
Cooling Architectures<br />
Space pace Organization within<br />
High-Density gh-Density for Enclosures<br />
Data Centers<br />
White Paper #130<br />
An Improved Architecture<br />
for High-Efficiency,<br />
High-Density Data Centers<br />
White Paper #130<br />
“ An Improved Architecture<br />
for High-Efficiency,<br />
High-Density<br />
Data Centers”<br />
White Paper #126<br />
$ 120 00 FREE!<br />
Time well spent...<br />
The Advantages of Row Row<br />
and Rack-Oriented<br />
Cooling Architectures res<br />
for Data Centers<br />
White Paper #130<br />
White Paper #130<br />
“ The Advantages of<br />
Row and Rack-Oriented<br />
Cooling Architectures<br />
for Data Centers”<br />
White Paper #130<br />
$ 85 00 FREE!<br />
Deploying ng High-Density<br />
High-Density<br />
Zones in n a a Low-Density<br />
Low-Density<br />
Data Center nter<br />
White White Paper Paper #130 #130<br />
“ Deploying High-Density<br />
Zones in a Low-Density<br />
Data Center”<br />
White Paper #134<br />
$ 00<br />
115 FREE!<br />
Power and Cooling<br />
Capacity Management<br />
for Data Centers<br />
White Paper #150<br />
©2010 Schneider Electric Industries SAS, All Rights Reserved. Schneider Electric and APC are owned by Schneider Electric, or its affiliated companies in the United States and other countries.<br />
<br />
“ Power and Cooling<br />
Capacity Management<br />
for Data Centers”<br />
White Paper #150<br />
$ 00 225<br />
Download FREE APC White Papers to avoid<br />
the most common mistakes in planning<br />
IT power and cooling.<br />
FREE!<br />
Have a plan for your data center.<br />
<br />
<br />
cases, turnover and budget cuts resulted in no plan at all.<br />
Get the answers you need and avoid headaches tomorrow.<br />
<br />
<br />
<br />
yourself money and headaches tomorrow.<br />
<br />
www.apc.com<br />
Choose and download any three white papers<br />
within the next 90 days for FREE!<br />
Visit www.apc.com/promo Key Code s145w x6165 <br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
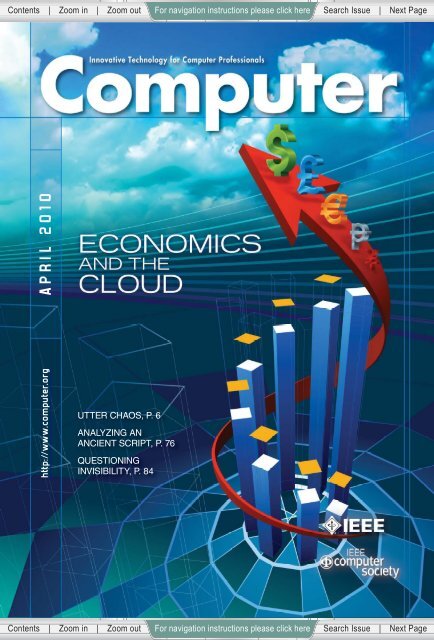
CONTENTS<br />
ABOUT THIS ISSUE<br />
Growing interest in cloud <strong>computing</strong> also raises the<br />
question of cost/benefit. In this issue, we feature an<br />
article describing a federated, open-source cloud platform<br />
that lowers the entry barriers to systems and<br />
applications research communities, an economic model<br />
for determining whether to lease or buy storage, and an<br />
analysis of energy consumption and battery life in<br />
mobile devices offloading computation to the cloud. We<br />
also look at puzzle-based learning, ethical codes of conduct<br />
in the legal realm, and the linkage of software<br />
development and business strategy.<br />
COMPUTING PRACTICES<br />
20 Puzzle-Based Learning for<br />
Engineering and Computer<br />
Science<br />
Nickolas Falkner, Raja Sooriamurthi,<br />
and Zbigniew Michalewicz<br />
To attract, motivate, and retain students and<br />
increase their mathematical awareness and<br />
problem-solving skills, universities are<br />
introducing courses or seminars that explore<br />
puzzle-based learning. The authors introduce<br />
and define this learning approach, describe<br />
course variations, and highlight early student<br />
feedback.<br />
PERSPECTIVES<br />
29 Using Codes of Conduct<br />
to Resolve Legal Disputes<br />
Peter Aiken, Robert M. Stanley, Juanita<br />
Billings, and Luke Anderson<br />
In the absence of other published standards of<br />
care, it is reasonable for contractual parties to<br />
rely on an applicable, widely available code of<br />
conduct to guide expectations.<br />
COVER FEATURES<br />
35 Open Cirrus: A Global<br />
Cloud Computing Testbed<br />
Arutyun I. Avetisyan, Roy Campbell, Indranil<br />
Gupta, Michael T. Heath, Steven Y. Ko,<br />
Gregory R. Ganger, Michael A. Kozuch,<br />
David O’Hallaron, Marcel Kunze, Thomas T.<br />
Kwan, Kevin Lai, Martha Lyons, Dejan S.<br />
Milojicic, Hing Yan Lee, Yeng Chai Soh,<br />
http://computer.org/computer<br />
For more information on <strong>computing</strong> topics, visit the Computer Society Digital Library at www.computer.org/csdl.<br />
Ng Kwang Ming, Jing-Yuan Luke,<br />
and Han Namgoong<br />
Open Cirrus is a cloud <strong>computing</strong> testbed<br />
that, unlike existing alternatives, federates<br />
distributed data centers. It aims to spur<br />
innovation in systems and applications<br />
research and catalyze development of an<br />
open source service stack for the cloud.<br />
44 To Lease or Not to Lease<br />
from Storage Clouds<br />
Edward Walker, Walter Brisken,<br />
and Jonathan Romney<br />
Storage clouds are online services for leasing<br />
disk storage. A new modeling tool,<br />
formulated from empirical data spanning<br />
many years, lets organizations rationally<br />
evaluate the benefit of using storage clouds<br />
versus purchasing hard disk drives.<br />
51 Cloud Computing for Mobile<br />
Users: Can Offloading<br />
Computation Save Energy?<br />
Karthik Kumar and Yung-Hsiang Lu<br />
The cloud heralds a new era of <strong>computing</strong><br />
where application services are provided<br />
through the Internet. Cloud <strong>computing</strong> can<br />
enhance the <strong>computing</strong> capability of mobile<br />
systems, but is it the ultimate solution for<br />
extending such systems’ battery lifetimes?<br />
RESEARCH FEATURE<br />
57 Linking Software<br />
Development and<br />
Business Strategy<br />
through Measurement<br />
Victor R. Basili, Mikael Lindvall, Myrna<br />
Regardie, Carolyn Seaman, Jens Heidrich,<br />
Jürgen Münch, Dieter Rombach,<br />
and Adam Trendowicz<br />
The GQM + Strategies approach extends the<br />
goal/question/metric paradigm for<br />
measuring the success or failure of goals and<br />
strategies, adding enterprise-wide support<br />
for determining action on the basis of<br />
measurement results. An organization can<br />
thus integrate its measurement program<br />
across all levels.<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
IEEE Computer Society: http://computer.org<br />
Computer: http://computer.org/computer<br />
computer@computer.org<br />
___________<br />
IEEE Computer Society Publications Office: +1 714 821 8380<br />
Cover image © Lolaferari Dreamstime.com<br />
6 The Known World<br />
Utter Chaos<br />
David Alan Grier<br />
10 32 & 16 Years Ago<br />
Computer, April 1978 and 1994<br />
Neville Holmes<br />
NEWS<br />
13 Technology News<br />
Will HTML 5 Restandardize the Web?<br />
Steven J. Vaughan-Nichols<br />
16 News Briefs<br />
Linda Dailey Paulson<br />
MEMBERSHIP NEWS<br />
66 IEEE Computer Society<br />
Connection<br />
69 Call and Calendar<br />
COLUMNS<br />
76 AI Redux<br />
Probabilistic Analysis of an Ancient<br />
Undeciphered Script<br />
Rajesh P.N. Rao<br />
81 Software Technologies<br />
When TV Dies, Will It Go to the Cloud?<br />
Karin Breitman, Markus Endler, Rafael<br />
Pereira, and Marcello Azambuja<br />
Flagship Publication of the IEEE<br />
Computer Society<br />
April 2010, Volume 43, Number 4<br />
84 Invisible Computing<br />
Questioning Invisibility<br />
Leah Buechley<br />
87 Education<br />
Cutting Across the Disciplines<br />
Jim Vallino<br />
90 Security<br />
Integrating Legal and Policy Factors in<br />
Cyberpreparedness<br />
James Bret Michael, John F. Sarkesain,<br />
Thomas C. Wingfield, Georgios Dementis,<br />
and Gonçalo Nuno Baptista de Sousa<br />
96 The Profession<br />
Computing a Better World<br />
Kai A. Olsen<br />
DEPARTMENTS<br />
4 Elsewhere in the CS<br />
71 Computer Society Information<br />
72 Career Opportunities<br />
74 Advertiser/Product Index<br />
93 Bookshelf<br />
Reuse Rights and Reprint Permissions: Educational or personal use of this<br />
material is permitted without fee, provided such use: 1) is not made for profit;<br />
2) includes this notice and a full citation to the original work on the first page of<br />
the copy; and 3) does not imply IEEE endorsement of any third-party products<br />
or services. Authors and their companies are permitted to post their IEEE-copyrighted material on<br />
their own Web servers without permission, provided that the IEEE copyright notice and a full citation<br />
to the original work appear on the first screen of the posted copy.<br />
Permission to reprint/republish this material for commercial, advertising, or promotional purposes<br />
or for creating new collective works for resale or redistribution must be obtained from the IEEE by<br />
writing to the IEEE Intellectual Property Rights Office, 445 Hoes Lane, Piscataway, NJ 08854-4141<br />
or pubs-permissions@ieee.org. _______________ Copyright © 2010 IEEE. All rights reserved.<br />
Abstracting and Library Use: Abstracting is permitted with credit to the source. Libraries are permitted<br />
to photocopy for private use of patrons, provided the per-copy fee indicated in the code at<br />
the bottom of the first page is paid through the Copyright Clearance Center, 222 Rosewood Drive,<br />
Danvers, MA 01923.<br />
IEEE prohibits discrimination, harassment, and bullying. For more information, visit www.ieee.org/<br />
______________________<br />
web/aboutus/whatis/policies/p9-26.html.<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
4<br />
ELSEWHERE IN THE CS<br />
Computer Highlights Society Magazines<br />
The IEEE Computer Society offers a lineup<br />
of 13 peer-reviewed technical magazines<br />
that cover cutting-edge topics in <strong>computing</strong><br />
including scientific applications, design and<br />
test, security, Internet <strong>computing</strong>, machine intelligence,<br />
digital graphics, and computer history. Select articles from<br />
recent issues of Computer Society magazines are highlighted<br />
below.<br />
The March/April issue of Software features an overview<br />
of tools and technologies for improved collaboration titled<br />
“Collaboration Tools for Global Software Engineering,” by<br />
Filippo Lanubile, Christof Ebert, Rafael Prikladnicki, and<br />
Aurora Vizcaíno. Effective tool support for collaboration<br />
is a strategic initiative for any company with distributed<br />
resources, no matter whether the strategy involves offshore<br />
development, outsourcing, or supplier networks. Software<br />
needs to be shared, and appropriate tool support is the only<br />
way to do this efficiently, consistently, and securely.<br />
No single solution has yet emerged to unify communications<br />
among the various and proliferating messaging<br />
systems available today. In “Understanding Unified Messaging,”<br />
in the January/February issue of IT Pro, Clinton M.<br />
Banner of Alcatel-Lucent surveys the issues and solutions—<br />
both proprietary and open—that are in development.<br />
“Integrating Visualization and Interaction Research to<br />
Improve Scientific Workflows,” by the University of Minnesota’s<br />
Daniel F. Keefe, identifies three goals—improving<br />
accuracy, linking multiple visualization strategies, and<br />
making data analysis more fluid—that serve as a guide<br />
for future interactive-visualization research targeted<br />
COMPUTER<br />
at improving visualization tools’ impact on scientific<br />
workflows.<br />
The article, which appears in the March/April issue of<br />
CG&A, also offers four examples that illustrate the potential<br />
and challenges of integrating visualization research and<br />
interaction research: 3D selection techniques in brain visualizations,<br />
interactive multiview scientific visualizations,<br />
fluid pen- and touch-based interfaces for visualization, and<br />
modeling human performance in interactive visualizationrelated<br />
tasks.<br />
The Cell Broadband Engine is a heterogeneous chip<br />
multiprocessor that combines a PowerPC processor core<br />
with eight single-instruction, multiple-data accelerator<br />
cores and delivers high performance on many computationally<br />
intensive codes. “Application Acceleration with the<br />
Cell Broadband Engine” by Guochun Shi, Volodymyr Kindratenko,<br />
Frederico Pratas, Pedro Trancoso, and Michael<br />
Gschwind appears in the January/February issue of CiSE.<br />
Demand-response systems provide detailed powerconsumption<br />
data to utilities and those angling to assist<br />
consumers in understanding and managing energy use.<br />
Such data reveals information about in-home activities that<br />
can be mined and combined with other readily available<br />
information to discover more about occupants’ activities.<br />
“Inferring Personal Information from Demand-Response<br />
Systems” by Mikhail Lisovich, Deirdre Mulligan, and Stephen<br />
Wicker appears in the January/February issue of S&P.<br />
The March/April issue of Intelligent Systems focuses<br />
on new paradigms in business and market intelligence.<br />
The emergence of user-generated Web 2.0 content offers<br />
Published by the IEEE Computer Society 0018-9162/10/$26.00 © 2010 IEEE<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
opportunities to listen to the voice of the market as articulated<br />
by a vast number of business constituents. An<br />
overview in this issue of IS includes five short articles by<br />
distinguished experts on today’s trends in business and<br />
market intelligence. Each article presents a unique, innovative<br />
research framework, computational methods, and<br />
selected results and examples.<br />
In the world of Web 2.0, Internet 2, and open systems,<br />
most learning is still done in traditional classrooms. As<br />
education costs continue to far outpace inflation, what is<br />
e-learning’s role? In the March/April issue of Internet Computing,<br />
Stephen Ruth of George Mason University addresses<br />
these questions in “Is E-Learning Really Working? The<br />
Trillion Dollar Question.”<br />
Spectacles is a hardware/software platform developed<br />
from off-the-shelf components and ready for market. It<br />
includes local computation and communication facilities,<br />
an integrated power supply, and modular system building<br />
blocks such as sensors, voice-to-text and text-to-speech<br />
components, localization and positioning units, and microdisplay<br />
units. Its see-through display components are<br />
integrated into eyeglass frames. “Wearable Displays—for<br />
Everyone!” by Alois Ferscha and Simon Vogl appears in the<br />
January-March issue of PvC.<br />
The January/February issue of Micro continues a<br />
seven-year tradition of featuring top picks from computer<br />
architecture conferences. Guest editor Trevor Mudge of<br />
the University of Michigan participated in a program committee<br />
of 31 computer architects from both industry and<br />
academia. The committee reviewed 91 submissions, selecting<br />
13 papers for abridgment in the magazine. Topics range<br />
from practical prefetching to application-domain-specific<br />
<strong>computing</strong> and nonvolatile memory.<br />
Current media-synchronization techniques range from<br />
the very theoretical to the very practical. In “Modeling<br />
Media Synchronization with Semiotic Agents,” researchers<br />
from the City University of Hong Kong and the University of<br />
Reading describe a modeling technique for mapping theoretical<br />
models to system implementations. The technique<br />
combines agent technology with semiotics to offer a sound<br />
theoretical framework for expressing and manipulating<br />
media-synchronization attributes in real-world applications.<br />
Read more in the January-March issue of Multimedia.<br />
reduced 70%<br />
reduced 70%<br />
As CMOS technology scales down to the nanometer<br />
range, variation control in semiconductor manufacturing<br />
becomes ever more challenging. Introducing D&T’s March/<br />
April special issue in “Compact Variability Modeling in<br />
Scaled CMOS Design,” guest editors Yu Cao of Arizona State<br />
University and Frank Liu of IBM Austin Research Laboratory<br />
preview five articles that address these challenges.<br />
An article by Fred Brooks, renowned computer scientist<br />
and author of The Mythical Man-Month, opens the first issue<br />
of Annals in 2010. In “Stretch-ing Is Great Exercise—It Gets<br />
You in Shape to Win,” Brooks recounts the history of the<br />
IBM Stretch Project (1955-1961). Although the company lost<br />
$35 million on the project in 1960, Brooks describes how<br />
Stretch drove technologies that enabled the rapid development<br />
of IBM’s successful 7000-series computers and the<br />
architectural innovations of its System/360 product family.<br />
Editor: Bob Ward, Computer; bnward@computer.org<br />
____________<br />
http://computer.org/cn/ELSEWHERE<br />
April Theme:<br />
AGILITY AND<br />
ARCHITECTURE<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
5
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
6<br />
THE KNOWN WORLD<br />
Utter Chaos<br />
As far as I can tell, they live<br />
<strong>lives</strong> of utter chaos. The<br />
three of them, all young<br />
physicians who seem<br />
no older than 16, seize<br />
control of the locker room every<br />
morning. They apparently finish a<br />
rather raucous game just as I arrive<br />
to begin my swim.<br />
They typically appear with an<br />
explosion of noise, a clash of locker<br />
doors, and a litter of sweaty athletic<br />
clothes that bear the seals of expensive<br />
and exclusive institutions of<br />
higher education. They talk as if no<br />
one else is listening, as if they were<br />
standing in the most private seminar<br />
room of the local hospital, albeit<br />
standing buck naked, dripping wet,<br />
and yelling for no good reason.<br />
Surprisingly, they talk not of<br />
women or sports or one of the few<br />
topics of male discourse but of medicine.<br />
They pay inordinate attention<br />
to every corner and fold of their<br />
own bodies and speculate on what<br />
signs of good or ill they find. If you<br />
believe their words, these young doctors<br />
are the most medicated human<br />
beings on the planet. They spend an<br />
unusual amount of time talking about<br />
the medicines that they prescribe<br />
for themselves in much the same<br />
way that a small child will discuss<br />
the color of a recently encountered<br />
COMPUTER<br />
David Alan Grier, George Washington University<br />
No matter what we may believe, scientific practice often begins with<br />
a season when we don’t know what we know.<br />
puppy. One can be grateful that these<br />
physicians know the effects of their<br />
own medicine but simultaneously<br />
worried that these pharmaceuticals<br />
will impair their judgment when they<br />
recommend some treatment.<br />
For the most part, these young<br />
men talk about their cases and the<br />
treatments that they recommend.<br />
Although most of the medical terms<br />
are a complete mystery to the rest of<br />
us, we can all tell that these are young<br />
doctors who don’t know yet how to<br />
be professional physicians. They’re<br />
a little too offended when someone<br />
questions their judgment. They give<br />
far too many details about their<br />
patients and make it far too easy for<br />
the rest of us to identify, or at least<br />
imagine, the individual in question.<br />
These young physicians, in spite<br />
of their enthusiasm, their elite educations,<br />
and their practical experience<br />
with drugs, are still learning how to<br />
organize and discipline their practice.<br />
They’re living a medicine of<br />
utter chaos. Their conversation cycles<br />
around the various bodily systems,<br />
maps every symptom to every possible<br />
cause imaginable, and identifies<br />
extraordinary lists of information that<br />
they would like to extract from their<br />
patients.<br />
Even with this chaos, they’re still<br />
in love with their profession and still<br />
excited to encounter new problems.<br />
Yet they don’t realize that they’re<br />
only now learning to discipline their<br />
professional activity, to build a framework<br />
that will guide their work. Well<br />
before they reach the age of 30, they<br />
will learn to organize their professional<br />
knowledge into a structure that<br />
will guide the rest of their <strong>lives</strong>.<br />
UNINHIBITED SPECULATION<br />
We usually live so completely<br />
within our professional knowledge<br />
that we remember the effort required<br />
to discipline our thoughts only when<br />
we approach a topic that is new to us.<br />
New ideas can dislocate that mental<br />
structure, that vague semantic network,<br />
which gives us a foundation in<br />
the field.<br />
Over the past three months, I have<br />
had many opportunities to demonstrate<br />
that a career in computer<br />
science can still leave you grossly<br />
ignorant of many subjects and completely<br />
disoriented as you try to learn<br />
the basics of a new topic. The search<br />
tools of modern digital libraries give<br />
you little guidance in this work. You<br />
can retrieve hundreds of articles that<br />
seem relevant, spend hours reading<br />
material about some peripheral bit<br />
of research, and never find that key<br />
document describing the basic concepts<br />
of the field.<br />
Published by the IEEE Computer Society 0018-9162/10/$26.00 © 2010 IEEE<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
After years of doing this kind of<br />
research, I’ve learned that all new<br />
fields of scientific endeavor will go<br />
through periods of utter chaos before<br />
they settle into a regular discipline<br />
with well-defined terms, stable categories,<br />
and general methods. The task<br />
of any researcher is to work through<br />
the early literature and find that key<br />
moment when ideas begin to solidify.<br />
THE CHAOS OF<br />
RÖNTGEN’S XfiRAYS<br />
The early days of physics produced<br />
many fields that began in chaos and<br />
moved quickly into order. Few present<br />
a more dramatic story than the discovery<br />
of X-rays by Wilhelm Röntgen<br />
in late 1895. To both scientists and the<br />
public, X-rays seemed to be an entirely<br />
new phenomenon that didn’t exactly<br />
fit into the theories of electricity and<br />
magnetism that had been maturing<br />
over the prior 50 years.<br />
Röntgen discovered X-rays in<br />
early November and was mystified<br />
by them. Being a careful scientist, he<br />
attempted to identify the basic nature<br />
of this radiation. He assembled his<br />
notes from this work into an article<br />
that is little more than a list of observations.<br />
“A Discharge from a large<br />
induction coil is passed through a<br />
Hittorf’s vacuum tube,” he begins.<br />
This apparatus will cause a piece of<br />
paper covered with barium platinocyanide<br />
to glow. “The fluorescence is<br />
still visible at two meters distance,”<br />
he wrote. “It is easy to show that the<br />
origin of the fluorescence lies within<br />
the vacuum tube.”<br />
In the last paragraphs of the article,<br />
Röntgen admitted that he didn’t have<br />
a theory that explained the properties<br />
of X-rays. He rejected as “unlikely” the<br />
idea that they were a form of electromagnetic<br />
radiation and hence related<br />
to visible light. Instead, he speculated<br />
that his discovery was an entirely new<br />
form of energy. “Should not the new<br />
rays,” he asked, “be ascribed to longitudinal<br />
waves in the ether?”<br />
Had X-rays been less novel, had<br />
they not been able to a pass through<br />
soft human tissue and reveal the<br />
hidden bones, then Röntgen’s speculations<br />
about the luminiferous ether<br />
and longitudinal waves would have<br />
percolated through the community<br />
of physicists and would have been<br />
tested in a relatively systematic way.<br />
However, X-rays were indeed novel,<br />
and they could reveal the inner parts<br />
of the human body, so Röntgen’s<br />
ideas quickly moved into the laboratory<br />
and living room.<br />
All new fields of<br />
scientific endeavor<br />
will go through<br />
periods of utter<br />
chaos before they<br />
settle into a regular<br />
discipline with welldefined<br />
terms, stable<br />
categories, and<br />
general methods.<br />
THE EXCITEMENT<br />
OF THE POPULAR PRESS<br />
Barely four weeks after the original<br />
article appeared, news of this<br />
strange new ray reached all the<br />
capitals of Europe. “The invention of<br />
neither the telephone nor the phonograph<br />
has stirred up such scientific<br />
excitement as this Röntgen discovery<br />
in photography,” reported the London<br />
correspondent for The New York<br />
Times. “The papers everywhere are<br />
full of reports of experiments, and of<br />
reproductions of more or less ghastly<br />
anatomical pictures.”<br />
In general, the Times and other<br />
newspapers offered accurate descriptions<br />
of the experiments and the<br />
phenomena that had been observed.<br />
Yet, the papers weren’t scholarly<br />
journals and couldn’t distinguish<br />
well-conceived theory from rampant<br />
assumption. They speculated about<br />
what Röntgen meant when he mentioned<br />
“longitudinal waves in the<br />
ether” and listened to everyone who<br />
claimed credit for the discovery. “A<br />
French savant is said to have been<br />
securing similar results for several<br />
years by the use of an ordinary kerosene<br />
lamp,” offered the Times, which<br />
also claimed that it had found “that<br />
this discovery was not only made by<br />
a Prague professor in 1885” and that<br />
“a full report of the achievement was<br />
made to the Austrian Academy of Sciences<br />
in 1885.”<br />
ORGANIZING IGNORANCE<br />
Surprisingly, the popular press<br />
wasn’t alone in publishing speculation.<br />
The discovery of X-rays<br />
created a massive wave of papers<br />
that crashed on the scholarly community<br />
that winter. More than 125<br />
appeared before the first anniversary<br />
of the discovery. Some were good.<br />
Some were poorly conceived and ill<br />
written. Some identified the major<br />
applications for the waves. Some<br />
wandered into strange and unsupported<br />
speculations.<br />
The articles appeared so quickly<br />
that few could have been reviewed<br />
only by an editor and not an outside<br />
referee. Researchers would read a<br />
description of X-rays in a newspaper,<br />
conduct an experiment, and see their<br />
results published in fewer than six<br />
weeks. Many of these articles were<br />
part of a growing chain of work, in<br />
which one article spawns new experiments,<br />
which in turn spawn new<br />
work. Unfortunately, most of these<br />
researchers were engaged in speculation<br />
that was no better informed<br />
than the newspapers. On 14 February<br />
1896, Columbia physicist Michael<br />
Pupin published a simple framework<br />
for studying these waves, but his<br />
ideas had limited influence in those<br />
first months.<br />
Less than two weeks after Pupin’s<br />
paper appeared, a pair of researchers<br />
built a simple X-ray apparatus and<br />
started applying it to everything that<br />
they could find. A colleague asked<br />
them to “undertake the location of a<br />
bullet in the head of a child that had<br />
been accidentally shot.” They agreed<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
7
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
8<br />
THE KNOWN WORLD<br />
to do it but had enough doubts about<br />
the process to test the safety of their<br />
machine. “Accordingly, Dr. Dudley,<br />
with his characteristic devotion to<br />
the cause of science,” explained the<br />
report, “lent himself to the experiment.”<br />
They taped a coin to one side<br />
of his head, placed a photographic<br />
plate on the other, and exposed him<br />
to the X-ray machine for an hour.<br />
The experiment produced no<br />
useful outcome, but it may have<br />
spared the child. “The plate developed<br />
nothing,” they reported. But<br />
three weeks after the experiment,<br />
Dudley lost all of his hair in the area<br />
where the X-rays had been directed.<br />
“The spot is perfectly bald, being two<br />
inches in diameter,” they noted. “We,<br />
and especially Dr. Dudley, shall watch<br />
with interest the ultimate effect.”<br />
THE ELECTRICAL ENGINEERS<br />
START ORGANIZING<br />
Twelve full months passed before<br />
the scientific community began to<br />
develop a coherent approach to the<br />
study of X-rays. The key article is a<br />
report from the American Institute<br />
of Electrical Engineers (AIEE) that<br />
appeared in December 1896. “We<br />
were very much surprised, something<br />
like a year ago, by this very great discovery,”<br />
the report begins, “but we<br />
cannot say that we know very much<br />
more about it now than we did then.<br />
The whole world seems to have been<br />
working on it for all this time without<br />
having discovered a great deal with<br />
respect to it.”<br />
This report also reveals much<br />
about the nature of scientific practice<br />
at the time. It was a record of a discussion<br />
among a half-dozen senior<br />
scientists, all of whom lived within<br />
easy travel distance to New York and<br />
could easily congregate there for a<br />
meeting. Most important, they represented<br />
most of the major research<br />
universities and, among them, knew<br />
most of the scientists who could<br />
contribute to the field. When they discussed<br />
and debated ideas, they were<br />
speaking for an entire community.<br />
COMPUTER<br />
The report is strong and detailed<br />
but a little cautious as none of the participants<br />
wished to offend the others<br />
or give a conclusion that might be<br />
disproved later. The majority of the<br />
group concluded that X-rays were a<br />
form of electro-magnetic radiation<br />
and that they “most likely consist of<br />
vibrations of such small wavelengths<br />
as to be comparable with the distances<br />
between molecules of the most<br />
dense substances.” That hypothesis<br />
would be the basis for the serious<br />
study of X-rays.<br />
The flood of papers<br />
has continued to rise,<br />
as scientists from<br />
laboratories near and<br />
far try to make a name<br />
for themselves.<br />
THE POWER OF PUBLICATION<br />
Scientific periodicals have always<br />
had a central role in the process that<br />
turns chaos into order, although that<br />
role has often changed. At the time<br />
of Röntgen’s discovery, the editors<br />
of the oldest and most prestigious<br />
scientific journal in the English language,<br />
the Philosophical Transactions,<br />
stated that they selected articles for<br />
publication because of “the importance<br />
and singularity of the subjects,<br />
or the advantageous manner of<br />
treating them.” At the same time,<br />
they rejected the idea that they<br />
were validating or proving the science<br />
of any article that appeared in<br />
the Transactions. They didn’t pretend<br />
“to answer for the certainty of the<br />
facts, or propriety of the reasonings<br />
contained in the several papers so<br />
published,” they explained, “which<br />
must still rest on the credit or judgment<br />
of their respective authors.”<br />
The editors could take such a stand<br />
because the scientific community<br />
was still relatively small. Readers had<br />
other information to help them assess<br />
the articles. Moreover, they actually<br />
knew most of the people and laboratories<br />
engaged in active research and<br />
contributing to the field.<br />
The role of periodicals changed<br />
substantially over the next 50 years.<br />
By the middle of the 20th century,<br />
scientific periodicals were acting as<br />
validators—institutions that verified<br />
scientific research. “Science is<br />
moving rapidly,” noted the editor of<br />
the journal Science. He argued that scientific<br />
periodicals “in every discipline<br />
should take their responsibilities with<br />
respect to critical reviews” of every<br />
paper submitted to them. As an editor<br />
of a leading journal, he felt that Science<br />
needed to set the standard for<br />
scientific publication and regularly<br />
published articles that described<br />
the process of peer review, the rules<br />
that should guide reviewers, and the<br />
kinds of judgments that editors should<br />
make.<br />
At the same time it was promoting<br />
peer review, Science’s editor acknowledged<br />
that the expansion of scientific<br />
research was making it difficult for<br />
editors to validate every article that<br />
reached their desks. “With the great<br />
flood of manuscripts that today’s<br />
editors receive, in every scientific<br />
discipline, it is not possible to spend<br />
so much time and effort debating<br />
details,” he wrote. And as the century<br />
progressed, the flood of manuscripts<br />
only increased.<br />
THE ORIGINAL COLD FUSION<br />
As the waters rose, so rose the calls<br />
for scientific periodicals to test and<br />
validate the papers that they published.<br />
These calls reached a high<br />
point in 1989, when a pair of researchers<br />
announced to the public that they<br />
had made a discovery every bit as dramatic<br />
as the story of X-rays a century<br />
before. Two chemists “started a scientific<br />
uproar last month by asserting<br />
that they had achieved nuclear fusion<br />
at room temperature,” reported The<br />
New York Times. The writer added,<br />
“Many scientists remain skeptical.”<br />
The story of cold fusion lived<br />
for two years as laboratories<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
tried to make sense of the report. As the<br />
narrative unfolded, it quickly turned into a<br />
debate over the process of validating scientific<br />
ideas. Many claimed that the scientists who had<br />
performed the original experiments had taken<br />
their ideas too quickly to the public press. Their<br />
supporters argued that traditional laboratories<br />
were too skeptical of new ideas and that the<br />
scientific journals wouldn’t protect the patent<br />
rights of the discoverers. As the excitement of<br />
the moment faded and the realities of the story<br />
became clear, most commentators concluded<br />
that the public had not been well served. “Some<br />
scholars lunge too hastily for glory,” editorialized<br />
Times science writer Nicholas Wade. He<br />
told scientists to never announce their claims<br />
“until your manuscript has at least been<br />
accepted for publication in a reputable journal.”<br />
Nothing has become easier since the<br />
cold fusion controversy or those<br />
first exciting days of X-rays. Science<br />
has expanded. The number of<br />
subdisciplines has increased. The<br />
flood of papers has continued to rise, as scientists<br />
from laboratories near and far try to<br />
make a name for themselves. In that flood are<br />
ideas good and bad, breathtakingly original<br />
and utterly derivative. They’re the gift of painstaking<br />
research, the theft by 15 minutes of edits<br />
with a word processor, an instantaneous forgery<br />
by a clever bit of code that mocks the way<br />
that scientists write.<br />
By themselves, scientific journals aren’t the<br />
only institutions that attempt to organize the<br />
utter chaos of scientific research. They’re part<br />
of an infrastructure that includes laboratories,<br />
funding agencies, professional societies, review<br />
boards, and other institutions. These organizations<br />
will have to continue to grow and evolve as<br />
editors and publishers grapple with the forces<br />
acting on the scientific community, just as my<br />
young physician friends will have to mature<br />
into wise doctors who know how to draw disciplined<br />
judgment from the anarchy of energetic<br />
speculation.<br />
David Alan Grier is an associate professor of<br />
international science and technology policy at<br />
George Washington University and is the author<br />
of When Computers Were Human (Princeton,<br />
2005) and Too Soon to Tell (Wiley, 2009). Contact<br />
him at grier@computer.org.<br />
_____________<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
UMassAmherst<br />
ISENBERG<br />
SCHOOL OF MANAGEMENT<br />
<br />
_____________________<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
9
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
32 & 16 YEARS AGO<br />
APRIL 1978<br />
INTERNATIONAL DATA (p. 6) “AFIPS has named a panel<br />
of US experts to study foreign countries’ activities which<br />
restrict the international exchange of information. The<br />
panel is also expected to respond to the State Department’s<br />
position paper, Protecting Privacy in International<br />
Data Processing.”<br />
SOFTWARE QUALITY (p. 10) “For computer software<br />
systems, quality appears to be a characteristic that can<br />
be neither built in with assurance at system creation<br />
time nor retrofitted with certainty after a product is<br />
in use. Apart from the issues of logistics (copying and<br />
distributing software) there appears to be a continuing<br />
need to demonstrate some minimum level of quality in<br />
typical wide-use software systems. At the same time<br />
this appears to be impossible to accomplish: the best<br />
designed systems have had errors revealed many years<br />
after introduction, and several programs that had been<br />
publicly ‘proved correct’ contained outright mistakes!”<br />
SOFTWARE REVALIDATION (p. 14) “The problems of revalidating<br />
software following maintenance have received<br />
little attention, yet typically 70 percent of the effort<br />
expended on software occurs as program maintenance.<br />
There are two reasons to perform maintenance on a<br />
software system: to correct a problem or to modify the<br />
capabilities of the system. Revalidation must verify the<br />
corrected or new capability, and also verify that no other<br />
capability of the system has been adversely affected<br />
by the modification. Revalidation is facilitated by good<br />
documentation and a system structure in which functions<br />
are localized to well-defined modules.”<br />
ERROR DETECTION (p. 25) “It is well known that one<br />
cannot find all the errors in a program simply by testing<br />
it for a set of input data. Nevertheless, program testing is<br />
the most commonly used technique for error detection<br />
in today’s software industry. Consequently, the problem<br />
of finding a program test method with increased errordetection<br />
capability has received considerable attention<br />
in the field of software research.<br />
“There appear to be two major approaches to this problem.<br />
One is to find better criteria for test-case selection. The<br />
other is to find a way to obtain additional information (i.e.,<br />
information other than that provided by the output of the<br />
program) that can be used to detect errors.”<br />
PROGRAM TESTING (p. 41) “So, there is certainly no need<br />
to apologize for applying ad hoc strategies in program<br />
testing. A programmer who considers his problems well<br />
and skillfully applies appropriate techniques—regardless<br />
of where the techniques arise—will succeed.”<br />
SYMBOLIC<br />
PROGRAM<br />
EXECUTION<br />
(p. 51) “The<br />
notion of<br />
symbolically<br />
executing a program<br />
follows quite<br />
naturally from normal<br />
program execution. First assume<br />
that there is a given programming language (say, Algol-<br />
60) and the normal definition of program execution for<br />
that language. One can extend that definition to provide<br />
a symbolic execution in the same manner as one extends<br />
arithmetic over numbers to symbolic algebraic operations<br />
over symbols and numbers. The definition of the symbolic<br />
execution is such that trivial cases involving no symbols<br />
are equivalent to normal executions, and any information<br />
learned in a symbolic execution applies to the corresponding<br />
normal executions as well.”<br />
COMPONENT PROGRESS (p. 64) “It is clear, looking back,<br />
that progress in component performance, size, cost, and<br />
reliability has been reflected in corresponding improvements<br />
in systems. Looking forward then, an analysis of<br />
coming developments in logic and memory components<br />
appears to be one approach to forecasting future system<br />
characteristics. Prediction at the system level, however,<br />
is complicated by various options in machine organization,<br />
such as parallel processing and pipelining, which<br />
interact with component features to establish the performance<br />
limits of the system.”<br />
HEMISPHERICAL KEYBOARD (p. 99) “A new hemisphericalshaped<br />
typing keyboard, called the Writehander, permits<br />
typing all 128 characters of the ASCII code with<br />
one hand.<br />
“To use the keyboard, the typist places his four fingers<br />
on four press-switches and his thumb on one of eight<br />
press-switches. The four finger-switches operate as the<br />
lower four bits of the 7-bit ASCII code, selecting one of<br />
16 character groups which contain the desired character.<br />
Each group contains eight letters, numerals, or symbols.<br />
The thumb then presses one switch to select the desired<br />
character from the group of eight. The shape and switch<br />
locations have been designed so that the fingers naturally<br />
locate themselves on the switches, according to the<br />
designer, Sid Owen.”<br />
PDFs of the articles and departments of the April issues of<br />
Computer for 1978 and 1994 are available through the IEEE<br />
Computer Society’s website: www.computer.org/computer.<br />
10 COMPUTER<br />
Published by the IEEE Computer Society 0018-9162/10/$26.00 © 2010 IEEE<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
APRIL 1994<br />
ATM (p. 8) “This year is an important one for asynchronous<br />
transfer mode. The technology now has the backing<br />
of vendors.<br />
“Membership of the ATM Forum, a consortium formed<br />
in October 1991 to accelerate the development and implementation<br />
of ATM products and services, has risen to 465<br />
with new faces from the likes of Microsoft and Novell.<br />
According to Fred Sammartino, forum president, 1994<br />
will be the year many companies set up serious trial<br />
implementations with intent to later incorporate the<br />
technology.”<br />
MBONE (p. 30) “Short for Multicast Backbone, MBone is<br />
a virtual network that has been in existence since early<br />
1992. It was named by Steve Casner of the University of<br />
Southern California Information Sciences Institute and<br />
originated from an effort to multicast audio and video<br />
from meetings of the Internet Engineering Task Force.<br />
Today, hundreds of researchers use MBone to develop<br />
protocols and applications for group communication.<br />
Multicast provides one-to-many and many-to-many<br />
network delivery services for applications such as<br />
videoconferencing and audio where several hosts need<br />
to communicate simultaneously.”<br />
MOBILE COMPUTING (p. 38) “Recent advances in technology<br />
have provided portable computers with wireless<br />
interfaces that allow networked communication even<br />
while a user is mobile. Whereas today’s first-generation<br />
notebook computers and personal digital assistants<br />
(PDAs) are self-contained, networked mobile computers<br />
are part of a greater <strong>computing</strong> infrastructure. Mobile<br />
<strong>computing</strong>—the use of a portable computer capable of<br />
wireless networking—will very likely revolutionize the<br />
way we use computers.”<br />
TELEROBOTICS (p. 49) “The significant communication<br />
latency between an earth-based local site and an<br />
on-orbit remote site drove much of the Steler [Supervisory<br />
Telerobotics Laboratory (at the Jet Propulsion<br />
Laboratory)] design. Such a large latency precludes<br />
direct real-time control of the robot in what nonetheless<br />
remains a real-time operation. To meet these<br />
real-time control requirements, our group devised<br />
a control scheme similar to the one used to control<br />
spacecraft.… Instead of transmitting programs to the<br />
remote site, we transmit command blocks (a set of data<br />
parameters) that control the execution of the remote<br />
site software that provides task-level control. This<br />
allows the remote site to handle a variety of control<br />
modes without requiring changes in the remote site<br />
software.”<br />
DIGITAL SOUPS (p. 65) “Last August, Apple Computer<br />
released a much-talked-about new computer called the<br />
Newton MessagePad. It’s the first platform in a series of<br />
Newton products that fall under the term personal digital<br />
assistant (Sharp’s ExpertPad is another). Although Apple<br />
doesn’t describe ‘the Newton’ as a computer, it’s actually<br />
an advanced system that includes handwriting recognition,<br />
full memory management and protection, and<br />
preemptive multitasking. But one feature that the MessagePad<br />
doesn’t have is files. The Newton stores similar<br />
data objects in formats called ‘soups.’ These soups are<br />
available to all applications.”<br />
SOFTWARE STANDARDS (p. 68) “The International<br />
Organization for Standardization is developing a suite<br />
of standards on software process under the rubric of<br />
Spice, an abbreviation for Software Process Improvement<br />
and Capability Determination. Spice was inspired<br />
by numerous efforts on software process around the<br />
world, including the Software Engineering Institute’s<br />
work with the Capability Maturity Model (CMM), Bell<br />
Canada’s Trillium, and ESPRIT’s Bootstrap.”<br />
VIDEOCONFERENCING (p. 96) “For the past two years,<br />
United Technologies Corp. (UTC) has been experimenting<br />
with desktop video communications in its Topdesc (Total<br />
Personal Desktop Communications) program, which has<br />
the goals of completeness and convenience: allowing<br />
separated personnel to communicate as completely and<br />
easily as if they were at the same location, and doing<br />
so whenever and from wherever it is convenient. This<br />
means that parties should be able to see objects and<br />
documents and collaborate easily using computer data.<br />
In addition, the communications unit must be sized and<br />
priced to fit into an office or lab.”<br />
THE SOFTWARE CRISIS (p. 104) “There’s been so much<br />
talk about a ‘software crisis’ over the past decade or two<br />
that you’d think software practitioners were the original<br />
Mr. Bumble, barely able to program their way out of a<br />
simple application problem. But when I look around, I see<br />
a world in which computers and the software that drives<br />
them are dependable and indispensable. They make my<br />
plane reservations, control my banking transactions, and<br />
send people into space. They even wage war—in entirely<br />
new and apparently successful ways.”<br />
Editor: Neville Holmes; neville.holmes@utas.edu.au<br />
_________________<br />
APRIL 2010 11<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
______________________<br />
_______________________<br />
_______________________<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
TECHNOLOGY NEWS<br />
Will HTML 5<br />
Restandardize<br />
the Web?<br />
Steven J. Vaughan-Nichols<br />
The World Wide Web Consortium is developing HTML 5 as a standard<br />
that provides Web users and developers with enhanced functionality<br />
without using the proprietary technologies that have<br />
become popular in recent years.<br />
In theory, the Web is a resource<br />
that is widely and uniformly<br />
usable across platforms. As<br />
such, many of the Web’s<br />
key technologies and architectural<br />
elements are open and<br />
platform-independent.<br />
However, some vendors have<br />
developed their own technologies<br />
that provide more functionality than<br />
Web standards—such as the ability to<br />
build rich Internet applications.<br />
Adobe System’s Flash, Apple’s<br />
QuickTime, and Microsoft’s Silverlight<br />
are examples of such proprietary<br />
formats.<br />
In addition, Google’s Gears and<br />
Oracle’s JavaFX—which the company<br />
acquired along with Sun Microsystems—have<br />
technologies that enable<br />
creation of offline and client-side Web<br />
applications.<br />
Although these approaches provide<br />
additional capabilities, they have<br />
also reduced the Web’s openness and<br />
platform independence, and tend to<br />
lock in users to specific technologies<br />
and vendors.<br />
In response, the World Wide Web<br />
Consortium (W3C) is developing<br />
HTML 5 as a single standard that provides<br />
Web users and developers with<br />
0018-9162/10/$26.00 © 2010 IEEE<br />
enhanced functionality without using<br />
proprietary technologies.<br />
Indeed, pointed out Google<br />
researcher Ian Hickson, one of the<br />
W3C’s HTML 5 editors, “One of our<br />
goals is to move the Web away from<br />
proprietary technologies.”<br />
The as-yet-unapproved standard<br />
takes HTML from simply describing<br />
the basics of a text-based Web to creating<br />
and presenting animations, audio,<br />
mathematical equations, typefaces,<br />
and video, as well as providing offline<br />
functionality. It also enables geolocation,<br />
a rich text-editing model, and<br />
local storage in client-side databases.<br />
The Web isn’t just about reading<br />
the text on the page and clicking<br />
on the links anymore, noted Bruce<br />
Lawson, standards evangelist at<br />
browser developer Opera Software.<br />
Added W3C director Tim Berners-<br />
Lee, “HTML 5 is still a markup language<br />
for webpages, but the really big<br />
shift that’s happening here—and, you<br />
could argue, what’s actually driving<br />
the fancy features—is the shift to the<br />
Web [supporting applications].”<br />
“HTML 5 tries to bring HTML into<br />
the world of application development,”<br />
explained Microsoft senior<br />
principal architect Vlad Vinogradsky.<br />
Published by the IEEE Computer Society<br />
“Microsoft is investing heavily in<br />
the W3C HTML 5 effort, working with<br />
our competitors and the Web community<br />
at large. We want to implement<br />
ratified, thoroughly tested, and stable<br />
standards that can help Web interoperability,”<br />
said Paul Cotton, cochair of<br />
the W3C HTML Working Group and<br />
Microsoft’s group manager for Web<br />
services standards and partners in<br />
the company’s Interoperability Strategy<br />
Team.<br />
At the same time though, Web<br />
companies say their proprietary technologies<br />
are already up and running,<br />
unlike HTML 5.<br />
Adobe vice president of developer<br />
tools Dave Story said, “The HTML 5<br />
timeline states that it will be at least a<br />
decade before the evolving efforts are<br />
finalized, and it remains to be seen<br />
what parts will be implemented consistently<br />
across all browsers.”<br />
In fact, while HTML 5 recently<br />
became a working draft, it’s not<br />
expected to become even a W3C candidate<br />
recommendation until 2012 or<br />
a final W3C standard until 2022.<br />
Nonetheless, some browser<br />
designers, Web authors, and websites—<br />
such as YouTube—are already adopting<br />
HTML 5 elements. For more<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
13
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
14<br />
TECHNOLOGY NEWS<br />
PLAYING WITH HTML 5<br />
Several websites očer a taste of what HTML 5 will bring. Some of the applications work<br />
with only certain browsers.<br />
YouTube’s beta HTML 5 video project (www.youtube.com/html5) works with the standard’s<br />
video tag. Browsers must support the video tag and have a player that uses the<br />
H.264 codec. Otherwise, YouTube will use Flash to play video.<br />
Mozilla Labs’ BeSpin (https://bespin.mozillalabs.com) is an experimental programmer’s<br />
editor that uses a variety of HTML 5 elements.<br />
FreeCiv.net (www.freeciv.net) is an online game by the FreeCiv.net open source project<br />
that supports HTML 5’s Canvas element. HTML 5-compatible browsers display map<br />
changes faster than those that aren’t compatible.<br />
Google Wave (https://wave.google.com/wave), a cross between social networking<br />
and groupware, uses several HTML 5 elements.<br />
Merge Web Design’s HTML 5 Geolocation (http://merged.ca/iphone/html5geolocation)<br />
is, as the name indicates, a demo of HTML 5-based geolocation.<br />
Sticky Notes (http://webkit.org/demos/sticky-notes/index.html) is the WebKit Open<br />
Source Project’s demo of HTML 5’s client-side database storage API. WebKit is an open<br />
source Web browser engine now used by, for example, Apple’s Safari browser.<br />
information, see the “Playing with<br />
HTML 5” sidebar.<br />
BACKGROUNDER<br />
HTML is the predominant markup<br />
language for webpages. It uses tags<br />
to create structured documents via<br />
semantics for text—such as headings,<br />
paragraphs, and lists—as well<br />
as for links and other elements. HTML<br />
also lets authors embed images and<br />
objects in pages and can create interactive<br />
forms.<br />
HTML, which stemmed from the<br />
mid-1980s Standardized General<br />
Markup Language, first appeared as<br />
about a dozen tags in 1991.<br />
The Internet Engineering Task<br />
Force began the first organized effort<br />
to standardize HTML in 1995 with<br />
HTML 2.0.<br />
The IETF’s efforts to maintain<br />
HTML stalled, so the W3C took over<br />
standardization.<br />
In 1996, the W3C released HTML<br />
3.2, which removed the various proprietary<br />
elements introduced over<br />
time by Microsoft and Netscape.<br />
HTML 4.0, still not a final standard,<br />
followed in 1998. The approach<br />
provides mechanisms for style<br />
sheets, scripting, embedded objects,<br />
richer tables, enhanced forms, and<br />
improved accessibility for people<br />
with disabilities.<br />
COMPUTER<br />
However, HTML was still primarily<br />
focused on delivering text, not multimedia<br />
or client-based applications.<br />
Because of this, proprietary technologies<br />
such as Apple’s QuickTime<br />
and Microsoft’s multimedia players,<br />
both first released in 1991; and Adobe<br />
Flash, which debuted in 1996, have<br />
been used for video.<br />
Technologies such as Google<br />
Gears and Oracle’s JavaFX, both<br />
first released in 2007, make creating<br />
Web-based desktop-style applications<br />
easier for developers.<br />
HTML 5<br />
W3C is designing HTML 5 to create<br />
a standard with a feature set that<br />
handles all the jobs that the proprietary<br />
technologies currently perform,<br />
said specification editor Michael<br />
Smith, the consortium’s special-missions-subsection<br />
junior interim floor<br />
manager.<br />
In addition, HTML 5 will support<br />
newer mobile technologies such as<br />
geolocation and location-based services<br />
(LBS), as well as newer open<br />
formats such as scalable vector<br />
graphics. SVG, an open XML-based<br />
file format, produces compact and<br />
high-quality graphics.<br />
Developers would thus be able<br />
to develop rich webpages and Webbased<br />
applications without needing to<br />
master or license multiple proprietary<br />
technologies.<br />
And browsers would be able to do<br />
more without plug-ins.<br />
Canvas. One of HTML 5’s key<br />
new features is Canvas, which lets<br />
developers create and incorporate<br />
graphics, video, and animations, usually<br />
via JavaScript, on webpages.<br />
HTML Canvas 2D Context is an<br />
Apple-originated technology for rendering<br />
2D graphics and animations on<br />
the client rather than on Web servers.<br />
By rendering graphics locally, the<br />
bottlenecks of server and bandwidth<br />
restrictions are avoided. This makes<br />
graphics-heavy pages render faster.<br />
Video tags. HTML 5’s codecneutral<br />
video tags provide a way to<br />
include nonproprietary video formats,<br />
such as Ogg Theora and H.264,<br />
in a page.<br />
The tag and underlying code<br />
tell the browser that the associated<br />
information is to be handled as an<br />
HTML 5-compatible video stream.<br />
They would also let users view<br />
video embedded on a webpage without<br />
a specific video player.<br />
Location-based services. A location<br />
API offers support for mobile<br />
browsers and LBS applications by<br />
enabling interaction with, for example,<br />
GPS technology and data.<br />
Working offline. AppCache lets<br />
online applications store data and<br />
programming code locally so that<br />
Web-based programs can work as<br />
desktop applications, even without<br />
an Internet connection.<br />
HTML 5 has several other features<br />
that address building Web applications<br />
that work offline. These include<br />
support for a client-side SQL database<br />
and for offline application and data<br />
caching.<br />
Web applications thus can have<br />
their code, graphics, and data stored<br />
locally.<br />
Web Workers. The Web Workers<br />
element runs scripts in the background<br />
that can’t be interrupted by<br />
other scripts or user interactions.<br />
This speeds up background tasks.<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
Syntax and semantics. HTML 5<br />
makes some changes to the syntax<br />
and the semantics of the language’s<br />
elements and attributes.<br />
For example, as Figure 1 shows,<br />
HTML can be written in two syntaxes:<br />
HTML and XML.<br />
Using XML will enable more complex<br />
webpages that will run faster on<br />
Web browsers.<br />
XML requires a stricter, more accurate<br />
grammar than HTML and thus<br />
necessitates less work by the local<br />
computer to run quickly and correctly.<br />
However, XML pages require more<br />
work by the developer to achieve the<br />
higher accuracy level.<br />
HTML+RDFa. The W3C recently<br />
began dividing HTML 5 into subsections<br />
for easier development.<br />
For example, HTML+RDFa<br />
(Resource Description Framework in<br />
attributes) provides a way to embed<br />
resource description frames in<br />
webpages.<br />
RDF is a method for conceptually<br />
describing or modeling information<br />
implemented in Web resources.<br />
This would let developers incorporate<br />
machine-readable data into<br />
webpages, which would enable faster<br />
page rendering.<br />
TRIALS AND TRIBULATIONS<br />
Both nailing down details and the<br />
standardization process itself have<br />
been problematic for HTML 5.<br />
For example, the open source<br />
community supports making the<br />
open Ogg Theora format the default<br />
video codec for HTML 5’s video tag.<br />
Adobe, Google, and Microsoft<br />
opposed this, expressing videoquality,<br />
patent-related, and other<br />
concerns.<br />
According to Google’s Hickson,<br />
“There is no suitable codec that all<br />
vendors are willing to implement<br />
and ship.”<br />
The W3C thus decided not to select<br />
one as a default.<br />
What’s really slowing HTML 5<br />
is that the standardization effort<br />
“combines the worst elements of the<br />
Figure 1. HTML 5 lets HTML be written in two syntaxes: HTML and XML. XML’s stricter,<br />
more accurate grammar requires more work by the developer but less work by the<br />
local computer to run quickly and correctly. The browser ćrst parses out the various<br />
terms in HTML and XML and then sends them serially in an e cient and logical manner<br />
for rendering.<br />
IETF process and the W3C process,”<br />
said Adobe principal scientist Larry<br />
Masinter, a member of the W3C’s<br />
HTML Working Group.<br />
“[As is the case with] the IETF [process],<br />
there is the chaos of an open<br />
mailing list, wide-ranging comments,<br />
and free participation but without<br />
the ‘adult supervision’ that the IETF<br />
supplies in the form of the Internet<br />
Engineering Steering Group and area<br />
directors,” he explained.<br />
From the W3C, he added, there’s<br />
too much bureaucracy and the voting<br />
members don’t have enough responsibility<br />
and accountability for the<br />
final results.<br />
Another potential implementation<br />
concern is that some companies are<br />
already extending HTML 5 in ways<br />
that the final standard is unlikely to<br />
support.<br />
HTML 5 will blur the line between<br />
desktop and online applications and<br />
thus create an opportunity for malware<br />
writers, according to Dmitri<br />
Alperovitch, vice president of threat<br />
research with security vendor McAfee.<br />
By letting Web applications run on<br />
local systems, HTML 5 would allow<br />
Web-based malware to do the same.<br />
Timely user acceptance may<br />
be an issue for HTML 5.<br />
Trevor Lohrbeer, CEO<br />
of Lab Escape, a data-visualization-tool<br />
vendor, said<br />
sweeping Internet technologies must<br />
be supported by at least 80 percent<br />
of browsers before being considered<br />
reliable enough for deployment.<br />
He estimated HTML 5 won’t<br />
achieve this level of support until<br />
2013 at the earliest.<br />
However, Jay Baker, director of<br />
architecture at Viewlocity, a supplychain-management<br />
software vendor,<br />
said his company plans to adopt<br />
HTML 5 fairly aggressively.<br />
“Although there is a learning<br />
curve associated with HTML 5,” he<br />
explained, “many of the new features<br />
make today’s common hacks and<br />
workarounds obsolete.”fi<br />
Steven J. Vaughan-Nichols is a freelance<br />
technology writer based in Mills<br />
River, North Carolina. Contact him at<br />
sjvn@vna1.com.<br />
__________<br />
Editor: Lee Garber, Computer;<br />
l.garber@computer.org<br />
_____________<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
15
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
16<br />
NEWS BRIEFS<br />
New Technique Provides<br />
Energy Wirelessly<br />
Amethod for transferring<br />
energy wirelessly promises<br />
to streamline the<br />
device-charging process<br />
as well as provide power<br />
to an array of electronic devices such<br />
as cellular phones and MP3 players.<br />
WiTricity Corp.’s wireless energy<br />
system comes as a flat pad on which<br />
devices sit or as a domed pod that<br />
powers or charges devices placed<br />
nearby. Manufacturers could also<br />
place the WiTricity components into<br />
a computer or other electronic device<br />
that requires charging.<br />
The charging system is powered<br />
via an electrical outlet or battery,<br />
WiTricity Corp.’s energy system can provide power to or charge nearby devices<br />
wirelessly. The charging system turns incoming electric current into a magnetic field,<br />
which then induces current in and a magnetic field around a resonating coil. This<br />
induces a magnetic field in a coil in a nearby device, thereby transferring energy.<br />
Source: WiTricity Corp.<br />
COMPUTER<br />
noted David Schatz, the company’s<br />
director of business development and<br />
marketing.<br />
First, the charger converts incoming<br />
AC power to DC, then the radio<br />
amplifier creates and amplifies<br />
high-frequency signals, said Schatz.<br />
The high-frequency current flowing<br />
through the charger’s power source<br />
excites a tuned resonator coil that<br />
starts oscillating, which creates an<br />
oscillating magnetic field.<br />
The device being powered has a<br />
coil tuned to the same frequency as<br />
the charger. This induces the magnetic<br />
field to flow from the charger<br />
to the other device, thereby trans-<br />
ferring energy.<br />
So far, Schatz noted, the researchers<br />
have transferred electricity<br />
wirelessly over a distance of two<br />
meters. However, he said, the larger<br />
the resonator, the stronger the magnetic<br />
field and the farther the system<br />
could transfer power to devices.<br />
Because WiTricity’s system requires<br />
access to an energy source, it will not<br />
be a go-anywhere technology, Schatz<br />
noted. However, he added, it eventually<br />
may be able to work at outdoor<br />
locations with their own power<br />
sources, such as perhaps bus stops.<br />
Menno Treffers, chair of the<br />
Wireless Power Consortium and<br />
Philips Electronics’ senior director<br />
of standardization, said WiTricity’s<br />
approach appears to have the same<br />
limited-transmission-range issues<br />
as the technology developed by the<br />
consortium, to which WiTricity does<br />
not belong.<br />
When WiTricity demonstrated its<br />
product at January’s Computer Electronics<br />
Show, it powered a 32-inch<br />
TV from about half a meter away.<br />
WiTricity is also working on some<br />
specialized, classified military systems,<br />
according to Schatz.<br />
The company is already selling<br />
its components and systems<br />
directly to vendors and also plans to<br />
license the intellectual property to<br />
manufacturers.<br />
Now, Schatz said, research must<br />
look into how to integrate the technology<br />
within electronics devices.<br />
He predicted computer electronics<br />
companies will soon start working<br />
on incorporating WiTricity technology<br />
into products that will ship in<br />
2011.<br />
Published by the IEEE Computer Society 0018-9162/10/$26.00 © 2010 IEEE<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
Researchers Pioneer Innovative<br />
Antiphishing Approach<br />
Researchers have developed<br />
an innovative approach<br />
to identifying webpages<br />
that phishers use to trick<br />
victims into entering confidential<br />
information such as user<br />
names, passwords, and bank-account<br />
and credit-card numbers.<br />
Scientists at Taiwan’s Academia<br />
Sinica focused their efforts on<br />
recognizing the pages based on<br />
their appearance rather than their<br />
content, as current antiphishing<br />
approaches do.<br />
Phishers typically create webpages<br />
that look like those belonging<br />
to banks, e-commerce operations,<br />
or other businesses on which users<br />
might enter financial or accountaccess<br />
information. When a user<br />
enters such data on a fake page, the<br />
phisher captures the information and<br />
utilizes it to defraud the victim.<br />
Surveys by Gartner Inc., a market<br />
research firm, found that due to<br />
phishing attacks in the US alone, 3.6<br />
million people lost about $3.2 billion<br />
in 2007 and 5 million lost about $1.8<br />
billion in 2008.<br />
Traditional antiphishing approaches<br />
focus on user complaints and content<br />
analysis, explained Dave Cowings,<br />
Symantec Security Response’s senior<br />
manager for operations.<br />
Verified user complaints will<br />
put phishers’ pages on blacklists of<br />
websites.<br />
Some traditional approaches<br />
analyze the content of websites that<br />
appear similar to well-known sites. If<br />
the content on a suspect page is the<br />
same as on a genuine site but the URLs<br />
are different, the software assumes the<br />
suspect page originated with phishers.<br />
However, this approach can miss<br />
small differences between pages and<br />
thereby yield false positive findings.<br />
Also, said Academica Sinica<br />
researcher Kuan-Ta Chen, phishers<br />
commonly attempt to circumvent<br />
traditional approaches by designing<br />
webpages without actual text—such<br />
as by using images of text instead—<br />
thereby making content analysis<br />
useless.<br />
The Academia Sinica system analyzes<br />
the appearance of genuine and<br />
phishers’ versions of pages and looks<br />
for subtle differences.<br />
The system examines the appearance<br />
of websites that are common<br />
phishing targets, focusing on keypoints.<br />
According to Chen, keypoints<br />
are small, easily identifiable parts<br />
of a page, such as edges, corners, or<br />
areas with large color or contrast differences.<br />
Analyzing keypoints can<br />
identify tiny differences and also<br />
eliminates the need to examine entire<br />
pages, saving both time and computational<br />
overhead.<br />
In addition to copying pages<br />
imprecisely, Chen explained, “phishers<br />
[sometimes] add messages to their<br />
pages designed to convince victims<br />
that they must enter private information<br />
immediately and also include<br />
advertisements that, when clicked on,<br />
direct users to yet another malicious<br />
website.”<br />
The Academia Sinica system looks<br />
for such differences.<br />
The researchers have already<br />
examined 2,058 pages on 74 websites<br />
that phishers commonly replicate,<br />
including the top five targets: eBay,<br />
PayPal, Marshall & Ilsley Bank, Charter<br />
One Bank, and Bank of America.<br />
In tests, Chen said, his system has<br />
accurately recognized phishing sites<br />
between 95 and 98 percent of the<br />
time.<br />
The scientists have implemented<br />
their technology in their Phishgig<br />
website (http://mmnet.iis.sinica.edu.<br />
___________<br />
tw/proj/phishgig), from which users<br />
can download a Firefox browser<br />
plugin capable of detecting phishing<br />
pages. Once Phishgig detects a fraudulent<br />
page, it displays a warning that<br />
users can heed or ignore.<br />
The team is developing plugins for<br />
other browsers, including Internet<br />
Explorer and Google Chrome.<br />
Marty Lindner—principal engineer<br />
at CERT, a security research center<br />
at Carnegie Mellon University’s Software<br />
Engineering Institute—said the<br />
approach will probably be effective<br />
only long enough for phishers to<br />
figure out how to circumvent it.<br />
The most important aspect of<br />
phishing security is careful behavior<br />
by potential victims, he explained,<br />
and many users are insufficiently<br />
cautious.<br />
Chen said he realizes that phishers<br />
commonly change their methods,<br />
so his team is monitoring activity<br />
to see if and how they alter their<br />
approaches in response to the new<br />
technique.<br />
Meanwhile, he noted, the technology<br />
works only with copies of<br />
the pages the system has already<br />
examined.<br />
Chen said the researchers are<br />
open to commercialization opportunities.<br />
News Briefs written by Linda Dailey<br />
Paulson, a freelance technology<br />
writer based in Portland, Oregon.<br />
Contact her at ldpaulson@yahoo.com.<br />
Editor: Lee Garber, Computer;<br />
l.garber@computer.org<br />
_____________<br />
______________<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
17
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
18<br />
NEWS BRIEFS<br />
MIT Media Lab researchers have built an<br />
interface project called the Living<br />
Wall. The project would let users touch the<br />
wall to activate lamps, music systems, and<br />
other items in a room.<br />
The Living Wall uses electronically<br />
enabled wallpaper covered with electronically<br />
conductive paints that create not only<br />
decorative patterns but also circuitry that<br />
helps enable device control.<br />
Earlier wall-based interfaces required<br />
energy-hungry projectors to throw images<br />
on the walls for decoration.<br />
The Living Wall project, led by MIT assistant<br />
professor Leah Buechley, takes a<br />
dičerent, inexpensive, and energy-ećcient<br />
approach.<br />
The researchers used a copper-based<br />
conductive paint to draw lines that function<br />
as circuits. This, in essence, applies a large,<br />
exible printed circuit board to a wall.<br />
They then magnetically attached electronic<br />
components—such as accelerometers,<br />
light sensors, touch sensors, temperature<br />
sensors, and Bluetooth wireless-communications<br />
modules for controlling smaller devices<br />
such as computers and cellular phones—to<br />
the wall’s circuit board.<br />
The wireless modules could be used to<br />
control larger appliances in the future,<br />
according to Buechley.<br />
Users press the touch sensors to control<br />
devices. The other sensors monitor envi-<br />
Anew technology promises<br />
to enable fast, wireless<br />
personal-area networks<br />
that could let users download<br />
videos to and access<br />
the Internet via mobile devices at<br />
high speeds.<br />
IEEE has approved standard<br />
802.15.3c-2009, which defines how<br />
to design interoperable WPAN radio<br />
equipment capable of providing ad<br />
hoc connectivity, quality of service,<br />
and reliability.<br />
The technology would offer theo-<br />
COMPUTER<br />
RESEARCHERS BUILD A WALL THAT ACTS LIKE A REMOTE CONTROL<br />
ronmental variables near the wall to make<br />
lighting, temperature, and other adjustments<br />
as necessary.<br />
The system runs at about 20 volts, she<br />
noted, and draws about 2 amps and 40<br />
watts when fully loaded with devices to<br />
retical maximum data rates of 5.8<br />
gigabits per second at distances<br />
up to 10 meters under ideal conditions,<br />
4 to 5 Gbps under typical<br />
conditions, and 1 to 2 Gbps under<br />
conditions degraded by, for example,<br />
obstacles in transmission paths<br />
or interference from other signals,<br />
noted Bob Heile, chair and CEO of<br />
the ZigBee Alliance and also chair<br />
of the IEEE’s 802.15 WPAN Working<br />
Group.<br />
Today’s fastest wireless systems<br />
are generally much slower, he said.<br />
control. By comparison, a laptop consumes<br />
about 50 watts and a microwave, about<br />
1,000 watts.<br />
Buechley said her team is discussing<br />
commercializing the technology with several<br />
companies, which she declined to name.<br />
MIT’s Living Wall project uses wallpaper and paint, both electronically enabled,<br />
that create not only decorative patterns but also electronic circuitry. This lets users<br />
touch the wall and control electronic items in the same room.<br />
Wireless Technology Promises<br />
Ultrafast Personal Area Networks<br />
For example, IEEE 802.11n, Wi-Fi’s<br />
speediest version, offers up to 600<br />
Mbps.<br />
IEEE 802.15.3c-2009 is fast largely<br />
because it works in the unlicensed<br />
57-to-64-GHz frequency range, which<br />
offers large amounts of available<br />
bandwidth.<br />
The standard’s completion is a<br />
key data-communications milestone<br />
because it is the first IEEE 802 series<br />
wireless standard to specify operation<br />
in the 60-GHz spectrum and<br />
offer data rates of at least 1 Gbps,<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
explained Paul Nikolich, IEEE 802<br />
LAN/MAN standards committee<br />
chair and chief strategy officer at YAS<br />
Broadband Ventures.<br />
This technology is fast enough to<br />
provide the consumer-electronics<br />
market with effective options for wirelessly<br />
connecting high-performance<br />
elements of home-entertainment<br />
systems, such as a high-definition TV<br />
and a set-top box, Heile noted.<br />
He said IEEE 802.15.3c-2009 could<br />
also provide connections in other set-<br />
tings, such as body-area networks for<br />
medical applications.<br />
In addition, the standard’s high<br />
data rates and ability to provide<br />
guaranteed time slots for designated<br />
transmissions support applications,<br />
such as high-end video, that require<br />
quality of service.<br />
Like other radio-based technologies,<br />
IEEE 802.15.3c-2009 is<br />
implemented via a chip that includes<br />
a transmitter, receiver, and antenna.<br />
Heile said the system can identify<br />
lost packets and get replacements to<br />
the destination fast enough to preserve<br />
packet order with minimal<br />
delay. Thus, he noted, it can coexist<br />
with interference from other technologies<br />
operating in the 60-GHz band.<br />
If successful, the new technology<br />
could provide an improved way to<br />
play video and other types of multimedia<br />
via wireless technologies,<br />
said Filomena Berardi, Connectivity<br />
Group research analyst with IMS<br />
Research.<br />
IEEE SOFTWARE<br />
offers pioneering ideas,<br />
expert analyses, and<br />
thoughtful insights for<br />
software professionals<br />
who need to keep up<br />
with rapid technology<br />
change. It’s the authority<br />
on translating software<br />
theory into practice.<br />
www.computer.org/<br />
software/SUBSCRIBE<br />
___________________<br />
<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
19
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
20<br />
COMPUTING PRACTICES<br />
Puzzle-Based Learning<br />
for Engineering and<br />
Computer Science<br />
Nickolas Falkner, University of Adelaide<br />
Raja Sooriamurthi, Carnegie Mellon University<br />
Zbigniew Michalewicz, University of Adelaide<br />
To attract, motivate, and retain students and increase their<br />
mathematical awareness and problem-solving skills, universities are<br />
introducing courses or seminars that explore puzzle-based learning.<br />
We introduce and define this learning approach with a sample syllabus<br />
and course material, describe course variations, and highlight early<br />
student feedback.<br />
Arecent article describes a puzzle-based freshman<br />
seminar introduced at the University of<br />
California, Santa Barbara, to motivate and<br />
retain computer engineering students. 1 The<br />
author argues that attracting students to computer<br />
science and engineering programs represents only<br />
one aspect of a broader problem, the shortage of a skilled<br />
information technology workforce, and that recruitment<br />
efforts must be augmented with additional strategies for<br />
retaining and motivating students—strategies that are<br />
missing in curricula recommendations of the IEEE Computer<br />
Society and the ACM.<br />
The problem may be even broader. Today’s marketplace<br />
needs more skilled graduates capable of solving real<br />
problems of innovation in a changing environment. Missing<br />
in the majority of engineering and computer science<br />
curricula is a focus on developing problem-solving skills.<br />
Further, many courses that introduce elements of problemsolving<br />
skills do so at the programs’ third or fourth level,<br />
after students have already faced the majority of their inacademy<br />
intellectual challenges.<br />
While some courses with a design content emphasis<br />
might meet this requirement, most engineering students<br />
never learn how to think about solving problems in general.<br />
Throughout their education, they are constrained<br />
to concentrate on textbook questions at the end of each<br />
COMPUTER<br />
chapter, solved using material discussed in the chapter.<br />
This constrained form of “problem solving” is not sufficient<br />
preparation for addressing real-world problems. On<br />
entering the real world, students find that problems do not<br />
come with instructions or a guidebook. One of our favorite<br />
examples for illustrating this point is a puzzle on breaking<br />
a chocolate bar:<br />
A rectangular chocolate bar consists of m × n small rectangles,<br />
and you wish to break it into its constituent parts. At<br />
each step, you can only pick up one piece and break it along<br />
any of its vertical or horizontal lines. How should you break<br />
the chocolate bar using the minimum number of steps?<br />
If you do not know the answer, which textbook would<br />
you search to discover the solution? The same applies to<br />
solving many real-world problems: Which textbook should<br />
you search to find a solution, if that is the solution strategy<br />
you’ve learned?<br />
Students often have difficulty applying independent<br />
thinking or problem-solving skills regardless of the nature<br />
of a problem. At the same time, educators are interested<br />
in teaching “thinking skills” rather than “teaching information<br />
and content.” The latter approach has dominated<br />
in the past. As Alex Fisher 2 wrote “though many teachers<br />
would claim to teach their students ‘how to think’, most<br />
Published by the IEEE Computer Society 0018-9162/10/$26.00 © 2010 IEEE<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
would say that they do this indirectly or implicitly in the<br />
course of teaching the content which belongs to their special<br />
subject. Increasingly, educators have come to doubt<br />
the effectiveness of teaching ‘thinking skills’ in this way,<br />
because most students simply do not pick up the thinking<br />
skills in question.”<br />
Further, many analysts lament students’ decreasing<br />
mathematical skills. A recent Mathematics Working<br />
Party Final Report, issued by the University of Adelaide, 3<br />
includes statements such as, “There is an urgent need to<br />
raise the profile and importance of mathematics among<br />
young people” and “The declining participation in mathematics<br />
and related subjects is not limited to Australia.”<br />
Our universities, the University of Adelaide and Carnegie<br />
Mellon University, have introduced a new puzzle-based<br />
learning course to address all the issues raised here.<br />
PUZZLEfiBASED LEARNING APPROACH<br />
The puzzle-based learning approach aims to encourage<br />
engineering and computer science students to think about<br />
how they frame and solve problems not encountered at<br />
the end of some textbook chapter. Our goal is to motivate<br />
students while increasing their mathematical awareness<br />
and problem-solving skills by discussing a variety of puzzles<br />
and their solution strategies. The course is based on<br />
the best traditions introduced by Gyorgy Polya and Martin<br />
Gardner over the past 60 years. 4,5<br />
Many teachers have used puzzles for teaching purposes,<br />
and the puzzle-based learning approach has a tradition that<br />
exceeds 60 years. 6 Historians found the first mathematical<br />
puzzles in Sumerian texts from circa 2500 BC. However,<br />
some of the best evidence for the puzzle-based learning<br />
approach can be found in the works of Alcuin, an English<br />
scholar born around 732 AD, whose main work, Problems<br />
to Sharpen the Young, included more than 50 puzzles.<br />
Some 1,200 years later, one of Alcuin’s puzzles—the “river<br />
crossing problem”—is still used in artificial intelligence<br />
textbooks to educate computer science students.<br />
In our course, we concentrate on educational puzzles<br />
that support problem-solving skills and creative thinking.<br />
These educational puzzles satisfy most of the following<br />
criteria.<br />
Independence<br />
The puzzles are not specifically tied to a single problem-solving<br />
domain.<br />
Generality<br />
Educational puzzles should explain some universal mathematical<br />
problem-solving principles. This is key. Most people<br />
agree that problem solving can only be learned by actually<br />
solving problems. This activity, however, must be supported<br />
by instructor-provided strategies. These general strategies<br />
allow for solving yet unknown problems in the future.<br />
Simplicity<br />
Educational puzzles should be easy to state and remember.<br />
This is important because easy-to-remember puzzles<br />
increase the chance students will remember the solution<br />
method, including the universal mathematical problemsolving<br />
principles.<br />
Eureka factor<br />
Educational puzzles should initially frustrate the problem<br />
solver, but hold out the promise of resolution. A puzzle<br />
should be interesting because its result is not immediately<br />
intuitive. Problem solvers often use intuition to start their<br />
quest for the solution, and this approach can lead them<br />
astray. Eventually they reach a “Eureka moment”—Martin<br />
Gardner’s Aha!—when students recognize the correct path<br />
to solving the puzzle. A sense of relief accompanies this<br />
moment, and the frustration felt during the process dissipates,<br />
giving the problem solvers a sense of reward at their<br />
cleverness for solving the puzzle. The Eureka factor also<br />
implies that educational puzzles should have elementary<br />
solutions that are not obvious.<br />
There is a strong connection<br />
between the ability to solve puzzles<br />
and the ability to solve industry and<br />
business problems.<br />
Entertainment factor<br />
Educational puzzles should be entertaining and engaging.<br />
Entertainment is often a side effect of simplicity,<br />
frustration, the Eureka factor, and an interesting setting<br />
such as playing in a casino environment, fighting against<br />
dragons, or dropping eggs from a tower.<br />
THE LURE OF EDUCATION<br />
Educational puzzles can play a major role in attracting<br />
students to computer science and engineering programs,<br />
and can be used in talks to high school students and<br />
during open-day events. Puzzles can also be a factor that<br />
helps retain and motivate students. Above all, they are<br />
responsible for developing critical thinking and problemsolving<br />
skills as well as raising the profile and importance<br />
of mathematics. Further, there is a strong connection<br />
between the ability to solve puzzles and the ability to<br />
solve industry and business problems. Many real-world<br />
problems can be perceived as large-scale puzzles. William<br />
Poundstone, when investigating the purpose of famous<br />
Microsoft/Silicon Valley interview puzzles, 7 wrote,<br />
“At Microsoft, and now at many other companies, it is believed<br />
that there are parallels between the reasoning used to solve<br />
puzzles and the thought processes involved in solving the real<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
21
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
22<br />
COMPUTING PRACTICES<br />
Real world<br />
Abstract/model<br />
world<br />
problems of innovation and a changing marketplace. […] When<br />
technology is changing beneath your feet daily, there is not much<br />
point in hiring for a specific, soon-to-be-obsolete set of skills. You<br />
have to try to hire for general problem-solving capacity, however<br />
difficult that may be. […] Both the solver of a puzzle and a<br />
technical innovator must be able to identify essential elements<br />
in a situation that is initially ill-defined. It is rarely clear what<br />
type of reasoning is required or what the precise limits of the<br />
problem are.”<br />
Puzzle-based versus problem-based versus<br />
project-based learning<br />
The ultimate goal of puzzle-based learning is to lay a<br />
foundation for students to be effective problem solvers in<br />
the real world. At the highest level, problem solving in the<br />
real world calls into play three categories of skills: dealing<br />
with the vagaries of uncertain and changing conditions;<br />
harnessing domain-specific knowledge and methods; and<br />
critical thinking and applying general problem-solving<br />
strategies.<br />
These three skill categories are captured in the three<br />
forms of learning Figure 1 depicts. In this continuum, each<br />
layer of skills builds upon the layers below it. Puzzle-based<br />
learning focuses on domain-independent, transferable<br />
skills. In addition, we aim to foster introspection and<br />
reflection on the personal problem-solving process: What<br />
was I thinking? What is the solution? Why did I not see it?<br />
Both problem-based and project-based learning are well<br />
established methodologies. 8,9 By our description, problembased<br />
learning requires significant domain knowledge.<br />
This is the form of learning typically emphasized in a<br />
domain-specific undergraduate course such as electromagnetism,<br />
data structures, or circuit theory. Project-based<br />
learning, on the other hand, deals with complex situations<br />
in which usually no clearly unique or correct way<br />
of proceeding exists. For example, “How can we increase<br />
the adherence of cystic fibrosis patients to following their<br />
treatment protocol?” Determining the best solution in such<br />
a situation can be difficult.<br />
The pedagogical objectives of project-based learning<br />
include dealing with ambiguity and complexity, integrating<br />
COMPUTER<br />
Working in teams<br />
identifying the question<br />
Acquisition of<br />
domain knowledge<br />
Critical thinking<br />
logical reasoning<br />
Dealing with uncertainty<br />
and changing conditions<br />
Reasoning with<br />
domain-specific methods<br />
Abstract reasoning<br />
domain independent<br />
Figure 1. Problem solving in the real world requires a continuum of<br />
learning and skills in which each layer of skills builds upon the layers<br />
below it.<br />
a variety of approaches, user testing of the proposed<br />
solutions’ value, and working with a team<br />
composed of diverse backgrounds and skills. In<br />
both problem-based and project-based learning,<br />
the problem drives the learning: Students must<br />
assess what they already know, the knowledge<br />
they need to address the problem, and how to<br />
bridge the knowledge and skill gap.<br />
Puzzle-based learning focuses on domainindependent<br />
critical thinking and abstract<br />
reasoning. This leads us to ask, “What is the difference<br />
between a puzzle and a problem?” One<br />
way to characterize the difference measures the<br />
extent to which domain-specific knowledge is needed to<br />
solve it. The general flavor of puzzles asserts that their<br />
solution should require only domain-neutral general reasoning<br />
skills—biologists, musicians, and artists should all<br />
be able to solve the same puzzle. The different styles of<br />
reasoning required for problem-based and puzzle-based<br />
learning could be compared to the difference between a<br />
field investigator and an armchair detective: one emphasizes<br />
pure reasoning more.<br />
Dropping eggs<br />
The well-known egg-drop experiment provides an<br />
example that compares and contrasts problem-based and<br />
puzzle-based learning. The traditional problem-based<br />
learning version of this experiment involves finding a way<br />
to drop an egg from a maximal height without breaking<br />
it. A puzzle-based learning version of this experiment also<br />
involves dropping an egg from a building, but the question<br />
under investigation, although related, is quite different.<br />
In the problem-based learning approach, students conduct<br />
a series of physical experiments to determine how to<br />
maximize the height from which an egg can be dropped<br />
without breaking. There are two broad approaches:<br />
Dampen the impact’s effect (leading to padding-based<br />
solutions) or lessening the impact (leading to delivery<br />
mechanisms such as a parachute). The team-based learning<br />
outcomes of such an experiment determine different<br />
ways to dampen or lessen an impact.<br />
A puzzle-based learning approach to a similar problem<br />
does not involve a physical experiment, but rather<br />
a thought experiment. One approach would be to ask a<br />
question along the lines of the following: Using multiple<br />
eggs, what would be an effective strategy for determining<br />
the highest floor from which I could drop an egg without<br />
breaking it? This question has interesting variations. This<br />
thought experiment has three entities: the number of eggs,<br />
number of drops, and number of floors.<br />
One puzzle-based learning question could be, “Given a<br />
fixed number of eggs and a number of allowed drops, what<br />
is the maximum height of a building whose breaking floor<br />
we can determine? This could be denoted as F e,d .<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
An alternate question could be, “Given a fixed number of<br />
floors—say, 100—and a number of eggs—say, three—what<br />
is the maximum number of drops needed to determine<br />
the breaking floor (D e,f )?” Yet another version might be to<br />
ask how many eggs would be needed to determine the<br />
breaking floor given a fixed number of floors and allowed<br />
number of drops (E f,d ).<br />
Note that all three puzzle-based learning versions of<br />
the problem require only basic math skills and analytical<br />
reasoning. One goal of puzzle-based learning is to foster<br />
the skill of analyzing and understanding problems clearly.<br />
Part of this requires the clarification of any assumptions<br />
needed to solve the problem. For example, for the egg-drop<br />
thought experiment, some reasonable assumptions include<br />
“all eggs behave the same way” and “an egg that survives<br />
a drop is not damaged and may be dropped again.” To<br />
constrain the problem, we would consider assumptions<br />
such as “an egg surviving a drop from floor x would have<br />
survived a drop from any floor less than x.”<br />
Suppose, given a fixed number of eggs, e, and a specified<br />
number of drops, d, we want to determine the maximal<br />
height of a building whose breaking floor we can determine<br />
(F e,d ). Applying the heuristic of “try to solve a similar<br />
but simpler problem,” let us consider the situation where<br />
we have only one egg (e = 1). In this case, we are required<br />
to search sequentially.<br />
If we are allowed 10 drops (d = 10), then we can determine<br />
the breaking floor of a ten-floor building by starting<br />
at floor one and working our way up. Now suppose we had<br />
two eggs (e = 2). What strategy could we follow? Students<br />
who have had some prior programming experience often<br />
give binary search as a possible strategy, although this is<br />
not the best solution.<br />
Students are led through the reasoning process in a<br />
lecture environment and encouraged to contribute and<br />
refine their suggestions, with controlled prompting. By<br />
considering examples and reasoning about what happens<br />
if the first egg does or doesn’t break, students are guided<br />
through the general version of this puzzle, culminating in<br />
the derivation of the general solution.<br />
Puzzle-based learning shares many pedagogical goals<br />
with the emerging paradigm of computational thinking. 10<br />
Puzzle-based learning resonates with the computational<br />
thinking emphasis on abstraction and analytical thinking.<br />
With reference to Figure 1, computational thinking straddles<br />
the problem skill spectrum but places more emphasis<br />
on problem-based and project-based learning. With its<br />
emphasis on domain-independent, rigorous, and transferable<br />
reasoning, we believe that puzzle-based learning<br />
lays a basis for computational thinking in the curriculum.<br />
PUZZLEfiBASED LEARNING COURSES<br />
A few different versions of the puzzle-based learning<br />
course are currently being taught. The course can be<br />
offered as a three-unit full semester elective course, typically<br />
of three contact hours per week, split into lectures<br />
and tutorials; a three-unit full-semester freshman seminar<br />
of three contact hours per week; or a one-unit freshman<br />
seminar and a one-unit core module as part of some other<br />
course.<br />
One important point about puzzle-based learning<br />
courses is that they are not about presenting and discussing<br />
a variety of puzzles, but rather about presenting,<br />
discussing, and understanding problem-solving principles<br />
and some mathematical principles in the context<br />
of puzzles that serve as entertaining illustrations of the<br />
concepts presented. Also, the process of understanding<br />
problem-solving principles leads students through a variety<br />
of topics, exposing them to many important concepts<br />
at early stages of their college education.<br />
The process of understanding<br />
problem-solving principles leads<br />
students through a variety of topics,<br />
exposing them to many important<br />
concepts.<br />
Despite a variety of possible puzzle-based learning<br />
offerings, the course’s structure is very much the same.<br />
The topics listed below correspond to a 12-week semester<br />
regardless of whether each topic is allocated one hour<br />
or three. Although the topics have some dependency, as<br />
we build and develop our model for problem solving, the<br />
later topics’ order can be rearranged. The topic structure<br />
also supports a high-level first pass and a secondary,<br />
detailed pass model for younger students or for development<br />
over a multiyear curriculum. Similar topic structures<br />
are employed across both secondary and tertiary student<br />
environments, as well as our presentations of puzzle-based<br />
learning concepts to industry, as the following list shows:<br />
1. Introduction. What it is it all about?<br />
2. The problem. Rule #1: Understand the problem.<br />
3. Intuition. Rule #2: Be cautious of your intuitions—<br />
guess, but verify.<br />
4. Modeling. Rule #3: Reason, model, calculate.<br />
5. Some mathematical principles. Do you know how much<br />
you already know?<br />
6. Constraints. Am I aware of all of the constraints?<br />
7. Optimization. What is the best arrangement, and is it<br />
one that I can actually use?<br />
8. Probability. Counting skills and counterintuitive<br />
results.<br />
9. Statistically speaking. What does an apparently convincing<br />
statement actually mean?<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
23
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
24<br />
COMPUTING PRACTICES<br />
10. Let’s simulate. Can we generate the answer?<br />
11. Pattern recognition. What is next?<br />
12. Strategy. Shall we play?<br />
We illustrate each topic with a variety of puzzles presented<br />
interactively. The course introduces a few simple<br />
problem-solving rules that we refer to in every class.<br />
Each week, students receive homework assignments<br />
that cover one or more puzzles addressed in class. The<br />
following week, at the beginning of class, the instructor<br />
presents and discusses solutions. In one instance of the<br />
course, homework contributes 30 percent toward the<br />
final grade, and the final exam contributes the remaining<br />
70 percent. Students can access all lecture slides, audio<br />
Without understanding the problem,<br />
all efforts to find a solution usually<br />
simply waste time: the dictum of<br />
solve the right problem and solve the<br />
problem right.<br />
lecture recordings, and additional material, including<br />
course software. Sample course work might include a<br />
sample lecture that poses the following question: “The<br />
problem: What are you after?” The lecture introduces the<br />
most important problem-solving rule.<br />
First rule of problem solving<br />
Be sure you understand the problem and all the basic<br />
terms and expressions used to define it.<br />
Indeed, without understanding the problem, all<br />
efforts to find a solution usually simply waste time: the<br />
dictum of solve the right problem and solve the problem<br />
right. Underspecificationfican be used as a tool that<br />
encourages students to determine what they know,<br />
what they don’t know and must find out, and what they<br />
cannot find out.<br />
The approach places the emphasis for knowledge discovery<br />
on the students and forces them to accept that,<br />
on occasion, they must provide their best guess. The first<br />
puzzle we use to illustrate this simple observation is one<br />
of Martin Gardner’s favorites.<br />
Puzzle 1<br />
A farmer has the following: 20 pigs, 40 cows, and 60<br />
horses. How many horses does he have, if he calls the<br />
cows horses?<br />
It takes students a short time to understand the problem,<br />
“calling,” which has little to do with “having.” The<br />
farmer still has 60 horses.<br />
This example can be followed by another classic.<br />
COMPUTER<br />
Puzzle 2<br />
You drive a car at a constant speed of 40 kph from A to<br />
B, and on arrival at B, you return immediately to A but at<br />
a higher speed of 60 kph. What was your average speed<br />
for the whole trip?<br />
Again, many students would jump immediately into<br />
the obvious answer of 50 kph without much understanding<br />
of what the average speed is—or rather, how<br />
average speed is defined. Most students are surprised to<br />
discover the correct answer of 48 kph. The next time, in<br />
any course they take in their programs, they will think<br />
twice before they answer a question on some average.<br />
We seek to foster this clear and thoughtful analysis to<br />
hone and guide intuition.<br />
Homework<br />
Clearly, there are strong connections between the process<br />
of understanding the problem and critical thinking. A lecture<br />
might include a slide with a statement containing loose terminology,<br />
strawman arguments, and logical fallacies, and<br />
students are asked to discuss it. We seek to encourage a focus<br />
on critical thinking toward finding a solution.<br />
One weekly assignment given to the students at the end<br />
of this lecture proceeded as follows.<br />
With a 7-minute hourglass and an 11-minute hourglass,<br />
find the simplest way to time the boiling of an egg for 15<br />
minutes.<br />
Note that we are not after any solution, but the simplest<br />
solution. One week later, after all homework has been<br />
handed in, the lecturer has interesting material for discussion,<br />
as some students found the solution A:<br />
Start with the 7- and 11-minute hourglasses, when the<br />
egg is dropped into the boiling water.<br />
After 7 minutes, invert the 7-minute hourglass.<br />
After 4 additional minutes (when sand in the<br />
11-minute hourglass stops), invert the 7-minute hourglass<br />
again.<br />
When the sand stops in the 7-minute hourglass, 15<br />
minutes will have elapsed.<br />
Whereas other students found solution B:<br />
Start the 7- and 11-minute hourglasses.<br />
After 7 minutes, drop the egg into the boiling water.<br />
After 4 additional minutes (when the sand in an<br />
11-minute hourglass stops), invert the 11-minute<br />
hourglass.<br />
When the sand stops in the 11-minute hourglass<br />
again, 15 minutes will have elapsed from the time<br />
the egg dropped into the water.<br />
Which of these solutions is simpler? Solution A takes<br />
15 minutes to complete and requires two inversions.<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
Solution B requires 22 minutes, but only one inversion.<br />
Most students believed that solution A was simpler, as<br />
it required less time. They were, however, less certain<br />
about that when they were told that the hourglasses<br />
involved were quite heavy, weighing 100 kg each. Such<br />
a puzzle provides excellent material not only for a discussion<br />
on understanding the problem, but also on what<br />
the simplest solution means. This also introduces the<br />
concept of multiobjective optimization, a concept students<br />
are usually exposed to during their third year of<br />
studies.<br />
OTHER EXAMPLES<br />
We can use many different puzzles to illustrate fundamental<br />
concepts of probability, statistics, pattern<br />
recognition, games, constraint processing, and optimization.<br />
Here we present a few examples.<br />
Puzzle 3<br />
A farmer sells 100 kg of mushrooms for $1 per kg. The<br />
mushrooms contain 99 percent moisture. A buyer makes<br />
an offer for these mushrooms at the same price a week<br />
later. However, another week later the mushrooms would<br />
have lost 98 percent of their moisture content. How much<br />
will the farmer lose if he accepts the offer?<br />
This is a good example for resisting immediately intuitive<br />
answers—it might not be obvious that the farmer will<br />
lose $50.<br />
Puzzle 4<br />
A bag contains a single ball, which is known to be either<br />
white or black, with equal probability. A white ball is put in,<br />
the bag shaken, and a ball is then randomly removed. This<br />
ball happens to be white. What is the probability now that<br />
the bag currently contains the white ball? Puzzle 4 thus<br />
introduces basic concepts in probability.<br />
Puzzle 5<br />
There are n dots on the flat surface of a plane. Two<br />
players, A and B, move alternatively, with A moving first.<br />
The game’s rules are the same for both players: At each<br />
move, they can connect two points, but they cannot<br />
connect points that were already directly connected to<br />
each other or connect a point with itself. They build a<br />
graph with predefined n vertices by connecting some of<br />
the dots.<br />
The winner is the one who connects the graph (a graph<br />
is connected if there is a path between any two nodes of<br />
the graph; however, not every two nodes must be connected<br />
directly). Which player, A or B, has a winning<br />
strategy?<br />
This puzzle introduces graphs and investigating the<br />
concept of strategies—discovering the winning strategies<br />
of the first or second player is not trivial.<br />
More puzzles<br />
We collected and organized a few hundred educational<br />
puzzles into meaningful subsets. All teaching materials<br />
and the new textbook (Puzzle-Based Learning: Introduction<br />
to Critical Thinking, Mathematics, and Problem Solving) are<br />
now in active use—the text follows the structure of the<br />
course given earlier. Chapter 13 of the text includes a collection<br />
of problems without a solution. These can be used<br />
for homework, assignments, and exams.<br />
There are many ways to evaluate students’ progress in<br />
the puzzle-based learning course. These vary from evaluations<br />
based on participation through evaluations based<br />
From this point, students could still<br />
discuss different interpretations of<br />
the result, encouraging thought.<br />
on homework to final exams. Many students might be<br />
a bit nervous on encountering a final exam loaded with<br />
puzzles. However, the exam can be organized in many<br />
ways that will make it meaningful. For example, last<br />
semester the final exam questions included the following<br />
two examples.<br />
Question 1<br />
Five minutes after midnight of April 13th, 2004, a heavy<br />
rain fell in Melbourne. What is the probability that, 72 hours<br />
later, it would be sunny there? Justify your answer.<br />
This question checked students’ skills for understanding<br />
the problem before providing an answer. (For the curious,<br />
the probability is zero percent.)<br />
Question 2<br />
The hour and minute indicators of my watch cover each<br />
other every 65 minutes. Is my watch running too quickly or<br />
too slowly? Justify your answer.<br />
This question tested students’ modeling skills and<br />
rewarded them for identifying the implicit question “When<br />
should the hands of a watch cover each other,” and for<br />
modeling the problem, even if they reached an incorrect<br />
conclusion.<br />
Wide range<br />
As a glimpse into the range of approaches to a<br />
problem consider the following: In class we examined<br />
different reasoning styles—quantitative versus qualitative<br />
versus intuitive versus wild guess. Both quantitative<br />
and qualitative methods are rigorous, using numbers<br />
and algebra while the other uses language and logic.<br />
One student group went through the precise calculations<br />
to determine when an overlap should occur on<br />
a correct watch, while another group qualitatively<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
25
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
26<br />
COMPUTING PRACTICES<br />
reasoned that if a clock were correctly running, then at<br />
60 minutes past noon, the minute hand would be over<br />
the 12 and the hour hand over the 1. Five minutes later,<br />
the minute hand would be over the 1 and the hour hand<br />
would have moved a little forward. From this point,<br />
students could still discuss different interpretations of<br />
the result, encouraging thought.<br />
For more information on the nature of puzzles and<br />
the approaches used in puzzle-based learning, we direct<br />
readers to the website associated with the text, ____<br />
www.<br />
PuzzleBasedLearning.edu.au.<br />
___________________<br />
UNIVERSITY OF ADELAIDE<br />
We now explore two of this course’s implementations:<br />
the primary development site at the University of Adelaide<br />
and another at Carnegie Mellon University, Pittsburgh. The<br />
initial implementation of puzzle-based learning offered<br />
Students are interested in the<br />
material, but their interest can<br />
easily be capped when they feel<br />
constrained by the assessment<br />
mechanisms.<br />
a one-unit course set as a component of a thee-unit firstyear<br />
course, Introduction to Electronic Engineering. After<br />
gaining support from the Dean of the Faculty of Engineering,<br />
Computer and Mathematical Sciences, from 2009, the<br />
university placed this one-unit offering into introductory<br />
courses across the engineering programs available within<br />
the university.<br />
A three-unit, first-year course for students planning<br />
to major in computer science launched simultaneously<br />
in 2009, and was made available to all nonengineering<br />
students at the university. We refer to the one-unit offering<br />
as PBL-E (PBL for Engineers), and the three-unit offering<br />
as PBL Main. The courses cover the same material, but at<br />
different levels of depth.<br />
The intake for the two courses is quite different, as<br />
PBL-E students have a higher Tertiary Entrance Rank on<br />
average and have also taken two mathematics courses<br />
from secondary school. The students in PBL Main might<br />
have a single course of mathematics if enrolled in the<br />
Bachelor of Computer Science program, or might have no<br />
mathematics beyond the middle of Secondary School, if<br />
from other programs.<br />
In 2008, 325 students undertook the first offering<br />
of one-unit PBL, with a weekly one-hour lecture,<br />
supported with online forums and assessed through<br />
weekly assignments and a final, hour-long examination.<br />
In 2009, 428 students undertook the one-unit PBL<br />
COMPUTER<br />
course, with another 102 students undertaking the<br />
three-unit PBL Main course. The PBL-E course remained<br />
essentially the same in structure, but the three-unit<br />
course added an additional lecture per week, along<br />
with weekly tutorials. This let instructors explore the<br />
material’s development in further depth. The majority<br />
of PBL Main homework consisted of two questions to<br />
be completed during the week, rather than the single<br />
question posed by PBL-E.<br />
Patterns of learning<br />
Lectures in PBL follow a set pattern. Each week, the<br />
first lecture presents the solution to the previous homework,<br />
identifies key points for that week’s lectures, then<br />
builds on the topic area. The lecture concludes with the<br />
next assignment. Lectures are recorded and the lecture<br />
slides, recordings, and all assignment work made available<br />
on the course’s electronic forum. These forums also<br />
provide message boards for student interaction.<br />
PBL Main has a second lecture that develops the<br />
themes of the week’s topic. Lecture materials are developed<br />
in parallel, with the single PBL-E lecture derived<br />
from a revision and abridgement of the two PBL Main<br />
lectures for that topic to maintain currency between<br />
the two courses.<br />
The university offers tutorials for PBL Main that let students<br />
take part in collaborative problem-solving exercises,<br />
while a tutor provides assistance and guidance. Tutorial<br />
groups can hold up to 25 students, divided into subgroups<br />
of five to eight for problem solving. During these sessions,<br />
we introduce fundamental mathematical concepts useful<br />
in the later course, including counting and the bases of<br />
probability, such as factorials, combinations, and permutations.<br />
This addresses the differences in mathematical<br />
preparation identified in the intake.<br />
While a good grasp of mathematics can be useful for<br />
PBL, it is not essential. Problem specification has been<br />
a key concern, as the larger classes contain students<br />
accustomed to a completely specified problem, and thus<br />
feel uncomfortable when confronted with problems not<br />
completely specified or, in the student’s opinion, not sufficiently<br />
and exactly specified. While some students regard<br />
this as a challenge, and also as an intellectual freedom,<br />
others have found it to be a stumbling block.<br />
Assessment of the course has proven to be one of the<br />
largest implementation issues. Students are interested in<br />
the material, but their interest can easily be capped when<br />
they feel constrained by the assessment mechanisms, or<br />
feel they haven’t received sufficient, personalized feedback.<br />
Early assessment for PBL-E revolved around a mark<br />
for each assignment out of five, followed by feedback to<br />
the group that demonstrated the marking scheme and<br />
solution. Instructors also presented the previous lesson’s<br />
solution at the lecture’s start, which corresponded with the<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
hand-in time, to let students immediately gain feedback on<br />
the quality of their solution.<br />
PBL-E’s student numbers posed a significant resource<br />
issue: Without detailed feedback, it takes approximately<br />
two to three minutes to mark each assignment. Thus, the<br />
marking load starts at approximately eight hours for each<br />
assignment, with a team of markers employed and trained<br />
to provide consistency of response.<br />
PBL Main has a much smaller enrollment but employs<br />
detailed, personalized feedback that also takes approximately<br />
eight hours to complete a week’s assignments. The<br />
requirement for a consistent and reproducible marking<br />
scheme that can be assigned to multiple markers constrains<br />
the range of problems that can be offered. Problems<br />
with too many possible solutions become effectively<br />
impossible to mark across 450 students.<br />
In response to this, we have considered many alternatives<br />
and are currently developing problems that might<br />
have multiple possible solutions, all of which may appear<br />
to be correct when, in fact, only one is. Again, this is an<br />
issue of problem and solution specification. Controlled use<br />
of multiple-choice questions, with between eight and ten<br />
options, lets markers quickly identify the flaw in reasoning<br />
and correctly mark the student’s work. We also investigate<br />
the possibility of reducing the dependency on a markbased<br />
assessment for this course.<br />
Early student response shows that they enjoy the course<br />
material and it does develop their thinking skills. However,<br />
several students, especially in PBL-E, encounter issues<br />
with the assessment model and its perceived lack of feedback.<br />
Others worry that the assessment mechanism can<br />
develop a negative and unproductive approach to the<br />
course. We are actively seeking to address these concerns<br />
by allocating more resources to marking and feedback,<br />
and through the use of automated marking mechanisms<br />
that allow more rapid response. Future implementations<br />
of PBL-E may include tutorials or alternative assessment<br />
mechanisms.<br />
CARNEGIE MELLON UNIVERSITY<br />
Carnegie Mellon University offered puzzle-based learning<br />
as a nine-unit, three-credit freshman seminar in spring<br />
2009. Given the spring course’s seminar nature, instructors<br />
capped enrollment at 15, but we found it encouraging to<br />
see that the wait list exceeded the class’s enrollment.fiThe<br />
class had an interdisciplinary mix of students majoring<br />
in Information Systems, Computer Science, Psychology,<br />
Statistics, Cognitive Science, Economics, and Physics. The<br />
class met twice a week for 80 minutes.<br />
In addition to the knowledge gained from the Adelaide<br />
experience, the smaller size of this class let us experiment<br />
with several alternative themes. For example, after the<br />
introductory classes, each session started with a puzzle<br />
of the day.<br />
First, a student would present a puzzle of his or her<br />
choice. The class as a whole tried to solve this puzzle,<br />
with hints and guidance provided by the puzzle poser.<br />
Puzzles chosen by the students ranged the gamut from<br />
logic puzzles to diagrammatic reasoning to physical-puzzle<br />
tangrams. Students submitted a one-page write-up of their<br />
puzzle, solution, and—most importantly—their reflection<br />
on the puzzle: What captured their interest in the puzzle<br />
and its variations, and how did the solution tie in with the<br />
overall course’s instruction?<br />
In addition to the daily puzzle, we also conducted a<br />
puzzlethon that again presented a puzzle of the students’<br />
choice. But this time the class voted on the best puzzle (a<br />
combination of presentation and the puzzle’s nature) and<br />
instructors distributed prizes to the winners.<br />
During our discussion of scientific and mathematical<br />
induction, given the smaller size of the class, we played<br />
Robert Abbott’s inductive game Eleusis, 11 which models the<br />
To emphasize the link between<br />
the thought processes involved in<br />
solving puzzles and addressing open<br />
real-world problems, we examined a<br />
few case studies.<br />
scientific method. To introduce students to some problemsolving<br />
thoughts of leaders in the field, we watched a few<br />
videos. These included Polya’s “Let us teach guessing” in<br />
which he beautifully illustrates several problem-solving<br />
heuristics embraced by puzzle-based learning in the process<br />
of deriving a solution to the five-plane problem; an<br />
interview with Herb Simon on being a researcher with<br />
advice to undergraduates; Richard Feynman’s discussion<br />
of problem solving and induction; and Will Shortz’s documentary<br />
Wordplay on crossword puzzles, their creators,<br />
and solvers.<br />
We also visited the Pittsburgh Super<strong>computing</strong> Center<br />
open house to glimpse problem solving in the real world.<br />
To emphasize the link between the thought processes<br />
involved in solving puzzles and addressing open real-world<br />
problems, we examined a few case studies, including the<br />
recently cracked Netflix Prize (www.netflixprize.com) and<br />
the classic work of Mosteller 12 in resolving the authorship<br />
of some of the disputed Federalist papers.<br />
Student evaluation was done with components for class<br />
participation, puzzle presentations, homework assignments,<br />
three exams, and a few in-class quizzes. It has<br />
been gratifying to see that the response to the class has<br />
been favorable, with some students commenting it was<br />
the best class they had that semester. Some have also commented<br />
on the revisiting of PBL themes in their subsequent<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
27
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
28<br />
COMPUTING PRACTICES<br />
discipline-specific courses. Carnegie Mellon University’s<br />
Doha, Qatar, campus hosted a summer 2009 version of this<br />
course, while the freshman seminar is slated to be offered<br />
in Pittsburgh during spring 2010.<br />
Puzzle-based learning is an in-progress experiment<br />
that seeks to foster general domain-independent<br />
reasoning and critical thinking skills that can lay<br />
a foundation for problem-solving in future course<br />
work. As fun as puzzles inherently are, they provide<br />
only a means to this pedagogical end. Our preliminary<br />
experience in different instantiations of the course and<br />
educational contexts has been encouraging and well<br />
received as we explore this approach. We continue collecting<br />
relevant data to demonstrate the benefit of our<br />
approach. Early results 13 indicate that students who enroll<br />
in our course perceive an improvement in their thinking<br />
and general problem-solving skills.<br />
References<br />
1. B. Parhami, Puzzling Problems in Computer Engineering,<br />
Computer, Mar. 2009, pp. 26-29.<br />
2. A. Fisher, Critical Thinking: An Introduction, Cambridge<br />
University Press, 2001.<br />
3. University of Adelaide, Mathematics Working Party<br />
Final Report, internal document, June 2008.<br />
4. G. Polya, How to Solve It: A New Aspect of Mathematical<br />
Method, Princeton Univ. Press, 1945.<br />
5. M. Gardner, Entertaining Mathematical Puzzles, Dover<br />
Publications, 1961.<br />
6. M. Danesi, The Puzzle Instinct: The Meaning of Puzzles<br />
in Human Life, Indiana Univ. Press, 2002.<br />
7. W. Poundstone, “How Would You Move Mount Fuji?”<br />
Microsoft’s Cult of the Puzzle—How the World’s<br />
Smartest Companies Select the Most Creative Thinkers,<br />
Little Brown and Company, 2000.<br />
8. P.C. Blumenfeld et al., “Motivating Project-Based<br />
Learning: Sustaining the Doing, Supporting the<br />
Learning,” Educational Psychologist, vol. 26, nos. 3<br />
and 4, 1991, pp. 369-398.<br />
9. J.D. Bransford et al., “Teaching Thinking and Problem<br />
Solving: Research Foundations,” Am. Psychologist,<br />
vol. 41, 1986, pp. 1078-1089.<br />
10. J.M. Wing, “Computational Thinking,” Comm. ACM,<br />
Mar. 2006, pp. 33-35.<br />
11. M. Gardner, Penrose Tiles to Trapdoor Ciphers, Mathematical<br />
Assoc. of America, 1997.<br />
12. F. Mosteller and D. Wallace, “Deciding Authorship,”<br />
Mathematics: People, Problems, Results, D.M. Campbell<br />
and J.C. Higgins, eds., Wadsworth Publishing,<br />
1984.<br />
COMPUTER<br />
13. N.J.G. Falkner, R. Sooriamurthi, and Z. Michalewicz,<br />
“Puzzle-Based Learning: The First Experiences,”<br />
Proc. 20th Ann. Conf. Australasian Assoc. for Eng.<br />
Education (AaeE 09), 2009.<br />
Nickolas Falkner is a lecturer in the School of Computer<br />
Science at the University of Adelaide. He received a PhD in<br />
discovery and classification of information in large systems<br />
from the University of Adelaide. His research interests<br />
include wireless sensor networks, automated network configuration,<br />
data fusion, and data stream management.<br />
He is also active in educational research, with a focus on<br />
increasing student participation, retention, and enthusiasm.<br />
Contact him at jnick@cs.adelaide.edu.au.<br />
_________________<br />
Raja Sooriamurthi is an associate teaching professor<br />
with Carnegie Mellon's Information Systems Program and<br />
also has a faculty appointment at Carnegie Mellon's Heinz<br />
College. He received his PhD in computer science from Indiana<br />
University, Bloomington. His research interests are in<br />
artificial intelligence, case-based reasoning, and CS/IS pedagogy.<br />
His pedagogical efforts have been recognized with<br />
several awards for distinguished teaching. Sooriamurthi<br />
is a member of the IEEE Computer Society, the ACM, and<br />
Decision Sciences Institute. Contact him at raja@cmu.edu.<br />
__________<br />
Zbigniew Michalewicz is a professor in the School of<br />
Computer Science, University of Adelaide. He is also at<br />
the Institute of Computer Science, Polish Academy of Sciences<br />
and at the Polish-Japanese Institute of Information<br />
Technology, Poland. He received a PhD in computer science<br />
from the Polish Academy of Science. His research interests<br />
include problem-solving methodologies, evolutionary computation,<br />
modern heuristic methods, and adaptive business<br />
intelligence. Michalewicz is a Fellow of the Australian Computer<br />
Society. Contact him at zbyszek@cs.adelaide.edu.au.<br />
___________________<br />
Selected CS articles and columns are available for free<br />
at http://ComputingNow.computer.org.<br />
For more information<br />
on any topic<br />
presented in Computer,<br />
visit the IEEE<br />
Computer Society<br />
Digital Library at<br />
www.computer.org/csdl<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
PERSPECTIVES<br />
Using Codes of Conduct<br />
to Resolve Legal Disputes<br />
Peter Aiken, Virginia Commonwealth University<br />
Robert M. Stanley and Juanita Billings, Data Blueprint<br />
Luke Anderson, Duane Morris LLC<br />
In the absence of other published standards of care, it is reasonable<br />
for contractual parties to rely on an applicable, widely available code<br />
of conduct to guide expectations.<br />
When legal disputes arise, the primary<br />
focus of judges, juries, and arbitration<br />
panels is on interpreting facts. In<br />
cases of alleged underperformance,<br />
they must evaluate facts against contract<br />
language, which typically states that services will<br />
be provided in accordance with industry standards. Legal<br />
arbiters seek well-articulated “standards of care” against<br />
which to evaluate the behavior of contractual parties and,<br />
in the absence of other published standards, increasingly<br />
rely on codes of conduct (CoCs) to establish an objective<br />
context. In fact, they have successfully applied CoCs—<br />
including the ACM/IEEE-CS CoC—in instances where the<br />
parties were not even affiliated with the CoC-sponsoring<br />
organization.<br />
We illustrate the current application of CoCs with a<br />
fictional enterprise resource planning (ERP) system implementation<br />
failure that is a compilation of real-life cases.<br />
Subject to binding panel arbitration, the plaintiff and defendant<br />
in the case presented conflicting interpretations of the<br />
same facts: From the plaintiff’s perspective, the defendant<br />
0018-9162/10/$26.00 © 2010 IEEE<br />
Published by the IEEE Computer Society<br />
failed to migrate the ERP system as promised; the defendant<br />
countered that defective and poor-quality data delayed<br />
the migration. Using the ACM/IEEE-CS CoC as a reference,<br />
expert testimony convinced the arbitration panel that the<br />
defendant’s position was untenable, and the panel accordingly<br />
awarded the plaintiff a multimillion-dollar judgment.<br />
CASE STUDY<br />
Acme Co. received a directive from its parent corporation<br />
mandating replacement of its legacy pay and<br />
personnel systems with a specific ERP software package<br />
designed to standardize payroll and personnel processing<br />
enterprise-wide. Upon the vendor’s “referred specialist”<br />
recommendation, Acme Co. contracted with ERP Systems<br />
Integrators to implement the new system and convert its<br />
legacy data for $1 million.<br />
The contracted timeline was six months, beginning in<br />
July and wrapping up with a “big bang” conversion at the<br />
end of December. The year-end conversion failed, allegedly<br />
due to ERP Systems Integrators’ poor data migration<br />
practices, and Acme Co. had to run the old and new sys-<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
29
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
30<br />
PERSPECTIVES<br />
ARBITRATION VERSUS CIVIL SUITS<br />
In contrast to civil suits tried in a court of law, arbitration vests the<br />
functions of judge and jury in a panel of arbitrators, typically<br />
lawyers or industry professionals, whose time is paid for by the<br />
involved parties. Arbitration is private and frequently subject to<br />
cončdentiality and nondisclosure agreements—because only the<br />
participants know the details, arbitration inćuences future litigation<br />
at a slower rate than do public court proceedings.<br />
An arbitration panel does not issue an opinion; instead, it hands<br />
down a one-page decision to award damages (or not)—typically<br />
monetary—to one party or the other. The reasoning supporting<br />
any judgment thus must be inferred from the parties’ arguments.<br />
Arbitration decisions are čnal and generally cannot be appealed.<br />
Remaining rules of court are much like those in a trial. A preliminary<br />
phase is dedicated to evidence gathering, motion exchanges,<br />
depositions, and other discovery forms. Lawyers for each party try<br />
to convince the panel of the validity of their client’s position.<br />
tems in parallel—a complex and expensive situation that<br />
it had carefully planned to avoid and that ERP Systems<br />
Integrators had assured them would not occur. When the<br />
conversion was pushed into April of the following year,<br />
Acme Co. slowed and then ceased paying ERP Systems<br />
Integrators’ invoices. In July, ERP Systems Integrators<br />
pulled its implementation team and Acme Co. initiated<br />
arbitration.<br />
Most IT projects are governed by contracts that assign<br />
responsibilities to each party and provide specific remedies<br />
for delayed implementation or project failure. Such<br />
contracts require the parties to submit to private, binding<br />
arbitration to resolve disputes. As the “Arbitration versus<br />
Civil Suits” sidebar indicates, this process slightly differs<br />
from civil litigation in a court of law. However, the use of<br />
CoCs applies equally to both settings.<br />
Almost a year passed before the arbitration hearing.<br />
Meanwhile, Acme Co. and ERP Systems Integrators<br />
deposed witnesses, and experts scrutinized sales materials,<br />
project artifacts (e-mails, status reports, project plans,<br />
and so on), contract documents, application software,<br />
migration tools, and contents of the shared-drive implementation<br />
environment.<br />
THE “STANDARD OF CARE” DILEMMA<br />
The arbitration panel had to resolve three key issues:<br />
Who was responsible for project management? Acme<br />
Co. produced paperwork indicating that responsibility<br />
rested with ERP Systems Integrators. The plaintiff<br />
claimed that it had no idea how to implement such a<br />
system and had hired the defendant to provide such<br />
expertise—including project management.<br />
What standards applied to the programming used for<br />
data conversion? Acme Co. attacked specific conversion<br />
software changes as harmful in that they<br />
COMPUTER<br />
increased the amount of incorrect data within the<br />
converted database by an unnecessarily complicated<br />
order of magnitude. ERP Systems Integrators<br />
responded that the referenced software changes did<br />
not constitute “software engineering” and thus were<br />
not subject to CoC guidance.<br />
How significant were project communication failures?<br />
During discovery, numerous intracompany e-mails<br />
from ERP Systems Integrators described the project<br />
in a markedly more pessimistic tone than the communications<br />
delivered to Acme Co. in compliance with<br />
contract provisions.<br />
These issues collectively fell under the “standard of<br />
care” portion of the contract. The dilemma Acme Co.<br />
faced—one common to companies in the same position—was<br />
detailing the standard of care it expected from<br />
ERP Systems Integrators. The contract language specified<br />
that ERP Systems Integrators “warrants that the services<br />
it provides hereunder will be performed in a professional<br />
and workmanlike manner in accordance with industry<br />
standards.”<br />
As the following exchange shows, ERP Systems Integrators<br />
could not provide more detail regarding the warranty<br />
statement:<br />
Question: What are the industry standards that you are<br />
referring to?<br />
Defense: There is nothing written or codified, but they<br />
are the standards recognized by the consulting firms<br />
in our industry.<br />
Question: I understand that the industry standards that<br />
you are referring to here are not written down anywhere;<br />
is that correct?<br />
Defense: That is my understanding.<br />
Question: Have you made an effort to locate these<br />
industry standards and have simply not been able to<br />
do so?<br />
Defense: I would not know where to begin to look.<br />
For its part, Acme Co. argued that suitable Internetbased<br />
CoCs were available to guide various behaviors.<br />
The “Online Codes of Conduct” sidebar describes one<br />
useful resource, the Online Ethics Center, that aggregates<br />
numerous CoCs. In particular, the plaintiff referenced the<br />
ACM/IEEE-CS Software Engineering Code of Ethics and<br />
Professional Practice. The “SECEPP” sidebar provides a<br />
brief history of this CoC.<br />
Acme Co. successfully argued to the arbitration panel<br />
that, when faced with obscure or publicly available standards,<br />
contracting parties should expect the accessible<br />
standards to apply. The plaintiff then cited objective,<br />
concrete portions of SECEPP that directly supported its<br />
positions on the three disputed issues.<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
PROJECT<br />
MANAGEMENT<br />
RESPONSIBILITY<br />
In pre-arbitration depositions,<br />
ERP Systems Integrators<br />
asserted that it was not the<br />
project manager and that the<br />
contract specified its performance<br />
solely at the direction<br />
of Acme Co. The plaintiff contended<br />
that, while contract<br />
language did exist, overall<br />
project management lay<br />
with the defendant because<br />
it assumed that role in spite<br />
of its denials. In its defense,<br />
Acme Co. cited Section 2.7<br />
of SECEPP, which states that<br />
“<strong>computing</strong> professionals<br />
have a responsibility to share<br />
technical knowledge with<br />
the public by encouraging<br />
understanding of <strong>computing</strong>,<br />
including the impacts of<br />
computer systems and their<br />
limitations.”<br />
The panel members<br />
understood SECEPP to be<br />
analogous to a building<br />
code and that, because of its<br />
broad wording, applied to the<br />
project in general and not<br />
specifically to its software<br />
engineering aspects.<br />
Expert testimony supported<br />
Acme Co.’s claims.<br />
Referencing widely published<br />
and accepted principles 1 that<br />
supplemented SECEPP, the<br />
plaintiff prepared a framework of project management<br />
behaviors as shown in Table 1. Specific evidence included<br />
a timesheet signed weekly by ERP Systems Integrators<br />
charging approximately 2,000 hours against the<br />
job category “Project Manager” and the task “Project<br />
Management.”<br />
It was obvious from the evidence that ERP Systems Integrators<br />
was hired in a specialist capacity and that Acme Co.<br />
had no ability to provide oversight. The arbitration panel<br />
determined that the defendant acted as, and clearly was,<br />
the project manager.<br />
RELEVANT PROGRAMMING STANDARDS<br />
ERP Systems Integrators blamed the conversion failure<br />
on “bad data.” However, Acme Co. provided evidence of<br />
ONLINE CODES OF CONDUCT<br />
The Online Ethics Center for Engineering and Research (http://onlineethics.org) is a joint project of<br />
the Center for Ethics, Engineering, and Society at the National Academy of Engineering and the<br />
Ethics Education Library at the Center for the Study of Ethics in the Professions at the Illinois Institute<br />
of Technology. Funded by a grant from the National Science Foundation, the website brings together<br />
more than 50 CoCs from organizations including:<br />
Institute of Electrical<br />
and Electronics Engineers<br />
(IEEE)<br />
<br />
-<br />
<br />
<br />
<br />
<br />
<br />
-<br />
<br />
<br />
<br />
<br />
Association for<br />
Computing Machinery<br />
(ACM)<br />
<br />
<br />
<br />
<br />
<br />
Institute for Certification<br />
of Computing<br />
Professionals (ICCP)<br />
<br />
<br />
<br />
<br />
While not uničed, the collection exhibits a striking cohesiveness.<br />
SECEPP<br />
Data Management<br />
Association (DAMA)<br />
<br />
-<br />
<br />
<br />
Originally adopted in 1972 by the ACM and the IEEE Computer Society, the Software Engineering<br />
Code of Ethics and Professional Practice principally served as a method of “self-regulation,”<br />
listing violations and accompanying sanctions. In 1993, SECEPP was revised to “clarify and formally<br />
state” the consensus of professional ethical requirements for which “the profession (is) accountable<br />
to the public.” The more comprehensive code was also designed to serve “as an aid to individual<br />
decision making.” 1 In the years since adoption, SECEPP (www.computer.org/computer/code-ofethics.pdf)<br />
has provided the foundation for numerous subsequent guidelines. Knowledgeable<br />
persons are aware of the code’s positive impact on professionalism within the IT industry. 2<br />
______________________<br />
______<br />
References<br />
1. R.E. Anderson et al., “Using the New ACM Code of Ethics in Decision Making,” Comm. ACM, Feb.<br />
1993, pp. 98-107.<br />
2. S. Rogerson, “An Ethical Review of Information Systems Development and the SSADM<br />
Approach,” Centre for Computing and Social Responsibility, De Montfort Univ., UK, 2 Jan.<br />
2008; www.ccsr.cse.dmu.ac.uk/staff/Srog/teaching/ssadm.htm.<br />
flawed programming practices, missing analysis data, and<br />
measurably lower-quality converted data.<br />
Failure to test for other values<br />
The plaintiff alleged that the defendant failed to follow<br />
generally accepted testing standards. Evidence consisted<br />
of instances involving poorly implemented conversion<br />
software.<br />
For example, the conversion software was supposed to<br />
check a specific field value for one of two possible values—<br />
say, “1” and “2” corresponding to the values “male” and<br />
“female,” respectively. The software executed by ERP Systems<br />
Integrators checked to see if the source field value<br />
was “1” and, if so, assigned the value “male” to the converted<br />
field; if the source field value was not “1,” it assigned<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
31
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
32<br />
PERSPECTIVES<br />
Table 1. Summary evidence of project management behaviors.<br />
Process area<br />
the value “female” to the converted field without determining<br />
and reporting possible nonconforming values.<br />
Section 1.2 of SECEPP states that “to minimize the<br />
possibility of indirectly harming others, <strong>computing</strong><br />
professionals must minimize malfunctions by following<br />
generally accepted standards for system design and<br />
testing.” Accepted software engineering programming<br />
standards would call for testing for positive confirmation<br />
of “2” before setting the converted value to “female” and<br />
for reporting incoming values and numbers of values not<br />
“1” or “2.” The defendant’s failure to follow these standards<br />
permits “3” in the source data to be assigned the value<br />
“female” after conversion, resulting in demonstrably lowerquality<br />
converted data.<br />
Failure to prevent duplicate record insertion<br />
Acme Co. demonstrated that ERP Systems Integrators’<br />
software produced other structure-related conversion<br />
errors. 1 The defendant’s e-mail traffic revealed an urgent<br />
need to get records in the system “even if they weren’t<br />
the correct ones.” Instead of attempting to determine<br />
why the conversion programs would not successfully<br />
complete, ERP Systems Integrators identified the lines of<br />
code prohibiting the insertion of duplicate records and<br />
“commented them out,” thereby inactivating the software<br />
functionality.<br />
Consequently, there were 63,131 customers instead<br />
of approximately 6,000 and 100,236 employee records<br />
instead of approximately 10,000 in the system after con-<br />
COMPUTER<br />
Defendant lead<br />
Methodology Demonstrated<br />
Plainti<br />
lead<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
<br />
?<br />
<br />
<br />
<br />
?<br />
<br />
<br />
version. This in turn increased the data clean-up<br />
cost. Due to the inherent complexities of working<br />
in a multiflawed environment, 2 the cost to clean<br />
up 10 times more data is often much greater than<br />
10 times the cost of cleaning up the original data.<br />
Section 6.08 of SECEPP states that software<br />
engineers should “take responsibility for detecting,<br />
correcting and reporting errors in software<br />
and associated documents.” The arbitration panel<br />
agreed with the plaintiff that the code provided<br />
an objective measure to assess responsibility for<br />
minimizing software malfunctions and correcting<br />
errors, and as such could reasonably guide Acme<br />
Co.’s expectations.<br />
COMMUNICATION FAILURE<br />
RESPONSIBILITY<br />
Acme Co. alleged that ERP Systems Integrators<br />
withheld important information from the on-site<br />
consulting team. The plaintiff presented e-mails of<br />
defendant personnel exchanging dire predictions<br />
about the project’s fate. One message warned it<br />
could become “our biggest mess!” These starkly<br />
contrasted with the rosy reports presented by ERP<br />
Systems Integrators during status meetings.<br />
On the subject of a client’s obligation to communicate<br />
project failure indicators, SECEPP is unambiguous: According<br />
to Section 2.06, “any signs of danger from systems<br />
must be reported to those who have opportunity and/<br />
or responsibility to resolve them.” The evidence clearly<br />
showed a pattern by the defendant of communicating one<br />
message internally (project failure) and a second message<br />
to plaintiff (everything okay).<br />
A second communication failure occurred at a more<br />
systematically significant level. All project management<br />
guidelines stress the importance of treating project<br />
planning diagrams as living documents, and most are<br />
managed via specialized software that permits determination<br />
of planned versus actual. Drawing on the Project<br />
Management Body of Knowledge (PMBOK), Acme Co. demonstrated<br />
that by never updating the project plan shown in<br />
Figure 1, developed using a simple spreadsheet, ERP Systems<br />
Integrators was unable to report fact-based measures<br />
of progress and thus failed to meet expected standards.<br />
Project statistic metadata lets stakeholders and implementers<br />
respond to challenges with all parties speaking<br />
the same vocabulary. Static project plans are out of date<br />
as soon as any task deviates from the plan and, as a result,<br />
management cannot determine the status of and impact<br />
on subsequent tasks.<br />
Additional evidence indicating a vastly overbooked<br />
resource pointed to a project that was out of control. Figure<br />
2 indicates a “plan” for one individual to accomplish the<br />
work of 18 others. This kind of error occurs in projects<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
Figure 1.<br />
where the existing environment has not<br />
been understood well enough to properly<br />
plan.<br />
Acme Co. proved that ERP Systems<br />
Integrators had not performed legacy<br />
system analysis 3 and that it failed to<br />
adequately manage project risk. These<br />
activities are subsumed under Section<br />
2.5 of SECEPP: “Give comprehensive<br />
and thorough evaluations of computer<br />
systems and their impacts, including<br />
analysis of possible risks.”<br />
The arbitration panel concluded<br />
that ERP Systems Integrators’ failure<br />
to update project plans, communicate<br />
responsibly, and manage risk appropriately<br />
constituted an inadequate<br />
standard of care. The defendant had<br />
obviously foreseen failure and hid<br />
from the plaintiff information indicating<br />
that the project had no possibility<br />
of succeeding.<br />
RESOLUTION AND DISCUSSION<br />
Days after the arbitration hearing concluded, the panel<br />
issued a one-page decision awarding $5 million to Acme<br />
Co.: five times the project’s worth. The decision was particularly<br />
hard-hitting because ERP Systems Integrators’<br />
insurance carrier denied coverage for the incident based<br />
on the evidence of its “failure to perform in a workmanlike<br />
manner.”<br />
The ruling favorable to the plaintiff indicated overwhelming<br />
support for its CoC-based case. The arguments<br />
Acme Co. presented are deciding factors in a growing<br />
number of real-life judicial disputes. In technology<br />
contexts where key issues revolve around competing<br />
Figure 2.<br />
<br />
interpretations of behaviors, CoCs are influencing various<br />
contracting parties as well as the IT, business, and consulting<br />
communities.<br />
Because arbitration results are private, word-of-mouth<br />
has been the chief means of propagating the success of<br />
comparing litigant behavior against CoCs. Moving from<br />
arbitration into case law, CoCs will be increasingly applied.<br />
In spite of limited current awareness, SECEPP is well on its<br />
way to becoming a de facto standard as it enjoys growing<br />
awareness throughout the legal community and increasing<br />
compliance in the IT profession. 4<br />
More extensive application of publicly available standards—and<br />
growing awareness of them—will positively<br />
impact the IT industry. Five initial benefits accrue to organizations<br />
capitalizing on CoC knowledge:<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
33
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
34<br />
PERSPECTIVES<br />
Increasing use and broader applicability. As awareness<br />
of CoCs grows, so also will their popularity. Moreover,<br />
as the legal community becomes more familiar<br />
with CoC-based arguments, they will be applied<br />
more broadly. CoC expertise could become ubiquitous<br />
and perhaps as branded as the PMP designation<br />
from the Program Management Institute (www.pmi.<br />
org/CareerDevelopment/Pages/Obtaining-Credential.<br />
___ aspx). CoCs are not only easy to use, they are unambiguous<br />
about specific, holistic IT professional<br />
responsibilities—to the project, stakeholders, our<br />
profession, and society.<br />
Public codification of conduct standards by IT professionals.<br />
Evidence is mounting that public CoCs<br />
serve as standards for evaluating the performance<br />
and determining the responsibilities not only of IEEE<br />
members, but IT professionals in general. Organizations<br />
and professionals are using CoCs to determine<br />
specific attributes of compliance and noncompliance.<br />
Preventing and resolving disputes. Guidance to first<br />
prevent and subsequently settle disputes is generally<br />
welcome. CoCs provide objective particulars that litigants<br />
can use in a proactive manner. Following a CoC<br />
is one way to promote a successful project environment<br />
and insulate contracting parties from potential<br />
legal liability. In doing so, it is possible to identify critical<br />
prelitigation and other decision points that allow<br />
parties to better deal with or entirely avoid disputes.<br />
Better understanding of IT project implementation. The<br />
current dispute resolution process favors contractors.<br />
Understanding CoC utility enables organizations to<br />
rethink their relationships with clients. This could<br />
impact how organizations evaluate, select, and interact<br />
with IT professionals.<br />
Organization-wide CoC applicability. SECEPP is guided<br />
by the philosophy that CoCs generally apply to organizations—including<br />
those that do not have members<br />
belonging to the ACM or IEEE Computer Society—as<br />
well as to their leaders. The potential implications for<br />
organizations and leadership are staggering.<br />
Seeking a legal resolution to a dispute over contracted<br />
IT services is a growing trend. This is not surprising given<br />
the alarming statistic that up to 70 percent of IT projects<br />
fail (www.it-cortex.com/stat_failure_rate.htm). Litigation<br />
of software-intensive endeavors has been called a “major<br />
growth industry,” with forecasted legal costs rising “faster<br />
than any other aspect of software development.” 5<br />
As companies increasingly rely on IT systems to drive<br />
their business, failures and delayed implementations can<br />
cause costly ripples throughout their organization. Many<br />
are unwilling to absorb these costs and, consequently,<br />
expect IT professionals and especially their vendor partners<br />
to share responsibility.<br />
COMPUTER<br />
The evidence speaks for itself. Courts, juries,<br />
and arbitration panels are finding that failure<br />
to follow generally accepted public<br />
standards for design and testing of software<br />
are grounds for seeking damages. A<br />
wider understanding of the existence and usefulness of<br />
existing ethical and professional standards will represent<br />
added value to in-house IT managers and enhance the<br />
stature of IT professionals. An organization’s ability to<br />
evaluate conduct and, when appropriate, consider potential<br />
legal matters more knowledgeably is paramount to<br />
imposing accountability on all participants.<br />
Acknowledgments<br />
The authors express gratitude to the anonymous reviewers<br />
for their comments. They also thank the hundreds of<br />
unnamed data management and legal professionals with<br />
whom they have worked and who have contributed to a better<br />
understanding of this field as it is practiced and as it should<br />
be practiced.<br />
References<br />
1. V.Y. Yoon, P. Aiken, and T. Guimaraes, “Managing Organizational<br />
Data Resources: Quality Dimensions,” Information<br />
Resources Management J., July-Sept. 2000, pp. 5-13.<br />
2. P. Aiken and P. Piper, “Estimating Data Reverse Engineering<br />
Projects,” Proc. 5th Ann. Systems Reengineering Workshop,<br />
Naval Surface Warfare Center, 1995, pp. 133-145.<br />
3. P. H. Aiken, “Reverse Engineering of Data,” IBM Systems J.,<br />
Apr. 1998, pp. 246-269.<br />
4. D. Gotterbarn, “How the New Software Engineering Code<br />
of Ethics Affects You,” IEEE Software, Nov./Dec. 1999, pp.<br />
58-64.<br />
5. T. DeMarco and T. Lister, “Both Sides Always Lose: Litigation<br />
of Software-Intensive Contracts,” CrossTalk, Feb. 2000;<br />
www.stsc.hill.af.mil/crossTalk/2000/02/demarco.html.<br />
Peter Aiken is an associate professor of information systems<br />
at Virginia Commonwealth University and founding<br />
director of Data Blueprint, a data management consulting<br />
firm based in Richmond, Virginia. Contact him at _____<br />
peter@<br />
datablueprint.com.<br />
Robert M. Stanley is a senior member of the technical<br />
staff and a project lead specializing in project and quality<br />
management for Data Blueprint. Contact him at _______ bstanley@<br />
datablueprint.com.<br />
Juanita Billings is a senior member of the technical staff<br />
and a project lead specializing in legal support, systems<br />
analysis, and project management for Data Blueprint. Contact<br />
her at jbillings@datablueprint.com.<br />
___________________<br />
Luke Anderson is a law partner specializing in technology<br />
and intellectual property matters with Duane Morris<br />
LLC in Atlanta, Georgia. Contact him at ________<br />
landerson@<br />
duanemorris.com.<br />
Selected CS articles and columns are available for free at<br />
http://ComputingNow.computer.org.<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
COVER FEATURE<br />
Arutyun I. Avetisyan, Institute for System Programming of the Russian Academy of Sciences<br />
Roy Campbell, Indranil Gupta, Michael T. Heath, and Steven Y. Ko, University of Illinois at<br />
Urbana-Champaign<br />
Gregory R. Ganger, Carnegie Mellon University<br />
Michael A. Kozuch and David O’Hallaron, Intel Labs<br />
Marcel Kunze, Karlsruhe Institute of Technology, Germany<br />
Thomas T. Kwan, Yahoo! Labs<br />
Kevin Lai, Martha Lyons, and Dejan S. Milojicic, HP Labs<br />
Hing Yan Lee and Yeng Chai Soh, Infocomm Development Authority of Singapore<br />
Ng Kwang Ming and Jing-Yuan Luke, Malaysian Institute of Microelectronic Systems<br />
Han Namgoong, Electronics and Telecommunications Research Institute, South Korea<br />
Open Cirrus is a cloud <strong>computing</strong> testbed<br />
that, unlike existing alternatives, federates<br />
distributed data centers. It aims to spur<br />
innovation in systems and applications<br />
research and catalyze development of an<br />
open source service stack for the cloud.<br />
There is growing interest in cloud <strong>computing</strong><br />
within the systems and applications research<br />
communities. However, systems researchers<br />
often find it difficult to do credible work<br />
without access to large-scale distributed data<br />
centers. Application researchers could also benefit from<br />
being able to control the deployment and consumption<br />
of hosted services across a distributed cloud <strong>computing</strong><br />
testbed.<br />
0018-9162/10/$26.00 © 2010 IEEE<br />
OPEN CIRRUS:<br />
A GLOBAL CLOUD<br />
COMPUTING<br />
TESTBED<br />
Published by the IEEE Computer Society<br />
Pay-as-you-go utility <strong>computing</strong> services by companies<br />
such as Amazon and new initiatives by Google, IBM,<br />
Microsoft, and the National Science Foundation (NSF)<br />
have begun to provide applications researchers in areas<br />
such as machine learning and scientific <strong>computing</strong> with<br />
access to large-scale cluster resources. However, system<br />
researchers, who are developing the techniques and software<br />
infrastructure to support cloud <strong>computing</strong>, still have<br />
trouble obtaining low-level access to such resources.<br />
Open Cirrus (http://opencirrus.org) aims to address this<br />
problem by providing a single testbed of heterogeneous<br />
distributed data centers for systems, applications, services,<br />
and open source development research. The project is a<br />
joint initiative sponsored by Hewlett-Packard (HP), Intel,<br />
and Yahoo! in collaboration with the NSF, the University<br />
of Illinois at Urbana-Champaign (UIUC), the Karlsruhe Institute<br />
of Technology (KIT), the Infocomm Development<br />
Authority (IDA) of Singapore, the Russian Academy of<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
35
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
36<br />
COVER FEATURE<br />
Open source cloud stack (Zoni, Hadoop, Tashi)<br />
Shared infrastructure (>10*1,000 cores)<br />
Global services (sign-on, monitoring, store, sustainability dashboard, and so on)<br />
COMPUTER<br />
HP<br />
UIUC Intel<br />
CMU<br />
Yahoo!<br />
KIT<br />
RAS<br />
MIMOS<br />
Figure 1. Open Cirrus testbed. Each of the 10 current sites<br />
consists of a cluster with at least 1,000 cores and associated<br />
storage. The testbed očers a cloud stack consisting of<br />
physical and virtual machines and global services such as<br />
sign-on, monitoring, storage, and job submission.<br />
Sciences (RAS), the Electronics and Telecommunications<br />
Research Institute (ETRI) of South Korea, the Malaysian Institute<br />
of Microelectronic Systems (MIMOS), and Carnegie<br />
Mellon University (CMU). Additional members are expected<br />
to join Open Cirrus later this year.<br />
As Figure 1 shows, the current testbed is composed of 10<br />
sites in North America, Europe, and Asia. Each site consists<br />
of a cluster with at least 1,000 cores and associated storage.<br />
Authorized users can access any Open Cirrus site using the<br />
same login credential.<br />
MOTIVATION AND CONTEXT<br />
Open Cirrus has four main goals.<br />
First, the project aims to foster systems-level research<br />
in cloud <strong>computing</strong>. In the current environment, only big<br />
service providers such as Yahoo!, Google, Amazon, and Microsoft<br />
have access to large-scale distributed data centers<br />
to develop and test new systems and services. Most cloud<br />
<strong>computing</strong> researchers must typically rely on simulations<br />
or small clusters. Open Cirrus aims to help democratize<br />
innovation in this area by providing two unique features<br />
essential to systems-level research:<br />
Open Cirrus sites allow access to low-level hardware<br />
and software resources—for example, install OS,<br />
access hardware features, and run daemons.<br />
The testbed comprises heterogeneous sites in different<br />
administrative domains around the world,<br />
enabling researchers to leverage multiple data centers.<br />
Second, Open Cirrus seeks to encourage new cloud<br />
<strong>computing</strong> applications and applications-level research.<br />
Providing a platform for real-world applications and services<br />
is an important part of Open Cirrus. Particularly<br />
exciting are<br />
IDA<br />
ETRI<br />
the potential for developing new application models<br />
and using them to understand the necessary systemslevel<br />
support, and<br />
using the federated nature of Open Cirrus to provide<br />
a platform for new kinds of federated applications<br />
and services that run across multiple data centers.<br />
Third, Open Cirrus offers a collection of experimental<br />
data. Cloud <strong>computing</strong> researchers often lack data<br />
sets with which to conduct high-quality experimental<br />
evaluations. Open Cirrus sites will let researchers<br />
import, store, and share large-scale data sets such as<br />
Web crawls and data-center workload traces. With<br />
such facilities, Open Cirrus could become a “watering<br />
hole” where researchers with similar interests can exchange<br />
data sets and develop standard cloud <strong>computing</strong><br />
benchmarks.<br />
Fourth, Open Cirrus aims to develop open source<br />
stacks and APIs for the cloud. To become widespread,<br />
cloud <strong>computing</strong> requires a nonproprietary and vendor-neutral<br />
software stack. Open Cirrus will serve as<br />
a platform that the open source community can use to<br />
design, implement, and evaluate such codes and interfaces<br />
for all cloud stack levels. Open source is as much<br />
about community as it is about software, and Open<br />
Cirrus seeks to become the foundation offia largerfiopen<br />
cloud community.<br />
The Open Cirrus sites are working together to provide<br />
a single federated testbed, as opposed to each site<br />
building and operating a separate cluster, for three<br />
reasons:<br />
collaborating on a single, larger effort will achieve<br />
greater impact than participants could individually;<br />
testing in the different site environments will improve<br />
the quality of software and services; and<br />
pooling resources will improve efficiency because the<br />
sites will be sharing innovations.<br />
One measure of efficiency is management cost. Figure 2<br />
shows ballpark cost figures gleaned from the current Open<br />
Cirrus sites. While the costs of running a cloud infrastructure<br />
increase with the number of sites, the savings from<br />
sharing software development and operational methods<br />
reduces overall costs. For example, several participating<br />
organizations are prominent developers of the software<br />
components in the Open Cirrus service architecture. By<br />
sharing these new systems and the lessons learned in deploying<br />
them, all of the sites benefit.<br />
ARCHITECTURE, DESIGN,<br />
AND IMPLEMENTATION<br />
Several high-level architectural choices drove the Open<br />
Cirrus design:<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
Systems versus application-only research. In contrast<br />
to clusters such as Google/IBM, Microsoft Windows<br />
Azure, and Amazon EC2/S3, Open Cirrus enables<br />
research using physical machines in addition to virtualized<br />
machines. This requires provisioning of the bare<br />
metal, enabling root access to provisioned servers,<br />
providing isolation at the network level, and reclaiming<br />
access in case of fraudulent or erroneous behavior.<br />
Federated versus unified sites. In contrast to a unified<br />
architecture such as PlanetLab, Open Cirrus federates<br />
numerous sites with various hardware, services, and<br />
tools. The sites exist on different continents, under<br />
different regulations and subject to different privacy<br />
concerns. Commonality is enabled by Open Cirrus<br />
global services under development, such as global<br />
sign-on and monitoring. Some local services may<br />
vary across sites, but common practices and regulations<br />
will promote consistent administration and<br />
oversight.<br />
Data-center focus versus centralized homogeneous<br />
infrastructure. Compared to a centralized approach<br />
such as Emulab, Open Cirrus revolves around multiple<br />
data centers. This data-center focus enables<br />
independent research while sharing resources. It has<br />
implications for security, enforcing authorizations<br />
between users and individual sites, and integration<br />
with existing organizational regulations.<br />
Service architecture design<br />
Design of the Open Cirrus service architecture is guided<br />
by a desire to create a unified and coherent resource,<br />
rather than several completely disjoint clusters.<br />
Direct access to physical resources. Systems research is<br />
supported by allowing direct access to physical resources<br />
on the machine. For example, researchers can have root<br />
passwords, install kernel images, and access processors,<br />
chipsets, and storage. However, some resources, particularly<br />
network resources needed for proper isolation such<br />
as virtual local area network (VLAN) switch configurations,<br />
may be virtualized or unavailable.<br />
Similar operating environments. Given that multiple<br />
organizations with different practices manage the Open<br />
Cirrus sites, it’s infeasible for these sites to have identical<br />
operating environments. However, it’s possible to create<br />
similar operating environments by defining a minimum<br />
set of services that every site must offer.<br />
Support for near-production use. While supporting<br />
cloud <strong>computing</strong> system software research is Open Cirrus’<br />
central mission, robust research often requires access to<br />
real-world use cases. Therefore, Open Cirrus sites strive<br />
to offer high-quality services to researchers who aren’t<br />
necessarily conducting research at the systems level. This<br />
use provides the workloads, traces, and testing needed for<br />
insights into real-world use.<br />
Annual cost per site in $K<br />
$1,800<br />
$1,600<br />
$1,400<br />
$1,200<br />
$1,000<br />
$800<br />
$600<br />
$400<br />
$200<br />
$0<br />
1 5 10 20 50<br />
Number of sites<br />
Global services available from any site. A small set<br />
of global services is available from any Open Cirrus site.<br />
Examples include the global sign-on authentication service,<br />
global monitoring, and a moderate-scale storage service for<br />
configuration files, intermediate results, or binaries.<br />
Service stack architecture<br />
A typical Open Cirrus site consists of foundation, utility,<br />
and primary domain services, as Figure 3 shows.<br />
Zoni. The foundation service for the software architecture<br />
is Zoni. Fundamentally, Zoni is the software<br />
component responsible for managing physical resources<br />
in the cluster and is crucial to providing users with baremetal<br />
server access to conduct software system research.<br />
This component provides five key functions:<br />
allocation of server nodes;<br />
isolation of node groups, called domains;<br />
provisioning of key software in a domain;<br />
out-of-band server management; and<br />
debugging of allocated nodes.<br />
(Shared) Innovation on OC<br />
OC development<br />
Running/managing OC<br />
System administration<br />
Invest./maint. for 1K cores<br />
Figure 2. Open Cirrus management costs: annual cost per<br />
site for dičerent numbers of sites. While the costs of running<br />
a cloud infrastructure increase with the number of sites, the<br />
savings from sharing software development and operational<br />
methods reduces overall costs.<br />
Zoni maintains a database of all available cluster resources.<br />
User requests, which are primarily for some<br />
number of nodes, are satisfied by allocating resources<br />
from that inventory. Users request allocations of physical<br />
nodes for various reasons. One common reason is to conduct<br />
controlled performance measurements; another is<br />
for experimentation with system software that involves<br />
aspects of networking—for example, developing a new<br />
cluster management system may require controlling a<br />
Dynamic Host Configuration Protocol (DHCP) server.<br />
Experiments that belong to this latter group must be iso-<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
37
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
38<br />
COVER FEATURE<br />
lated from other activities in the cluster to maintain both<br />
experimental integrity and cluster stability. Node allocations<br />
isolated from the rest of the cluster in this way are<br />
domains. The current implementation creates domains<br />
by programming the cluster switches to create VLANs.<br />
To bootstrap a domain for remote users, Zoni must<br />
also provide a mechanism for provisioning software onto<br />
at least one of the allocated nodes. This feature is currently<br />
implemented through a process based on Preboot<br />
Execution Environment (PXE) booting. However, even<br />
though the software may be provisioned properly, there<br />
is no guarantee that it will behave as intended or boot at<br />
all. Consequently, Zoni also provides users with out-ofband<br />
debugging and management facilities. Currently, the<br />
key debugging facility is remote console access, and the<br />
management facility consists primarily of remote power<br />
control. Both are provided through the Intelligent Platform<br />
Management Interface (IPMI).<br />
Primary domain services. Naturally, not all cluster<br />
users are interested in managing a Zoni domain; some are<br />
interested in developing higher-level services, and some<br />
are interested in simply using the services offered. To<br />
serve these last two user groups, one domain in each site<br />
is designated the primary domain and provides a stable<br />
set of services for production use.<br />
To support users working with very large data sets, a<br />
cluster storage system, in particular the Hadoop distributed<br />
file system (HDFS), is used to aggregate the storage<br />
of all the nodes in the domain. A key property of HDFS is<br />
that it supports location-aware <strong>computing</strong>—that is, the file<br />
system exports the location of data blocks in such a way<br />
that runtime services can schedule a <strong>computing</strong> task that<br />
processes a block on the node that contains that block.<br />
This capability reduces pressure on the cluster network.<br />
To support a diverse set of user needs, the recommended<br />
primary domain services include a virtual<br />
machine management (VMM) layer, which provides a convenient<br />
mechanism for allocating resources to various<br />
users and services. Hadoop, for example, implements a<br />
map/reduce programming paradigm and offers a popular<br />
runtime system for building cloud services. The Maui<br />
Cluster Scheduler combined with the Torque resource<br />
manager is another popular runtime system that provides<br />
COMPUTER<br />
Foundation services (Zoni) Site utility services Primary domain services<br />
Domain<br />
isolation<br />
(VLAN)<br />
Physical<br />
machine<br />
control<br />
(IPMI)<br />
Networking<br />
(DNS,<br />
DHCP)<br />
Provisioning<br />
(PXE)<br />
Monitoring<br />
(Ganglia)<br />
Power<br />
management<br />
Accounting<br />
and<br />
billing<br />
Attached<br />
storage<br />
(NFS)<br />
Domain<br />
isolation<br />
(DLS)<br />
Resource<br />
telemetry<br />
(RTS)<br />
Application frameworks<br />
(Hadoop, MPI, Maui/Torque)<br />
Virtual machine management<br />
(AWS-compatible systems<br />
such as Tashi and Eucalyptus)<br />
Cluster storage<br />
(HDFS)<br />
Figure 3. Open Cirrus site services. A typical site consists of foundation, utility, and primary domain services.<br />
a job submission service. By providing the two services<br />
through a disjoint set of virtual machines, the primary<br />
domain’s administrator can dynamically adjust the pool<br />
of resources available to each service according to need<br />
simply by adding or removing VMs. Of course, users<br />
whose jobs aren’t accommodated by one of the existing<br />
application framework services may request a private<br />
pool of VMs.<br />
Different sites may select any VMM service as long as<br />
it supports the EC2 interface from Amazon Web Services<br />
(AWS). Good candidates include Tashi and Eucalyptus.<br />
Tashi is an open source cluster management system for<br />
cloud <strong>computing</strong> on massive Internet-scale data sets being<br />
developed as an Apache Incubator project; it is designed<br />
specifically to complement Open Cirrus. While Tashi is<br />
similar to other systems that manage logical clusters of<br />
VMs, it was developed to support research in coscheduling<br />
computation, storage, and power.<br />
Coscheduling of computation and storage using the<br />
location information provided by storage systems such as<br />
Hadoop must overcome additional challenges in a virtualized<br />
environment. In particular, instances of the Hadoop<br />
runtime executing within VMs may be unable to correctly<br />
assess the relative distances to data blocks whose locations<br />
HDFS described with nonvirtualized location information.<br />
Two additional services may overcome this problem: The<br />
Data Location Service (DLS) is a clearinghouse for data<br />
location information independent of a storage mechanism,<br />
and the Resource Telemetry Service (RTS) provides<br />
a means to obtain an abstract distance measure between<br />
two location identifiers. 1<br />
Example. Figure 4 illustrates how Open Cirrus services<br />
fit together. In this example, the cluster is partitioned<br />
into four domains. From left to right, the first domain is<br />
used for low-level systems research, where researchers<br />
install their own OS kernels and run their own experimental<br />
codes and services. The second domain runs<br />
a VMM system that provides users with virtual clusters<br />
of VMs that share physical nodes and storage in<br />
the Zoni domain. Users build their own services and<br />
applications on top of these virtual clusters. The third<br />
domain provides a dedicated storage service that applications<br />
running on the second partition use. The fourth<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
domain offers a sandbox for developing the<br />
next version of the Tashi cluster management<br />
component.<br />
Site utility services. To manage an Open<br />
Cirrus site easily, many additional, less critical<br />
services are required. For example, a monitoring<br />
service such as Ganglia not only enables the site<br />
administrator to monitor the cluster’s health, it<br />
also facilitates collection of cluster operational<br />
data that may inform future research projects.<br />
Some conventional network file system storage<br />
is convenient for storing user scripts, small<br />
data sets, and small output files. Site utilities<br />
also include facilities for tracking resources<br />
consumed by users and managing the cluster’s<br />
power consumption.<br />
Open Cirrus federation<br />
The Open Cirrus testbed provides a unique opportunity<br />
for experimenting with issues involving federation in<br />
cloud <strong>computing</strong>. To support these experiments, developers<br />
are adding a small set of “global” services—common<br />
services that run at participating sites to provide a common<br />
infrastructure.<br />
Global sign-on. While users are granted access to each<br />
site separately, this authentication clearinghouse service<br />
enables users to access all granting sites with the same<br />
credentials.<br />
Global monitoring. By collecting the monitoring output<br />
from each site into a central location, administrators can<br />
quickly assess the health of the entire testbed, users can<br />
determine which sites are busy, and cross-site statistics<br />
can be archived for future research.<br />
User directories. Mounting a user directory in a<br />
common location at each site facilitates the distribution<br />
of small files, such as execution scripts and configuration<br />
files, for conducting experiments.<br />
Global storage. Similarly, some data sets may be made<br />
available across all sites, either through replication or<br />
some other distribution technology, as appropriate.<br />
Scheduling. Ultimately, users may find it convenient to<br />
submit a job without having to specify where the job must<br />
run. A global scheduling component could automatically<br />
dispatch jobs to the optimal cluster according to some<br />
criteria: load balancing, minimizing data movement, minimizing<br />
energy consumption, and so on.<br />
Resource tracking. As jobs are scheduled across multiple<br />
sites, the resources that users consume may need to<br />
be tracked and credits exchanged between sites based on<br />
resource consumption.<br />
RESEARCH USING OPEN CIRRUS<br />
Table 1 summarizes basic characteristics of the current<br />
Open Cirrus sites. More important than physical charac-<br />
Services<br />
Virtual cluster<br />
Systems research Tashi<br />
Zoni service<br />
Applications<br />
Virtual cluster<br />
Storage service Tashi development<br />
Network-isolated<br />
Zoni domains<br />
Physical cluster<br />
Figure 4. Example service hierarchy possible in Open Cirrus, with the<br />
cluster partitioned into four domains.<br />
teristics are the types of collaboration that Open Cirrus<br />
enables.<br />
Approximately 100 research projects at 10 sites use<br />
Open Cirrus at the systems and applications levels.<br />
Systems-level projects include robust adaptive routing<br />
over redundant layer-2 networks, data computation<br />
overlay for aggregation and analyses, and Open Cirrus<br />
and PlanetLab federation (at HP); use of optical switches<br />
to break data-center networking bottlenecks, power-aware<br />
workload scheduling, and optimizing service energy-delay<br />
product (at Intel); and applying RAID techniques to HDFS,<br />
pipelining data between map and reduce stages of Hadoop<br />
jobs to improve user interaction, and deploying log-analysis<br />
techniques to improve performance of Hadoop clusters<br />
(at Yahoo!).<br />
Applications-level projects include computerized<br />
language translation, astrophysics, graph data mining,<br />
and computer design simulation (at CMU); real-time<br />
streaming applications such as gesture recognition<br />
from video and simulation of material that changes its<br />
shape under software control (at Intel); DNA sequencing,<br />
search, and annotation (at ETRI); and continuously<br />
extracting knowledge from webpages, natural-language<br />
processing, large-scale graph algorithms, analysis<br />
of Wikipedia group dynamics, statistical machine<br />
translation, large-scale document analysis, statistical<br />
machine-learning algorithms, and computational sustainability<br />
(at Yahoo!).<br />
In most of these research projects, Open Cirrus offers<br />
the benefits of running experiments at scale; leveraging<br />
commonly shared stack, services, and best practices;<br />
and creating synergies across the layers. Systems-level<br />
research—for example, networking, power, and cooling—leverages<br />
applications to better understand the<br />
cloud load, while applications improve in performance<br />
and scalability using results from the underlying systems<br />
research.<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
39
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
40<br />
COVER FEATURE<br />
Site Cores Servers<br />
OPEN CIRRUS ECONOMIC MODEL<br />
The emergence of each individual site in Open Cirrus<br />
and the expected growth of the federation are driven by<br />
the economy in today’s cloud <strong>computing</strong> environment.<br />
Explicit break-even points for the choice between renting<br />
versus owning a cloud infrastructure implicitly justify<br />
Open Cirrus’ economic rationale.<br />
Single site<br />
Consider a medium-sized organization—for example, a<br />
start-up or a university department—seeking to provide a<br />
Web service to a client population. The service will run in<br />
a cloud, accessing stored data and consuming CPU cycles.<br />
Suppose this service is identical to the UIUC Open Cirrus<br />
site: 128 servers (1,024 cores) and 524 Tbytes. Should the<br />
organization rent the infrastructure from a cloud provider,<br />
such as EC2 (Elastic Compute Cloud) and S3 (Simple Storage<br />
Service) from Amazon Web Services, or should it buy<br />
and maintain a cloud?<br />
At average AWS rates of US$0.12 per Gbyte/month<br />
and $0.10 per CPU-hour, renting the cloud infrastructure<br />
would incur a monthly storage cost of 524 × 1,000<br />
× $0.12, or $62,880; the total monthly cost would be<br />
$62,880 + 1,024 × 24 × 30 × $0.10 = $136,608. In the<br />
case of owning a cloud, amortized monthly costs would<br />
be split among the hardware, power, and network 45<br />
percent, 40 percent, and 15 percent, respectively. 2-4 If the<br />
service lifetime is M months, it would incur a monthly<br />
storage cost, assuming $300 1-Tbyte disks and scaling<br />
for power and networking, of 524 × $300/0.45/M, or<br />
$349,333/M; the total monthly cost, based on actual systems<br />
cost and the salary of one system administrator for<br />
about 100 servers, 3,4 would be $700,000/0.45/M + $7,500,<br />
or $1,555,555/M + $7,500.<br />
COMPUTER<br />
Public<br />
partition<br />
(servers)<br />
Table 1. Characteristics of current Open Cirrus sites.<br />
Memory<br />
size<br />
(Tbytes)<br />
Storage<br />
size<br />
(Tbytes) Spindles<br />
Network data<br />
rate Focus<br />
CMU 1,165 159 50 2.40 892 784 1 Gbps Tashi, distributed file systems,<br />
applications/data sets<br />
ETRI 1,024 256 200 0.50 128 256 1 Gbps Large data sets, cloud infrastructure<br />
HP 1,024 256 178 3.30 632 1,152 10 Gbps internal;<br />
1 Gbps x-rack<br />
Networking, federation<br />
IDA 2,400 300 100 4.80 59+ 600 1 Gbps Applications based on Hadoop, Pig<br />
Intel 1,364 198 198 1.77 610 746 1 Gbps Tashi, Zoni, MPI, Hadoop<br />
KIT 2,656 232 128 10.00 280 192 40 Gbps Applications with high throughput<br />
MIMOS 1,024 167 16 0.50 36 258 1 Gbps Platform, tools, testing, security<br />
UIUC 1,024 128 64 2.00 524 258 1 Gbps Data sets, cloud infrastructure<br />
RAS 1,136 142 600 9.10 36 142 1 Gbps Hadoop, Tashi, Zoni, Pig, MPI<br />
Yahoo! 3,200 480 400 2.40 1,200 1,600 1 Gbps Hadoop, Pig<br />
The break-even point for storage would be $349,000/M<br />
< $62,880, or M > 5.55 months; the overall break-even<br />
point would be $1,555,555/M + $7,500 < $136,608, or<br />
M > 12 months. Thus, if the service runs for more than 12<br />
months, owning the cloud infrastructure is preferable to<br />
renting it. Similarly, it’s better to own storage if you use it<br />
for more than six months.<br />
Clouds are typically underutilized. 2 With X percent<br />
resource utilization, the break-even time becomes<br />
12 × 100/X months. Given the typical hardware lifetime<br />
of 36 months, the break-even resource utilization is<br />
12 × 100/X < 36, or X > 33.3 percent. Even at the<br />
current 20 percent CPU utilization rates observed in industry,<br />
storage utilization greater than 47 percent would<br />
make ownership preferable, as storage and CPU account<br />
evenly for costs.<br />
Federated sites<br />
Federation can help absorb overloads due to spikes—for<br />
example, at conference deadlines—or underprovisioning. 2,4<br />
Figure 5 plots the costs incurred by a single underprovisioned<br />
cloud for three options: offloading only to AWS,<br />
offloading to five federated clouds and AWS, and offloading<br />
to 49 federated clouds and AWS.<br />
A federation of six sites can defer costs up to 250 percent<br />
overload, while with 50 sites the break-even point is roughly<br />
2,500 percent. (This assumes that other sites are utilized<br />
50 percent and not idle; otherwise, the break-even point<br />
would be 500 percent and 5,000 percent, respectively.) The<br />
detailed data and spreadsheet for this calculation are available<br />
at http://opencirrus.org. Note that this is only a starting<br />
step—the calculation can be expanded by accounting for<br />
the economic costs of disasters, such as massive failure,<br />
project cancellation, and start-up time.<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
RELATED WORK<br />
We can broadly divide existing cloud <strong>computing</strong> testbeds<br />
into those that mainly support applications research<br />
and those that can support systems research. Table 2 compares<br />
the most prominent testbeds.<br />
The Google/IBM cluster (www.google.com/intl/en/<br />
press/pressrel/20071008_ibm_univ.html), TeraGrid, 5 and<br />
Microsoft Windows Azure platform (www.microsoft.<br />
com/windowsazure) all focus on supporting <strong>computing</strong><br />
applications research. Thus, these testbeds don’t enable<br />
access to bare-metal hardware or root access to the OS;<br />
instead, services such as MPI and Hadoop are installed<br />
to ease access to the resources. For example, the Google/<br />
IBM cluster is configured with the Hadoop service and<br />
targets data-intensive applications research such as largescale<br />
data analytics. TeraGrid is a multisite infrastructure<br />
mainly used for scientific research, and Microsoft provides<br />
a Windows Azure interface but no access to systems-level<br />
data.<br />
The Open Cloud Testbed (www.opencloudconsortium.<br />
org) focuses on cloud <strong>computing</strong> middleware research and<br />
is currently configured as a smaller-scale testbed with four<br />
32-node sites.<br />
Testbeds such as PlanetLab, 6 Emulab, 7 DETER (cyber-<br />
DEfense Technology Experimental Research), 8 ___________________________<br />
___<br />
and<br />
Amazon EC2 (http://aws.amazon.com) are designed to support<br />
systems research but with diverse goals.<br />
PlanetLab consists of a few hundred machines spread<br />
around the world and is mainly designed to support<br />
Characteristics Open Cirrus<br />
Type of<br />
research<br />
Systems and<br />
services<br />
Approach Federation of<br />
heterogeneous<br />
data centers<br />
Participants CMU, ETRI, HP,<br />
Intel, IDA, KIT,<br />
MIMOS, RAS,<br />
UIUC, Yahoo!<br />
Monthly cost in $K<br />
100,000<br />
10,000<br />
1,000<br />
100<br />
Table 2. Comparison of cloud <strong>computing</strong> testbeds.<br />
Google/<br />
IBM cluster TeraGrid PlanetLab Emulab<br />
Dataintensive<br />
applications<br />
Cluster<br />
supported<br />
by Google<br />
and IBM<br />
Google,<br />
IBM, MIT,<br />
Stanford<br />
Univ.,<br />
Univ. of<br />
Washington<br />
Distribution 10 sites Centralized—one<br />
data center<br />
in Atlanta<br />
Scientific<br />
applications<br />
Multisite<br />
heterogeneous<br />
clusters for<br />
super<strong>computing</strong><br />
Many<br />
universities<br />
and<br />
organizations<br />
11 partners<br />
in US<br />
Existing data center<br />
Open Cirrus 6<br />
Open Cirrus 50<br />
10<br />
100 200 300 400 500 600 700 800 900 1,000<br />
Utilization (percent)<br />
Figure 5. Costs incurred by a single underprovisioned cloud<br />
for three options: oćoading only to Amazon Web Services<br />
(existing data center), oćoading to ve federated clouds<br />
(Open Cirrus 6) and AWS, and oćoading to 49 federated<br />
clouds (Open Cirrus 50) and AWS.<br />
wide-area networking and distributed systems research.<br />
Although it doesn’t provide access to bare-metal hardware,<br />
it does provide root access to the OS through a lightweight<br />
virtualization similar to FreeBSD jails.<br />
Emulab, the original Zoni service, is a single-site testbed<br />
where each user can reserve a certain number of machines<br />
(typically a few tens) and get exclusive access to bare-metal<br />
hardware. Emulab also provides mechanisms to emulate<br />
different network characteristics. Open Cirrus provides<br />
Emulab-like flexibility for systems research with federation<br />
and heterogeneity, which are crucial for cloud <strong>computing</strong>.<br />
Systems and<br />
services<br />
Nodes<br />
hosted by<br />
research<br />
institution<br />
Many<br />
universities<br />
and<br />
organizations<br />
More than<br />
700 nodes<br />
worldwide<br />
Open Cloud<br />
Testbed<br />
Systems Interoperability<br />
across<br />
clouds using<br />
open APIs<br />
Singlesite<br />
cluster<br />
with<br />
exible<br />
control<br />
Univ. of<br />
Utah<br />
More<br />
than 300<br />
machines<br />
Multisite heterogeneous<br />
clusters<br />
Amazon<br />
EC2<br />
Commercial<br />
use<br />
Raw access<br />
to virtual<br />
machines<br />
APRIL 2010<br />
LANL<br />
cluster<br />
Systems<br />
Reuse of<br />
LANL’s<br />
retiring<br />
clusters<br />
Four centers Amazon CMU,<br />
LANL, NSF<br />
480 cores distributed<br />
in<br />
four locations<br />
Several<br />
unified<br />
data<br />
centers<br />
Thousands<br />
of<br />
older but<br />
still useful<br />
nodes at<br />
one site<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
41
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
42<br />
COVER FEATURE<br />
The DETER testbed is an installation of the Emulab<br />
software and is mainly used for security research—for<br />
example, collecting a large-scale worm trace. Consisting<br />
of two heterogeneous sites, DETER may be viewed as a<br />
federated Emulab installation. However, the two sites are<br />
tightly coupled: The controller resides in one site and controls<br />
physical resources in both sites. In Open Cirrus, all<br />
sites are loosely coupled.<br />
Amazon EC2 provides VMs on a pay-as-you-go basis.<br />
Although it allows complete control over the VMs, users<br />
can’t control network resources, reducing its flexibility as<br />
a systems research testbed.<br />
Finally, CMU’s Garth Gibson is leading an effort to recycle<br />
Los Alamos National Laboratory’s retiring clusters<br />
(typically with a few thousand machines) by making them<br />
available for systems research.<br />
Other related cloud <strong>computing</strong> efforts such as Reservoir<br />
(http://sysrun.haifa.il.ibm.com/hrl/reservoir) and<br />
RightScale (www.rightscale.com) aren’t testbeds per se.<br />
Reservoir (Resources and Servers Visualization without<br />
Barriers) is an EU-funded grid <strong>computing</strong> project that enables<br />
massive-scale deployment and management of IT<br />
services across administrative domains. RightScale is a<br />
cloud services management platform.<br />
Open Cirrus offers unique opportunities for<br />
cloud <strong>computing</strong> research that no existing<br />
alternatives offer. It federates heterogeneous<br />
sites, systems and applications research, and<br />
data sets. In addition, it provides an open<br />
source service stack with nonproprietary APIs for cloud<br />
<strong>computing</strong>. And through shared innovation, Open Cirrus<br />
will have a greater impact on research communities<br />
around the globe.<br />
While working on Open Cirrus during the past year,<br />
we realized the value of common stacks and services,<br />
but even more, we came to appreciate the benefits of a<br />
research community working together toward the same<br />
goals. Heterogeneity of the individual sites has contributed<br />
to the diversity of solutions and has strengthened our approaches,<br />
even though it does make global services more<br />
complex to develop, deploy, and maintain.<br />
Future work on Open Cirrus will revolve around<br />
increased use across the sites. In particular, we’re exploring<br />
applications that can be used on multiple sites<br />
to increase their performance, scale, and reliability. Another<br />
area of interest is standards, but we need more<br />
experience in using stacks and services before exploring<br />
standardization.<br />
Acknowledgments<br />
Partial funding for the Open Cirrus UIUC site was provided by<br />
NSF. Funding for the Open Cirrus CMU/PDL site was provided<br />
by Intel, NSF, ARO, and the PDL Consortium. Open Cirrus is<br />
COMPUTER<br />
a trademark of Yahoo! Inc. Several people made significant<br />
contributions to Open Cirrus, including A. Chien, R. Gass,<br />
K. Goswami, C. Hsiung, J. Kistler, M. Ryan, C. Whitney, and<br />
especially J. Wilkes, who was instrumental in formulating<br />
the original Open Cirrus vision as well as the concept of a<br />
management layer like Zoni.<br />
References<br />
1. M.A. Kozuch et al., “Tashi: Location-Aware Cluster Management,”<br />
Proc. 1st Workshop Automated Control for<br />
Datacenters and Clouds (ACDC 09), ACM Press, 2009, pp.<br />
43-48.<br />
2. M. Armbrust et al., “Above the Clouds: A Berkeley View<br />
of Cloud Computing,” tech. report UCB/EECS-2009-28,<br />
EECS Dept., Univ. of California, Berkeley, 2009; www.eecs.<br />
________________________________<br />
berkeley.edu/Pubs/TechRpts/2009/EECS-2009-28.pdf.<br />
3. J. Hamilton, “Internet-Scale Service Efficiency,” keynote<br />
at 2nd Large-Scale Distributed Systems and Middleware<br />
Workshop (LADIS 08), 2008; http://mvdirona.com/jrh/<br />
TalksAndPapers/JamesRH_Ladis2008.pdf.<br />
_________________________<br />
4. A. Greenberg et al., “The Cost of a Cloud: Research Problems<br />
in Data Center Networks,” ACM SIGCOMM Computer<br />
Communication Rev., Jan. 2009, pp. 68-73.<br />
5. C. Catlett et al., “TeraGrid: Analysis of Organization,<br />
System Architecture, and Middleware Enabling New Types<br />
of Applications,” High Performance Computing and Grids in<br />
Action, L. Grandinetti, ed., IOS Press, 2007, pp. 225-249.<br />
6. L. Peterson et al., “A Blueprint for Introducing Disruptive<br />
Technology into the Internet,” ACM SIGCOMM Computer<br />
Communication Rev., Jan. 2003, pp. 59-64.<br />
7. B. White et al., “An Integrated Experimental Environment<br />
for Distributed Systems and Networks,” ACM SIGOPS Operating<br />
Systems Rev., winter 2002, pp. 255-270.<br />
8. T. Benzel et al., “Design, Deployment, and Use of the<br />
DETER Testbed,” Proc. DETER Community Workshop Cyber<br />
Security Experimentation and Test, Usenix Assoc., 2007;<br />
__________________________________<br />
www.isi.edu/deter/docs/200708-usecdw-deter-design-<br />
_______ deploy.pdf.<br />
Arutyun I. Avetisyan is deputy director of the Institute for<br />
System Programming of the Russian Academy of Sciences<br />
(ISP RAS), RAS’s representative in Open Cirrus. Contact<br />
him at __________<br />
arut@ispras.ru.<br />
Roy Campbell is Sohaib and Sara Abbasi Professor in the<br />
Department of Computer Science at the University of Illinois<br />
at Urbana-Champaign (UIUC). Contact him at rhc@<br />
________ illinois.edu.<br />
Indranil Gupta is an associate professor in the Department<br />
of Computer Science at UIUC, where he also heads<br />
the Distributed Protocols Research Group. Contact him at<br />
____________<br />
indy@illinois.edu.<br />
Michael T. Heath is a professor and Fulton Watson Copp<br />
Chair in the Department of Computer Science at UIUC,<br />
where he’s also director of the Computational Science and<br />
Engineering Program. Contact him at ____________<br />
heath@illinois.edu.<br />
Steven Y. Ko is a postdoctoral research associate in the Department<br />
of Computer Science at Princeton University who<br />
worked on Open Cirrus as a PhD student at UIUC. Contact<br />
him at steveko@cs.princeton.edu.<br />
_________________<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
____
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
Gregory R. Ganger is a professor in the Department of<br />
Electrical and Computer Engineering at Carnegie Mellon<br />
University (CMU), where he’s also director of the Parallel<br />
Data Lab. Contact him at ______________<br />
ganger@ece.cmu.edu.<br />
Michael A. Kozuch is a principal researcher for Intel Labs<br />
Pittsburgh working in the area of computer architecture<br />
and system software. Contact him at _____________<br />
michael.a.kozuch@<br />
intel.com.<br />
David O’Hallaron is the director of Intel Labs Pittsburgh<br />
and an associate professor in the Department of Computer<br />
Science and the Department of Electrical and Computer<br />
Engineering at CMU. Contact him at ______________<br />
david.ohallaron@intel.<br />
___ com.<br />
Marcel Kunze heads the Cloud Computing research group<br />
at the Steinbuch Centre for Computing, Karlsruhe Institute<br />
of Technology, Germany, and is a technical lead in Open<br />
Cirrus. Contact him at _______________<br />
marcel.kunze@kit.edu.<br />
Thomas T. Kwan is director of research operations at<br />
Yahoo! Labs, where he manages multiple cloud <strong>computing</strong><br />
research partnerships for Yahoo!. Contact him at ______ tkwan@<br />
yahoo-inc.com.<br />
Kevin Lai is a research scientist in the Social Computing<br />
Lab at HP Labs and has worked on various projects at the<br />
intersection of operating systems and incentive engineering.<br />
Contact him at klai@hp.com.<br />
________<br />
Martha Lyons is a Distinguished Technologist at HP Labs<br />
focused on incubating and delivering innovative capabilities<br />
to HP’s customers. Contact her at _______________<br />
martha.lyons@hp.com.<br />
Dejan S. Milojicic is a scientist and senior researcher manager<br />
in the Strategy and Innovation Office at HP Labs and director of<br />
Open Cirrus. Contact him at _______________<br />
dejan.milojicic@hp.com.<br />
Hing Yan Lee is program director of the National Grid<br />
Office at the Infocomm Development Authority (IDA) of<br />
Singapore. Contact him at _________________<br />
lee_hing_yan@ida.gov.sg.<br />
Yeng Chai Soh is a professor in the School of Electrical and<br />
Electronic Engineering at Nanyang Technological University,<br />
Singapore, and is also affiliated with IDA. Contact him<br />
at _____________<br />
eycsoh@ntu.edu.sg.<br />
Ng Kwang Ming is director of the Grid Computing Lab at the<br />
Malaysian Institute of Microelectronic Systems (MIMOS).<br />
Contact him at ________________<br />
kwang.ming@mimos.my.<br />
Jing-Yuan Luke is a staff engineer in the Grid Computing<br />
Lab at MIMOS. Contact him at _____________<br />
jyluke@mimos.my.<br />
Han Namgoong is a director in the Cloud Computing Research<br />
Department of the Software Research Laboratory at<br />
the Electronics and Telecommunications Research Institute<br />
(ETRI), South Korea. Contact him at nghan@etri.re.kr.<br />
Selected CS articles and columns are available for free at<br />
http://ComputingNow.computer.org.<br />
COMPUTING LIVES<br />
www.computer.org/annals/<strong>computing</strong>-<strong>lives</strong><br />
___________________________________________________<br />
___________<br />
The “Computing Lives” podcast series of selected articles from the IEEE Annals of the History<br />
of Computing cover the breadth of computer history. This series features scholarly accounts<br />
by leading computer scientists and historians, as well as fi rsthand stories by computer pioneers.<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
43
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
44<br />
COVER FEATURE<br />
Edward Walker, University of Texas at Austin<br />
Storage clouds are online services for<br />
leasing disk storage. A new modeling<br />
tool, formulated from empirical data<br />
spanning many years, lets organizations<br />
rationally evaluate the benefit of using<br />
storage clouds versus purchasing hard<br />
disk drives.<br />
Hard disk drives provide storage for a broad range<br />
of devices, from mobile phones to large IT<br />
server farms. In 2008, approximately 590 million<br />
hard disk drives were shipped worldwide, 1<br />
largely driven by the vast amount of information<br />
our digital society is generating. For example, a report<br />
from researchers at the University of California, Berkeley,<br />
estimates that 92 percent of the five exabytes (10 18 ) of<br />
new information created in 2002 was stored on magnetic<br />
media, primarily hard disk drives. 2<br />
At the same time, the business of selling infrastructure<br />
as a service through the Internet is growing. This technology<br />
trend, also known as cloud <strong>computing</strong>, lets individuals<br />
and organizations outsource their IT requirements to<br />
remote data centers, paying for only what they use. The<br />
cloud <strong>computing</strong> industry’s worth was estimated at more<br />
than $16 billion in 2008, and it’s expected to grow to $42<br />
billion by 2012. 3<br />
Several online services currently lease storage infrastructure.<br />
These storage clouds let anyone with a credit<br />
card purchase storage capacity online, paying a monthly<br />
fee for the storage they use. __________<br />
Amazon.com’s S3 service<br />
(http://aws.amazon.com/s3), for example, lets users store<br />
COMPUTER<br />
TO LEASE OR NOT<br />
TO LEASE FROM<br />
STORAGE CLOUDS<br />
Walter Brisken and Jonathan Romney, National Radio Astronomy Observatory<br />
arbitrary objects of up to 5 Gbytes each in their online<br />
storage repositories. The S3 service uses a tiered pricing<br />
structure, with storage getting cheaper as more is used. As<br />
of late 2008, Amazon.com reported that users stored more<br />
than 40 billion objects in the S3 service. 4<br />
With the significant growth of society’s storage requirements,<br />
and the availability of pay-per-use online storage<br />
services, when should a consumer consider using storage<br />
clouds? We focus on the problem of resolving this buy-orlease<br />
storage decision.<br />
BUY OR LEASE<br />
An organization’s decision to buy or lease long-term<br />
assets is often a critical dilemma. The literature describes<br />
numerous models to assist firms in resolving this acquisition<br />
decision. 5-7 However, there is a significant lack of work<br />
in applying these models to compare the cost of purchasing<br />
versus leasing storage from cloud services. Important<br />
studies have examined the cost of performing scientific<br />
experiments using the Amazon.com cloud services, 8,9 but<br />
these prior works are difficult to generalize outside the<br />
scope of the applications used in the studies.<br />
We believe our proposed model for evaluating the benefits<br />
of purchasing versus leasing storage from a cloud<br />
service is the first reported in the literature, offering a<br />
method for deriving a reasonable estimate of the best possible<br />
outcomes from the alternative investment choices.<br />
Furthermore, our model, which we formulated using<br />
empirical disk price data we’ve been collecting weekly<br />
from Pricewatch.com over many years, is agnostic to the<br />
application using the storage cloud. Our empirical data<br />
tracks the lowest prices for serial advanced technology<br />
attachment (SATA) disk drives for sale online since the<br />
Published by the IEEE Computer Society 0018-9162/10/$26.00 © 2010 IEEE<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
technology’s introduction in 2003. This data is significant<br />
because SATA is the predominant drive technology used<br />
in desktop and nearline systems.<br />
Most organizations use financial models as only one data<br />
point in deciding whether to buy or lease an asset. Other<br />
factors also influence their decision. 7 However, our proposed<br />
model bridges a critical gap in the literature and, more<br />
importantly, the market. Our model helps users understand<br />
the premium they’re paying for what seems to be an arbitrarily<br />
priced online storage market. Our research agenda<br />
aims to provide a quantitative framework for rationally reasoning<br />
about the cost of leasing infrastructure from cloud<br />
services, and extends our prior work on leasing from compute<br />
clouds. 10 Importantly, the systematic understanding of<br />
the real cost of leasing assets from cloud services lets users<br />
make rational decisions with innovative pricing structures.<br />
This promotes market transparency and ultimately supports<br />
a competitive product market.<br />
PRELIMINARIES<br />
A key principle in economic finance is the time value<br />
of money. Basically, this principle states that an investor<br />
always prefers to receive some fixed amount of money<br />
today rather than in the future. Hence, when making<br />
buy-or-lease decisions, investors often compare future<br />
cash flows in an investment over time, discounted to their<br />
present value by some interest rate. 5-7 The discounting<br />
interest rate used reflects the risk involved in raising the<br />
capital needed to invest.<br />
In equation form, the simplified standard capitalbudgeting<br />
format for calculating a purchased asset’s net<br />
present value (NPV) is as follows:<br />
NPV P =<br />
N<br />
<br />
T = 0<br />
P P C T T<br />
(1+ I ) K T<br />
S<br />
+ E , N (1+ I ) K<br />
where P is the annual profit resulting from the purchased<br />
T<br />
P asset in year T; C is the asset’s expected annual operat-<br />
T<br />
ing cost at year T; I is the firm’s cost of capital, defined<br />
K<br />
as the interest rate of its outstanding debt used to finance<br />
the purchase; 11 N is the asset’s productive life in years; S is<br />
the asset’s salvage value after N years; and E is the asset’s<br />
purchase (capital) cost.<br />
Similarly, the equation for calculating a leased asset’s<br />
NPV is as follows:<br />
NPV L =<br />
L P C T T<br />
( ) T<br />
N<br />
<br />
T = 0<br />
1+ I K<br />
<br />
LT ( ) T<br />
N<br />
<br />
T = 0<br />
1+ I R<br />
L where C is the leased asset’s expected annual operat-<br />
T<br />
ing cost at year T; L is the lease payment at year T; and<br />
T<br />
I is the interest rate for financing the lease payments. In<br />
R<br />
this formulation, the lease’s financing rate is generally<br />
regarded as smaller than the cost of capital, I , because of<br />
K<br />
,<br />
Table 1. Parameter terms in the buy-or-lease decision model.<br />
Term Description<br />
Cost of electric utility ($/kilowatt hour)<br />
Size of purchased disk drives (Gbytes)<br />
Proportional difierence between human efiort in main -<br />
taining a purchased versus a leased storage infrastructure<br />
ϒ Used disk depreciation factor on salvage ([0.0, 1.0])<br />
C Disk controller unit cost ($)<br />
H Annual human operator salary ($)<br />
T<br />
I Risk-free interest rate (percent)<br />
F<br />
Κ Current per-Gbyte storage price ($/Gbyte)<br />
LT Pc PD VT Expected annual per-Gbyte lease payment ($/Gbyte/year)<br />
Disk controller power consumption (kW)<br />
Disk drive power consumption (kW)<br />
Expected storage requirement in year T (Gbytes)<br />
the involved payment structure’s predictability. 5<br />
With this NPV formulation for asset purchase and lease,<br />
investors can make the buy-or-lease decision using the<br />
following criteria: If the incremental NPV (NPV) 0 <br />
buy; if NPV < 0 lease, where NPV = NPV P – NPV L .<br />
DECISION MODEL<br />
We derive a buy-or-lease decision model that calculates<br />
the comparative NPVs from storage purchase versus<br />
lease. Our model accounts for the expected capital expenditure<br />
from SATA hard disk drive purchase, replacement,<br />
and end-of-use salvage. It also accounts for the expected<br />
operational expenditure for utility consumption and<br />
human operator cost. The “Derivation of the Decision<br />
Model” sidebar describes how we derived our decision<br />
model. We summarize it as follows: If NPV 0 buy; if<br />
NPV < 0 lease, where<br />
C − E + L T T T<br />
ΔNPV =<br />
( 1+ I F ) T<br />
N<br />
S<br />
∑<br />
+ − C<br />
N<br />
T = 0<br />
( 1+ I F )<br />
S =γ ∗ Ω∗⎡⎢ V ⎤ ∗ K ∗e T ⎥Ω −0.438T<br />
C =−ρ∗H − 365 ∗24<br />
T T ( ⎡⎢ ⎤⎥Ω )<br />
( )∗δ ∗ P + P ∗ V C D T<br />
( ⎡⎢ ⎤ − ⎡⎢ V ⎤ ⎥Ω T −1 ⎥Ω )∗Ω∗K ∗e −0.438T<br />
E T = 1.03∗ V T<br />
Table 1 lists the model parameters. We assume ⎡V⎤ fl is<br />
an operator returning the minimum number of fl-sized<br />
disk drives needed to store V Gbytes of data. The derived<br />
terms S, C T , and E T represent the expected end-of-life disk<br />
salvage value, the operating cost in year T, and the capital<br />
cost in year T, respectively.<br />
EXAMPLE APPLICATION<br />
We used our decision model to evaluate the advantages<br />
of purchasing versus leasing storage from a hypothetical<br />
storage cloud vendor.<br />
.<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
(1)<br />
45
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
46<br />
COVER FEATURE<br />
We calculate the incremental net present value (ΔNPV) as<br />
follows:<br />
ΔNPV = NPV − NPV P L<br />
⇒<br />
PT − C P<br />
T<br />
( 1+ IK ) T<br />
N<br />
L<br />
S<br />
P − C L T T<br />
T<br />
∑ + − E − +<br />
T T<br />
T =0 ( 1+ IK ) ( 1+ IK ) ( 1+ IR ) T<br />
N<br />
N<br />
∑ ∑<br />
T =0<br />
T =0<br />
⇒<br />
C L P − CT<br />
T<br />
( 1+ IK ) T<br />
N<br />
S<br />
L T<br />
∑ + +<br />
N<br />
T =0 ( 1+ IK ) ( 1+ IR ) T<br />
N<br />
∑ − E.<br />
T =0<br />
Assuming that profit from storage is equal in both the buy and<br />
lease cases—that is, using 1 Tbyte of storage from a purchased<br />
disk or from a storage cloud results in the same level of<br />
productivity—the above simplification results in the removal of<br />
the profit term P T .<br />
Capital cost<br />
Three components make up the cost of purchasing storage E:<br />
The consumer needs a disk controller to house the purchased<br />
disks.<br />
The consumer purchases disk drives in blocks based on<br />
increasing storage needs.<br />
The consumer must periodically replace disks due to<br />
failure.<br />
These components contribute to the future cash flow E as<br />
follows:<br />
E =<br />
COMPUTER<br />
DERIVATION OF THE DECISION MODEL<br />
( ( ⎡⎢ V ⎤ − ⎡⎢ V ⎤ T ⎥Ω T −1⎥Ω<br />
)∗Ω+R T )∗G T<br />
( ) T<br />
E T<br />
1+ I K<br />
⇒ E = + C<br />
T<br />
( 1+ IK )<br />
E = V T ( ( ⎡⎢ ⎤ − ⎡⎢ V ⎤ T ⎥Ω T −1⎥Ω<br />
)∗Ω+R T )∗G , T<br />
where Ω represents the hard disk drive size in Gbytes; V T is the<br />
storage requirement in Gbytes at year T; ⎡V T ⎤ Ω is an operator that<br />
returns the minimum number of Ω-sized disk drives needed to<br />
store V T ; G T is the predicted cost per Gbyte of disk storage at year<br />
T; R T is the disk replacement in Gbytes at year T; and C is the disk<br />
controller cost.<br />
The important insight in this formulation is that the capital<br />
cost isn’t all incurred at the start of the project, unlike in traditional<br />
NPV models. Rather, it’s a time-varying formula in which<br />
users can grow their storage systems as their requirements<br />
evolve. We modify ΔNPV to reflect this growth in capital cost:<br />
ΔNPV =<br />
N<br />
∑<br />
T =0<br />
S<br />
+<br />
1+ IK L P C − CT − ET<br />
T<br />
( )<br />
( ) T<br />
1+ I K<br />
Operating cost<br />
− C<br />
LT +<br />
N<br />
( ) T<br />
N<br />
∑<br />
T =0<br />
1+ I R<br />
P We estimate the operating cost of purchased storage, C , by T<br />
calculating the electric utility cost associated with running the<br />
+ C<br />
disk controller and the disk units, plus the cost of a human<br />
operator to manage the system/data. These cost components<br />
P contribute to C as follows:<br />
T<br />
P C = (365⋅24)∗δ ∗ PC + P T<br />
( ∗⎡⎢ V ⎤ D T ⎥Ω )+α∗H , T<br />
where δ is the utility cost ($/kilowatt per hour); P is the control-<br />
C<br />
ler’s power requirement in kWs; P is the power requirement in<br />
D<br />
kWs per disk drive; and α is the proportion of the human operator<br />
cost, H , required to maintain the system/data at year T.<br />
T<br />
L The operating cost for leased storage, C , only includes the<br />
T<br />
cost of a human operator to manage the data. Thus, we calculate<br />
L L<br />
C as CT = β∗HT , where β is the proportion of the human opera-<br />
T<br />
tor cost required to maintain the data on the leased storage at<br />
year T. Substituting ρ for (α – β), we can modify ΔNPV to reflect the<br />
operating costs as follows:<br />
ΔNPV =<br />
N<br />
∑<br />
T =0<br />
−ρ∗H T − 365⋅24<br />
( )∗δ ∗( P + P ∗⎡⎢ V ⎤ C D T ⎥Ω )− ET ( ) T<br />
L T<br />
1+ I K<br />
S<br />
− C + +<br />
.<br />
N<br />
( 1+ IK ) ( 1+ IR ) T ∑<br />
T =0<br />
Approximating the best outcomes<br />
N<br />
Consumers often find it difficult to estimate their capital cost<br />
and the lease financing rates available to them. We therefore suggest<br />
an approximate method of evaluating the buy-or-lease<br />
decision by deriving the best possible outcome in both the purchase<br />
and lease cases.<br />
From the well-known economic Law of One Price, 1 we can<br />
derive the upper bounds for NPV P and NPV L by substituting I K and<br />
I R with the risk-free interest rate I F . The “Corollary for Estimating<br />
the Upper-bound Present Value” sidebar explains this in more<br />
detail. In turn, we can estimate the risk-free interest rate, I F , from<br />
the published return on an instrument such as government treasury<br />
bills. We can therefore derive an approximation of the<br />
decision criteria using these best NPVs, letting us further simplify<br />
the currently derived version of ΔNPV to:<br />
ΔNPV =<br />
N<br />
∑<br />
T =0<br />
( )∗δ ∗( P + P ∗⎡⎢ V ⎤ C D T ⎥Ω )− E + L T T<br />
( ) T<br />
−ρ∗H T − 365∗24<br />
S<br />
− C +<br />
.<br />
( 1+ IF ) N<br />
Disk price trends<br />
1+ I F<br />
We haven’t yet provided a function for the term G , which we need<br />
T<br />
to calculate E and to estimate the cost of disk storage at year T.<br />
T<br />
Since April 2003, we’ve been collecting SATA disk price data<br />
from Pricewatch.com on a weekly basis. We collected price data<br />
for all available disk drive sizes each week—250 Gbytes, 500<br />
Gbytes, and so on—regardless of manufacturer or model. Figure<br />
A plots the 10 lowest prices each week for SATA disk drives across<br />
all the available drive sizes. Approximating the observed exponential<br />
trend line using regression analysis, we obtain the formula<br />
′ − 0.0012 X G = 1.2984e .<br />
X<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
′ The function G predicts the cost per Gbyte<br />
X<br />
of SATA disk storage X days from 20 April 2003,<br />
′ with G = 1.2984 when X = 0. We can therefore<br />
X<br />
approximate the function G by assuming that<br />
T<br />
the future disk price trend conforms to the<br />
equation K ∗ eC ∗ T , where K represents the lowest<br />
storage price per Gbyte available to the consumer<br />
at T = 0; and T represents the number of<br />
years in the future. We therefore derive G as G T T<br />
= K ∗ e –0.0012∗ 365 ∗ T⇒ G = K ∗ e T –0.438∗ T .<br />
Disk replacement rates<br />
Any realistic cost model for disk storage ownership<br />
must estimate the disk replacement cost.<br />
A recent large-scale study of disk failures measured<br />
the annualized replacement rate (ARR) of<br />
disk drives in real data centers. 2 The study<br />
observed ARRs in the range of 0.5 to 13.5 percent,<br />
with the most commonly observed ARRs in<br />
the 3 percent range.<br />
In our model, we approximate R T with this<br />
empirical approximation of the disk replacement<br />
rate by using the formula R T = 0.03 * Ω *<br />
⎡V T ⎤ Ω . In this formula, the constant 0.03 represents the observed<br />
3 percent disk replacement rate. 2 Thus, we can simplify E T to:<br />
–0.438∗ T<br />
E = (( ⎡V ⎤ – ⎡V ⎤ ) ∗ Ω + 0.03 ∗ Ω ∗⎡V⎤ ) ∗ K ∗ e T T Ω T – 1 Ω T Ω<br />
⇒ E = (1.03 ∗⎡V⎤ – ⎡V ⎤ ) ∗ Ω ∗ K · e T T Ω T – 1 Ω –0.438∗ T .<br />
Disk salvage value<br />
$/GByte<br />
We assume a hard disk drive can be sold in the used market for<br />
some salvage value at the end of its life. To predict this salvage<br />
value, we leverage the future disk price prediction formula, discounting<br />
the predicted price by some depreciation factor, γ, in the<br />
We assume this vendor lets users purchase raw disk<br />
storage over the Internet. We’re only interested in the storage<br />
cloud’s pricing structure for the end user, and we don’t<br />
assume any particular service access technology. Table 2<br />
shows the assumed tiered monthly pricing structure. For<br />
illustrative purposes, we don’t consider data uploading or<br />
downloading costs.<br />
Single-user computers<br />
Single-user computers make up the vast majority of all<br />
shipped disk storage capacity. 2 For our study, we assume<br />
the same user owns and operates the single-user computer.<br />
This user’s storage requirement grows at a moderate rate<br />
of 100 Gbytes per year. Therefore, regardless of where<br />
data is stored, we assume the level of effort in managing<br />
the system/data is approximately equal in both cases<br />
because of the low storage volume involved—that is,<br />
= 0. We assume the user must purchase a new disk<br />
controller (C = $1,000), specified to consume 0.5 kW of<br />
power. Also, as storage is required, the user will purchase<br />
2.5<br />
2.0<br />
1.5<br />
1.0<br />
0.5<br />
y = 1.2984e – 0.0012 X<br />
Disk price<br />
Exponential (disk price)<br />
0 200 400 600 800 1,000 1,200 1,400 1,600 1,800 2,000<br />
Start date: 20 April 2003<br />
Days<br />
Figure A. Weekly SATA disk price data collected from Pricewatch.com from<br />
20 April 2003 to 19 August 2008.<br />
range [0, 1]. In equation form, this gives us the salvage value S = γ<br />
* Ω * ⎡V T ⎤ Ω ∗ K ∗ e –0.438 ∗ T , simplifying into ΔNPV as shown by<br />
Equation 1 in the main text.<br />
References<br />
1. O.A. Lamont and R.H. Thaler, “Anomalies: The Law of One<br />
Price in Financial Markets,” J. Economic Perspective, vol. 17, no.<br />
4, 2003, pp. 191-202.<br />
2. B. Schroeder and G. Gibson, “Disk Failures in the Real World:<br />
What Does an MTTF of 1,000,000 Hours Mean to You?” Proc.<br />
5th Usenix Conf. File and Storage Technologies (FAST 07),<br />
Usenix Assoc., 2007, pp. 1-16.<br />
COROLLARY FOR ESTIMATING THE<br />
UPPER-BOUND PRESENT VALUE<br />
We derive the following corollary from the economic Law of<br />
One Price, which states, “In an efficient market, identical<br />
goods will have only one price.”<br />
Corollary 1. The upper bound of the present values for the purchase<br />
and lease price equilibrium in an efficient market is derived<br />
from the risk-free interest rate, I . F<br />
Informal proof: In an efficient market, an arbitrager has no<br />
opportunity to make a risk-free profit. Assuming an efficient market<br />
in which financing at the risk-free rate is possible for a subset of<br />
agents, the proof is by contradiction. Thus, if the present value of<br />
the lease price is higher than that derived from the risk-free rate, I , F<br />
an arbitrager can purchase disks from monies borrowed at the riskfree<br />
rate, lease at this higher price, and pocket the risk-free profit.<br />
Also, if the present value of the purchase price is higher than that<br />
derived from the risk-free rate, I , an arbitrager can purchase a disk<br />
F<br />
from monies borrowed at the risk-free rate, sell the disk at some<br />
future instance at this higher price, and pocket the risk-free profit.<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
47
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
48<br />
Year<br />
(T)<br />
ΔNPV (thousands of dollars)<br />
–50<br />
COVER FEATURE<br />
0<br />
–100<br />
–150<br />
–200<br />
–250<br />
–300<br />
0 2 4 6<br />
Operational years<br />
8 10 12<br />
Figure 1. The calculated NPV values for a medium-size enterprise deciding<br />
whether to buy or lease storage with life expectancy from 0 to 10 years.<br />
ΔNPV (thousands of dollars)<br />
150<br />
100<br />
50<br />
0<br />
–50<br />
–100<br />
–150<br />
–200<br />
0 2 4 6 8 10 12<br />
Operational years<br />
Figure 2. The calculated NPVs for a large-size enterprise deciding whether to<br />
buy or lease storage with life expectancy from 0 to 10 years.<br />
500-Gbyte disk drives ( = 500), with a present cost of<br />
$150 per drive (K = $0.30), each specified to consume 0.01<br />
kW of power. Finally, we assume the electric utility cost<br />
is $0.04 per kilowatt hour (kWh), and the end-of-life disk<br />
salvage depreciation factor is 0.1.<br />
Table 3 shows the worksheet for the buy-or-lease deci-<br />
COMPUTER<br />
Table 2. Hypothetical storage cloud pricing structure.<br />
Default Storage > 50 Tbytes Storage > 100 Tbytes Storage > 500 Tbytes<br />
$0.15/Gbyte/month $0.14/Gbyte/month $0.13/Gbyte/month $0.12/Gbyte/month<br />
Storage<br />
requirement<br />
in Gbytes (V T )<br />
Purchased<br />
drives<br />
Table 3. Buy-or-lease decision model worksheet for a single-user computer.<br />
Operating<br />
cost (C T )<br />
Capital<br />
cost<br />
(E T )<br />
Lease<br />
payment<br />
(L T ) Recurring cost (CPV T )<br />
sion model for an expected storage life<br />
expectancy of 0 to 6 years. We compute the<br />
values for the “purchased drive” column<br />
using V T 500 – V T–1 500 , and the NPVs using<br />
Equation 1. In addition, we calculate the<br />
recurring costs (CPV T ) and salvage values<br />
(SPV T ) representing terms in the formula:<br />
ΔNPV = CPV + SPV – C<br />
T T<br />
C – E + I T T T<br />
CPV = T<br />
( 1 + I K ) T<br />
T<br />
∑<br />
T – 0<br />
SPV .<br />
T =<br />
S<br />
( 1 + I K ) T<br />
Salvage value<br />
(SPV T )<br />
Incremental<br />
net present<br />
value (NPV)<br />
0 100 1 ($178.70) $154.50 $98 ($236) $15.00 ($1,221)<br />
1 200 0 ($178.70) $2.90 $278 ($141) $9.58 ($1,131)<br />
2 300 0 ($178.70) $1.87 $458 $131 $6.12 ($863)<br />
3 400 0 ($178.70) $1.21 $638 $575 $3.91 ($421)<br />
4 500 0 ($178.70) $0.78 $818 $1,188 $2.50 $190<br />
5 600 1 ($182.21) $17.79 $998 $1,947 $3.19 $950<br />
6 700 0 ($182.21) $0.65 $1,178 $2,884 $2.04 $1,886<br />
Notes: C = $1,000, = 500 Gbytes, Κ = $0.30 ($150 per 500 Gbytes), = 0, = 0.1, = $0.04, P = 0.5 kW, P = 0.01 kW, and I = 1 percent.<br />
C D K<br />
The worksheet shows that for an<br />
expected storage life expectancy of less<br />
than four years, leasing is always the preferred<br />
option. This is because of the high<br />
cost of the disk controller the user purchases<br />
at the outset. If the storage system<br />
will likely exist for more than four years,<br />
however, purchasing storage is the superior<br />
choice.<br />
Medium-size enterprises<br />
Medium-size enterprises—those with<br />
clusters of tens to hundreds of servers—<br />
made up approximately 50 percent of all<br />
data centers installed in the US from 2000 to 2007. 12 We<br />
assume our medium-size enterprise has a storage requirement<br />
that grows at 1 Tbyte a year to serve a moderate-size<br />
data center of tens or low hundreds of servers.<br />
For such an enterprise, the human operator burden<br />
in owning and operating a storage cluster will be larger<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
than that of leasing from the storage cloud vendor. We<br />
therefore assume the proportional difference in the operator’s<br />
level of effort required to manage the system/data<br />
(H T = $70,000 per year) is = 0.5. We assume that<br />
the firm must purchase an enterprise-class RAID disk<br />
controller (C = $2,000), specified to consume 0.7 kW<br />
of power. Also, as storage is needed, the enterprise will<br />
purchase 1-Tbyte disk drives ( = 1,000), with a present<br />
cost of $300 per drive (K = $0.30), each specified<br />
to consume 0.01 kW of power. Finally, we assume the<br />
electric utility cost is $0.04 per kWh, and the end-of-life<br />
disk salvage depreciation factor is 0.1.<br />
Figure 1 shows the calculated NPV values for a storage<br />
life expectancy of 0 to 10 years. In all the operational lifetimes<br />
examined, the model shows that leasing is always<br />
preferable to purchasing storage. In this case, the clear<br />
recommendation to the medium-size enterprise is to lease<br />
storage from the storage cloud vendor.<br />
Large-size enterprises<br />
Next, we look at the benefits of purchasing versus leasing<br />
storage for a large-size enterprise—for example, a<br />
data center with thousands of servers. In this scenario, we<br />
assume the large enterprise’s storage requirement grows<br />
at 10 Tbytes per year.<br />
In this case, the human operator burden in owning and<br />
operating a storage cluster is even larger than that of leasing<br />
from the storage cloud vendor. We therefore assume<br />
the proportional difference in the operator’s level of effort<br />
required to manage the system/data (H T = $70,000/year)<br />
is = 1.0. We also assume that the firm must purchase an<br />
enterprise-class RAID disk controller (C = $2,000), specified<br />
to consume 0.7 kW of power. Furthermore, we assume<br />
the controller has a peak capacity of 100 Tbytes, and the<br />
firm will purchase additional controllers as the storage<br />
need arises.<br />
For the actual storage, the enterprise will purchase<br />
1-Tbyte disk drives ( = 1,000), with a present cost of<br />
$300 per drive (K = $0.30), each specified to consume 0.01<br />
kW of power. Finally, as before, we assume the electric utility<br />
cost is $0.04 per kWh, and the end-of-life disk salvage<br />
depreciation factor is 0.1.<br />
Figure 2 shows the calculatedNPVs for a storage life<br />
expectancy of 0 to 10 years. As the graph shows, leasing<br />
storage is advantageous up to a nine-year storage life<br />
expectancy. After that, it becomes more advantageous for<br />
the enterprise to purchase and maintain a storage cluster.<br />
Thus, the final decision to buy or lease storage will depend<br />
on the expected use of the storage and data. For example,<br />
if the storage is destined for use by a server cluster with<br />
a five-year life expectancy, the enterprise should lease<br />
storage. However, if the storage is destined for a long-term<br />
archival system with an indefinite life expectancy, the<br />
enterprise should purchase storage instead.<br />
LATENCY IS NOT ZERO<br />
A common flawed assumption in designing distributed<br />
systems is the notion that latency is zero. In fact, latency isn’t<br />
zero for cloud services. Accessing storage from across the<br />
commodity Internet can incur a substantial cost in terms<br />
of I/O latency. Our model doesn’t account for this latency.<br />
However, future extensions can incorporate this factor by<br />
estimating the profit parameter, P T , which we assumed to<br />
be equal when deriving our current model. We can use this<br />
profit parameter to reward services with faster response<br />
times. For example, an enterprise might naïvely consider a<br />
service that’s two times faster to be more productive, and<br />
hence two times more profitable. For the moment, we leave<br />
this substantive extension to a future time.<br />
Our primary purpose in this article is to stimulate<br />
discussion, debate, and future work in the quantitative<br />
modeling of the cloud <strong>computing</strong> industry.<br />
To this end, we propose a model to assist consumers,<br />
researchers, and policy makers in estimating the<br />
benefit of leasing from storage clouds.<br />
Ultimately, an organization’s buy-or-lease decision will<br />
depend on their anticipated parameters in the analysis.<br />
Our model simply provides a first stepping-stone for rational<br />
decision making to prevail in the cloud <strong>computing</strong><br />
market.<br />
Acknowledgments<br />
This article is based on work supported in part by US National<br />
Science Foundation grant 0721931.<br />
References<br />
1. K. Chandar, “SSD & HDD Market Tracker,” iSuppli<br />
research report, 2009; www.isuppli.com/Abstract/<br />
________________________________<br />
ABSTRACT - SSD_HDD Market Tracker 2009.pdf.<br />
2. P. Lyman and H.R. Varian, “How Much Information?”<br />
Oct. 2003, School of Information Management and Systems,<br />
Univ. of Calif., Berkeley; ______________<br />
www2.sims.berkeley.<br />
_____________________________<br />
edu/research/projects/how-much-info-2003.<br />
3. N. Leavitt, “Is Cloud Computing Really Ready for<br />
Prime Time?” Computer, Jan. 2009, pp. 15-20.<br />
4. A. Henry, “Keynote Address: Cloud Storage FUD<br />
(Failure, Uncertainty, and Durability),” presented at<br />
the 7th Usenix Conf. File and Storage Technologies,<br />
2009; www.usenix.org/media/events/fast09/tech/<br />
____________<br />
videos/henry.mov.<br />
5. R.W. Johnson and W.G. Lewellen, “Analysis of Leaseor-Buy<br />
Decision,” J. Finance, vol. 27, no. 4, 1972, pp.<br />
815-823.<br />
6. G.B. Harwood and R.H. Hermanson, “Lease-or-Buy<br />
Decisions,” J. Accountancy, vol. 142, no. 3, 1976, pp.<br />
83-87.<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
49
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
50<br />
COVER FEATURE<br />
7. P.F. Anderson and J.D. Martin, “Lease vs. Purchase<br />
Decisions: A Survey of Current Practice,” Financial<br />
Management, vol. 6, no. 1, 1977, pp. 41-47.<br />
8. M. Palankar et al., “Amazon S3 for Science Grids: A<br />
Viable Solution?” Proc. Int’l Workshop Data-Aware<br />
Distributed Computing, ACM Press, 2008, pp. 55-64.<br />
9. E. Deelman et al., “The Cost of Doing Science on the<br />
Cloud: The Montage Example,” Proc. ACM/IEEE Conf.<br />
Super<strong>computing</strong>, IEEE Press, pp. 1-16.<br />
10. E. Walker, “The Real Cost of a CPU Hour,” Computer,<br />
Apr. 2009, pp. 35-41.<br />
11. W.G. Lewellen, The Cost of Capital, Wadsworth Publishing,<br />
1970.<br />
12. US Environmental Protection Agency, Energy<br />
Star Program, Report to Congress on Server and<br />
Data Center Energy Efficiency, Public Law 109-<br />
431, Aug. 2007; www.energystar.gov/ia/partners/<br />
___________________________________<br />
prod_development/downloads/EPA_Datacenter_<br />
Report_Congress_Final1.pdf.<br />
___________________<br />
Edward Walker is a researcher with the Texas Advanced<br />
Computing Center at the University of Texas at Austin.<br />
His research interests include distributed systems, storage<br />
systems, and operating systems. Walker received a PhD in<br />
Welcomes Your Contribution<br />
COMPUTER<br />
Computer<br />
magazine<br />
looks ahead<br />
to future<br />
technologies<br />
computer science from the University of York, UK. He is a<br />
member of IEEE and the ACM. Contact him at ewalker@ ______<br />
computer.org.<br />
Walter Brisken is a scientist at the National Radio Astronomy<br />
Observatory. His research interests include pulsars,<br />
the ionized interstellar medium, and very long baseline<br />
interferometry. Brisken received a PhD in physics from<br />
Princeton University. He is a member of the American<br />
Astronomical Society. Contact him at _____________<br />
wbrisken@nrao.edu.<br />
Jonathan Romney is a scientist at the National Radio<br />
Astronomy Observatory. His research interests include<br />
active galactic nuclei and astronomical instrumentation.<br />
Romney received a PhD in astronomy from the California<br />
Institute of Technology. He is a member of the American<br />
Astronomical Society, the International Astronomical<br />
Union, and the International Union of Radio Science (URSI).<br />
Contact him at jromney@aoc.nrao.edu.<br />
________________<br />
Selected CS articles and columns are available for free<br />
at http://ComputingNow.computer.org.<br />
Computer, the flagship publication of the IEEE<br />
Computer Society, publishes peer-reviewed<br />
technical content that covers all aspects of<br />
computer science, computer engineering,<br />
technology, and applications.<br />
Articles selected for publication in Computer<br />
are edited to enhance readability for the nearly<br />
100,000 <strong>computing</strong> professionals who receive<br />
this monthly magazine.<br />
Readers depend on Computer to provide current,<br />
unbiased, thoroughly researched information on<br />
the newest directions in <strong>computing</strong> technology.<br />
To submit a manuscript for peer review,<br />
see Computer’s author guidelines:<br />
www.computer.org/computer/author.htm<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
COVER FEATURE<br />
Karthik Kumar and Yung-Hsiang Lu, Purdue University<br />
The cloud heralds a new era of <strong>computing</strong><br />
where application services are provided<br />
through the Internet. Cloud <strong>computing</strong><br />
can enhance the <strong>computing</strong> capability of<br />
mobile systems, but is it the ultimate solution<br />
for extending such systems’ battery<br />
lifetimes?<br />
Cloud <strong>computing</strong> 1 is a new paradigm in which<br />
<strong>computing</strong> resources such as processing,<br />
memory, and storage are not physically present<br />
at the user’s location. Instead, a service<br />
provider owns and manages these resources,<br />
and users access them via the Internet. For example,<br />
Amazon Web Services lets users store personal data via<br />
its Simple Storage Service (S3) and perform computations<br />
on stored data using the Elastic Compute Cloud (EC2).<br />
This type of <strong>computing</strong> provides many advantages<br />
for businesses—including low initial capital investment,<br />
shorter start-up time for new services, lower maintenance<br />
and operation costs, higher utilization through virtualization,<br />
and easier disaster recovery—that make cloud<br />
<strong>computing</strong> an attractive option. Reports suggest that there<br />
are several benefits in shifting <strong>computing</strong> from the desktop<br />
to the cloud. 1,2 What about cloud <strong>computing</strong> for mobile<br />
users? The primary constraints for mobile <strong>computing</strong> are<br />
limited energy and wireless bandwidth. Cloud <strong>computing</strong><br />
can provide energy savings as a service to mobile users,<br />
though it also poses some unique challenges.<br />
0018-9162/10/$26.00 © 2010 IEEE<br />
CLOUD COMPUTING<br />
FOR MOBILE USERS:<br />
CAN OFFLOADING<br />
COMPUTATION<br />
SAVE ENERGY?<br />
Published by the IEEE Computer Society<br />
SAVING ENERGY FOR MOBILE SYSTEMS<br />
Mobile systems, such as smart phones, have become<br />
the primary <strong>computing</strong> platform for many users. Various<br />
studies have identified longer battery lifetime as the most<br />
desired feature of such systems. A 2005 study of users in<br />
15 countries 3 found longer battery life to be more important<br />
than all other features, including cameras or storage. A<br />
survey last year by ChangeWave Research 4 revealed short<br />
battery life to be the most disliked characteristic of Apple’s<br />
iPhone 3GS, while a 2009 Nokia poll showed that battery<br />
life was the top concern of music phone users.<br />
Many applications are too computation intensive to<br />
perform on a mobile system. If a mobile user wants to use<br />
such applications, the computation must be performed in<br />
the cloud. Other applications such as image retrieval, voice<br />
recognition, gaming, and navigation can run on a mobile<br />
system. However, they consume significant amounts of<br />
energy. Can offloading these applications to the cloud save<br />
energy and extend battery lifetimes for mobile users?<br />
Low-power design has been an active research topic for<br />
many years. In IEEE Xplore, searching “low” and “power”<br />
in the document title produces more than 5,000 results.<br />
There are four basic approaches to saving energy and extending<br />
battery lifetime in mobile devices:<br />
Adopt a new generation of semiconductor technology.<br />
As transistors become smaller, each transistor<br />
consumes less power. Unfortunately, as transistors<br />
become smaller, more transistors are needed to provide<br />
more functionalities and better performance; as<br />
a result, power consumption actually increases.<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
51
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
52<br />
COVER FEATURE<br />
Communication D<br />
COMPUTER<br />
Never<br />
offioad<br />
Computation C<br />
Depends<br />
on<br />
bandwidth<br />
B<br />
Always<br />
offioad<br />
Figure 1. Očoading is benećcial when large amounts of<br />
computation C are needed with relatively small amounts of<br />
communication D.<br />
Avoid wasting energy. Whole systems or individual<br />
components may enter standby or sleep modes to<br />
save power.<br />
Execute programs slowly. When a processor’s clock<br />
speed doubles, the power consumption nearly octuples.<br />
If the clock speed is reduced by half, the<br />
execution time doubles, but only one quarter of the<br />
energy is consumed.<br />
Eliminate computation all together. The mobile system<br />
does not perform the computation; instead, computation<br />
is performed somewhere else, thereby extending<br />
the mobile system’s battery lifetime.<br />
We focus on the last approach for energy conservation.<br />
Ofioading computation to save energy<br />
Sending computation to another machine is not a new<br />
idea. The currently popular client-server <strong>computing</strong> model<br />
enables mobile users to launch Web browsers, search<br />
the Internet, and shop online. What distinguishes cloud<br />
<strong>computing</strong> from the existing model is the adoption of virtualization.<br />
Instead of service providers managing programs<br />
running on servers, virtualization allows cloud vendors<br />
to run arbitrary applications from different customers on<br />
virtual machines.<br />
Cloud vendors thus provide <strong>computing</strong> cycles, and users<br />
can use these cycles to reduce the amounts of computation<br />
on mobile systems and save energy. Thus, cloud <strong>computing</strong><br />
can save energy for mobile users through computation<br />
offloading. 5 Virtualization, a fundamental feature in cloud<br />
<strong>computing</strong>, lets applications from different customers run<br />
on different virtual machines, thereby providing separation<br />
and protection.<br />
Energy analysis for computation ofioading<br />
Various cost/benefit studies focus on whether to offload<br />
computation to a server. 6,7 The following example provides<br />
a simple analysis for this decision.<br />
Suppose the computation requires C instructions. Let<br />
S and M be the speeds, in instructions per second, of the<br />
cloud server and the mobile system, respectively. The same<br />
task thus takes C/S seconds on the server and C/M seconds<br />
on the mobile system. If the server and mobile system exchange<br />
D bytes of data and B is the network bandwidth, it<br />
takes D/B seconds to transmit and receive data. The mobile<br />
system consumes, in watts, P c for <strong>computing</strong>, P i while<br />
being idle, and P tr for sending and receiving data. (Transmission<br />
power is generally higher than reception power,<br />
but for the purpose of this analysis, they are identical.)<br />
If the mobile system performs the computation, the<br />
energy consumption is P c × (C/M). If the server performs<br />
the computation, the energy consumption is [P i × (C/S)] +<br />
[P tr × (D/B)]. The amount of energy saved is<br />
P c × C<br />
M − P i<br />
× C<br />
S − P tr<br />
D<br />
× . (1)<br />
B<br />
Suppose the server is F times faster—that is, S = F × M.<br />
We can rewrite the formula as<br />
C<br />
M × Pc − P ⎛ ⎞ i<br />
⎝<br />
⎜ F ⎠<br />
⎟ − P D<br />
× . (2)<br />
tr B<br />
Energy is saved when this formula produces a positive<br />
number. The formula is positive if D/B is sufficiently small<br />
compared with C/M and F is sufficiently large. The values<br />
of M, P , P , and P are parameters specific to the mobile<br />
i c th<br />
system. For example, an HP iPAQ PDA with a 400-MHz<br />
(M = 400) Intel XScale processor has the following values:<br />
P fi 0.9 W, P fi 0.3 W, and P fi 1.3 W.<br />
c i tr<br />
If we use a four-core server, with a clock speed of 3.2<br />
GHz, the server speedup F may be given by (S/M) fi [(3.2<br />
× 1,024 × 4 × X)/400], where X is the speedup due to<br />
additional memory, more aggressive pipelining, and so<br />
forth. If we assume X = 5, we obtain the value of F fi 160.<br />
The value of F can increase even more with cloud <strong>computing</strong><br />
if the application is parallelizable, since we can<br />
offload computation to multiple servers. If we assume that<br />
F = 160, Equation 2 becomes<br />
C<br />
400<br />
⎛ 0.3 ⎞<br />
× 0.9 −<br />
⎝<br />
⎜<br />
160⎠<br />
⎟ − 1.3 × D<br />
B<br />
D<br />
≈ 0.00225 × C − 1.3 × . (3)<br />
B<br />
For offloading to break even, we equate Equation 3 to<br />
zero and obtain<br />
B ≈ 577.77 × o D<br />
, (4)<br />
C<br />
where B o is the minimum bandwidth required for offloading<br />
to save energy, determined by the ratio of (D/C). If (D/C)<br />
is low, then offloading can save energy. Thus, as Figure<br />
1 shows, offloading is beneficial when large amounts of<br />
computation C are needed with relatively small amounts<br />
of communication D.<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
Sample applications bene ting from ofioading<br />
Two sample applications illustrate the benefits of<br />
offloading: a chess game and image retrieval.<br />
Chess is one of the world’s most popular games. A<br />
chessboard has 8 × 8 = 64 positions. Each player controls<br />
16 pieces at the beginning of the game. Chess is<br />
Markovian, meaning that the game is fully expressed by<br />
the current state. Each piece may be in one of the 64 possible<br />
locations and needs 6 bits to represent the location.<br />
(This is an overestimate: Some pieces have restrictions—<br />
for example, a bishop can move to only half of the board,<br />
that is, 32 possible locations). To represent a chess game’s<br />
current state, it is sufficient to state that 6 bits × 32 pieces<br />
= 192 bits = 24 bytes; this is smaller than the size of a<br />
typical wireless packet.<br />
The amount of computation for chess is very large; Claude<br />
Shannon and Victor Allis estimated the complexity of chess<br />
to exceed the number of atoms in the universe. Chess can be<br />
parallelized, 8 making the value of F in Equation 2 very large.<br />
Since the amount of computation C is extremely large, and D<br />
is very small, chess provides an example where offloading is<br />
beneficial for most wireless networks.<br />
An image retrieval application retrieves images similar<br />
in content to a query from an image collection. The<br />
program accomplishes this by comparing numerical representations<br />
of the images, called features. The features<br />
for the image collection can be computed in advance;<br />
for a query, the program computes its features during<br />
retrieval and compares these with the image collection.<br />
Since most of the computation is done in advance, less<br />
computation is performed online, and the value of C is<br />
small. D is large since considerable data must be sent. As<br />
a result, even if the values of F become fl, D/B might still<br />
be too large when compared to C/M in Equation 2. Thus,<br />
offloading saves energy only if B is very large—that is,<br />
at high bandwidths.<br />
The “Mobile Image Processing” sidebar has more detail<br />
on the advantages of mobile devices offloading image retrieval<br />
to the cloud.<br />
Making computation ofioading more attractive<br />
Analysis indicates that the energy saved by computation<br />
offloading depends on the wireless bandwidth B, the<br />
amount of computation to be performed C, and the amount<br />
of data to be transmitted D. Existing studies thus focus on<br />
determining whether to offload computation by predicting<br />
the relationships among these three factors.<br />
However, there is a fundamental assumption underlying<br />
this analysis with the client-server model: Because the<br />
server does not already contain the data, all the data must<br />
be sent to the service provider. The client must offload the<br />
program and data to the server. For example, typically a<br />
newly discovered server for computation offloading does<br />
not already contain a mobile user’s personal image collec-<br />
MOBILE IMAGE PROCESSING<br />
Mobile devices such as cell phones and PDAs are becoming<br />
increasingly popular. Most of these devices are equipped<br />
with cameras and have several gigabytes of ash storage<br />
capable of storing thousands of images. With such large image<br />
collections, two functionalities become important: accessing<br />
specićc sets of images from the collection, and transmitting the<br />
images over a wireless network to other devices and servers for<br />
storage.<br />
For accessing a specićc set of images, content-based image<br />
retrieval (CBIR) can be a better alternative than manually browsing<br />
through all of them. For example, a user might want to view<br />
all images containing a specićc person or captured at a specićc<br />
location. Mobile image retrieval allows the user to obtain the<br />
relevant pictures by comparing images and eliminating the<br />
irrelevant matches on the mobile system.<br />
Several studies propose performing CBIR on mobile<br />
devices. 1-4 Because these mobile devices are battery powered,<br />
energy conservation is important. 2-4 It is energy e cient to par -<br />
tition CBIR between the mobile device and server depending on<br />
the wireless bandwidth. 3 As the bandwidth increases, očoad -<br />
ing image retrieval saves more energy.<br />
Most of the energy consumption for očoaded applications<br />
is due to transmission. For image retrieval, transmitting the<br />
images over a wireless network consumes signićcant amounts<br />
of energy. The images may be preprocessed on the mobile<br />
device before transmission5 to reduce the transmission energy.<br />
This reduction in transmission energy is achieved by reducing<br />
the ćle sizes. However, the amount of energy saved depends on<br />
the wireless bandwidth and the image contents.<br />
Preprocessing the images saves energy if the reduction in<br />
transmission energy compensates for the energy spent due to<br />
preprocessing. If the wireless bandwidth is high, the value of the<br />
former reduces. Moreover, di erent images may have di erent<br />
values of the latter based on their contents. Hence preprocessing<br />
must be adaptive based on the wireless bandwidth and the<br />
image contents. Wireless transmission energy is the most signić -<br />
cant bottleneck to energy savings in mobile cloud <strong>computing</strong>,<br />
and such techniques will become increasingly signićcant as it<br />
becomes more popular.<br />
References<br />
1. J. Yang et al., “A Fast Image Retrieval System Using Index<br />
Lookup Table on Mobile Device,” Proc. 19th Int’l Conf. Pattern<br />
Recognition (ICPR 08), IEEE Press, 2008, pp. 265-271.<br />
2. C. Zhu et al., “iScope: Personalized Multimodality Image<br />
Search for Mobile Devices,” Proc. 7th Int’l Conf. Mobile Systems,<br />
Applications, and Services (Mobisys 09), ACM Press,<br />
2009, pp. 277-290.<br />
3. Y-J. Hong, K. Kumar, and Y-H. Lu, “Energy-Efficient Content-<br />
Based Image Retrieval for Mobile Systems,” Proc. IEEE Int’l<br />
Symp. Circuits and Systems (ISCAS 09), IEEE Press, 2009, pp.<br />
1673-1676.<br />
4. D. Chen et al., “Tree Histogram Coding for Mobile Image<br />
Matching,” Proc. 2009 Data Compression Conf., IEEE CS Press,<br />
2009, pp. 143-152.<br />
5. Y. Nimmagadda, K. Kumar, and Y-H. Lu, “Energy-Efficient<br />
Image Compression in Mobile Devices for Wireless Transmission,”<br />
Proc. IEEE Int’l Conf. Multimedia and Expo (ICME 09), IEEE<br />
Press, 2009, pp. 1278-1281.<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
53
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
54<br />
COVER FEATURE<br />
(a)<br />
(b)<br />
User<br />
User<br />
tion. However, cloud <strong>computing</strong> changes that assumption:<br />
The cloud stores data and performs computation on it. For<br />
example, services like Google’s Picasa and Amazon S3<br />
can store data, and Amazon EC2 can be used to perform<br />
computation on the data stored using S3.<br />
This results in a significant change in the value of D for<br />
most applications. There is no longer a need to send the<br />
data over the wireless network; it suffices to send a pointer<br />
to the data. Also, the value of F is elastic: Large numbers of<br />
processors can be obtained on the cloud. This increases<br />
the energy savings in Equation 2: A very small D and very<br />
large F imply that energy can always be saved.<br />
CHALLENGES AND POSSIBLE SOLUTIONS<br />
Does this make cloud <strong>computing</strong> the “ultimate” solution<br />
to the energy problem for mobile devices? Not<br />
quite. While cloud <strong>computing</strong> has tremendous potential<br />
to save energy, designers must consider several issues<br />
including privacy and security, reliability, and handling<br />
real-time data.<br />
Privacy and security<br />
In cloud <strong>computing</strong>, Web applications and data replace<br />
traditional stand-alone programs, which are no longer<br />
stored in users’ computers. Shifting all data and <strong>computing</strong><br />
resources to the cloud can have implications for privacy<br />
and security. Because the data is stored and managed in<br />
the cloud, security and privacy settings depend on the IT<br />
management the cloud provides.<br />
A bug or security loophole in the cloud might result in<br />
a breach of privacy. For example, in March 2009, a bug<br />
in Google caused documents to be shared without the<br />
owners’ knowledge, 9 while a July 2009 breach in Twitter<br />
allowed a hacker to obtain confidential documents. 10<br />
Cloud service providers typically work with many thirdparty<br />
vendors, and there is no guarantee as to how these<br />
vendors safeguard data. For example, a phishing attack in<br />
2007 duped a staff member for salesforce.com into reveal-<br />
COMPUTER<br />
Data<br />
Data<br />
E (data) E (data)<br />
Encrypt Internet<br />
E(data)<br />
Encrypt<br />
E (data) E (data)<br />
Internet<br />
Cloud<br />
storage<br />
Data<br />
Decrypt Data<br />
Cloud<br />
storage<br />
Figure 2. Two encryption scenarios for cloud <strong>computing</strong>. (a) Data remain decrypted at the cloud storage site, preventing<br />
unauthorized access through the Internet; the cloud vendor cannot access the data either. (b) Data are decrypted by the cloud<br />
vendor to enable necessary operations on the data.<br />
ing a password; 13 the attacker then used the password to<br />
access confidential data.<br />
Another potential privacy violation is the “tracking”<br />
of individuals through location-based navigation data<br />
offloaded to the cloud. Moreover, data stored at one location<br />
may not be secure at another due to different access<br />
rules. For example, the EU has stricter privacy protection<br />
than the US, where laws such as the Patriot Act give government<br />
agencies and other entities more power to access<br />
personal information. Since the storage locations are typically<br />
unknown to the user, determining what laws apply to<br />
safeguarding data can be difficult. This may raise serious<br />
security concerns for a company that stores its trade secrets<br />
in the cloud, or a user who uploads a patentable idea<br />
from a mobile system to the cloud.<br />
Clearly, some types of data cannot be stored in the<br />
cloud without considering these privacy and security implications.<br />
One possible solution is to encrypt data before<br />
storage. However, encryption alone will not solve the problem.<br />
Figure 2 shows two encryption scenarios. In Figure 2a,<br />
the data remain encrypted at the cloud storage site. This<br />
can prevent unauthorized access even when the storage is<br />
breached in the cloud; the cloud vendor cannot access the<br />
data either. In Figure 2b, the cloud vendor decrypts data to<br />
perform operations on that data. For example, in the case<br />
of a document, the cloud vendor must know which words<br />
are used to check spelling; for a spreadsheet, the cloud<br />
application must know the numbers for calculation. This<br />
is the general case for cloud services.<br />
Another possible privacy and security solution is to<br />
use a technique called steganography, as described in the<br />
“Data Outsourcing and Privacy” sidebar. Steganographic<br />
techniques can be used to transform the data so that operations<br />
can be performed without exposing them.<br />
Performing encryption or steganographic techniques<br />
before sending data to the cloud requires some additional<br />
processing C p on the mobile system and consumes additional<br />
energy. Equation 2 thus can be rewritten as<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
DATA OUTSOURCING AND PRIVACY<br />
Data outsourcing refers to sending data outside users’ immediate <strong>computing</strong><br />
environment. This is an increasingly important concern for cloud <strong>computing</strong>. As<br />
government agencies shift to the cloud (for example, www.apps.gov and www.data.<br />
gov), information like healthcare, criminal, and tax records move to the cloud. This<br />
makes security and privacy a critical concern.<br />
Multimedia content like images and videos have signićcant redundancy. This<br />
makes it possible to hide data in multimedia using steganography. 1 Figure A shows<br />
an example of steganography: images (a) and (c) look identical, but image (c) contains<br />
image (b) hidden in it. Applying appropriate transformations to image (c) can<br />
obtain image (b). Steganographic techniques can be used to transform the data<br />
before storage so that operations can still be performed on the data.<br />
(a) (b) (c)<br />
Figure A. An example of steganography: images (a) and (c) look identical,<br />
but image (c) contains image (b) hidden in it. Applying appropriate<br />
transformations to image (c) can obtain image (b).<br />
For text documents and spreadsheets, however, there is little redundancy. This<br />
makes it di cult to transform the data and still perform operations. For example,<br />
it is hard to spell check a text document that has alphabets mapped onto symbols.<br />
If the mapping is one-to-one and onward, alphabet frequency can be easily used<br />
to determine the words. Similarly, if the elements in a spreadsheet are transformed,<br />
performing meaningful mathematical operations on them is di cult.<br />
Performing computation on encrypted or steganographic data still remains an<br />
open research problem.<br />
Developing a hybrid cloud is an interim solution to the data outsourcing problem.<br />
A hybrid cloud is “a cloud <strong>computing</strong> environment in which an organization<br />
provides and manages some resources in-house and has others provided externally”<br />
(searchcloud<strong>computing</strong>.com). _________________<br />
The claim is that this is more feasible<br />
currently because large enterprises already have the substantial investments in<br />
their infrastructure required to provide resources in-house. In addition, many<br />
organizations would prefer to keep sensitive data under their own control to<br />
ensure privacy and security.<br />
Reference<br />
1. F.A.P. Petitcolas, R.J. Anderson, and M.G. Kuhn, “Information Hiding—A Survey,”<br />
Proc. IEEE, Special Issue on Protection of Multimedia Content, vol. 87, no. 7, 1999,<br />
pp. 1062-1078.<br />
C<br />
M × Pc − P ⎛ ⎞ i<br />
⎝<br />
⎜ F ⎠<br />
⎟ − Ptr D<br />
×<br />
B − Pc × C p<br />
, (5)<br />
M<br />
where P c × (C p /M) is the additional energy required to protect privacy and<br />
security. If this value is significant, cloud <strong>computing</strong> might not save energy<br />
for the mobile user. Instead, it may be more energy efficient to perform<br />
operations on the mobile system, since C p = 0 when the device performs<br />
the computation.<br />
Reliability<br />
Another potential concern with mobile<br />
cloud <strong>computing</strong> is reliability. 11 A mobile<br />
user performing computation in the cloud<br />
depends on the wireless network and<br />
cloud service. Dependence on the wireless<br />
network implies that cloud <strong>computing</strong><br />
may not even be possible, let alone energy<br />
efficient, when connectivity is limited.<br />
This is typical in regions like national<br />
parks; a user may thus not be able to organize,<br />
retrieve, or identify any images<br />
captured in the park. Mobile cloud <strong>computing</strong><br />
is also difficult in locations such<br />
as the basement of a building, interior of<br />
a tunnel, or subway. In these cases, where<br />
the value of B in Equation 2 can become<br />
very small or even zero, cloud <strong>computing</strong><br />
does not save energy.<br />
Dependence on the cloud for important<br />
computations could lead to problems<br />
during service outages. Several service<br />
providers such as Google, Amazon, and<br />
T-Mobile have experienced such outages,<br />
as Table 1 shows. These can significantly<br />
reduce the value of F in Equation 2.<br />
Data storage presents another reliability<br />
problem. In October 2009, both<br />
T-Mobile’s and Microsoft’s mobile Sidekick<br />
service crashed, and all customers<br />
lost their data and contacts. One option<br />
in such scenarios involves an independent<br />
backup of data with an alternate service<br />
provider, which might increase the value<br />
of D in Equation 2.<br />
Real-time data<br />
Some applications—including chess,<br />
searching newly captured images for<br />
content-based image retrieval, mobile surveillance,<br />
and context-aware navigation<br />
—have real-time data. In such scenarios,<br />
D in Equation 2 is no longer a pointer to<br />
the data; it refers to the actual data. For<br />
applications like chess, the value of D is<br />
small and hence offloading can still save<br />
energy. When the value of D is large,<br />
offloading may not save energy. In such<br />
cases, performing the computation on the<br />
mobile system may be more energy efficient.<br />
A possible solution is partitioning<br />
computation between the mobile system<br />
and the cloud to reduce energy consumption.<br />
Such a solution may include partially<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
55
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
56<br />
COVER FEATURE<br />
processing the real-time data on the mobile system. If the<br />
processed data are smaller in size, sending the processed<br />
data to the server reduces the wireless transmission energy.<br />
Our analysis suggests that cloud <strong>computing</strong> can<br />
potentially save energy for mobile users. However,<br />
not all applications are energy efficient<br />
when migrated to the cloud. Mobile cloud<br />
<strong>computing</strong> services would be significantly<br />
different from cloud services for desktops because they<br />
must offer energy savings. The services should consider<br />
the energy overhead for privacy, security, reliability, and<br />
data communication before offloading.<br />
Acknowledgments<br />
We thank Jibang Liu for the steganography images used in<br />
this article.<br />
References<br />
1. M. Creeger, “CTO Roundtable: Cloud Computing,” ACM<br />
Queue, June 2009, pp. 1-2.<br />
2. Google Tech Talk, “Away with Applications: The Death<br />
of the Desktop,” 4 May 2007; http://video.google.com/<br />
__________________________<br />
videoplay?docid=-6856727143023456694.<br />
3. CNN.com, “Battery Life Concerns Mobile Users,” 23 Sept.<br />
2005; www.cnn.com/2005/TECH/ptech/09/22/phone.<br />
____ study.<br />
4. J. Paczkowski, “Iphone Owners Would Like to Replace<br />
Battery,” All Things Digital, 21 Aug. 2009; http://<br />
digitaldaily.allthingsd.com/20090821/iphone-ownerswould-like-to-replace-battery-att.<br />
COMPUTER<br />
Table 1. Service provider outages. 11,12<br />
Outage date Vendor Service<br />
July 2008 Amazon S3 outage<br />
Feb 2008 Amazon S3 outage<br />
August 2008 Google Gmail service outage<br />
October 2009 T-Mobile/Microsoft Sidekick loses users’ data<br />
build your career<br />
IN COMPUTING<br />
5. K. Yang, S. Ou, and H.H. Chen, “On Effective Offloading<br />
Services for Resource-Constrained Mobile Devices Running<br />
Heavier Mobile Internet Applications,” IEEE Comm.<br />
Magazine, vol. 46, no. 1, 2008, pp. 56-63.<br />
6. C. Wang and Z. Li, “Parametric Analysis for Adaptive Computation<br />
Offloading,” ACM SIGPLAN Notices, vol. 39, no. 6,<br />
2004, pp. 119-130.<br />
7. R. Wolski et al., “Using Bandwidth Data to Make Computation<br />
Offloading Decisions,” Proc. IEEE Int’l Symp. Parallel<br />
and Distributed Processing (IPDPS 08), 2008, pp. 1-8.<br />
8. M. Newborn, “A Parallel Search Chess Program,” Proc. ACM<br />
Ann. Conf. Range of Computing: Mid-80’s Perspective, ACM<br />
Press, 1985, pp. 272-277.<br />
9. J. Kincaid, “Google Privacy Blunder Shares Your Docs<br />
without Permission,” TechCrunch, 7 Mar. 2009; ____ http://<br />
___________________________________<br />
techcrunch.com/2009/03/07/huge-google-privacy-blunder-<br />
_______________________<br />
shares-your-docs-without-permission.<br />
10. R. McMillan, “Hacker: I Broke into Twitter,” PCWorld.<br />
com, 1 May 2009; www.pcworld.com/businesscenter/<br />
______________________________<br />
article/164182/hacker_i_broke_into_twitter.html.<br />
11. M. Armbrust et al., “Above the Clouds: A Berkeley View of<br />
Cloud Computing,” tech. report UCB/EECS-2009-28, EECS<br />
Dept., Univ. of California, Berkeley, 2009.<br />
12. T-Mobile Forums, “A Message from Our Chief Operations<br />
Officer, Jim Alling,” 6 Oct. 2009; http://forums.t-mobile.<br />
com/t5/Previous-Sidekick-Models/A-Message-From-Our-<br />
_____________________________<br />
Chief-Operations-Officer-Jim-Alling/m-p/200661.<br />
13. R. McMillan, “Salesforce.com Warns Customers of Phishing<br />
Scam,” PCWorld, 6 Nov. 2007; http://www.pcworld.<br />
___________________________________<br />
com/businesscenter/article/139353/salesforcecom_warns_<br />
customers_of_phishing_scam.html.<br />
______________________<br />
Karthik Kumar is a PhD candidate in the School of Electrical<br />
and Computer Engineering at Purdue University.<br />
His research interests include energy conservation for<br />
mobile systems and resource allocation for scalable <strong>computing</strong>.<br />
Kumar is a student member of IEEE. Contact him<br />
at kumar25@purdue.edu.<br />
_______________<br />
Yung-Hsiang Lu is an associate professor in the School of<br />
Electrical and Computer Engineering at Purdue University.<br />
His research focuses on energy efficiency of <strong>computing</strong><br />
systems. Lu received a PhD in electrical engineering from<br />
Stanford University. He is a senior member of IEEE. Contact<br />
him at yunglu@purdue.edu.<br />
_____________<br />
www.computer.org/buildyourcareer<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
RESEARCH FEATURE<br />
Linking Software<br />
Development<br />
and Business<br />
Strategy through<br />
Measurement<br />
Victor R. Basili, Mikael Lindvall, Myrna Regardie, and Carolyn Seaman,<br />
Fraunhofer Center for Experimental Software Engineering<br />
Jens Heidrich, Jürgen Münch, Dieter Rombach, and Adam Trendowicz,<br />
Fraunhofer Institute for Experimental Software Engineering<br />
The GQM + Strategies approach extends the goal/question/metric<br />
paradigm for measuring the success or failure of goals and strategies,<br />
adding enterprise-wide support for determining action on the basis<br />
of measurement results. An organization can thus integrate its<br />
measurement program across all levels.<br />
Most organizations that develop software try<br />
to retain their competitive edge by reducing<br />
software-related risks. Effective risk management<br />
requires aligning business goals<br />
with development strategies and translating<br />
the results into a quantitative project management<br />
plan. In addition, organizations must also justify cost and<br />
resources for software and system development and other<br />
IT services. Often, such justification demands a concrete<br />
demonstration of how such development will contribute<br />
to the organization’s overall business goals—the top-level<br />
goals the organization desires to accomplish.<br />
Working against both alignment and justification is the<br />
lack of methods for linking business goals and softwarerelated<br />
efforts. Without a deep understanding of how software<br />
development fits into their organization’s business<br />
objectives, decision makers can neither plan development<br />
nor evaluate the organization-wide success of development<br />
strategies.<br />
0018-9162/10/$26.00 © 2010 IEEE<br />
Published by the IEEE Computer Society<br />
To address this need, we have developed GQM + Strategies,<br />
which uses measurement to link goals and strategies on all<br />
organizational levels. The approach is based on rationales for<br />
deciding when and how to transform goals into operations<br />
and how to evaluate the success of strategies with respect<br />
to those goals. The “Why Business Alignment?” sidebar describes<br />
our motivation for developing this approach.<br />
As the name implies, GQM + Strategies is based on the<br />
goal/question/metric (GQM) paradigm 1 but adds the ability<br />
to create measurement programs that ensure alignment<br />
between goals and strategies from the highest strategic<br />
business levels to individual development projects and vice<br />
versa. 2 Although we derived the approach from software<br />
development experiences, it is not necessarily applicable<br />
solely to this domain.<br />
GOAL-ORIENTED APPROACHES<br />
Software development organizations often encounter<br />
problems when instituting measurement programs, such<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
57
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
58<br />
RESEARCH FEATURE<br />
as collecting too much data, failing to gather useful or correct<br />
data, and not having a mechanism for analyzing the<br />
data in a way that contributes to sound strategic decisions.<br />
This leads to numerous problems, including decreased<br />
cost-effectiveness of the measurement program and disillusionment<br />
about metrics on the part of developers and<br />
managers. The end result is often the eventual failure of<br />
the measurement program as a whole.<br />
COMPUTER<br />
WHY BUSINESS ALIGNMENT?<br />
With the increasing dependence on software and other<br />
information technology (IT) has come a commensurate<br />
growth in software system size and complexity. This growth in<br />
turn has magnified the cost, schedule, and quality concerns<br />
that have always plagued software development. For decades,<br />
software engineering researchers and practitioners<br />
have attempted to reduce development cost, shorten development<br />
time, and increase quality. Although great strides<br />
have been made in all three areas, software growth along all<br />
dimensions (size, complexity, pervasiveness, criticality, and so<br />
on) has outpaced the ability to control all the developmentrelated<br />
factors.<br />
Ečorts to dećne and understand these relationships have made<br />
one notion crystal clear: Issues related to software cost, schedule,<br />
and quality are inextricably linked with the larger issues that face<br />
the businesses developing the software—regardless of the specićc<br />
business objectives. Some businesses sell what they develop,<br />
either as contracted custom software or as commercial shrinkwrapped<br />
applications. Others sell a product or service, of which<br />
software is a signićcant component. Still others might develop<br />
software only to support their organizational IT infrastructure so<br />
that they can develop and market products more ečectively.<br />
Finally, some have no commercial interest at all, such as nonproćt<br />
organizations, government entities, or educational institutions.<br />
Although all these organizational conćgurations challenge their<br />
development projects in dičerent ways, the point is that all have a<br />
larger business context, which encompasses larger business goals,<br />
strategies, and success measures. All software development<br />
projects must consider context factors—the variables that represent<br />
the organizational environment and ačect the kind of models<br />
and data the project can use.<br />
The problem is not that businesses fail to achieve their objectives,<br />
but rather that they do not always state these objectives<br />
explicitly or clearly enough to verify that they have indeed achieved<br />
those objectives. It is even less clear how a business translates its<br />
objectives into its lower organizational levels and into individual<br />
projects. At present, no methodology bridges the gap between<br />
business strategies and their project-level implementation.<br />
Quantitative data is a prerequisite to understanding the relationships<br />
between the business and project-level goals and<br />
verifying the achievement of objectives—one reason that software<br />
development maturity requires the use of quantitative measures.<br />
However, popular software improvement strategies, such as Capability<br />
Maturity Model Integration and the IT Infrastructure Library,<br />
are not directly and explicitly linked to business value. Consequently,<br />
the investment in collecting data does not result in the<br />
expected benećts, and the contribution of project performance to<br />
the achievement of strategic goals remains unclear.<br />
To address these problems, researchers have developed<br />
goal-oriented approaches—so called because they<br />
use goals, objectives, strategies, or other mechanisms to<br />
guide the choice of data to be collected and systematically<br />
analyzed. The GQM approach, for example, provides a<br />
method for an organization or a project to define goals,<br />
refine those goals into specifications of the data to be collected,<br />
and then analyze and interpret the resulting data in<br />
light of the original goals. Implicit in the GQM approach is<br />
the use of interpretation models, which help practitioners<br />
interpret the resulting data in a specific context. The GQM<br />
approach has served the software industry for several decades<br />
in defining measurement programs, but it does not<br />
explicitly provide support for motivating and integrating<br />
the measurement of goals at various organizational levels,<br />
such as project goals, business objectives, and corporate<br />
strategies. It also does not encourage users to explicitly<br />
document assumptions, estimated unknowns that can<br />
affect data interpretation.<br />
Another goal-oriented approach, Balanced Scorecard<br />
(BSC), 3 links strategic objectives and measures through a<br />
scorecard, which consists of four perspectives: financial,<br />
customer, internal business processes, and learning and<br />
growth. BSC does not dictate a static set of measures, but<br />
rather serves as a framework for strategic measurement<br />
and management. As such, it is a tool for defining strategic<br />
goals from multiple perspectives beyond a purely financial<br />
focus, but it does not address lower-level goal setting.<br />
Practical Software Measurement (PSM) 4 offers detailed<br />
guidance on software measurement, including providing<br />
a catalog of specific measures and information on how an<br />
organization can apply those measures in projects. PSM<br />
also includes a process for choosing measures according<br />
to the issues and objectives relevant to a software development<br />
project. For the most part, however, approaches such<br />
as BSC and PSM do not support the alignment of objectives<br />
at different organizational levels, or this is simply not the<br />
focus of these approaches.<br />
Researchers have also proposed various combinations<br />
of GQM, BSC, and PSM 5-8 that recognize the need to link<br />
higher- and lower-level goals. However, because these<br />
approaches do not support different goals at explicitly<br />
linked organizational levels, it is difficult to feed analytical<br />
results and interpretations back up the chain. In<br />
contrast, GQM + Strategies creates mappings between the<br />
data related to goals at different levels so that insights<br />
gained relative to one goal at one level—whether project<br />
or departmental, or a business objective—can support and<br />
contribute to satisfying goals at other organizational levels<br />
without requiring that each level share the same goals.<br />
Some application domains have specific requirements<br />
that emphasize the need to link business goals to lowerlevel<br />
properties. Organizations are becoming increasingly<br />
aware, for example, that the IT infrastructure itself im-<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
Goal + Strategies element GQM graph<br />
inffiuences<br />
Context/<br />
assumption<br />
inffiuences<br />
Figure 1. GQM + Strategies components. The primary components are the Goal + Strategies element and the GQM graph. The<br />
Goal + Strategies element includes a single goal and derived strategies, as well as all context information and assumptions that<br />
explain how goals and strategies link. The GQM graph refiects a single GQM goal, the corresponding questions and metrics, and an<br />
interpretation model.<br />
poses significant risks, which has led to several regulatory<br />
constraints in both the IT governance and IT service domains,<br />
such as the Sarbanes-Oxley Act in the US. 9<br />
The solutions proposed by models in these domains<br />
offer connections between predefined sets of goals and attributes<br />
of the IT infrastructure. They are sharply focused<br />
on a particular domain, such as IT governance, and define<br />
a very detailed model that fits that domain quite well. To<br />
apply such an approach, however, the organization must<br />
strictly follow the prescribed model. Release 4 of the Control<br />
Objectives for Information and Related Technology<br />
(CoBIT) standard (www.isaca.org), for example, is based<br />
on a process model that subdivides IT into four domains<br />
and 34 processes.<br />
Approaches such as CoBIT and the IT Infrastructure<br />
Library (ITIL) provide no mechanism for adapting and tailoring<br />
the solution, nor do they support addressing the<br />
specific context or documenting inherent assumptions.<br />
No clearly defined interpretation model indicates if an<br />
overall strategy is working or has to be changed to avoid<br />
business failure.<br />
COMPONENTS OF AN<br />
INTEGRATED APPROACH<br />
Goal<br />
Strategy<br />
realized<br />
by a<br />
set of<br />
leads to<br />
a set of<br />
> made<br />
measurable<br />
through<br />
< measures<br />
achievement<br />
of<br />
GQM + Strategies aims to address the weaknesses of existing<br />
goal-oriented approaches by providing both explicit<br />
links among organizational levels and the flexibility to<br />
tailor the approach to the organization’s specific needs and<br />
objectives. Eight conceptual components form the basis for<br />
constructing a consistent model. Figure 1 illustrates how<br />
these components interrelate.<br />
GQM goal<br />
Goal + Strategies element GQM graph<br />
made measurable through<br />
Question<br />
Question<br />
Interpretation model<br />
is part of<br />
Metric<br />
Metric<br />
Metric<br />
Business goals: goals the organization wishes to accomplish<br />
in general to achieve its strategic objectives.<br />
Context factors: environmental variables that represent<br />
the organizational environment and affect the<br />
kind of models and data that can be used.<br />
Assumptions: estimated unknowns that can affect the<br />
interpretation of the data.<br />
Strategies: a set of possible approaches for achieving a<br />
goal that may be refined by a set of concrete activities.<br />
Level i goals: a set of lower-level goals inherited from<br />
the previous level’s (i 1) goals as part of the previous<br />
level’s goal strategy—an example is a goal related to<br />
a project that is part of a selected software strategy.<br />
Interpretation models: models that help interpret<br />
data to determine if the goals at all levels have been<br />
achieved.<br />
Goal + Strategies element: a single goal and derived<br />
strategies (including a set of concrete activities), as<br />
well as all context information and assumptions that<br />
explain how the goal and corresponding strategies<br />
are linked.<br />
GQM graph: a single GQM goal that measures a<br />
Goal + Strategies element and its corresponding questions,<br />
metrics, and interpretation models.<br />
All organizations have business goals, such as improving<br />
customer satisfaction, garnering market share, and<br />
reducing production costs, and they devise strategies<br />
to deal with them, taking into account the context and<br />
making explicit any assumptions. Strategies specify how<br />
to achieve the goal and should, in turn, define lower-level<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
59
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
60<br />
RESEARCH FEATURE<br />
Figure 2. A GQM + Strategies model for ABC, a company that provides its customers with information services through the Web.<br />
GQM + Strategies enforces the explicit documentation of the relevant context factors and assumptions that are necessary for<br />
understanding and evaluating each goal. A Goal + Strategies element consists of a goal and an associated strategy (bottom of each<br />
goal box). Each element, in turn, is associated with a GQM graph (green rectangle to the right of the goal) representing questions and<br />
metrics as well as an interpretation model that evaluates if the goal was achieved.<br />
goals for various parts of the organization, such as software,<br />
hardware, and marketing. An organization might<br />
devise a separate set of strategies to deal with these lowerlevel<br />
goals. The number of goal and strategy levels depends<br />
on the organization’s internal structure.<br />
Assumptions and context information about the organization<br />
strongly influence the definition of goals and<br />
strategies. Measuring the effectiveness and the accomplishment<br />
of goals and the effectiveness of strategies at<br />
all levels is critical for business success. And making goals<br />
connected and transparent at all levels helps in communicating<br />
and achieving them. What most organizations need<br />
is support for these concepts.<br />
The components in Figure 1 provide this support by allowing<br />
multiple goal levels and multiple strategies for each<br />
goal (a GQM + Strategies element), as well as a measurement<br />
plan (GQM graph). The GQM + Strategies element provides<br />
the basic components for deriving the goals and strategies<br />
as influenced by the context; the basic known facts about<br />
the market, the organization, the product, and so on; and<br />
the assumptions—factors that are assumed or guessed<br />
but not known for sure. A key element is making the context<br />
and assumptions explicit so that they can be verified.<br />
The relevant context and assumptions aid in defining the<br />
rationale for choosing specific goals and strategies. A set<br />
COMPUTER<br />
Business level<br />
Software level<br />
Project level<br />
GQM + Strategies elements<br />
Goal 1: Increase profit<br />
from software service usage<br />
Strategy 1: Deliver<br />
added functionality<br />
Goal 2: Deliver 5% new<br />
functionality every 6 months<br />
within 10% of budget<br />
Strategy 2: Use MoSCoW<br />
and Cocomo<br />
Goal 3: Apply MoSCoW<br />
and Cocomo effectively<br />
Strategy 3: Conduct<br />
training, determine tools,<br />
perform pilot study<br />
GQM goals<br />
G1: Evaluate<br />
trend in profit<br />
G2: Evaluate<br />
functional<br />
growth of each<br />
release<br />
G3: Evaluate<br />
effectiveness<br />
of MoSCow<br />
and Cocomo<br />
Questions Metrics Interpretation model<br />
Q1: What is<br />
the current<br />
profit?<br />
Q2: What is<br />
the profit for<br />
year 2 and<br />
year 3?<br />
Q3: How<br />
many M<br />
requirements<br />
in each release?<br />
Q4: How<br />
long between<br />
releases?<br />
Q5: Cost<br />
estimation<br />
accuracy? BV: budget<br />
variance<br />
Q6: How<br />
extensive<br />
was the<br />
training?<br />
Q7: What is<br />
cost of<br />
training?<br />
P0: current<br />
annual<br />
profit<br />
PX: annual<br />
profit for<br />
year x<br />
MR: number<br />
of customerrequested<br />
requirements<br />
(M)<br />
implemented<br />
RD: release<br />
duration<br />
NT: number<br />
of trainees<br />
TC: hours<br />
spent in<br />
training<br />
If P2 0<br />
and<br />
P3 2<br />
and …<br />
then goal is<br />
satisfied<br />
of predefined goals and strategies can become part of an<br />
organization-specific experience base and allow different<br />
parts of the organization to select and adapt predefined<br />
goals and strategies.<br />
Associated with each GQM + Strategies element is a<br />
measurement plan that uses the GQM approach measurement<br />
and evaluation framework to specify how to<br />
evaluate the goal, what data to collect, and how to interpret<br />
that data. The nodes of each GQM graph consist of<br />
a measurement goal, which describes what knowledge<br />
needs to be gained from the measurement activity; a set<br />
of questions to be answered; the metrics and data items<br />
required to answer the questions; and an interpretation<br />
model that specifies how the data items are to be<br />
combined and what the criteria are for determining the<br />
goal’s success.<br />
The nodes are related semihierarchically. A goal can<br />
have several associated measurement goals, each of<br />
which is the basis for an entire GQM graph. However, different<br />
GQM structures are likely to use some of the same<br />
questions and metrics, and interpretation models might<br />
combine data from different GQM structures, thus optimizing<br />
metrics collection. The results of the lower-level<br />
interpretation models feed into the higher-level ones to<br />
provide feedback on lower-level goal achievement.<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
…<br />
…
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
With the complete model, an organization can<br />
not only define measurement consistent with<br />
larger, upper-level organizational concerns, but<br />
also interpret and roll up the resulting measurement<br />
data at each level.<br />
AN APPLICATION<br />
To illustrate the features of our approach, we<br />
consider a fictitious but representative type of<br />
organization, ABC, which provides information<br />
services to its customers through the Web. Customers<br />
do not buy the software, but rather pay a<br />
service fee for access to information and to software<br />
that searches, analyzes, and presents that<br />
information. Thus, the business model implies that<br />
the number of customer accesses to ABC’s system<br />
determines the company’s revenue. Figure 2 represents<br />
a model of this application.<br />
Business goals<br />
Although the approach is flexible enough to accommodate<br />
several different entry points, the starting point of the<br />
GQM + Strategies process in this example is a business goal.<br />
As Goal 1 shows, one of ABC’s business goals is to increase<br />
profit from software service use. The GQM + Strategies approach<br />
enforces the explicit documentation of the relevant<br />
context factors and assumptions necessary for understanding<br />
and evaluating each goal. For Goal 1, one such<br />
context factor is that how often customers access ABC<br />
software products determines the amount of revenue generated<br />
at ABC.<br />
The GQM + Strategies goal template documents other<br />
details. Each template includes the desired magnitude of<br />
improvement, the time frame for achieving the goal, the<br />
scope of responsibility for achieving the goal, and any<br />
constraints or conflicting goals as well as relationships to<br />
other goals. Figure 3 shows a partial template for Goal 1.<br />
The GQM graph in Figure 2 is based on the measurement<br />
goal, G1. In full GQM notation, G1 is<br />
Analyze the trend in profit for the purpose of evaluation<br />
with respect to a 10 percent increase in annual income per<br />
year from the point of view of ABC’s management in the<br />
context of the ABC organization.<br />
This goal leads to questions Q1 and Q2: What is the current<br />
profit (measured by P 0 ), and what is the profit for each<br />
succeeding year (as measured by P x )? The decision maker<br />
analyzes the results using the criteria incorporated in the<br />
interpretation model (far right), which says that<br />
Starting in year 2, if the profit for the current year (P ) is 2<br />
at least 10 percent (1.1 times) higher than the profit for the<br />
initial preceding year (P ), then the goal has been satisfied.<br />
1<br />
Activity: Increase<br />
Focus: Net income<br />
Object: ABC Web services<br />
Magnitude: 10% per year<br />
Time frame: Annually, beginning in 2 years<br />
Scope: Development groups assessed at CMMI level 2 or higher<br />
Constraints: Available resources, ability to sustain CMMI levels<br />
Relations: CMMI-related goals<br />
Figure 3. Business goal “Increase pro t from software service usage”<br />
expressed in the GQM + Strategies goal template. Business goals are at the<br />
top level of the GQM + Strategies model. They become measurable through<br />
the derivation of one or more GQM graphs, which are then associated<br />
with other GQM graphs at other organizational levels.<br />
The full interpretation model, not shown for simplicity,<br />
includes an “else” part related to the effectiveness of the<br />
chosen strategies.<br />
The strategies associated with each goal come from a<br />
list of potential strategies that the GQM + Strategies user<br />
has enumerated, taking into account influencing context<br />
factors. Possible strategies for meeting Goal 1 are to deliver<br />
added capabilities to encourage heavier system use,<br />
increase rates charged to customers, or reduce development<br />
costs. The user opted for the strategy of delivering<br />
added functionality in the product releases at regular and<br />
frequent intervals. At this point, the user must also make<br />
explicit the assumption that this added functionality will<br />
lead to increased customer satisfaction, which will in turn<br />
lead to heavier use.<br />
The assumption is that ABC has enough projects with<br />
a Capability Maturity Model Integration maturity level<br />
greater than 1 that, if just those projects provide a 15 percent<br />
improvement, ABC will see a 10 percent improvement<br />
overall. In general, all context information and assumptions<br />
are attached to goals, strategies, and their relations<br />
(as Figure 1 shows) and are documented in a corresponding<br />
graph (not shown).<br />
Software-development goals<br />
At the next level down in the model is a goal derived<br />
from the strategy (or strategies) chosen at the top level.<br />
Goal 2 is to deliver a new release of the software every six<br />
months that incorporates at least 5 percent more functionality<br />
than the previous release and to keep the cost<br />
of this increased functionality to within 10 percent of the<br />
current budget.<br />
These are really two interrelated but separate software<br />
goals, so the user defines them in separate GQM + Strategies<br />
goal templates. Figure 4 elaborates the first of these goals<br />
(increasing functionality by 5 percent). At this level, the<br />
goal is specific to software development, so it is treated as<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
61
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
62<br />
RESEARCH FEATURE<br />
Activity: Deliver<br />
Focus: More usable functionality, for example, M (must) type requirements<br />
from the backlog of customer-requested requirements<br />
Object: Each release of ABC Web services software<br />
Magnitude: 5% more functionality than the prior release<br />
Time frame: Every 6 months, beginning in 2 years<br />
Scope: Web services development projects with CMMI level 2 or higher<br />
Constraints: Available resources, ability to sustain CMMI levels, ability to estimate<br />
cost, and schedule for a release<br />
Relations: Achievement of cost and schedule estimate accuracy, ability to improve<br />
CMMI levels of development groups<br />
Figure 4. Software goal template for the goal “Deliver 5 percent new<br />
functionality every six months.” A separate but related software goal,<br />
which would have its own template, would address the 10 percent cost<br />
variance. Both these goals are derived from a higher-level strategy that<br />
addresses the business goal of increasing revenue from increased use of<br />
ABC’s software products.<br />
for x = 2, 3, …<br />
if Px ≥ 1.1 * Px–1 then<br />
the goal has been satisfied,<br />
else if functionality was increased appropriately, then<br />
either some assumption is incorrect or we have chosen the wrong level of strategy.<br />
Figure 5. Re ning the interpretation model from Figure 2 by adding<br />
an “else” part. Full interpretation—the exact reason that a particular<br />
goal was not satis ed—depends on goals at lower levels. This iterative<br />
re nement ensures that goals at all levels are linked and makes goal<br />
interrelationships explicit.<br />
a goal at the software level, as opposed to one at the business<br />
level. In general, the name accorded the lower levels<br />
depends on the organization applying GQM + Strategies and<br />
the number of levels to be modeled.<br />
The software goal template asks for the same categories<br />
of information as the business goal template in Figure<br />
3. The user defines the measurement and interpretation<br />
model for this goal and refines the interpretation model<br />
for the business goal. As Figure 5 shows, the refinement of<br />
Figure 2’s interpretation model involves adding an “else”<br />
part that recognizes that full interpretation depends on the<br />
lower-level goals. For example, if the functionality was not<br />
increased by 5 percent, perhaps the strategy associated<br />
with Goal 2 was not effective. The interpretation model becomes<br />
increasingly detailed, with more conditional logic,<br />
at each lower level in the overall GQM + Strategies model.<br />
The organization must decide to develop and carry out a<br />
strategy for accomplishing a software goal. The strategy for<br />
Goal 2 in Figure 2 is to adopt an approach such as rating the<br />
importance of different requirements, as in the MoSCoW<br />
prioritization approach 10 for requirements and release planning,<br />
and to adopt the Constructive Cost Model (Cocomo) 11<br />
for cost estimation. The user must explicitly document an<br />
COMPUTER<br />
important context factor relevant to this strategy:<br />
Someone with expertise in the MoSCoW approach<br />
(a consultant who recommends it) is available, but<br />
ABC has no staff with such experience.<br />
Three assumptions relevant to this strategy,<br />
which the user must also document, follow:<br />
The organization can estimate the percentage<br />
of functionality delivered, for example, by<br />
using a proxy such as additional lines of code<br />
delivered, number of function points delivered,<br />
or a formula based on an actual requirements<br />
count.<br />
The difficulty and importance of requirements<br />
are weighted in some way (hard, medium,<br />
easy) to provide input to the cost model.<br />
The backlog of customer-requested requirements<br />
continues to grow.<br />
As with the business goal, the software goal<br />
has an associated set of GQM structures that<br />
define how to evaluate the goal (G2 in Figure 2).<br />
In full GQM notation, G2 is<br />
Analyze each six-month release for the purpose<br />
of evaluation with respect to incorporation<br />
of 5 percent new functionality as compared to the<br />
previous release from the point of view of the Web<br />
services project manager in the context of the ABC<br />
organization.<br />
This goal leads to questions Q3 and Q4: How many new<br />
requirements of must (M) importance were included in<br />
each release? How much time elapsed between releases?<br />
The interpretation of this software goal’s achievement is<br />
If, at each six-month milestone, the growth in functionality<br />
of a release is 5 percent, then the level 2 goal is<br />
satisfied for this release; else, assumptions about MoSCoW<br />
are incorrect or we have not chosen the correct strategy.<br />
At this point, the user can also further refine the business<br />
goal’s interpretation. If the business goal is satisfied<br />
(ABC’s profit increased by 10 percent), but Goal 2 is not,<br />
then the assumptions are wrong. The delivery of a particular<br />
requirement alone might have caused the gain, for<br />
example.<br />
Project-specific goals<br />
The last goal level in Figure 2 consists of goals derived<br />
from the previous level’s strategy that apply to a particular<br />
software development group or project. In the sample<br />
application, Goal 3 is to apply the MoSCoW and Cocomo<br />
approaches effectively. The relevant development group<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
has developed a strategy for this goal that involves training<br />
personnel, acquiring tools that will assist in applying these<br />
methods, and piloting these methods on a single project. A<br />
relevant assumption is that training for these approaches<br />
can be targeted to a few specific individuals, so the impact<br />
of the training on cost and schedule is reasonable.<br />
The GQM graph at this level, only part of which is shown<br />
in Figure 2, involves evaluating the effectiveness of using<br />
MoSCoW and Cocomo and of the training and other tools.<br />
The GQM + Strategies user then uses these results to revisit<br />
the interpretation of higher-level goals. Some of the questions<br />
and metrics defined at the second level are reusable<br />
at subsequent levels—a benefit of basing GQM + Strategies<br />
on the GQM approach.<br />
SUPPORTING STRATEGIC MEASUREMENT<br />
In all cases, specifying a strategy for goal achievement<br />
creates explicit links among goals at the various levels, from<br />
business objectives to project operations, which is critical<br />
to strategic measurement. In the example, the highest-level<br />
goal was to increase profit, the next-level goal was to provide<br />
new functionality in short releases, and the lowest-level<br />
goal was to use specific application methods to achieve the<br />
previous level goals. The linking strategy specified that ABC<br />
will achieve its increased profit goal by providing customers<br />
with more functionality. Often such links are implicit, but<br />
making them explicit has many benefits.<br />
Templates<br />
Templates also support strategic measurement by guiding<br />
users in defining all goal types at the necessary detail<br />
level. In the example, the full template for the business<br />
goal partially described in Figure 3 includes more extensive<br />
information about the target increase in income,<br />
the time frame, and any constraints or conflicting goals.<br />
GQM + Strategies includes templates for all goal types in the<br />
measurement model.<br />
Tracking assumptions<br />
Although the ABC example did not show it, our approach<br />
also builds in the ability to track context factors<br />
and assumptions at each level (through the requirement<br />
to document them along with all strategy documentation)<br />
so that users can more easily assess the effects of<br />
changes in either context or assumptions. In the example,<br />
the approach required that users document the assumption<br />
about the training required for MoSCoW and Cocomo<br />
so that, if the assumption turns out to be false, the model<br />
will indicate what elements the assumption affects and,<br />
consequently, what requires reevaluating.<br />
Interpretation models<br />
Interpretation models tie together measurement goals,<br />
context factors, assumptions, and data, thus making it<br />
easier to correctly and usefully interpret measurement<br />
results. This idea stems from the original GQM approach,<br />
but we have broadened it to allow interpretation models<br />
at each level to inform not only that level, but also higher<br />
levels as the data is aggregated and rolled up. In the ABC<br />
example, the results of applying the interpretation model<br />
at the lowest level will yield information about how the<br />
piloting of MoSCoW and Cocomo went, as well as information<br />
about the training and tools. The information from the<br />
lower level can help diagnose any problems encountered at<br />
the next level up. Further, the results of the interpretation<br />
at the second level can inform the analysis at the top level.<br />
At the top level, if profit does not increase as expected, the<br />
analytical results from the second level will help determine<br />
if the problem is due to higher costs, inadequate functionality<br />
delivered, late releases, or some other cause.<br />
Our approach explicitly links goals<br />
at different levels, from business<br />
objectives to project operations,<br />
which is critical to strategic<br />
measurement.<br />
Flexibility<br />
Our approach is flexible enough to accommodate other<br />
software measurement approaches and business strategy<br />
approaches. ABC might have used BSC to define its business<br />
goals and strategies and then used that description as<br />
a starting point for applying GQM + Strategies. PSM might<br />
have been useful later in applying our approach, when ABC<br />
needed to define the metrics.<br />
Shared measurement planning and experience<br />
Because all goal levels are linked, measurement planning<br />
and results are organization-wide rather than limited<br />
to a single project or department. Often the results are<br />
lower costs and better return on the investment in a measurement<br />
program, greater likelihood that the program<br />
will succeed, more effective risk identification and management,<br />
and greater compliance with software process<br />
improvement models such as CMMI.<br />
A substantial benefit is that sharing makes it more<br />
feasible to build a measurement experience base that<br />
can become a valuable corporate asset. Such a base can<br />
make project measurement and planning easier over time<br />
and consequently decrease project costs. It might begin<br />
with the set of generic experiences already available in<br />
GQM + Strategies and add value as the organization populates<br />
it with organization-specific models.<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
63
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
64<br />
RESEARCH FEATURE<br />
Any part of the ABC model in Figure 2 is reusable. The<br />
assumptions and context factors are particularly important<br />
because they capture the properties that might not<br />
hold when the organization reuses the model for a different<br />
situation. However, because the model requires the explicit<br />
capture of assumptions and context factors and links these<br />
to particular goals and strategies, the organization can<br />
clearly see which parts of the model need to be reevaluated<br />
when an assumption or context factor changes. The<br />
result is the flexibility to adapt goals and strategies to particular<br />
market needs and to analyze the consequences to<br />
the organization.<br />
APPLICATION SCENARIOS<br />
We have already taken steps to apply the GQM + Strategies<br />
approach in various industrial settings. Although our approach<br />
focuses on software development, it is finding<br />
equal utility in broader contexts, as the applications in<br />
Table 1 illustrate.<br />
A few studies are ongoing to get more insights into<br />
the deployment of GQM + Strategies. So far, most of the<br />
studies have reached the phase of initially setting up a<br />
GQM + Strategies grid, but they have not yet progressed to<br />
the point of using and maintaining it.<br />
The GQM + Strategies approach provides many<br />
features for organizations that want to create a<br />
software measurement program that is consistent<br />
with and contributes to the achievement of<br />
goals at all organizational levels. Our sample<br />
application illustrates the use of GQM + Strategies in a<br />
single context with three goal levels. Other situations<br />
might call for additional levels, but generally the process<br />
of capturing multilevel goals includes a business goal<br />
level, a set of lower-level goals, and a project-specific goal<br />
level. Each of these levels, in turn, can have multiple peer<br />
goals. Regardless of how many levels the organization<br />
COMPUTER<br />
Table 1. Ongoing applications of the GQM + Strategies approach.<br />
Business Domain Application<br />
European telecommunications<br />
company<br />
Telecommunications Drive strategic improvement programs, support paradigm<br />
shift toward purpose-driven metrics<br />
European automotive supplier Automotive Support CMMI’s Measurement and Analysis process area<br />
European network testing<br />
company<br />
International software<br />
company<br />
Telecommunications Evaluate cost, benefit, and schedule for modernizing<br />
existing product suite<br />
Embedded systems used in<br />
telecommunications<br />
Increase the visibility at all organizational levels of how<br />
strategic decisions impact operations<br />
Asian insurance company Information systems Align strategies and goals for new business domain<br />
Asian systems engineering<br />
organization<br />
Joint research project to<br />
develop a common software<br />
platform<br />
Safety-critical software for aerospace<br />
application<br />
Support of complex, dynamic business processes<br />
in a variety of domains, including logistics,<br />
retail, and customized industrial facilities<br />
Increase visibility of goals and strategies and derived<br />
measurement goals to enhance supplier collaboration<br />
Align project objectives and business objectives of involved<br />
research and industry partners<br />
requires, all levels must be based on well-defined goals,<br />
each with an associated strategy, documented context<br />
factors and assumptions, and a measurement and evaluation<br />
framework.<br />
The most important benefit of applying GQM + Strategies<br />
is the resulting transparency of measurement motivations<br />
and goals at different organizational levels, which makes<br />
it easier to identify goal relationships and conflicts and<br />
facilitates communication for organizational segments,<br />
such as marketing and software development. In the ABC<br />
example, without the GQM + Strategies model, project personnel<br />
might have misdirected their training efforts or<br />
chosen the wrong tools. The model helped project personnel<br />
understand why they were being asked to implement<br />
MoSCoW and Cocomo, which was likely to produce more<br />
focused training or tailoring. This is one of the many benefits<br />
of using our approach in a short development cycle.<br />
Acknowledgments<br />
GQM + Strategies is registered trademark No.<br />
302008021763 at the German Patent and Trade Mark<br />
Office; international registration number IR992843.<br />
References<br />
1. V. Basili, G. Caldiera, and D. Rombach, “Goal, Question,<br />
Metric Paradigm,” Encyclopedia of Software Engineering,<br />
vol. 1, J.J. Marciniak, ed., John Wiley & Sons, 1994, pp.<br />
528-532.<br />
2. V. Basili et al., “Bridging the Gap between Business Strategy<br />
and Software Development,” Proc. Int’l Conf. Information<br />
Systems, Association for Information Systems Electronic<br />
Library; http://aisel.aisnet.org/icis2007/25.<br />
3. R. Kaplan and D. Norton, “The Balanced Scorecard—Measures<br />
That Drive Performance,” Harvard Business Rev.,<br />
Jan.-Feb. 1992, p. 71.<br />
4. US Dept. of Defense and US Army, Practical Software and<br />
Systems Measurement: A Foundation for Objective Project<br />
Management, v. 4.0c, Mar. 2003; www.psmsc.com.<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
5. S.A. Becker and M.L. Bostelman, “Aligning Strategic and<br />
Project Measurement Systems,” IEEE Software, May/June<br />
1999, pp. 46-51.<br />
6. L. Buglione and A. Abran, “Balanced Scorecards and GQM:<br />
What Are the Differences?” Proc. 3rd European Software<br />
Measurement Conf., Federation of European Software Measurement<br />
Assoc., 2000, pp. 18-20.<br />
7. A.J. Bianchi, “Management Indicators Model to Evaluate<br />
Performance of IT Organizations,” Proc. Int’l Conf. Management<br />
of Engineering and Technology, vol. 2, IEEE Press,<br />
2001, pp. 217-229.<br />
8. D. Card, “Integrating Practical Software Measurement and<br />
the Balanced Scorecard,” Proc. 27th Ann. Int’l Computer<br />
Software and Applications Conf., IEEE CS Press, 2003, p.<br />
362.<br />
9. Sarbanes-Oxley Act of 2002, Public Law No. 107-204, 116<br />
Stat. 745, codified in sections of 11, 15, 18, 28, and 29 in<br />
US Code, 30 July 2002.<br />
10. D. Clegg and R. Barker, Case Method Fast-Track: A RAD<br />
Approach, Addison-Wesley Professional, 1994.<br />
11. B.W. Boehm et al., Software Cost Estimation with COCOMO<br />
II, Prentice Hall, 2000.<br />
Victor R. Basili is a professor in the Department of Computer<br />
Science at the University of Maryland and chief<br />
scientist of the Fraunhofer Center for Experimental<br />
Software Engineering. His research interests include measuring,<br />
evaluating, and improving the software process<br />
and product via empirical studies. Basili received a PhD in<br />
computer science from the University of Texas. Contact him<br />
at basili@fc-md.umd.edu.<br />
_______________<br />
Mikael Lindvall is a senior scientist and division director<br />
at the Fraunhofer Center for Experimental Software<br />
Engineering. His research interests include agile methods,<br />
software process improvement, software architectures, and<br />
experience and knowledge management. Lindvall received<br />
a PhD in computer science from Linköping University,<br />
Sweden. Contact him at mikli@fc-md.umd.edu.<br />
Myrna Regardie is a senior engineer at the Fraunhofer<br />
Center for Experimental Software Engineering. Her research<br />
interests include software process improvement,<br />
measurement, and project and knowledge management.<br />
Regardie received a BS in mathematics from Juniata College,<br />
Huntingdon, Pennsylvania. Contact her at ________<br />
mregardie@<br />
fc-md.umd.edu.<br />
___________<br />
Carolyn Seaman is an associate professor of information<br />
systems at the University of Maryland, Baltimore County,<br />
and a scientist at the Fraunhofer Center for Experimental<br />
Software Engineering. Her research interests include<br />
software evolution, management of software projects,<br />
and qualitative research methods in software engineering.<br />
Seaman received a PhD in computer science from the<br />
University of Maryland. Contact her at ___________<br />
cseaman@fc-md.<br />
umd.edu.<br />
______<br />
_______________<br />
Jens Heidrich is a department head at the Fraunhofer Institute<br />
for Experimental Software Engineering. His research<br />
interests include project management, quality assurance,<br />
and measurement. Heidrich received a PhD in computer<br />
science from the University of Kaiserslautern, Germany.<br />
Contact him at jens.heidrich@iese.fraunhofer.de.<br />
______________________<br />
Jürgen Münch is division manager for quality management<br />
at the Fraunhofer Institute for Experimental Software Engineering.<br />
His research interests include quality assurance,<br />
process management, and measurement. Münch received<br />
a PhD in computer science from the University of Kaiserslautern.<br />
Contact him at ______________________<br />
juergen.muench@iese.fraunhofer.<br />
__ de.<br />
Dieter Rombach is a professor and chair of the Software<br />
Engineering Department at the University of Kaiserslautern<br />
and executive director of the Fraunhofer Institute<br />
for Experimental Software Engineering. His research<br />
interests include software methodologies, modeling and<br />
measurement of the software process and resulting products,<br />
software reuse, and distributed systems. Rombach<br />
received a PhD in computer science from the University<br />
of Kaiserslautern. Contact him at _______________<br />
dieter.rombach@iese.<br />
fraunhofer.de.<br />
_________<br />
Adam Trendowicz is a researcher at the Fraunhofer Institute<br />
for Experimental Software Engineering. His research<br />
interests include software cost modeling, measurement,<br />
and process improvement. Trendowicz received a PhD in<br />
computer science from the University of Kaiserslautern.<br />
Contact him at adam.trendowicz@iese.fraunhofer.de.<br />
________________________<br />
Selected CS articles and columns are available for free at<br />
http://ComputingNow.computer.org.<br />
Join the<br />
IEEE<br />
Computer Society<br />
www.computer.org<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
65
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
66<br />
COMPUTER SOCIETY CONNECTION<br />
Ken Birman Wins<br />
Kanai Award<br />
Ken Birman<br />
is a founding<br />
member of<br />
TRUST, a<br />
consortium<br />
that explores<br />
challenges in trustworthy <strong>computing</strong>.<br />
Kenneth P. Birman, N.<br />
Rama Rao Professor<br />
at Cornell University,<br />
recently received the<br />
IEEE Computer Society’s 2009<br />
Tsutomu Kanai Award. The award<br />
recognizes major contributions to<br />
state-of-the art distributed <strong>computing</strong><br />
systems and their applications.<br />
Birman was recognized “for funda-<br />
COMPUTER<br />
mental and practical contributions<br />
to distributed <strong>computing</strong>, fault tolerance,<br />
reliability and distributed<br />
systems management.”<br />
Birman’s work has focused on the<br />
development of trustworthy distributed<br />
<strong>computing</strong> systems. Early in his<br />
career, he developed the Isis Toolkit, a<br />
reliable group communication system<br />
that introduced the virtual synchrony<br />
model for fault tolerance. The widely<br />
adopted Isis was at the core of such<br />
mission-critical systems as the<br />
French air traffic control system, the<br />
New York Stock Exchange, and the US<br />
Navy’s Aegis-class warships.<br />
Birman’s group subsequently<br />
developed a series of systems that<br />
explored challenges of extreme<br />
COMPUTING<br />
THEN<br />
Learn about <strong>computing</strong> history<br />
and the people who shaped it.<br />
http://<strong>computing</strong>now.<br />
computer.org/ct<br />
scale using gossip and peer-topeer<br />
protocols. These included<br />
Horus, Ensemble, Bimodal Multicast,<br />
the Astrolabe platform, and<br />
the Gossip Objects platform. Ideas<br />
and technology from these efforts<br />
have helped shape modern cloud<br />
<strong>computing</strong> systems, including<br />
the communication layer of IBM’s<br />
flagship WebSphere product, Microsoft’s<br />
cluster management platform,<br />
and Amazon’s data-center management<br />
systems.<br />
Birman became a Fellow of the<br />
ACM in 1998 and won the 2009<br />
IEEE Transactions on Parallel and<br />
Distributed Systems Outstanding<br />
Achievement Award.<br />
Tsutomu Kanai Award<br />
The Tsutomu Kanai Award was<br />
established in 1997 by an endowment<br />
from Hitachi in honor of its<br />
president. The award consists of<br />
a crystal model, certificate, and<br />
$10,000 honorarium. The IEEE<br />
Computer Society Awards Committee<br />
considers the seminal nature<br />
of the achievements, their practical<br />
impact, breadth, and depth, as<br />
well as the quality of the nomination.<br />
The awards honor technical<br />
achievements as well as service<br />
to the computer profession and to<br />
the Society. Birman will accept his<br />
award at the Computer Society’s<br />
2010 awards ceremony in Denver.<br />
The deadline to make a nomination<br />
for the 2010 Tsutomu Kanai<br />
Award is 15 October. For more information,<br />
visit www.computer.org/<br />
portal/web/awards/kanai.<br />
________________<br />
Published by the IEEE Computer Society 0018-9162/10/$26.00 © 2010 IEEE<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
Francine Berman Wins Kennedy Award<br />
Francine Berman<br />
was one of<br />
two founding<br />
principal<br />
investigators<br />
on the National<br />
Science<br />
Foundation’s TeraGrid Project.<br />
rancine Berman, vice<br />
president for research at<br />
Rensselaer Polytechnic<br />
Institute, recently received<br />
the IEEE Computer Society’s Ken<br />
Kennedy Award for outstanding<br />
contributions to programmability<br />
or productivity in high-performance<br />
<strong>computing</strong>. She is a pioneer in grid<br />
<strong>computing</strong> and a leading advocate<br />
for the development of a national<br />
cyberinfrastructure for the access,<br />
use, stewardship, and preservation<br />
of digital data. Berman’s work has<br />
had a major impact on the direction<br />
of computational science and<br />
the cyberinfrastructure. Her citation<br />
reads “For her influential leadership<br />
in the design, development and<br />
deployment of national-scale cyber<br />
infrastructure, her inspiring work<br />
as a teacher and mentor, and her<br />
exemplary service to the high-<br />
performance community.”<br />
Berman is co-chair of the Blue<br />
Ribbon Task Force on Sustainable<br />
Digital Preservation and Access,<br />
an international group focusing<br />
on the economic sustainability of<br />
digital information that must be<br />
accessed and preserved for many<br />
decades.<br />
In 2001, Berman became director<br />
of both the San Diego Supercomputer<br />
Center and the National Partnership<br />
for Advanced Computational Infrastructure,<br />
a consortium of more than<br />
40 national and international partners<br />
who worked together to create a<br />
comprehensive national <strong>computing</strong><br />
infrastructure.<br />
Berman is a founding member and<br />
co-chair of the Computing Research<br />
Association’s Committee on the Status<br />
of Women in Computing Research<br />
and currently serves on the Anita<br />
Borg Institute for Women and Technology<br />
Board of Trustees.<br />
Before moving to RPI, Berman<br />
held the High Performance Computing<br />
Endowed Chair in the<br />
Jacobs School of Engineering at<br />
the University of California, San<br />
Diego. In 2000, she was named an<br />
ACM Fellow for pioneering work in<br />
application scheduling for parallel<br />
distributed <strong>computing</strong>. Berman<br />
received a BA in mathematics from<br />
the University of California, Los<br />
Angeles, and an MA and PhD in<br />
Top Educators Honored<br />
he IEEE Computer Society<br />
sponsors an active<br />
and prestigious awards<br />
program as part of its<br />
mission to promote the free exchange<br />
of ideas among computer professionals<br />
around the world and to recognize<br />
its members for their outstanding<br />
accomplishments. Several noted<br />
educators recently received two<br />
Computer Society awards that honor<br />
achievement in education.<br />
COMPUTER SCIENCE<br />
& ENGINEERING<br />
UNDERGRADUATE<br />
TEACHING AWARD<br />
The IEEE Computer Society<br />
Computer Science & Engineering<br />
Undergraduate Teaching Award is<br />
presented each year for outstanding<br />
contributions to undergraduate education<br />
through teaching and service,<br />
for helping to maintain interest in<br />
the field, and for making a statement<br />
mathematics from the University<br />
of Washington.<br />
Ken Kennedy Award<br />
The IEEE Computer Society Ken<br />
Kennedy Award was established<br />
in memory of the founder of Rice<br />
University’s nationally ranked computer<br />
science program and one of<br />
the world’s foremost experts on<br />
high-performance <strong>computing</strong>. A certificate<br />
and $5,000 honorarium are<br />
awarded jointly by the ACM and the<br />
Computer Society for outstanding<br />
contributions to programmability<br />
or productivity in high-performance<br />
<strong>computing</strong> together with significant<br />
community service or mentoring<br />
contributions.<br />
about the importance with which<br />
the Society views undergraduate<br />
education.<br />
Judy Robertson<br />
Judy Robertson of Heriot-Watt University,<br />
the 2009 award winner, was<br />
honored “for outstanding contributions<br />
to the undergraduate education<br />
through teaching and the innovative<br />
use of pioneering technologies in<br />
teaching.” Robertson is the principal<br />
investigator of a grant funded by the<br />
UK’s Engineering and Physical Sciences<br />
Research Council that supports<br />
high school teachers who use gamemaking<br />
projects with their students.<br />
She received a BS and PhD in computer<br />
science and artificial intelligence<br />
from the University of Edinburgh.<br />
Elizabeth Burd<br />
Elizabeth Burd of Durham University,<br />
the 2008 winner, was recognized<br />
“for outstanding contributions to<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
67
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
68<br />
COMPUTER SOCIETY CONNECTION<br />
Microsoft and IEEE have announced<br />
a collaboration that aims to<br />
increase the number of students<br />
engaged in technical pursuits. The IEEE<br />
Computer Society, which has long<br />
očered its student members access to<br />
free Microsoft software, is participating<br />
in the collaboration.<br />
“As an information provider to technical<br />
professionals, this collaboration<br />
with Microsoft will give us an expanded<br />
ability to introduce students to more<br />
internships, scholarships, and contests,”<br />
said Violet Doan, the Computer Society’s<br />
membership director.<br />
“Engineers make tremendous contributions<br />
to society by creating technologies<br />
that drive global economic<br />
growth,” said Walid Abu-Hadba, vice<br />
president of developer and platform<br />
evangelism at Microsoft. “The Microsoft-IEEE<br />
collaboration will provide<br />
aspiring engineers around the world<br />
undergraduate education through<br />
teaching and the organization of<br />
programs to promote excellence in<br />
undergraduate teaching.” Burd is<br />
the leader of Durham’s Technology<br />
Enhanced Learning Research Group.<br />
Her most recent grant, supported by<br />
the Teaching and Learning Research<br />
Program, focuses on investigating<br />
the use of multitouch software in<br />
classrooms.<br />
Call for Papers | General Interest<br />
I<br />
EEE Micro seeks general-interest submissions<br />
for publication in upcoming issues. These<br />
works should discuss the design, performance,<br />
or application of microcomputer and microprocessor<br />
systems. Of special interest are articles on<br />
performance evaluation ion and<br />
workload character-<br />
COMPUTER<br />
MICROSOFT AND IEEE COOPERATE<br />
TO SUPPORT STUDENTS<br />
with tools and resources to convert their<br />
innovative thinking into marketplace<br />
innovation by equipping today’s technical<br />
students for tomorrow’s jobs.”<br />
Microsoft and IEEE will work together<br />
to provide IEEE student members<br />
with access to Microsoft servers,<br />
development tools, and eLearning,<br />
including privileged access to more<br />
than 300 software titles as part of the<br />
MSDN Academic Alliance, a subscription<br />
service traditionally available only<br />
through educational institutions. An<br />
added benećt is the opportunity for<br />
science, technology, engineering, and<br />
math students to explore job opportunities<br />
with Microsoft partners and<br />
customers through the Microsoft Students<br />
to Business program.<br />
Learn more about IEEE Computer Society<br />
student activities at www.computer.<br />
org/portal/web/studentactivities/<br />
____ home.<br />
TAYLOR L. BOOTH<br />
AWARD<br />
Recipients of the Taylor L. Booth<br />
Award are presented with a bronze<br />
medal and $5,000 honorarium in<br />
recognition of an outstanding record<br />
in computer science and engineering<br />
education. A successful candidate<br />
must meet at least two of the following<br />
criteria in the computer science<br />
and engineering field:<br />
ization. Summaries of work in progress and descriptions<br />
of recently completed works are most<br />
welcome, as are tutorials. Micro does not accept<br />
previously published material.<br />
Check our author center (www.computer.org/mc/<br />
_________<br />
mi cro/author.htm) for word, fi gure, and reference<br />
limits. All submissions pass through peer review<br />
co consistent istent with<br />
other professional-level technical<br />
pu publications, ublications, and eediting<br />
for clarity, readability, and<br />
co conciseness. Contac Contact IEEE Micro at _____ micro-ma@<br />
computer.org with aany<br />
questions.<br />
Achieving recognition as a<br />
teacher of renown.<br />
Writing an influential text.<br />
Leading, inspiring, or providing<br />
significant education content<br />
during the creation of a curriculum<br />
in the field.<br />
Inspiring others to a career in<br />
computer science and engineering<br />
education.<br />
Michael Heath<br />
Michael Heath, chair of computer<br />
science at the University of Illinois<br />
at Urbana-Champaign, was selected<br />
in 2009 “for contributions to computational<br />
science and engineering<br />
education, curriculum and scholarship.”<br />
Heath is director of both the<br />
computational science and engineering<br />
program and the Center for<br />
Simulation of Advanced Rockets at<br />
UIUC. He was named an ACM Fellow<br />
in 2000.<br />
James P. Cohoon<br />
and Jack W. Davidson<br />
James P. Cohoon and Jack W.<br />
Davidson of the University of<br />
Virginia were recognized as winners<br />
in 2008 “for sustained effort<br />
to transform introductory computer<br />
science education through<br />
lab-based multimedia pedagogy<br />
coupled with examples that attract<br />
a diverse student body.” Cohoon’s<br />
research involves algorithms, probabilistic<br />
search, genetic algorithms,<br />
simulated annealing, and diversity<br />
in computer science education.<br />
Davidson performs research in<br />
programming languages, computer<br />
security, embedded systems, and<br />
computer architecture.<br />
Taylor L. Booth founded the<br />
University of Connecticut’s<br />
Booth Engineering Center<br />
for Advanced Technology and was a<br />
candidate for IEEE Computer Society<br />
president at the time of his death in<br />
1986. For more information on Computer<br />
Society awards, visit ____<br />
www.<br />
computer.org/portal/web/awards.<br />
______________________<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
CALL AND CALENDAR<br />
CALLS FOR ARTICLES FOR<br />
IEEE CS PUBLICATIONS<br />
IEEE Micro seeks contributions<br />
on a wide range of topics related to<br />
multicore processing for a September/<br />
October 2010 special issue on European<br />
multicore processing projects.<br />
Suitable topics include advancements<br />
in multicore architecture, interconnection<br />
networks, and design-space<br />
exploration.<br />
Articles are due by 19 April.<br />
Visit www.computer.org/portal/web/<br />
________________<br />
<strong>computing</strong>now/micfp5 to view the<br />
complete call for papers.<br />
IT Professional seeks papers for a<br />
January/February 2011 issue focusing<br />
on green IT.<br />
Green IT is, and will continue to<br />
be, a hot topic due to increasing<br />
awareness of the harmful effects of<br />
green gas emissions, new stringent<br />
environmental legislation, rising concern<br />
about electronic waste disposal<br />
practices that damage the environment,<br />
and corporate-image concerns<br />
that are pushing businesses and individuals<br />
to adopt green practices.<br />
Articles are due by 1 July. Visit<br />
www.computer.org/portal/web/<br />
_______________<br />
<strong>computing</strong>now/itcfp1 to view the<br />
complete call for papers.<br />
CALLS FOR PAPERS<br />
ICEBE 2010, IEEE Int’l Conf. on<br />
e-Business Eng., 20-22 October,<br />
Shanghai; papers due 20 April; ____<br />
http://<br />
conferences.computer.org/icebe/2010/<br />
cfp.htm<br />
____<br />
CW 2010, Int’l Conf. on Cyberworlds,<br />
20-22 October, Singapore; papers due<br />
30 April; ________________<br />
www3.ntu.edu.sg/SCE/<br />
cw2010/cfp.htm<br />
___________<br />
0018-9162/10/$26.00 © 2010 IEEE<br />
CALENDAR<br />
MAY<br />
2-3 May: VG 2010, IEEE/EG Int’l<br />
Symp. on Volume Graphics, Norrkoping,<br />
Sweden; www.eurographics2010.<br />
se/vg2010<br />
_______<br />
3-6 May: ASYNC 2010, IEEE Int’l<br />
Symp. on Asynchronous Circuits<br />
and Systems, Grenoble, France; ____ http://<br />
asyncsymposium.org/async2010<br />
17-20 May: CCGrid 2010, IEEE Int’l<br />
Symp. on Cluster Computing and<br />
the Grid, Southbank, Australia; ____ www.<br />
manjrasoft.com/ccgrid2010<br />
28-31 May: CSO 2010, 3rd Int’l Joint<br />
Conf. on Computational Sciences<br />
and Optimization, Huangshan Mountain,<br />
China; www.gip.hk/cso2010<br />
JUNE<br />
9-11 Jun: EuroVis 2010, IEEE Eurographics<br />
Symp. on Visualization,<br />
Talence, France; www.eurovis.org<br />
9-12 Jun: CCC 2010, IEEE Int’l Conf.<br />
on Computational Complexity, Cambridge,<br />
Massachusetts; http://facweb.<br />
cs.depaul.edu/jrogers/complexity<br />
______________________<br />
SUBMISSION INSTRUCTIONS<br />
The Call and Calendar section lists conferences, symposia, and workshops that the IEEE<br />
Computer Society sponsors or cooperates in presenting.<br />
Visit www.computer.org/conferences for instructions on how to submit conference<br />
or call listings as well as a more complete listing of upcoming computer-related<br />
conferences.<br />
Published by the IEEE Computer Society<br />
28-30 Jun: WET ICE 2010, IEEE<br />
Int’l Workshops on Enabling<br />
Technologies: Infrastructures for<br />
Collaborative Enterprises, Larissa,<br />
Greece; http://wetice.org<br />
AUGUST<br />
17-19 Aug: MASCOTS 2010, Int’l<br />
Symp. on Modeling, Analysis and<br />
Simulation of Computer and Telecommunications<br />
Systems, Miami;<br />
http://mascots2010.cis.fiu.edu<br />
20-22 Aug: SocialCom 2010, IEEE Int’l<br />
Conf. on Social Computing, Bloomington,<br />
Minnesota; www.iisocialcom.<br />
org/conference/socialcom2010<br />
23-26 Aug: ICPR 2010, 20th Int’l<br />
Conf. on Pattern Recognition, Istanbul;<br />
www.icpr2010.org<br />
24-26 Aug: EMS 2010, Int’l Conf. on<br />
Eng. Management and Service Sciences,<br />
Wuhan, China; www.scirp.org/<br />
_________<br />
conf/ems2010<br />
SEPTEMBER<br />
12-18 Sep: ICSM 2010, Int’l Conf. on<br />
Software Maintenance, Timisoara,<br />
Romania; http://icsm2010.upt.ro<br />
20-24 Sep: Cluster 2010, IEEE Int’l<br />
Conf. on Cluster Computing, Heraklion,<br />
Crete; www.cluster2010.org<br />
OCTOBER<br />
3-8 Oct: MODELS 2010, IEEE Model-<br />
Driven Eng. Languages and Systems,<br />
Oslo, Norway; http://models2010.ifi.<br />
uio.no<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
____<br />
69
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
70<br />
COMPUTER<br />
CALL AND CALENDAR<br />
EVENTS IN 2010<br />
May<br />
2-3 ..........................VG 2010<br />
3-6 ......................ASYNC 2010<br />
17-20 ....................CCGrid 2010<br />
28-31 .......................CSO 2010<br />
June<br />
9-11 .................... EuroVis 2010<br />
9-12 ........................CCC 2010<br />
28-30 ..................WET ICE 2010<br />
August<br />
17-19 .................MASCOTS 2010<br />
20-22 . . . . . . . . . . . . . . . . SocialCom 2010<br />
23-26 ...................... ICPR 2010<br />
24-26 .......................EMS 2010<br />
20-22 Oct: CW 2010, Int’l Conf. on<br />
Cyberworlds, Singapore; _______<br />
www3.ntu.<br />
____________<br />
edu.sg/sce/cw2010<br />
20-22 Oct: ICEBE 2010, IEEE Int’l<br />
Conf. on e-Business Eng., Shanghai;<br />
http://conferences.computer.<br />
org/icebe<br />
2 Free Sample Issues!<br />
A $26 value<br />
The magazine of computational tools<br />
and methods for 21st century science.<br />
Cloud Computing<br />
Computational Astrophysics<br />
Computational Nanoscience<br />
Computational Engineering<br />
Geographical Information<br />
Systems<br />
http://cise.aip.org | www.computer.org/cise<br />
Send an e-mail to jbebee@aip.org to receive the two<br />
most recent issues of CiSE. (Please include your mailing address.)<br />
Recent Peer-Reviewed Topics:<br />
SC 2010<br />
stablished 21 years ago, the SC conference has built a community of participants<br />
E that includes researchers, scientists, <strong>computing</strong> center stač members, IT and data<br />
center managers, application developers, computer builders, program managers,<br />
journalists, and congressional stačers.<br />
The technical program addresses virtually every area of scientific and engineering<br />
research as well as technological development, innovation, and education. Its presentations,<br />
tutorials, panels, and discussion forums have contributed to breakthroughs in<br />
many new and innovative areas of <strong>computing</strong>.<br />
SC 2010 is sponsored by the IEEE Computer Society Technical Committee on Scalable<br />
Computing in cooperation with ACM SIGARCH. The conference takes place 13-19 November<br />
in New Orleans. Visit www.sc-conference.org for complete conference details.<br />
23-26 Oct: FOCS 2010, Symp. on<br />
Foundations of Computer Science,<br />
Las Vegas; http://theory.stanford.<br />
_________<br />
edu/focs2010/<br />
NOVEMBER<br />
1-3 Nov: SRDS 2010, IEEE Int’l Symp.<br />
on Reliable Distributed Systems,<br />
New Directions<br />
Petascale Computing<br />
Reproducible Research<br />
Software Engineering<br />
New Delhi, India; www.scs.ryerson.<br />
________________<br />
ca/iwoungan/SRDS2010<br />
13-19 Nov: SC 2010, Int’l Conf. for<br />
High-Performance Computing, Networking,<br />
Storage, and Analysis,<br />
New Orleans; www.sc-conference.<br />
org<br />
______________<br />
MEMBERS<br />
$47/year<br />
for print & online<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
___
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
PURPOSE: The IEEE Computer Society is the world’s largest<br />
association of <strong>computing</strong> professionals and is the leading<br />
provider of technical information in the field.<br />
MEMBERSHIP: Members receive the monthly magazine<br />
Computer, discounts, and opportunities to serve (all activities<br />
are led by volunteer members). Membership is open to all IEEE<br />
members, affiliate society members, and others interested in the<br />
computer field.<br />
COMPUTER SOCIETY WEB SITE: www.computer.org<br />
OMBUDSMAN: To check membership status or report a change<br />
of address, call the IEEE Member Services toll-free number,<br />
+1 800 678 4333 (US) or +1 732 981 0060 (international). Direct<br />
all other Computer Society-related questions—magazine delivery<br />
or unresolved complaints—to ____________<br />
help@computer.org.<br />
CHAPTERS: Regular and student chapters worldwide provide the<br />
opportunity to interact with colleagues, hear technical experts,<br />
and serve the local professional community.<br />
AVAILABLE INFORMATION: To obtain more information on any<br />
of the following, contact Customer Service at +1 714 821 8380 or<br />
+1 800 272 6657:<br />
Membership applications<br />
Publications catalog<br />
Draft standards and order forms<br />
Technical committee list<br />
Technical committee application<br />
Chapter start-up procedures<br />
Student scholarship information<br />
Volunteer leaders/staff directory<br />
IEEE senior member grade application (requires 10 years<br />
practice and significant performance in five of those 10)<br />
PUBLICATIONS AND ACTIVITIES<br />
Computer: The flagship publication of the IEEE Computer Society,<br />
Computer, publishes peer-reviewed technical content that<br />
covers all aspects of computer science, computer engineering,<br />
technology, and applications.<br />
Periodicals: The society publishes 13 magazines, 18 transactions,<br />
and one letters. Refer to membership application or request<br />
information as noted above.<br />
Conference Proceedings & Books: Conference Publishing<br />
Services publishes more than 175 titles every year. CS Press<br />
publishes books in partnership with John Wiley & Sons.<br />
Standards Working Groups: More than 150 groups produce<br />
IEEE standards used throughout the world.<br />
Technical Committees: TCs provide professional interaction in<br />
more than 45 technical areas and directly influence computer<br />
engineering conferences and publications.<br />
Conferences/Education: The society holds about 200<br />
conferences each year and sponsors many educational activities,<br />
including <strong>computing</strong> science accreditation.<br />
Certifications: The society offers two software developer<br />
credentials.<br />
For more information, visit www.computer.org/certification.<br />
revised 20 Jan. 2010<br />
EXECUTIVE COMMITTEE<br />
President: James D. Isaak*<br />
President-Elect: Sorel Reisman*<br />
Past President: Susan K. (Kathy) Land, CSDP*<br />
VP, Standards Activities: Roger U. Fujii (1st VP)*<br />
Secretary: Jeffrey M. Voas (2nd VP)*<br />
VP, Educational Activities: Elizabeth L. Burd*<br />
VP, Member & Geographic Activities: Sattupathu V. Sankaran†<br />
VP, Publications: David Alan Grier*<br />
VP, Professional Activities: James W. Moore*<br />
VP, Technical & Conference Activities: John W. Walz*<br />
Treasurer: Frank E. Ferrante*<br />
2010–2011 IEEE Division V Director: Michael R. Williams†<br />
2009–2010 IEEE Division VIII Director: Stephen L. Diamond†<br />
2010 IEEE Division VIII Director-Elect: Susan K. (Kathy) Land, CSDP*<br />
Computer Editor in Chief: Carl K. Chang†<br />
* voting member of the Board of Governors † nonvoting member of the Board of Governors<br />
BOARD OF GOVERNORS<br />
Term Expiring 2010: Piere Bourque; André Ivanov; Phillip A. Laplante;<br />
Itaru Mimura; Jon G. Rokne; Christina M. Schober; Ann E.K. Sobel<br />
Term Expiring 2011: Elisa Bertino, George V. Cybenko, Ann DeMarle,<br />
David S. Ebert, David A. Grier, Hironori Kasahara, Steven L. Tanimoto<br />
Term Expiring 2012: Elizabeth L. Burd, Thomas M. Conte, Frank E.<br />
Ferrante, Jean-Luc Gaudiot, Luis Kun, James W. Moore, John W. Walz<br />
EXECUTIVE STAFF<br />
Executive Director: Angela R. Burgess<br />
Associate Executive Director; Director, Governance: Anne Marie Kelly<br />
Director, Finance & Accounting: John Miller<br />
Director, Information Technology & Services: Carl Scott<br />
Director, Membership Development: Violet S. Doan<br />
Director, Products & Services: Evan Butterfield<br />
Director, Sales & Marketing: Dick Price<br />
COMPUTER SOCIETY OFFICES<br />
Washington, D.C.: 2001 L St., Ste. 700, Washington, D.C. 20036<br />
Phone:<br />
Email: ____________<br />
hq.ofc@computer.org<br />
Los Alamitos: 10662 Los Vaqueros Circle, Los Alamitos, CA 90720-1314<br />
Phone: +1 714 821 8380<br />
Email: ___________<br />
help@computer.org<br />
Membership & Publication Orders:<br />
Phone:<br />
Email: ___________<br />
help@computer.org<br />
Asia/Pacific: Watanabe Building, 1-4-2 Minami-Aoyama,<br />
Minato-ku, Tokyo 107-0062, Japan<br />
Phone:<br />
Email: _____________<br />
tokyo.ofc@computer.org<br />
IEEE OFFICERS<br />
President: Pedro A. Ray<br />
President-Elect: Moshe Kam<br />
Past President: John R. Vig<br />
Secretary: David G. Green<br />
Treasurer: Peter W. Staecker<br />
President, Standards Association Board of Governors:<br />
W. Charlston Adams<br />
VP, Educational Activities: Tariq S. Durrani<br />
VP, Membership & Geographic Activities: Barry L. Shoop<br />
VP, Publication Services & Products: Jon G. Rokne<br />
VP, Technical Activities: Roger D. Pollard<br />
IEEE Division V Director: Michael R. Williams<br />
IEEE Division VIII Director: Stephen L. Diamond<br />
President, IEEE-USA: Evelyn H. Hirt<br />
Next Board Meeting:<br />
11 June 2010, Denver, CO, USA<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
72<br />
CAREER OPPORTUNITIES<br />
SOFTWARE ENGINEER: High Performance<br />
Computing, Maxeler Technologies.<br />
Maxeler Technologies provides<br />
software and hardware systems which<br />
accelerate high performance scientific<br />
<strong>computing</strong> applications by an order of<br />
magnitude. Tier 1 companies currently<br />
use Maxeler consulting and hardware<br />
solutions to gain a competitive advantage.<br />
We’re currently seeking software<br />
engineers with experience of high performance<br />
software development (C/<br />
C++/Java/FORTRAN) for positions based<br />
in London. See http://www.maxeler.<br />
com/careers/ for more information or to<br />
apply.<br />
HEWLETT-PACKARD COMPANY has an<br />
opportunity for the following position in<br />
Cupertino, CA. PPM Developer: Reqs exp<br />
with: HP Project & Portfolio Mgmt s/w<br />
with the following modules: Demand<br />
Mgmt, Project Mgmt, Program Mgmt,<br />
Resources Mgmt, Finance Mgmt, Change<br />
Mgmt;Oracle PL/SQL; Shell Scripting;<br />
Process design; Organization change<br />
mgmt. Also requires Bachelors degree in<br />
CS, CE or rel field of study and 4 yrs. exp<br />
in job offered or rel. Send resume & refer<br />
to Job#CUPAHO2.: Please send resumes<br />
COMPUTER<br />
with job number to Hewlett-Packard<br />
Company, 19483 Pruneridge Ave., MS<br />
4206, Cupertino, CA 95014. No phone<br />
calls please. Must be legally authorized<br />
to work in the U.S. without sponsorship.<br />
EOE.<br />
PROJECT MANAGER, Senior Solutions<br />
Architect New York, NY. Utilize knowl. of<br />
complete SDLC & OO, JSF & Struts. Concepts<br />
to lead & participate in the design,<br />
development & maint. of complex software<br />
systems. Design & develop Java/<br />
J2EE/SOA applicatns using RSA, WID &<br />
WPS, BPEL, BPM, Webservices, SOAP/<br />
JMS. Familiar w/Datapower SOA Appliance.<br />
BS/MS-Engineering or foreign<br />
equivalent + related exp. Resumes: UTC<br />
Associates, Inc., 80 Wall St, Suite 1118,<br />
NY, NY 10005.<br />
HP ENTERPRISE SERVICES, LLC is accepting<br />
resumes for the following position<br />
in Oklahoma City, OK: Services<br />
Information Developer (Ref. #HPESOCF-<br />
WA1). SW design, develop, implementation,<br />
consulting & testing. Project requirement<br />
analysis. Requires Master’s<br />
or foreign degree equivalent in Comp<br />
NEW TENURE TRACK FACULTY POSITION<br />
IN THE SCHOOL OF SYSTEMS AND ENTERPRISES<br />
AT STEVENS INSTITUTE OF TECHNOLOGY<br />
Faculty Position in Software Engineering<br />
The School of Systems and Enterprises at Stevens Institute of Technology invites applications<br />
for a full-time, tenure-track faculty position in Software Engineering. We are especially interested<br />
in candidates with research interests in modeling, simulation and visualization of complex<br />
systems; and synergies with systems engineering and security systems engineering. The<br />
successful candidate will have the ability to develop an innovative and impactful research<br />
program in this area. Furthermore, an enthusiasm for teaching and conducting collaborative<br />
research is essential.<br />
An application, formatted as a single .pdf file, should include the candidate’s curriculum<br />
vitae, a statement of research interest, a statement of teaching interest, three scientific manuscripts,<br />
and up to 5 references.<br />
This appointment will be at the Associate or Assistant Professor Rank, dependent on scholarly<br />
achievement and accomplishments. Applications should be submitted to:<br />
Jon Wade, Ph.D., Professor and Associate Dean of Research<br />
School of Systems and Enterprises, Stevens Institute of Technology<br />
1 Castle Point on Hudson, Hoboken, NJ 07030<br />
Email: jon.wade@stevens.edu Tel: 775.636.5811<br />
_____________<br />
This position will remain open until filled. Screening of candidates will start in<br />
April 2010. Stevens Institute of Technology is an equal opportunity/affirmative<br />
action employer and is dedicated to recruiting a diverse faculty community.<br />
We welcome all qualified applicants to apply, including women, minorities,<br />
veterans, and individuals with disabilities.<br />
www.stevens.edu/sse<br />
Cisco Systems, Inc. is accepting resumes for<br />
the following position:<br />
Richfield, OH<br />
Software Engineer<br />
(Ref#: RICH1)<br />
Responsible for the definition, design, development,<br />
test, debugging, release, enhancement<br />
and maintenance of networking software.<br />
Please mail resumes with reference number to<br />
Cisco Systems, Inc., Attn: J51W, 170 W. Tasman<br />
Drive, Mail Stop: SJC 5/1/4, San Jose, CA 95134.<br />
No phone calls please. Must be legally<br />
authorized to work in the U.S. without sponsorship.<br />
EOE.<br />
www.cisco.com<br />
Cisco Systems, Inc. is accepting resumes for<br />
the following position:<br />
Malvern, PA<br />
Solution Consultant<br />
(Ref#: MAL1)<br />
Provide specific solution, technology, and<br />
product consulting for software product.<br />
Please mail resumes with reference number<br />
to Cisco Systems, Inc., Attn: J51W, 170 W.<br />
Tasman Drive, Mail Stop: SJC 5/1/4, San Jose,<br />
CA 95134. No phone calls please. Must be<br />
legally authorized to work in the U.S. without<br />
sponsorship. EOE.<br />
www.cisco.com<br />
Published by the IEEE Computer Society 0018-9162/10/$26.00 © 2010 IEEE<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
Sci, Comp Eng, Electrical Eng, or related<br />
field + 4 yrs of exp in job offered, or as<br />
a programmer analyst, engineer, developer,<br />
or related occupation. Oracle SQL;<br />
Javascript; SOAP/Web Services; XML;<br />
AJAX; ASP.NET; C#. Please mail resumes<br />
with reference # to: Ref. # HPESOCF-<br />
WA1, Hewlett-Packard Company; 19483<br />
Pruneridge Avenue, MS 4206, Cupertino,<br />
CA 95014. No phone calls. Must be legally<br />
authorized to work in the U.S. without<br />
sponsorship. EOE.<br />
TECHNICAL CONSULTANT (Milpitas,<br />
CA) Provide prof’l computer consulting<br />
svcs in form of systems analysis, dsgn &<br />
dvlpmt, systems integration &/or testing<br />
consulting. Min req MS in Comp Sci.<br />
Resume: HR, GSPANN Technologies, Inc,<br />
362 Fairview Way, Milpitas, CA 95035.<br />
HEWLETT-PACKARD COMPANY is accepting<br />
resumes for a Software Designer<br />
in Vancouver, WA. (Ref. #VANSWD11).<br />
Design, develop, maintain, test, and provide<br />
quality/performance assurance of<br />
embedded software for enterprise class<br />
print and finishing devices. Mail resumes<br />
with reference # to: Ref. #VANSWD11,<br />
Hewlett-Packard Company, 19483<br />
Pruneridge Avenue, MS 4206, Cupertino,<br />
CA 95014. No phone calls please. Must<br />
be legally authorized to work in the U.S.<br />
without sponsorship. EOE.<br />
ADJILITY CONSULTING in Short Hills,<br />
NJ seeks Documentum Systems Engineer<br />
for Documentum imaging systems<br />
including configuration & issue troubleshooting<br />
& configuring application for<br />
system optimizations. Req Bachelor’s &<br />
5 yrs exp with EMC Documentum Content<br />
Server, EMC Documentum Captiva,<br />
EMC Documentum .Net & Java development,<br />
2 yrs exp with Windows platforms<br />
& Unix platforms, working knowledge of<br />
infrastructure topics and EMC Documentum<br />
System Administrator certification.<br />
Requires up to 100% travel to client locations<br />
w/in U.S. Email resume to _____<br />
38.adjil-<br />
___________<br />
ity@hiredesk.com.<br />
.NET DEVELOPER - Dsgn, dvlp, test<br />
& implmt applic s/w utilizing knowl of<br />
& exp w/ .NET 2.0/3.0/3.5, C#, VB.NET,<br />
AJAX, Classic ASP, VB 6, C++, IIS, Oracle<br />
8i/9i, SQL Server 2000/2005/2008,<br />
Java, Tomcat, JavaScript, Web Services,<br />
Cisco Systems, Inc. is accepting resumes for the following<br />
positions in San Jose/Milpitas/Santa Clara, CA<br />
IT Analyst (Ref#: SJ6)<br />
Responsible for evaluating and documenting business needs, recommending<br />
business process and Information Technology solution alternatives and<br />
coordinating delivery of technical solutions to clients.<br />
Network Consulting Engineer (Ref#: SJ9)<br />
Responsible for the support and delivery of Advanced Services to company’s<br />
major accounts.<br />
Manager, Advanced Services (Ref#: SJ52)<br />
Supervise the activities of a technical team with responsibility for results in<br />
terms of customer satisfaction and delivery assurance.<br />
Please mail resumes with reference number to Cisco Systems, Inc., Attn: J51W, 170<br />
W. Tasman Drive, Mail Stop: SJC 5/1/4, San Jose, CA 95134. No phone calls please.<br />
Must be legally authorized to work in the U.S. without sponsorship. EOE.<br />
www.cisco.com<br />
Georgia State University<br />
Department of Computer Science<br />
The Department of Computer Science of Georgia<br />
State University invites applications for an anticipated<br />
tenure-track position for Assistant or Associate<br />
Professor beginning the Fall semester, 2010,<br />
pending budgetary approval. Earned Ph.D. in Computer<br />
Science, or a closely related discipline, and<br />
excellent records of publications and funding are<br />
required. Preference is for individual with specialty<br />
in distributed systems and networking. An offer<br />
of employment will be conditional on background<br />
verification.<br />
Applicants should send: letter of interest, C.V. without<br />
birth date, but with citizenship status, and three<br />
letters of recommendation and transcripts of all<br />
graduate work to:<br />
Dr. Yi Pan, Chair<br />
Department of Computer Science<br />
Georgia State University<br />
34 Peachtree Street, Suite 1450<br />
Atlanta, Georgia, 30303<br />
Applications can also be sent via email to ___ pan@<br />
______ cs.gsu.edu and will be accepted until position is<br />
filled.<br />
Georgia State University, a Research University of<br />
the University System of Georgia, is an AA/EEO<br />
employer.<br />
Assistant Professor –<br />
Computer Engineering<br />
University of Pittsburgh<br />
The Department of Electrical and Computer Engineering<br />
(ECE) at the University of Pittsburgh<br />
(http://www.engr.pitt.edu/electrical/about/jobs.<br />
___ html) is searching for a tenure stream assistant<br />
professor in the area of Computer Engineering.<br />
The start date for this position is approximately<br />
Sept. 1, 2010. The preferred candidate will fill a<br />
core need in the area of “Computer Engineering,”<br />
with a demonstrated research focus is on one of the<br />
following Swanson School of Engineering Focus<br />
Areas: “Energy,” “Bioengineering,” “Manufacturing”<br />
(including RFID), “Sustainability,” or “Nanoscience<br />
and Engineering.” ECE partners with the<br />
Department of Computer Science to offer BS, MS<br />
and PhD degrees in Computer Engineering.<br />
To ensure full consideration, applications must be<br />
received by April 15, 2010, although later applications<br />
may be considered if time allows. Please<br />
send a resume (or CV), contact information for at<br />
least four references, plus a letter summarizing your<br />
teaching and research interests to:<br />
Chair, ECE Search Committee<br />
348 Benedum Engineering Hall,<br />
University of Pittsburgh<br />
Pittsburgh, PA 15261<br />
or alternatively to: __________<br />
eesearch@pitt.edu<br />
The University of Pittsburgh is an affirmative action,<br />
equal opportunity employer.<br />
APRIL 2010 73<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
74<br />
CAREER OPPORTUNITIES<br />
Cisco Systems, Inc. is accepting resumes for<br />
the following position:<br />
San Bruno/San Francisco, CA<br />
Quality Assurance<br />
Engineer<br />
(Ref#: SBR4)<br />
Responsible for all aspects of Quality Assurance<br />
and testing for multiple projects.<br />
Please mail resumes with reference number to<br />
Cisco Systems, Inc., Attn: J51W, 170 W. Tasman<br />
Drive, Mail Stop: SJC 5/1/4, San Jose, CA 95134.<br />
No phone calls please. Must be legally<br />
authorized to work in the U.S. without sponsorship.<br />
EOE.<br />
www.cisco.com<br />
Advertiser Page<br />
APC 1<br />
Cisco 72-75<br />
Georgia State University 73<br />
IEEE Computer Society CV3, CV4<br />
ISADS 2011 12<br />
Stevens Institute of Technology 72<br />
University of Massachusetts 9<br />
University of Pittsbrugh 73<br />
Classified Advertising 72-75<br />
Advertising Personnel<br />
Marion Delaney<br />
IEEE Media, Advertising Dir.<br />
Phone: +1 415 863 4717<br />
Email: ____________<br />
md.ieeemedia@ieee.org<br />
Marian Anderson<br />
Sr. Advertising Coordinator<br />
Phone: +1 714 821 8380<br />
Fax: +1 714 821 4010<br />
Email: ______________<br />
manderson@computer.org<br />
Sandy Brown<br />
Sr. Business Development Mgr.<br />
Phone: +1 714 821 8380<br />
Fax: +1 714 821 4010<br />
Email: ____________<br />
sb.ieeemedia@ieee.org<br />
COMPUTER<br />
Entrust Truepass, Red Dot, PVCS, Win-<br />
Runner; Req MS Comp Sci, Eng or rel.<br />
Mail resumes to HR-National Computer<br />
Systems, 6-70 Towne Center Dr , North<br />
Brunswick, NJ 08902.<br />
HEWLETT-PACKARD COMPANY has an<br />
opportunity for the following position in<br />
Houston, TX. Engineering Project Manager:<br />
Reqs: Ability to use lab equipmt<br />
incl Oscilloscopes, DMMS (Digital Multimeters),<br />
Pwr Meters, Gain/Phase analyzers.<br />
Exp. w/impedance analyzers; Data<br />
acquisition systms. Also requires Bachelors<br />
degree in Elec. Engrng, or rel field<br />
of study and 3 yrs. exp in job offered or<br />
rel. Send resume & refer to Job# HOUK-<br />
MI2.: Please send resumes with job number<br />
to Hewlett-Packard Company, 19483<br />
Pruneridge Ave., MS 4206, Cupertino,<br />
CA 95014. No phone calls please. Must<br />
be legally authorized to work in the U.S.<br />
without sponsorship. EOE.<br />
HEWLETT-PACKARD COMPANY has an<br />
opportunity for the following position<br />
in Houston, TX. Systems/Software Engineer:<br />
Reqs: 7yrs s/w dvlpmt exp on Linux<br />
&/or UNIX; C/C++; SCSI, SES and SAS; FC,<br />
SATA & RAID storage; SMI-S & CIM; SM-<br />
BIOS & IPMI; UNIX make, shell scripts &<br />
Perl; version cntrl systems; OOAD, design<br />
COMPUTER<br />
Advertising Sales<br />
Representatives<br />
Recruitment:<br />
Mid Atlantic<br />
Lisa Rinaldo<br />
Phone: +1 732 772 0160<br />
Fax: +1 732 772 0164<br />
Email: _______<br />
lr.ieeemedia@<br />
ieee.org<br />
New England<br />
John Restchack<br />
Phone: +1 212 419 7578<br />
Fax: +1 212 419 7589<br />
Email: ______<br />
j.restchack@<br />
ieee.org<br />
Southeast<br />
Thomas M. Flynn<br />
Phone: +1 770 645 2944<br />
Fax: +1 770 993 4423<br />
Email: _____ flynntom@<br />
mindspring.com<br />
Midwest/Southwest<br />
Darcy Giovingo<br />
Phone: +1 847 498 4520<br />
Fax: +1 847 498 5911<br />
Email: _______<br />
dg.ieeemedia@<br />
ieee.org<br />
Northwest/Southern CA<br />
Tim Matteson<br />
Phone: +1 310 836 4064<br />
Fax: +1 310 836 4067<br />
Email: _______<br />
tm.ieeemedia@<br />
ieee.org<br />
Japan<br />
Tim Matteson<br />
Phone: +1 310 836 4064<br />
Fax: +1 310 836 4067<br />
Email: _______<br />
tm.ieeemedia@<br />
ieee.org<br />
Europe<br />
Heleen Vodegel<br />
Phone: +44 1875 825700<br />
Fax: +44 1875 825701<br />
Email: _____ impress@<br />
impressmedia.com<br />
patterns & UML; HP-UX internals; SOAP/<br />
XML; multi-threaded applctns; Java;<br />
storage bnchmrkng tools. Also requires<br />
Bach degree in CS, CE or rel & 7 yrs exp<br />
in job offered or rel. Send resume & refer<br />
to Job #HOUPPU2. Please send resumes<br />
with job number to Hewlett-Packard<br />
Company, 19483 Pruneridge Ave., MS<br />
4206, Cupertino, CA 95014. No phone<br />
calls please. Must be legally authorized<br />
to work in the U.S. without sponsorship.<br />
EOE.<br />
HP ENTERPRISE SERVICES, LLC is accepting<br />
resumes for the following positions:<br />
TECHNOLOGY CONSULTANT IN<br />
FARMINGTON HILLS, MI. (Ref. #HPESF-<br />
HVPA1). Create & implement standard<br />
deployment image for using Windows<br />
XP & Windows 7. Script solutions, independent<br />
of deployment tools used, to<br />
deploy standard image across globe.<br />
Requires Master’s or foreign degree<br />
equiv. in Electrical Engg, Comp Engg,<br />
Comp Sci, or related + 2 yrs experience<br />
in job offered, or as programmer analyst,<br />
intern, or related. Hewlett Packard<br />
Configuration Automation Enterprise;<br />
Visual Basic Scripting; Microsoft Windows<br />
Image Mgmt; Microsoft Windows<br />
Software Distribution; Microsoft Active<br />
<strong>Directory</strong>.<br />
Product:<br />
US East<br />
Dawn Becker<br />
Phone: +1 732 772 0160<br />
Fax: +1 732 772 0164<br />
Email: _______<br />
db.ieeemedia@<br />
ieee.org<br />
US Central<br />
Darcy Giovingo<br />
Phone: +1 847 498 4520<br />
Fax: +1 847 498 5911<br />
Email: ___________<br />
dg.ieeemedia@ieee.org<br />
US West<br />
Lynne Stickrod<br />
Phone: +1 415 931 9782<br />
Fax: +1 415 931 9782<br />
Email: ___________<br />
ls.ieeemedia@ieee.org<br />
Europe<br />
Sven Anacker<br />
Phone: +49 202 27169 11<br />
Fax: +49 202 27169 20<br />
Email: _____ sanacker@<br />
__________<br />
intermediapartners.de<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
BUSINESS CONSULTANT IN GREENS-<br />
BURG, PA. (Ref. #HPESSCH1). Interact<br />
with client face to face on daily basis. Innovate<br />
& formulate business solutions &<br />
“technology enabled” business models<br />
& new ways of doing business to create<br />
breakthrough positions in marketplace.<br />
Master’s or foreign degree equiv. in<br />
Comp. Sci, Comp. Engg., Electrical Engg,<br />
or related + 2 yrs of exp in job offered,<br />
or as SW consultant, SW engineer, or related.<br />
SAP Project Mgmt; SAP ABAP; SAP<br />
Netweaver XI; SAP EDI / ALE / IDOCS; SAP<br />
Scripts – Smartforms; SAP Workflow.<br />
Please mail resumes with reference #<br />
to: Ref. #, HP Enterprise Services; 19483,<br />
Pruneridge Avenue, MS 4206, 95014.<br />
No phone calls please. Must be legally<br />
authorized to work in the U.S. without<br />
sponsorship. EOE.<br />
SR. DEVELOPER - eCommerce Industries,<br />
Inc. (ECI) has an opening in Big Sandy,<br />
TX for Sr. Developer. Position involves<br />
designing & developing complex software<br />
applications. Design, plan, develop,<br />
test & document accounting & office<br />
products software, applying knowledge<br />
of programming techniques & computer<br />
systems. Analyze user request for new<br />
or modified functions for our financial/<br />
accounting system analyze & develop<br />
specifications for the new design, to determine<br />
feasibility, cost & time required<br />
compatibility with the current system<br />
& computer capabilities. Consult with<br />
end users to identify current operating<br />
procedures & clarifying program objectives.<br />
Study relevant manuals, periodicals<br />
& technical reports to learn ways to develop<br />
software that meet user requirements.<br />
Formulate plans outlining steps<br />
required to develop programs, using<br />
structured analysis, designing & object<br />
oriented methodology. Prepare flowcharts<br />
& class diagrams to illustrate the<br />
sequence of steps a program must follow<br />
& describing the logical operations<br />
involved. Convert project specifications,<br />
using flowcharts & class diagrams into a<br />
sequence of detailed instructions & logical<br />
steps for coding into office product<br />
software language which is written in<br />
C++, JAVA, Windows, UNIX, LINUX, SQL<br />
Server, .Net, Visual Basic, SQL, Web appli-<br />
cations development networking. Code &<br />
software module design. Write documentation<br />
to describe program development,<br />
logic, coding & corrections & rectifying<br />
bugs. Develop understanding of the project<br />
scope & requirements & question any<br />
areas that are unclear. Identify potential<br />
problem areas in software design. Participate<br />
in training of new members of the<br />
department. Assist Customer Support<br />
& Technical Support in providing a customer<br />
response or assume responsibility<br />
for calls that have been escalated to Software<br />
Development. Requires Bachelor’s<br />
in Computer Science or CIS & 3 yrs exp. in<br />
JAVA programming OR Master’s in Computer<br />
Science or CIS & 1 year exp. in industry<br />
or as a graduate research assistant<br />
in JAVA programming. Submit your resume<br />
to ___________________<br />
developmentjobs@ecisolutions.<br />
___ com. An EOE.<br />
PROGRAMMER - eCommerce Industries,<br />
Inc. (ECI) has an opening in Fort<br />
Wayne, IN for Programmer. Position involves<br />
planning, developing, testing &<br />
documenting accounting & office products<br />
software, applying knowledge of<br />
programming techniques & computer<br />
systems. Analyzing user request for new<br />
or modified functions for our financial/<br />
accounting system to determine feasibility,<br />
cost & time required, compatibility<br />
with the current system & computer capabilities.<br />
Consulting with end users to<br />
identify current operating procedures &<br />
clarifying program objectives. Studying<br />
relevant manuals, periodicals & technical<br />
reports to learn ways to develop software<br />
that meet user requirements. Preparing<br />
flowcharts & class diagrams to illustrate<br />
sequence of steps a program must follow<br />
& describing logical operations involved.<br />
Converting project specifications into a<br />
sequence of detailed instructions & logical<br />
steps for coding into office product<br />
software language which is written in<br />
FoxPro & Microsoft .NET languages (C#,<br />
Visual Basic) using SQL server. Writing<br />
documentation to describe program development,<br />
logic, coding & corrections<br />
& rectifying bugs. Requires Bachelor’s<br />
in Computer Science or equivalent & 2<br />
yrs exp. in computer programming. Exp.<br />
to include Visual Basic & FoxPro. Submit<br />
your resume to _____________<br />
britdevjobs@ecisolutions.com.<br />
An EOE.<br />
______<br />
SUBMISSION DETAILS: Rates are $445.00 per column inch ($500 minimum).<br />
Eight lines per column inch and average five typeset words per line. Free<br />
online listing on careers.computer.org with print ad. Send copy at least one<br />
month prior to publication date to: Marian Anderson, Classified Advertising,<br />
Computer Magazine, 10662 Los Vaqueros Circle, Los Alamitos, CA 90720-1314;<br />
(714) 821-8380; fax (714) 821-4010. Email: _________________<br />
manderson@computer.org.<br />
Cisco Systems, Inc. is accepting resumes for<br />
the following position:<br />
San Bruno/San Francisco, CA<br />
Customer Support Engineer<br />
(Ref#: SBR2)<br />
Responsible for providing technical support<br />
regarding the company's proprietary systems<br />
and software.<br />
Please mail resumes with reference number<br />
to Cisco Systems, Inc., Attn: J51W, 170 W.<br />
Tasman Drive, Mail Stop: SJC 5/1/4, San Jose,<br />
CA 95134. No phone calls please. Must be<br />
legally authorized to work in the U.S.<br />
without sponsorship. EOE.<br />
www.cisco.com<br />
Cisco Systems, Inc. is accepting resumes for<br />
the following position:<br />
Boston, MA<br />
Systems Engineering Manager<br />
(Ref#: BOS1)<br />
Provide technical direction and business<br />
guidance to the regional sales team.<br />
Please mail resumes with reference number<br />
to Cisco Systems, Inc., Attn: J51W, 170 W.<br />
Tasman Drive, Mail Stop: SJC 5/1/4, San Jose,<br />
CA 95134. No phone calls please. Must be<br />
legally authorized to work in the U.S.<br />
without sponsorship. EOE.<br />
www.cisco.com<br />
APRIL 2010 75<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
76<br />
COMPUTER<br />
AI REDUX<br />
Probabilistic Analysis<br />
of an Ancient<br />
Undeciphered Script<br />
Rajesh P.N. Rao, University of Washington<br />
Probabilistic methods for analyzing sequences are providing<br />
new insights into the 4,000-year-old undeciphered script of the<br />
Indus civilization.<br />
In the latter half of the 19th<br />
century, railway workers in<br />
British India found an almost<br />
inexhaustible supply of precisely<br />
cut baked bricks at Harappa,<br />
a small town located in present-day<br />
Pakistan. They proceeded to use the<br />
bricks as ballast for laying down 100<br />
miles of railroad track. Little did they<br />
know that these bricks were more<br />
than 4,000 years old, products of<br />
South Asia’s oldest urban civilization.<br />
The Indus civilization, so named<br />
because its first important sites were<br />
discovered along the Indus River,<br />
flourished from 2600 to 1900 BC. At<br />
its peak, it encompassed more than<br />
1 million square kilometers and was<br />
larger than the roughly contemporaneous<br />
Egyptian and Mesopotamian<br />
civilizations. Its cities were laid out<br />
in a grid-like pattern with a sophisticated<br />
water management and<br />
drainage system that would be the<br />
envy of many towns today. Citizens<br />
of the Indus civilization were highly<br />
enterprising, traveling to lands as far<br />
away as the Persian Gulf and Mesopotamia<br />
(present-day Iraq) to trade.<br />
Remarkably, there is no evidence<br />
that powerful kings or elites ruled the<br />
Indus cities, as in other Bronze Age<br />
civilizations. No extravagant royal<br />
palaces, pyramids, or ziggurats have<br />
been found. What archaeologists<br />
have unearthed in large numbers are<br />
tiny seals like those shown in Figure<br />
1a, most around 1” × 1” in size. Each<br />
typically depicts an expertly crafted<br />
animal, with a short text of signs<br />
at the top. These texts, which also<br />
appear on miniature tablets, copper<br />
plates, tools, weapons, and pottery,<br />
constitute the Indus script, one of the<br />
last remaining undeciphered scripts<br />
of the ancient world.<br />
THE INDUS SCRIPT<br />
Figure 1b shows a small subset of<br />
the approximately 400 signs in the<br />
Indus script. The number of signs<br />
is more than in purely alphabetic<br />
or syllabic scripts, which typically<br />
contain a few dozen signs, but less<br />
than in logographic scripts such<br />
as Chinese, which contain large<br />
numbers of signs representing<br />
entire words. Researchers have<br />
therefore suggested that, like other<br />
ancient scripts such as Sumerian<br />
and Mayan, the Indus script was<br />
logosyllabic in nature, each sign<br />
representing either a word or a<br />
syllable.<br />
What the Indus signs actually<br />
mean remains a mystery, although<br />
the number of books claiming to have<br />
deciphered the script could occupy<br />
several bookshelves. None of these<br />
claims have been widely accepted.<br />
The major impediments to decipherment<br />
include<br />
the brevity of existing Indus<br />
texts—the average text length is<br />
about five signs while the longest<br />
text consists of 17 signs;<br />
our almost complete lack of<br />
knowledge of the language<br />
spoken by the Indus people; and<br />
the lack of a bilingual document<br />
such as the Rosetta Stone,<br />
which was instrumental in<br />
deciphering the Egyptian hieroglyphic<br />
script.<br />
Given such formidable obstacles,<br />
efforts to decipher the script have<br />
ranged from inspired guesswork to<br />
ideology-driven speculation.<br />
An alternate, more objective<br />
approach is to first analyze the script’s<br />
syntactic structure, in the hope that<br />
Published by the IEEE Computer Society 0018-9162/10/$26.00 © 2010 IEEE<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
such an analysis could eventually lead<br />
to decipherment. Are the symbols in<br />
Indus texts randomly ordered or do<br />
they follow specific rules? Do particular<br />
symbols have particular positions<br />
within texts? How much flexibility<br />
does the script allow when composing<br />
a string of symbols? How do the<br />
Indus script’s syntactical properties<br />
compare with those of other ancient<br />
and modern languages and scripts?<br />
Researchers are investigating such<br />
questions using statistics, probabilistic<br />
reasoning, and machine learning.<br />
EARLY STATISTICAL<br />
ANALYSIS<br />
G.R. Hunter conducted the first<br />
rudimentary statistical analysis of the<br />
Indus script in the early 1930s. In the<br />
absence of computers, Hunter handenumerated<br />
frequently occurring<br />
clusters of signs, segmenting Indus<br />
texts into short “words” of two or<br />
more signs. This enabled him to infer<br />
important syntactic characteristics<br />
of the script such as the tendency of<br />
certain symbols and words to occur<br />
at specific positions within texts. For<br />
example, Hunter was among the first<br />
to note that the “jar” sign , which is<br />
the most frequently occurring sign<br />
in the texts, acts as a “word ender,”<br />
and that the “fish” signs frequently<br />
occur in pairs (such as and ),<br />
occupying the same relative position<br />
within texts.<br />
In the 1960s, the fact that sign clusters<br />
have particular positions within<br />
Indus texts was confirmed independently<br />
with the help of computers by a<br />
Finnish team led by Asko Parpola and<br />
a Soviet team led by Yuri Knorozov<br />
(who played a key role in deciphering<br />
the Mayan script). More recent work<br />
has demonstrated that the frequency<br />
of certain two-, three-, and four-sign<br />
combinations is much higher than<br />
would be expected by chance, and<br />
that a majority of the texts longer<br />
than five signs can be segmented into<br />
these smaller, frequently occurring<br />
sign combinations (N. Yadav et al.,<br />
“Segmentation of Indus Texts,” Int’l<br />
(a) (b)<br />
Figure 1. Indus script. (a) Three examples of square stamp seals, each with an<br />
Indus text at the top (image credit: J.M. Kenoyer/Harappa.com). Texts were usually<br />
written from right to left (inferred, for example, from writing on pottery where a<br />
sign is overwritten by another on its left) but this direction was reversed in seals<br />
(that is, left to right as in these images) to form correctly oriented impressions. (b)<br />
A small subset of the 400 or so signs in the Indus script (selected from Mahadevan’s<br />
concordance).<br />
J. Dravidian Linguistics, vol. 37, no.<br />
1, 2008, pp. 53-72). Such regularities<br />
point to the existence of distinctive<br />
syntactic rules underlying the Indus<br />
texts.<br />
MARKOV AND<br />
NfiGRAM MODELS<br />
The presence of statistically significant<br />
clusters of symbols with<br />
positional preferences suggests that<br />
there is sequential order in the Indus<br />
script. One way to capture such<br />
sequential order is to learn a Markov<br />
model for the script from available<br />
texts.<br />
The simplest (first-order) model<br />
estimates the transition probabilities<br />
P(s i |s j ) that sign i follows sign j. The<br />
obvious way of estimating P(s i |s j ) is<br />
to count the number of times sign i<br />
follows sign j, an approach equivalent<br />
to maximum likelihood estimation.<br />
However, given that there are approximately<br />
400 signs and only a few<br />
thousand texts, a large number of<br />
sign pairs will have a frequency of 0<br />
even though their actual probability<br />
may not necessarily be 0. This is a<br />
common problem in statistical language<br />
modeling and can be addressed<br />
using smoothing techniques.<br />
A prominent smoothing technique,<br />
the modified Kneser-Ney algorithm,<br />
was used to learn a first-order Markov<br />
model of the Indus script (R.P.N. Rao<br />
et al., “A Markov Model of the Indus<br />
Script,” Proc. National Academy of<br />
Sciences, vol. 106, no. 33, 2009, pp.<br />
13685-13690). The data for training<br />
the model came from Iravatham<br />
Mahadevan’s The Indus Script: Texts,<br />
Concordance and Tables (Archaeological<br />
Survey of India, 1977). Once trained,<br />
the Markov model can be used to<br />
generate new samples of Indus texts.<br />
This can reveal interesting subunits of<br />
grammatical structure and recurring<br />
patterns, as Figure 2a shows.<br />
There exist a large number of damaged<br />
Indus seals, tablets, and other<br />
artifacts that contain texts with one<br />
or more missing or illegible signs. A<br />
Markov model of the Indus texts can<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
77
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
78<br />
COMPUTER<br />
Log likelihood<br />
AI REDUX<br />
0<br />
–10<br />
–20<br />
–30<br />
–40<br />
(a) (b)<br />
Indus A B C D<br />
(c)<br />
Figure 2. Markov model of the Indus script. (a) (Top) A new Indus text generated by<br />
the Markov model. (Below) Two closest matching texts in the training corpus. (b)<br />
(Left) Text from a damaged seal containing one or more missing signs (indicated<br />
by the shaded box). (Right) Three possible restorations predicted by the Markov<br />
model. The črst and third texts actually exist in the corpus. (c) Log likelihood under<br />
the Markov model for four texts (A through D) found in foreign lands compared to<br />
average log likelihood for a random set of 50 Indus region texts not included in the<br />
training data (error bar denotes +/- 1 standard error of mean). The 50 Indus region<br />
texts had the same average length as the foreign texts.<br />
be used to predict these missing or<br />
illegible signs. The first-order Markov<br />
model was found to be surprisingly<br />
good at predicting signs deliberately<br />
obliterated for testing purposes, performing<br />
at a 75 percent accuracy<br />
level in a fivefold cross-validation<br />
study. Figure 2b shows an example<br />
of restoration of an actual damaged<br />
Indus inscription from Mahadevan’s<br />
concordance, as suggested by the<br />
first-order Markov model.<br />
Several seals with Indus signs have<br />
been discovered outside the Indus<br />
region, as far away as Mesopotamia<br />
and the Persian Gulf. One can compute<br />
the likelihood of these “foreign”<br />
texts with respect to a Markov model<br />
trained only on texts from the Indus<br />
region. As Figure 2c shows, the likelihood<br />
values for many of these foreign<br />
texts are several orders of magnitude<br />
lower than those for Indus region<br />
texts, indicating their low probability<br />
of belonging to the same language.<br />
Indeed, an examination of these<br />
foreign texts reveals that although<br />
they contain commonly used Indus<br />
signs, the sequential order of the signs<br />
differs dramatically from that in texts<br />
originating in the Indus region—for<br />
example, the sequence in the foreign<br />
text C in Figure 2c never occurs<br />
on an Indus seal. This suggests that<br />
A<br />
B<br />
C<br />
D<br />
Indus traders in foreign lands may<br />
have used the script to represent different<br />
content, such as foreign names<br />
or goods, or an altogether different<br />
language.<br />
More recent work examined the<br />
utility of higher-order N-gram models.<br />
An N-gram model is essentially an<br />
(N 1)th-order Markov chain where<br />
the transition probability depends on<br />
the previous N 1 symbols instead<br />
of just the previous symbol. The<br />
results suggest that a bigram model<br />
(N = 2) captures a significant portion<br />
of the syntax, with trigrams and<br />
quadrigrams making more modest<br />
contributions (N. Yadav et al., “Statistical<br />
Analysis of the Indus Script<br />
Using N-Grams,” PLoS One, to appear<br />
in 2010).<br />
THE LANGUAGE QUESTION<br />
AND ENTROPIC ANALYSIS<br />
The brevity of existing Indus<br />
inscriptions and other attributes,<br />
such as the low frequency of many<br />
Indus signs, has prompted some<br />
to propose that the Indus script is<br />
not a script at all but instead is a<br />
collection of religious or political<br />
symbols. Adherents of the “nonscript”<br />
thesis have likened the Indus<br />
script to nonlinguistic systems such<br />
as traffic signs, medieval heraldry,<br />
markings on pottery in the Vinc a<br />
culture of southeastern Europe,<br />
and carvings of deities on boundary<br />
stones in Mesopotamia.<br />
Interestingly, this is not the first<br />
time that a script of a major ancient<br />
civilization has been deemed to be<br />
nonlinguistic. The Mayan script was<br />
long considered not to be a writing<br />
system at all until Knorozov and<br />
others finally worked out the rich<br />
phonetic underpinnings of the script<br />
in the 1950s and 1960s, revealing<br />
it to be a fully functional writing<br />
system.<br />
Several key features of the Indus<br />
script suggest that it represents<br />
language:<br />
the texts are usually linear, like<br />
the vast majority of linguistic<br />
scripts and unlike nonlinguistic<br />
systems such as heraldry or traffic<br />
signs;<br />
symbols are modified by the<br />
addition of specific sets of marks<br />
over, around, or inside a symbol,<br />
much like later Indian scripts<br />
that use such marks to modify<br />
the sound of a root consonant or<br />
vowel symbol;<br />
the script possesses rich syntactic<br />
structure, with particular<br />
signs or clusters of signs preferring<br />
particular positions<br />
within texts, similar to linguistic<br />
sequences;<br />
the script obeys the Zipf-<br />
Mandelbrot law, a power-law<br />
distribution on ranked data,<br />
which is often considered a necessary<br />
(though not sufficient)<br />
condition for language; and<br />
texts found in Mesopotamia and<br />
the Persian Gulf use the same<br />
signs as texts found in the Indus<br />
region but alter their ordering,<br />
suggesting that the script was<br />
versatile enough to represent<br />
different subject matter or a different<br />
language.<br />
Such attributes are hard to reconcile<br />
with the thesis that the script<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
merely represents religious or political<br />
symbols.<br />
Further evidence for the Indus<br />
script’s linguistic nature comes from<br />
quantitative studies comparing the<br />
entropy of the Indus texts with that<br />
of various languages. In some nonlinguistic<br />
systems, such as the Vinc a<br />
system, the signs do not seem to<br />
follow any order and appear to be<br />
juxtaposed randomly. Other nonlinguistic<br />
systems, such as deities<br />
carved on Mesopotamian boundary<br />
stones, exhibit a rigid order reflecting,<br />
for example, the hierarchical order of<br />
the deities.<br />
In languages, on the other hand,<br />
sequences of words and characters<br />
exhibit a degree of order intermediate<br />
between random and rigid. This<br />
intermediate degree of randomness<br />
arises from the grammatical rules<br />
and morphological structure of languages.<br />
The degree of randomness in<br />
a sequence can be measured quantitatively<br />
using entropy.<br />
The smoothed first-order Markov<br />
model can be used to compute conditional<br />
entropy, which measures the<br />
average flexibility allowed in choosing<br />
the next sign given a preceding<br />
sign. The conditional entropy of Indus<br />
texts has been shown to fall within the<br />
range of natural languages (R.P.N. Rao<br />
et al., “Entropic Evidence for Linguistic<br />
Structure in the Indus Script,” Science,<br />
vol. 324, no. 5931, 2009, p. 1165).<br />
A potential shortcoming of the<br />
conditional entropy result is that it<br />
only captures pairwise dependencies.<br />
Figure 3 shows new results<br />
(presented here for the first time)<br />
on higher-order entropies for blocks<br />
of up to six symbols. These block<br />
entropies were calculated using<br />
the state-of-the-art NSB estimator<br />
(I. Nemenman, F. Shafee, and<br />
W. Bialek, “Entropy and Inference,<br />
Revisited,” Advances in Neural Information<br />
Processing Systems 14, MIT<br />
Press, 2002, pp. 471-478), which has<br />
been shown to provide good estimates<br />
of entropy for undersampled<br />
discrete data.<br />
Normalized block entropy<br />
6<br />
5<br />
4<br />
3<br />
2<br />
1<br />
0<br />
1<br />
Indus<br />
Max Ent<br />
DNA<br />
Protein<br />
Tamil<br />
Eng chars<br />
Eng words<br />
Sansk<br />
Tagalog<br />
Sumer<br />
Fortran<br />
Min Ent<br />
The new results in Figure 3 extend<br />
the conditional entropy result to<br />
sequences of length up to six: The<br />
block entropies of the Indus texts<br />
remain close to those of a wide range<br />
of natural languages and far from<br />
the entropies for randomly and rigidly<br />
ordered sequences (Max Ent and<br />
Min Ent, respectively). Also shown in<br />
the plot for comparison are the entropies<br />
for a computer program written<br />
in Fortran and two sample biological<br />
sequences (DNA and proteins). The<br />
Fortran program and the biological<br />
sequences have noticeably lower and<br />
higher block entropies, respectively,<br />
than the Indus script and natural<br />
languages.<br />
Entropic similarity to natural languages<br />
by itself is not sufficient to<br />
prove that the Indus script is linguistic.<br />
However, given that it exhibits<br />
other key features of linguistic scripts<br />
as enumerated above, this similarity<br />
increases the probability in a<br />
Bayesian sense that the Indus script<br />
represents language.<br />
2 3<br />
4 5 6<br />
Sequence length (block size)<br />
Figure 3. Entropy of the Indus script compared to natural languages and other<br />
sequences. Symbols were signs for the Indus script; bases for DNA; amino acids for<br />
proteins; characters for English; words for English, Tagalog, and Fortran; symbols in<br />
abugida (alphasyllabic) scripts for Tamil and Sanskrit; and symbols in the cuneiform<br />
script for Sumerian. To compare sequences over dićerent alphabet sizes L, the<br />
logarithm in the entropy calculation was taken to base L: 417 for Indus, 4 for DNA,<br />
and so on. The resulting normalized block entropy is plotted as a function of block<br />
size. Error bars denote one standard deviation above/below mean entropy and are<br />
negligibly small except for block size 6.<br />
PROSPECTS FOR<br />
DECIPHERMENT<br />
Can the Indus script be deciphered<br />
without a bilingual artifact such as<br />
the Rosetta Stone? History suggests<br />
it could be: The Linear B script used<br />
in ancient Greece was deciphered in<br />
the 1950s without a bilingual artifact.<br />
The decipherment relied on several<br />
factors such as being able to identify<br />
common roots and suffixes, hypothesizing<br />
that the script was syllabic, and<br />
guessing the pronunciation of some<br />
symbols, which revealed the script<br />
to be a form of Greek. In the case of<br />
the Indus script, the short length of<br />
the available texts makes such an<br />
approach difficult. It may be possible,<br />
however, to obtain results by focusing<br />
on particular types of Indus texts and<br />
the contexts in which they are found.<br />
Most of the Indus texts found are<br />
on stamp seals, which were typically<br />
used in Bronze Age cultures for regulating<br />
trade. Seals were pressed onto<br />
clay tags affixed to packaged goods.<br />
The tags often listed the contents,<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
79
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
80<br />
origin or destination, type or amount<br />
of goods being traded, name and title<br />
of the owner, or some combination of<br />
these. Numerous such clay tags have<br />
been found at various sites in the Indus<br />
civilization, bearing seal impressions<br />
on one side and impressions of woven<br />
cloth, reed matting, or other packing<br />
material on the other.<br />
If the Indus script was used for<br />
trade, as the evidence suggests, then<br />
we would expect to find signs representing<br />
numerical quantities and<br />
units of measure. Progress in this<br />
direction has recently been reported<br />
by Bryan Wells, who estimated the<br />
volumes of two pots, one bearing<br />
the inscription and the other the<br />
inscription . By showing that the<br />
estimated volume of the second pot<br />
was in fact twice that of the first,<br />
Wells was able to conclude that<br />
strokes such as and represent<br />
numbers, and the sign probably<br />
represents a unit of volume.<br />
Other efforts by Parpola and<br />
Mahadevan have assumed that at<br />
least some of the texts probably<br />
represent names. Phonetic values<br />
for specific signs can then be sug-<br />
gested by assuming an underlying<br />
language—for example, proto-Dravidian—and<br />
using the rebus principle<br />
to guess the pronunciation of pictorial<br />
signs such as “fish,” “jar,” and<br />
“arrow.” In English, for example,<br />
the rebus principle could be used to<br />
represent an abstract word such as<br />
“belief” with the picture of a bee followed<br />
by a picture of a leaf. Ancient<br />
scripts often used the rebus principle<br />
to represent language.<br />
Probabilistic models could<br />
help in this decipherment process<br />
in several ways. Recently proposed<br />
algorithms for probabilistic<br />
grammar induction could allow<br />
construction of a partial grammar<br />
for the Indus texts, facilitating the<br />
identification of root words, suffixes,<br />
prefixes, and other modifiers.<br />
This may facilitate the use of deciphering<br />
techniques similar to those<br />
applied to Linear B. Reconstructing<br />
a grammar would also allow<br />
comparison with the grammars of<br />
other languages, helping narrow<br />
down the set of candidate language<br />
families to consider when using the<br />
rebus principle.<br />
Silver Bullet Security Podcast<br />
COMPUTER<br />
AI REDUX<br />
In-depth interviews with security gurus. Hosted by Gary McGraw.<br />
www.computer.org/security/podcasts<br />
Sponsored by<br />
A site-by-site analysis of the Indus<br />
texts using probabilistic models could<br />
indicate whether different languages<br />
or dialects were spoken in different<br />
regions of the Indus civilization. Similarly,<br />
training probabilistic models<br />
on texts found on specific types of<br />
artifacts, such as seals versus tablets,<br />
could ascertain whether the content<br />
of the texts varies according to artifact<br />
type.<br />
In summary, the study of the<br />
Indus script has emerged as an<br />
exciting area of interdisciplinary<br />
research, offering a unique opportunity<br />
for probabilistic models to shed<br />
new light on one of the world’s oldest<br />
civilizations.<br />
Rajesh P.N. Rao is an associate professor<br />
in the Department of Computer<br />
Science & Engineering at the University<br />
of Washington. Contact him at<br />
rao@cs.washington.edu.<br />
________________<br />
Editor: Naren Ramakrishnan, Dept. of<br />
Computer Science, Virginia Tech, Blacksburg,<br />
VA; _________<br />
naren@cs.vt.edu<br />
_____________________________________________<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
SOFTWARE TECHNOLOGIES<br />
When TV Dies, Will<br />
It Go to the Cloud?<br />
Karin Breitman and Markus Endler, PUC-Rio, Brazil<br />
Rafael Pereira and Marcello Azambuja, Globo.com<br />
Coupled with the expected growth in bandwidth through the<br />
next decade, cloud <strong>computing</strong> will change the face of TV.<br />
The increasing popularity<br />
of videos on the<br />
Internet, allied to recent<br />
advances in network<br />
technology, are drastically changing<br />
television as we know it. In the past<br />
few decades we experienced a very<br />
clear role distinction: TV channels<br />
and independent companies produced<br />
video footage to be distributed<br />
by broadcasters and consumed by<br />
passive general audiences. Roles and<br />
responsibilities were clear down the<br />
line, and everyone was happy.<br />
A few years ago this “family<br />
around the TV set” scenario began to<br />
crack. Television faced several daunting<br />
challenges as cable multiplied the<br />
number of viewing choices and hardware<br />
prices let middle-class families<br />
own as many TV sets as there were<br />
members in the family.<br />
SEA CHANGE<br />
The Internet brought the potential<br />
to completely reinvent TV. First,<br />
it let users see what they wanted,<br />
when they wanted, while suppressing<br />
the need for additional hardware.<br />
Digital video recorders, notably the<br />
TiVo, popularized the concept of letting<br />
users choose more convenient<br />
times to watch their favorite programs.<br />
However, with the increase<br />
in bandwidth availability for the<br />
last mile—via cable and asymmetric<br />
digital subscriber line (ADSL) technol-<br />
0018-9162/10/$26.00 © 2010 IEEE<br />
ogy—it makes more sense to stream<br />
the content directly from the Internet<br />
than record it for later use.<br />
Second, and more importantly, the<br />
Net removes the barrier that separates<br />
producers, distributors, and consumers.<br />
On the Internet, anyone can<br />
produce and distribute high-quality<br />
content. As a result, there is much<br />
more content available, making the<br />
competition for audiences tougher and<br />
changing viewing habits irreversibly.<br />
Third, the Internet allows mixing<br />
and matching of multisource content.<br />
It has become commonplace for networks<br />
to mix their own footage with<br />
user-generated content to provide a<br />
more holistic experience. Video production,<br />
distribution, and selection are<br />
no longer the privilege of a few. Users<br />
now have a front seat, forcing media<br />
giants to explore new business models.<br />
From a technical viewpoint, huge<br />
challenges remain, however, including<br />
the ability to process, index,<br />
store, and distribute nearly limitless<br />
amounts of data. This is why cloud<br />
<strong>computing</strong> will play a major role in<br />
redefining TV in the next few years.<br />
RAMPING UP<br />
Electronic devices that can be used<br />
to consume content on the Internet<br />
are proliferating at an increasing rate:<br />
PCs, tablet and laptop computers,<br />
PDAs, mobile phones, handheld video<br />
game consoles, and eBook readers,<br />
Published by the IEEE Computer Society<br />
not to mention router-type devices<br />
that let regular TV sets display Internet<br />
content.<br />
It seems our <strong>lives</strong> are driven by<br />
media displays, as Steve Jobs demonstrated<br />
with his recent unveiling<br />
of the iPad. It is easy to imagine a<br />
middle-class adult in the work force<br />
soon having access to two or more<br />
such displays on a regular basis.<br />
Displays can be organized in<br />
five strata, according to their evolution<br />
(B. Mazloff, Le 5éme écran<br />
– Les medias urbains dans la ville<br />
2.0 – editions Fyp - 2009), as Figure<br />
1 shows. Movie projection screens<br />
were the first to appear, in open<br />
public spaces. Then came the TV<br />
and PC—no longer public, but still<br />
collective. Mobile devices followed,<br />
for personal use in both private and<br />
public environments. More recently,<br />
public electronic displays on everything<br />
from billboards to bus stops are<br />
changing the urban landscape.<br />
Fifty years ago, video was produced<br />
in a single format since its<br />
consumption was restricted to some<br />
specific displays. Today, on the other<br />
hand, several different versions are<br />
required to enable access on PCs,<br />
iPhones, PDAs, game consoles,<br />
and other devices. This is a critical<br />
problem for broadcasters, as video<br />
processing is as computationally<br />
expensive as it is data intensive, consuming<br />
time and resources.<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
81
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
82<br />
SOFTWARE TECHNOLOGIES<br />
Shared<br />
public<br />
spaces<br />
open<br />
access<br />
Besides the proliferation of different<br />
devices, it is not uncommon for<br />
the market to prefer particular platforms.<br />
A decade ago, RealNetworks’s<br />
RealVideo and RealMedia took the<br />
lead, followed by MS Windows Media<br />
and Adobe’s Flash, with the future<br />
looking toward HTML 5. Each of these<br />
technologies defined a set of associated<br />
formats, codecs, and transport<br />
protocols that everyone must follow.<br />
On top of that, the last mile is pushing<br />
the demand for high-quality content<br />
and high-definition videos that require<br />
many more computational resources.<br />
SPLIT AND MERGE<br />
Split and Merge is a cloud-based<br />
platform for distributed video<br />
encoding that can overcome these<br />
drawbacks. The basic idea is to use the<br />
cloud’s elasticity to engage resources<br />
dynamically, then distribute and parallelize<br />
the video-encoding processes.<br />
The Split and Merge platform, shown<br />
in Figure 2, was designed to reduce<br />
video-encoding times to fixed thresholds,<br />
independently of the input size<br />
of the video file, using only dynamic<br />
resource provisioning in the cloud.<br />
Split and Merge fragments every<br />
video received, processes the<br />
fragments in a distributed cloud<br />
environment, and merges partial<br />
results. As in most map-reduce implementations,<br />
it makes efficient use of<br />
available <strong>computing</strong> resources. It also<br />
allows for the customization of tech-<br />
COMPUTER<br />
Shared<br />
private<br />
space<br />
open<br />
access<br />
Shared<br />
private<br />
space<br />
restricted<br />
access<br />
Individual<br />
mobile<br />
very<br />
restricted<br />
access<br />
Shared<br />
public<br />
spaces<br />
open<br />
access<br />
Figure 1. Evolution of media display types. The Internet is enabling the rapid<br />
proliferation of electronic displays.<br />
niques used in the split, distribute,<br />
process, and merge steps as needed.<br />
This ensures flexibility, adaptation,<br />
extensibility, and the accommodation<br />
of different applications. In the<br />
case of video processing, allowing<br />
a choice among codecs, containers,<br />
audio streams, and different splitting<br />
techniques is paramount.<br />
Considering the growth of Internet<br />
video use along with the demand<br />
for higher-quality HD-level content,<br />
dealing efficiently with transcoding<br />
processes is a strategic priority. The<br />
cloud solution offers a competitive<br />
advantage by providing the unprecedented<br />
possibility of processing<br />
videos several hours long in the same<br />
time frame as those that run only a<br />
few minutes.<br />
DISTRIBUTION CHALLENGES<br />
Unlike TV signals, which are transmitted<br />
independently of the number<br />
of viewers, Internet media consumption<br />
is based on connectivity: Each<br />
user who wants to watch a video<br />
must open a separate connection.<br />
With unicast, the most popular distribution<br />
model, there is a separate<br />
connection for each user to the server<br />
responsible for content distribution.<br />
This limitation becomes increasingly<br />
evident when a variable volume of<br />
information must be processed to<br />
meet spikes in demand during, for<br />
example, popular sports competitions<br />
or public emergencies.<br />
No matter how resourceful the<br />
entity distributing the contents is,<br />
there will be peak times with excessive<br />
demand and other times of<br />
idleness. Given that service providers<br />
can build applications with an elastic<br />
infrastructure and adjust effectively<br />
to demand variations, the cloud has<br />
all the characteristics needed to deal<br />
with this type of content.<br />
In cases where there is a very<br />
large or seasonal demand, the use<br />
of public clouds for information processing<br />
and storage is emerging as an<br />
attractive alternative. The concept of<br />
hardware as a service (HaaS) relieves<br />
the necessity of making large infrastructure<br />
investments, while allowing<br />
on-the-fly resizing and adaptation to<br />
current needs.<br />
With a public cloud, users can<br />
quickly gauge the resources required<br />
to perform a particular task and pay<br />
only for those effectively used. A<br />
successful example of this is the registration<br />
system for the Big Brother<br />
Brasil reality TV show.<br />
The application process is open<br />
to any resident in the country, with<br />
contestants required to send a video<br />
of themselves in the format of their<br />
choice. Videos are encoded in the<br />
MPEG-2 standard to facilitate visualization<br />
by the jurors and spare them<br />
the hassle of dealing with a plethora<br />
of different codecs. The system is<br />
able to receive a very large number of<br />
videos during the three-month application<br />
process.<br />
The system in particular leverages<br />
the power of cloud <strong>computing</strong> to deal<br />
with uncertain storage and processing<br />
requirements, allocate resources<br />
needed during the application and<br />
selection processes, and scale up to<br />
rare but extreme high-peak situations—for<br />
example, during the last<br />
weekend, when 60 percent of the<br />
total submissions with about 200,000<br />
videos are expected.<br />
Applications with seasonal but<br />
very large demand are not rare.<br />
The Internet transmission of sports<br />
events such as FIFA’s World Cup and<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
the Olympics, and of breaking news<br />
such as Michael Jackson’s death,<br />
require a huge infrastructure for a<br />
very short time, making them killer<br />
cloud applications.<br />
CONSUMER CHALLENGES<br />
The new paradigm of video content<br />
consumption quickly became<br />
clear to major broadcasters, whose<br />
revenues had been falling consistently<br />
since 2005 and who had<br />
been forced to rethink their content<br />
distribution models. For example,<br />
NBC Universal partnered with News<br />
Corp. to launch Hulu.com in 2007,<br />
with Disney joining two years later.<br />
The popular website, which offers<br />
commercial-supported streaming<br />
video of TV shows and movies, aims<br />
to recover part of the lost revenue<br />
resulting from the decrease of traditional<br />
TV audiences.<br />
During the recent high-definition<br />
format war between HD-DVD (supported<br />
by Microsoft and Toshiba) and<br />
Blu-ray (supported by Sony) technologies,<br />
videogames played an important<br />
role. Sony pushed Blu-ray adoption,<br />
using the technology as the underlying<br />
basis for its PlayStation 3, which<br />
doubles as a Blu-ray disc player.<br />
Although Microsoft’s Xbox 360 console<br />
supported HD-DVD, a disc player<br />
sold as expansion hardware and was<br />
not required to play videogames.<br />
Shortly after Blu-ray emerged victorious<br />
in 2008 (http://news.bbc.co.uk/1/<br />
________________<br />
hi/business/7252172.stm), it become<br />
clear that Microsoft’s strategy was not<br />
focused on the disc formats but rather<br />
on the rising market for online video.<br />
In July 2008, less than six months<br />
after the end of the HD format wars,<br />
Microsoft announced its partnership<br />
with Netflix to stream movies and<br />
TV episodes using the XBox 360 console<br />
(www.microsoft.com/presspass/<br />
________________________<br />
press/2008/jul08/07-14instantstreampr.<br />
____ mspx). This constituted a shift from<br />
the paradigm of media discs, enabling<br />
console owners to rent movies with the<br />
press of a button. Apple offered a similar<br />
initiative with Apple TV, enabling<br />
chunk1 chunk2<br />
subscribers to download movies<br />
through its iTunes store.<br />
While the Internet offered new revenue<br />
possibilities, it also augmented<br />
the complexity of production and<br />
distribution business models. Hulu<br />
(www.fastcompany.com/magazine/<br />
_____________________<br />
140/the-unlikely-mogul.html), for<br />
example, preferred to follow a model<br />
similar to that used by TV, with<br />
commercial spots at intervals in the<br />
content. Even this simple model can<br />
be further refined, with Web technology<br />
easily identifying and addressing<br />
specific group campaigns such as<br />
gender, age, and location.<br />
Cable TV networks are pursuing<br />
a similar approach to avoid losing<br />
ground to Internet-based TV providers.<br />
Many have launched their own<br />
video sites, which offer added services<br />
to justify their value. For example,<br />
Comcast recently launched Xfinity<br />
(blogs.wsj.com/digits/2009/12/15/<br />
______________________<br />
comcast-opens-fancast-xfinity-tv), a<br />
service that lets users watch TV programming<br />
on the Internet anywhere.<br />
The popularity of online videos<br />
has also raised the interesting possibility<br />
of the Internet serving as a large<br />
and collaborative content producer,<br />
with user-generated content complementing<br />
TV programming.<br />
Tempo<br />
chunkN<br />
chunk1 chunk2 chunkN<br />
Full encoded video<br />
Figure 2. Split and Merge architecture. The system fragments every video received,<br />
processes the fragments in a distributed cloud environment, and merges partial<br />
results.<br />
Video production and distribution<br />
are no longer<br />
restricted to large broadcasters.<br />
Users now have the power<br />
to make, distribute, mix, and match<br />
their own content. Cloud <strong>computing</strong><br />
will play a decisive role in this<br />
extremely demanding scenario. The<br />
evolution of connectivity, coupled<br />
with the expected growth in bandwidth<br />
over the next decade, will<br />
indelibly change the face of TV.<br />
Karin Breitman is an assistant<br />
professor in the Departamento de<br />
Informática, PUC-Rio. Contact her at<br />
______________<br />
karin@inf.puc-rio.br.<br />
Markus Endler is an associate<br />
professor in the Departamento de<br />
Informática, PUC-Rio. Contact him at<br />
______________<br />
endler@inf.puc-rio.br.<br />
Rafael Pereira is a senior media engineer<br />
at Globo.com. Contact him at<br />
____________________<br />
rafael.pereira@corp.globo.com.<br />
Marcello Azambuja is a digital media<br />
manager at Globo.com. Contact him at<br />
azambuja@ieee.org.<br />
_____________<br />
Editor: Mike Hinchey, Lero—The Irish<br />
Software Engineering Research Centre;<br />
mike.hinchey@lero.ie<br />
____________<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
83
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
84<br />
INVISIBLE COMPUTING<br />
Questioning Invisibility<br />
The invisibility of today’s<br />
technology is often a<br />
blessing. My laptop<br />
can be used as a word<br />
processor, TV, and stereo without<br />
COMPUTER<br />
Leah Buechley, MIT Media Lab<br />
Should invisibility be the guiding design goal for ubiquitous<br />
<strong>computing</strong>?<br />
A good tool is an invisible tool. By invisible, I mean that the tool does not intrude on your consciousness; you focus on the task,<br />
not the tool.<br />
– Mark Weiser<br />
changing shape, and I’m grateful<br />
that I don’t have to think about transistors,<br />
compilers, and operating<br />
systems while I use it. However, is<br />
invisibility always a good thing?<br />
Figure 1. Crashes and errors make the invisible technologies underlying our <strong>lives</strong><br />
alarmingly visible.<br />
Should it be the guiding design goal<br />
for ubiquitous <strong>computing</strong>?<br />
WHEN INVISIBILITY FAILS<br />
Benjamin Mako Hill has been<br />
examining instances where the invisibility<br />
of technology breaks down.<br />
His website, revealingerrors.com,<br />
documents occasions when a crash<br />
or error makes one of the invisible<br />
technologies underlying our <strong>lives</strong><br />
alarmingly visible, forcing us to confront<br />
its technological innards. Figure<br />
1 shows a few examples.<br />
The crashed ATM with its exposed<br />
Windows desktop and the GPS system<br />
that locates itself in the ocean are<br />
self-explanatory errors, but the third<br />
example requires some elucidation.<br />
The text at the top of the webpage<br />
should read “Gay eases into 100 final<br />
at Olympic trials,” Gay being the<br />
surname of athlete Tyson Gay. This<br />
strange headline reveals the fact that<br />
the website posting the news feed,<br />
a conservative network called One<br />
News Now, uses a program to adjust<br />
the language of AP news stories. Here<br />
we see that part of their program<br />
replaces instances of the word “gay”<br />
with the word “homosexual.”<br />
Hill argues that such breakdowns<br />
Published by the IEEE Computer Society 0018-9162/10/$26.00 © 2010 IEEE<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
Figure 2. The LilyPad Arduino toolkit consists of a set of sewable electronic modules that users can stitch together with electrically<br />
conductive thread to make interactive textile-based computers.<br />
aren’t necessarily bad. Though<br />
inconvenient and frustrating, they<br />
can reveal the inelegance, fragility,<br />
and questionable practices behind<br />
technological systems. I can use that<br />
information to make more informed<br />
decisions; I might very well change<br />
banks if I knew more about my favorite<br />
ATM’s operating system.<br />
Does this mean we should start<br />
designing error-prone systems? Of<br />
course not. But it does raise a question<br />
about the narrow design goal of<br />
invisibility. Systems that vanish into<br />
the background aren’t inherently<br />
good ones. The examples in Figure 1<br />
are troubling demonstrations of some<br />
of the things invisibility can hide.<br />
LEVERAGING VISIBILITY<br />
FOR EDUCATION<br />
The errors documented on Hill’s<br />
website are funny, fascinating, and<br />
enlightening; consequently, they<br />
provide wonderful opportunities for<br />
teaching and learning.<br />
Imagine the curiosity and delight<br />
that an encounter with one of these<br />
broken systems could inspire in a<br />
young person. There are two facets<br />
to this appeal. First, the errors are<br />
engaging—they surprise us and force<br />
us to notice technology we might<br />
have otherwise ignored. Second, they<br />
introduce legibility to technology—<br />
they reveal interesting information<br />
about how it works.<br />
In the research group I direct at<br />
the MIT Media Lab (hlt.media.mit.<br />
__________<br />
___ edu), we design educational technology<br />
that is deliberately engaging and<br />
legible. We exploit these properties<br />
to get students excited about technology.<br />
Our particular approach focuses<br />
on using new and unusual physical<br />
materials to create compelling and<br />
comprehensible systems.<br />
For example, during the past several<br />
years we have been working<br />
in the emerging field of electronic<br />
textiles, or “e-textiles,” integrating<br />
electronics, computers, and textiles.<br />
We began by tackling a fundamental<br />
engineering challenge: How do you<br />
attach computers to fabric? Once we<br />
had developed robust solutions to this<br />
problem, we focused on making the<br />
domain accessible to students.<br />
The result of our efforts was the<br />
LilyPad Arduino (L. Buechley et al.,<br />
“The LilyPad Arduino: Using Computational<br />
Textiles to Investigate<br />
Engagement, Aesthetics, and Diversity<br />
in Computer Science Education,” Proc.<br />
26th Ann. SIGCHI Conf. Human Factors<br />
in Computing Systems, ACM Press,<br />
2008, pp. 423-432). As the leftmost<br />
image in Figure 2 shows, this toolkit<br />
consists of a set of sewable electronic<br />
modules—similar in spirit to Lego<br />
Mindstorm modules—that users can<br />
stitch together with electrically conductive<br />
thread to make interactive<br />
textile-based computers.<br />
In a series of courses and workshops,<br />
we found that this very visible<br />
new technology could uniquely capture<br />
the imagination of teenagers<br />
and teach them the fundamentals of<br />
computer science and electrical engineering.<br />
Interestingly, young women<br />
were especially excited about this<br />
blend of textiles and <strong>computing</strong>. The<br />
other two images in Figure 2 show a<br />
young woman from one of our workshops<br />
first constructing and then<br />
modeling her course project, an interactive<br />
light-up jacket with an ambient<br />
thermometer.<br />
We’re now expanding this<br />
approach to another unusual material,<br />
paper—exploring how we can<br />
blend paper and paint with computers<br />
and electronics. We’ve designed a<br />
paper <strong>computing</strong> kit that consists of<br />
magnetic sensors, actuators, microcontrollers,<br />
and wireless devices;<br />
ferrous paper, to which the modules<br />
stick; and a jar of conductive paint,<br />
which is used to connect the modules<br />
across the paper. Students can<br />
use the kit to paint beautiful, functional<br />
electronic devices onto paper.<br />
Figure 3 shows images of a prototype<br />
kit and a construction example:<br />
an electronic pop-up book built by<br />
Jie Qi, an undergraduate researcher<br />
in our lab.<br />
We’ve just begun to hold workshops<br />
to explore how we might employ this<br />
kit to teach embedded <strong>computing</strong> (J. Qi<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
85
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
86<br />
INVISIBLE COMPUTING<br />
Figure 3. Paper <strong>computing</strong> kit. Left: Prototype kit. Right: Electronic popables.<br />
and L. Buechley, “Electronic Popables:<br />
Exploring Paper-Based Computing<br />
through an Interactive Pop-up Book,”<br />
Proc. 4th Int’l Conf. Tangible, Embedded,<br />
and Embodied Interaction, ACM<br />
Press, pp. 121-128).<br />
Technologies like these—ones that,<br />
at their best, captivate, empower,<br />
and educate people—stand in direct<br />
opposition to ubicomp’s tenet of<br />
invisibility; the kits, and often the<br />
devices constructed with them as<br />
well, are intentionally visible objects<br />
that reveal the inner workings of technology<br />
and explicitly require users’<br />
time and attention.<br />
Other researchers have also noted<br />
this conflict between invisibility and<br />
education (M. Eisenberg et al., “Invisibility<br />
Considered Harmful: Revisiting<br />
Traditional Principles of Ubiquitous<br />
Computing in the Context of Education,”<br />
Proc. 4th IEEE Int’l Workshop<br />
Wireless, Mobile, and Ubiquitous Technology<br />
in Education, IEEE CS Press, pp.<br />
103-110; Y. Rogers, “Moving On from<br />
Weiser’s Vision of Calm Computing:<br />
Engaging UbiComp Experiences,”<br />
Proc. 8th Int’l Conf. Ubiquitous Computing,<br />
LNCS 4206, Springer, 2006, pp.<br />
404-421).<br />
INVISIBILITY, VISIBILITY,<br />
AND DESIGN<br />
In our <strong>lives</strong> there are objects we<br />
ignore and objects we treasure. Some<br />
vanish into the background and stay<br />
there and others please, amuse,<br />
COMPUTER<br />
and comfort us. There are the forgotten<br />
paper clips, printers, and<br />
towels, and the beloved dining room<br />
tables, sports uniforms, and jewelry.<br />
Why should ubicomp—or any<br />
other <strong>computing</strong> discipline, for that<br />
matter—consign itself to the ignored,<br />
invisible realm?<br />
Our research group strives to build<br />
systems that fit into people’s aesthetic<br />
and emotional <strong>lives</strong> as much as their<br />
technological ones. As Figures 2 and 3<br />
suggest, exploring the aesthetic possibilities<br />
of technology provides us with<br />
new and unusual ways to excite and<br />
engage students. We also investigate<br />
aesthetic and emotional dimensions<br />
when we develop systems that are<br />
less explicitly educational.<br />
A recent project along these lines<br />
is a unique piece of wallpaper that<br />
we constructed with our paper <strong>computing</strong><br />
kit. The Living Wall is a flat<br />
surface built out of ferrous paint,<br />
conductive paint, traditional paint,<br />
and electronics to which our paper<br />
<strong>computing</strong> modules can be attached.<br />
With its wide range of attachable<br />
components, the Living Wall can provide<br />
lighting, sense information about<br />
its environment, communicate with<br />
other devices like computers and<br />
phones, and act as a large-scale input<br />
device. The News Brief “Researchers<br />
Build a Wall That Acts Like a Remote<br />
Control” on p. 18 has more information<br />
on the system and an illustration<br />
of its use.<br />
The Living Wall is a flexible ubicomp<br />
system. However, it also<br />
functions as a decorative element<br />
in a home. Like the other examples<br />
mentioned here, it wasn’t designed<br />
to be invisible; it elicits and rewards<br />
attention.<br />
Invisibility is a narrow design<br />
goal. It’s not necessarily a bad<br />
one, but it doesn’t capture the<br />
full range of technological or creative<br />
possibilities. If we as computer scientists<br />
and engineers only strive to<br />
build invisible systems, we’ll neglect<br />
to build important technology that is<br />
educational, engaging, and beautiful.<br />
We should expand our focus and our<br />
rhetoric.<br />
Leah Buechley is an assistant professor<br />
and AT&T Career Development<br />
Professor of Media Arts and Sciences<br />
at MIT Media Lab, where she also<br />
directs the High-Low Tech research<br />
group. Contact her at leah@media.<br />
mit.edu.<br />
Editor: Albrecht Schmidt, Institute for<br />
Computer Science and Business Information<br />
Systems, University of Duisburg-Essen,<br />
Germany; albrecht.schmidt@gmail.com<br />
Selected CS articles and columns<br />
are available for free at<br />
http://ComputingNow.computer.org.<br />
Join the<br />
IEEE<br />
Computer<br />
Society<br />
www.computer.org<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
EDUCATION<br />
Cutting Across<br />
the Disciplines<br />
Jim Vallino,<br />
Rochester Institute of Technology<br />
Engineering and <strong>computing</strong> educators must design curricula<br />
that require students to work outside their own domain.<br />
Multidisciplinary,<br />
interdisciplinary,<br />
transdisciplinary—<br />
these terms are<br />
all the buzz in engineering and<br />
<strong>computing</strong> curriculum design.<br />
Throughout their career, most<br />
graduates will work on project<br />
teams with people from multiple<br />
fields of expertise. Engineering and<br />
<strong>computing</strong> educators must accordingly<br />
design curricula that require<br />
students to work outside of their<br />
own domain. This opportunity can<br />
range from small-group collaboration<br />
in a single course to large-scale<br />
efforts that span every program at<br />
an institution.<br />
There is often resistance to incorporating<br />
multidisciplinary work into<br />
curricula. Academic institutions,<br />
like most other organizations, have<br />
administrative and management<br />
entities that can unintentionally construct<br />
impediments to cutting across<br />
entrenched boundaries. At colleges<br />
and universities, fingers usually point<br />
at the department as the main culprit.<br />
Typical impediments are joint sched-<br />
0018-9162/10/$26.00 © 2010 IEEE<br />
uling of cross-listed courses, faculty<br />
teaching-load accounting, and support<br />
for shared facilities.<br />
One reaction to this is a push to<br />
eliminate administrative entities.<br />
However, this creates a new set of<br />
problems when program responsibility<br />
becomes ill-defined. At the core,<br />
what is required is a commitment<br />
to improve students’ education by<br />
promoting multidisciplinary teams<br />
and projects. The motivation may<br />
be provided top-down, especially<br />
for institute-wide programs, but<br />
in most cases it will be a limited<br />
effort led from the bottom up by a<br />
small number of individual faculty<br />
members.<br />
ACCREDITATION<br />
PROVIDES A MOTIVATION<br />
Whether you believe that multidisciplinary<br />
work will be the savior<br />
of engineering and <strong>computing</strong> education<br />
or is just another fad that<br />
will blend into the curriculum landscape,<br />
educators will see it in one<br />
form or another in the foreseeable<br />
future.<br />
Published by the IEEE Computer Society<br />
Programs accredited by the Engineering<br />
Accreditation Commission of<br />
ABET (www.abet.org) must demonstrate<br />
that students have<br />
“(c) an ability to design a system,<br />
component, or process to meet<br />
desired needs within realistic<br />
constraints such as economic,<br />
environmental, social, political,<br />
ethical, health and safety, manufacturability,<br />
and sustainability”;<br />
“(d) an ability to function on<br />
multidisciplinary teams”; and<br />
“(h) the broad education necessary<br />
to understand the impact of<br />
engineering solutions in a global,<br />
economic, environmental, and<br />
societal context.”<br />
All three of these program outcomes<br />
look beyond a traditional<br />
single-discipline curriculum. Because<br />
the program is responsible for demonstrating<br />
these outcomes, the<br />
experiences can’t be haphazardly<br />
inserted in the curriculum or based<br />
on elective coursework that students<br />
may or may not actually take.<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
87
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
88<br />
COMPUTER<br />
EDUCATION<br />
The Computing Accreditation<br />
Commission specifies similar criteria<br />
for the accreditation of <strong>computing</strong><br />
programs.<br />
The broad field of <strong>computing</strong> cuts<br />
across disciplines in unique ways.<br />
Computing typically has a domain<br />
presence as a necessary tool rather<br />
than an area of detailed study—<br />
students must learn the fundamentals<br />
of <strong>computing</strong> to successfully<br />
apply it in all their work. Perhaps<br />
more important, they also must<br />
learn when a project has a <strong>computing</strong><br />
component that requires deeper<br />
expertise. This becomes an opportunity<br />
for educators to blend programs<br />
in <strong>computing</strong>, engineering, and other<br />
disciplines across an institution.<br />
MULTIDISCIPLINARY<br />
IN THE SMALL<br />
There are conflicting definitions<br />
for the terms multidisciplinary, interdisciplinary,<br />
and transdisciplinary,<br />
but educators shouldn’t get stuck on<br />
what to call it. Any approach that<br />
gets students interacting with material<br />
and people outside their own<br />
technical discipline, or in ways that<br />
are atypical for their discipline, is<br />
beneficial.<br />
Those who want to experiment<br />
with a multidisciplinary approach<br />
should start small within one of their<br />
courses by assigning exercises to<br />
students that require them to think<br />
from unfamiliar perspectives. In one<br />
course, I ask students to capture their<br />
thoughts on aspects of the course<br />
material in Haiku poems. Here’s an<br />
example of one called “Basic Principles”<br />
from a software engineering<br />
design course:<br />
Coupling, Cohesion<br />
Antagonistic forces<br />
Tradeoffs to be made.<br />
In that same course, I have students<br />
ask themselves about the<br />
structure shown in M.C. Escher’s<br />
Waterfall (www.mcescher.com/<br />
_____________________<br />
Gallery/recogn-bmp/LW439.jpg). For<br />
each of those questions about this<br />
illusionary structure, I ask them<br />
to pose an analog question when<br />
studying the design of a software<br />
system.<br />
This exercise isn’t what most<br />
readers may have in mind when<br />
they think multidisciplinary, but on<br />
a small scale that a faculty member<br />
can do in any course, it requires students<br />
to think using paradigms from<br />
other disciplines.<br />
The next step would be to have students<br />
enrolled in courses in different<br />
The students as well as the instructor must commit<br />
to the multidisciplinary approach.<br />
disciplines collaborate on projects.<br />
Individual faculty can coordinate this<br />
with little administrative support. As<br />
in all such instances, the students as<br />
well as the instructor must commit<br />
to the multidisciplinary approach: A<br />
project that serves as an extracurricular<br />
or small-credit activity for some<br />
students but counts as significant<br />
coursework for others won’t be very<br />
effective.<br />
MULTIDISCIPLINARY<br />
BY DESIGN<br />
If educators intend the multidisciplinary<br />
experience to satisfy<br />
accreditation requirements, it’s preferable<br />
to carefully design it into a<br />
program.<br />
All ABET-accredited software engineering<br />
programs require students to<br />
be able to work in one or more major<br />
application domains. However, what<br />
constitutes an application domain<br />
varies widely across programs (D.<br />
Bagert, “The Role of Application<br />
Domain Tracks in Software Engineering<br />
Programs,” Proc. 2006 Ann.<br />
Conf. Am. Soc. for Eng. Education,<br />
ACEE, 2006; http://soa.asee.org/paper/<br />
_______________________<br />
conference/paper-view.cfm?id=2832).<br />
Our software engineering program<br />
at the Rochester Institute of<br />
Technology (RIT) uses application<br />
domains as a vehicle to expose students<br />
to uses of <strong>computing</strong> outside<br />
their comfort zones. Each domain<br />
requires three courses, at least two<br />
of which must be taken from colleges<br />
other than our College of Computing<br />
and Information Sciences. This<br />
prevents the application domain<br />
from being simply a set of <strong>computing</strong><br />
electives.<br />
A cross-curriculum multidisciplinary<br />
approach involves designing<br />
a course, or course cluster, with<br />
multi-disciplinary interaction as a<br />
basic course principle. Educators<br />
must make the course material<br />
interesting and accessible to students<br />
from all the disciplines expected to<br />
participate.<br />
This can be challenging. With a<br />
computer engineering colleague, I<br />
created a cluster of three courses<br />
in real-time and embedded systems<br />
at RIT (J. Vallino and R.S.<br />
Czerniskowski, “Interdisciplinary<br />
Teaming as an Effective Method to<br />
Teach Real-Time and Embedded Systems<br />
Courses,” Proc. 2008 Workshop<br />
Embedded Systems Education, 2008,<br />
pp. 25-32). Even with closely related<br />
disciplines like software engineering<br />
and computer engineering, it<br />
was more difficult than we originally<br />
thought to keep the course interest<br />
balanced between the two.<br />
Educators must carefully select<br />
course projects to ensure that all<br />
disciplines contribute in different<br />
but equivalent ways. Some registration<br />
controls may be needed to<br />
help maintain balance across all<br />
disciplines. Ideally, these courses<br />
are team taught, but unless an<br />
institution’s teaching-load accounting<br />
easily accommodates that<br />
arrangement, it may have to settle<br />
for more traditional single-instructor<br />
teaching.<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
Finally, what seems like it should<br />
be easy could require regular attention.<br />
Each term, we have to schedule<br />
multiple course listings at the same<br />
time, in the same room, and with a<br />
common final exam time.<br />
We’re currently applying lessons<br />
learned from the successful multidisciplinary<br />
real-time and embedded<br />
systems cluster to an applied cryptography<br />
cluster incorporating computer<br />
science, computer engineering, and<br />
software engineering.<br />
LARGEfiSCALE<br />
MULTIDISCIPLINARY<br />
EXPERIENCES<br />
More ambitious forays into multidisciplinary<br />
work require significantly<br />
more coordination and administrative<br />
support. RIT has implemented many<br />
such programs for seniors in its College<br />
of Engineering (P.H. Stiebitz, E.C.<br />
Hensel, and J.R. Mozrall, “Multidisciplinary<br />
Engineering Senior Design<br />
at RIT,” Proc. 2004 Ann. Conf. Am.<br />
Soc. for Eng. Education, ACEE, 2004;<br />
http://soa.asee.org/paper/conference/<br />
_________________<br />
paper-view.cfm?id=20471).<br />
Extended multidisciplinary<br />
efforts start with designing appropriate<br />
content and uniform assessment<br />
mechanisms for courses that encompass<br />
a wide range of projects. It’s<br />
usually necessary to designate a<br />
project coordinator to solicit sufficient<br />
cross-disciplinary content<br />
from internal and external sponsors.<br />
Faculty coaches or advisors must be<br />
assigned to every project along with<br />
a student team. To achieve faculty<br />
buy-in, it may be necessary to give<br />
teaching credit to those working<br />
with project teams.<br />
Accreditation requirements initially<br />
motivate many college-level<br />
multidisciplinary programs. Once<br />
the programs have overcome startup<br />
problems and are steadily operating,<br />
however, the benefits beyond accreditation<br />
become evident.<br />
Ultimately, educators may want to<br />
embrace a multidisciplinary culture<br />
that spans the entire institution—for<br />
example, including business, fine<br />
arts, and liberal arts as well as engineering<br />
and <strong>computing</strong>. This might<br />
be tied to initiatives requiring undergraduate<br />
students to have research or<br />
international study experience.<br />
Cutting across disciplines with<br />
diverse curriculum models adds new<br />
challenges to making multidisciplinary<br />
work a reality. There should<br />
be a way to define projects from any<br />
corner of the campus. Each project<br />
needs at least one faculty member as<br />
an advocate to specify the necessary<br />
team skills.<br />
Every program must offer students<br />
an opportunity for required or elective<br />
multidisciplinary project work.<br />
Students could search a project registration<br />
database for interesting<br />
projects, or the system could suggest<br />
projects based on students’ selfdefined<br />
skill sets.<br />
Some material, such as discussion<br />
of problem-solving techniques<br />
and how to be a good team player,<br />
should be common to all projects or<br />
integrated into prerequisite courses,<br />
perhaps hosted by multiple entities<br />
using different paradigms. Students<br />
could be required to, for example,<br />
take a problem-solving course appropriate<br />
for their home discipline and<br />
one from another area.<br />
To satisfy accreditation requirements,<br />
a faculty member in a<br />
student’s home discipline would<br />
need to review the student’s work<br />
to ensure that he or she has gained<br />
discipline-appropriate experience on<br />
the project.<br />
The pressure on engineering<br />
and <strong>computing</strong> curricula<br />
is to broaden programs<br />
(National Academy of Engineering,<br />
The Engineer of 2020: Vision of Engineering<br />
in the New Century, National<br />
Academies Press, 2004). Many educators<br />
view the current curriculum<br />
model for most programs as being<br />
too focused. I’ve been in meetings<br />
where a view was expressed that<br />
highly structured engineering programs<br />
are a primary impediment<br />
to creative and innovative thought.<br />
I certainly don’t subscribe to that<br />
view, but given the direction that<br />
engineering and <strong>computing</strong> education<br />
is headed, I have some concerns.<br />
Teams work best when they bring<br />
together people with individual depth<br />
in multiple disciplines who are open<br />
to cutting across the disciplines.<br />
Will a collection of broadly trained<br />
students be as effective as one of students<br />
who have depth in their own<br />
individual disciplines?<br />
One benefit of multidisciplinary<br />
projects is the presence of “low-hanging<br />
fruit” between the disciplines.<br />
As institutions broaden programs<br />
and students attain breadth across<br />
disciplines, will educators abandon<br />
individual disciplines themselves<br />
in pursuit of easy-to-pick fruit? Will<br />
students be able to tackle the hard<br />
problems in the individual disciplines<br />
or even in the multidisciplinary<br />
domain?<br />
When redesigning curricula to<br />
incorporate multidisciplinary activities,<br />
educators must be careful. To<br />
students’ potential employers, it could<br />
be a short curricular distance from<br />
“Your students need more breadth”<br />
to “Your students don’t know very<br />
much.”<br />
Jim Vallino is a professor in the<br />
Department of Software Engineering<br />
in the B. Thomas Golisano College of<br />
Computing and Information Sciences<br />
at Rochester Institute of Technology.<br />
Contact him at j.vallino@se.rit.edu.<br />
_____________<br />
Editor: Ann E.K. Sobel, Department of<br />
Computer Science and Software Engineering,<br />
Miami University; sobelae@muohio.edu<br />
____________<br />
Selected CS articles and columns<br />
are available for free at ____<br />
http://<br />
ComputingNow.computer.org.<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
89
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
90<br />
COMPUTER<br />
SECURITY<br />
Integrating Legal<br />
and Policy Factors in<br />
Cyberpreparedness<br />
James Bret Michael, Naval Postgraduate School<br />
John F. Sarkesain, Aerospace Corp.<br />
Thomas C. Wingfield, George C. Marshall European<br />
Center for Security Studies<br />
Georgios Dementis, Hellenic Navy<br />
Gonçalo Nuno Baptista de Sousa, Portuguese Navy<br />
Cyberwarfare countermeasures must consider more than<br />
technological capabilities.<br />
Attacks in cyberspace<br />
are commonplace. The<br />
effects of such attacks<br />
can range from minor<br />
nuisances, such as defacing webpages<br />
or temporarily denying service<br />
to noncritical systems, to major disturbances<br />
that interrupt international<br />
commerce or threaten to destabilize<br />
a nation-state.<br />
Anyone can wage an attack in<br />
cyberspace: individual citizens,<br />
criminal syndicates, terrorist organizations,<br />
even entire nations. Such<br />
attacks can be extremely sophisticated<br />
and involve many actors. The<br />
cyberattacks on Estonia in 2007 by<br />
so-called “patriotic hackers,” criminal<br />
elements that leased out botnets,<br />
and alleged state-sponsored information<br />
warriors combined some<br />
of the characteristics of a military<br />
campaign with those of a covert<br />
operation (www.economist.com/<br />
________________________<br />
world/international/displaystory.<br />
cfm?story_id=E1_JNNRSVS).<br />
__________________<br />
CYBERPREPAREDNESS<br />
Regardless of who perpetrates<br />
a cyberattack, defenders of the<br />
attacked systems must be prepared<br />
to respond, even if only to mitigate<br />
the attack’s effects. Cyberpreparedness<br />
can be said to have three<br />
dimensions (E. Tikk and T. Wingfield,<br />
“Frameworks for International Cyber<br />
Security: The Cube, the Pyramid, and<br />
the Screen,” presentation, Int’l Cyber<br />
Conflict Legal and Policy Conf., 2009):<br />
technical feasibility—the<br />
“possible”;<br />
legal—the “permissible”; and<br />
policy—the “preferable.”<br />
From a technical vantage, a<br />
defender could use a computerbased<br />
tool such as NetSPA to assess<br />
a computer network’s vulnerability<br />
to attack and develop appropriate<br />
countermeasures (K. Ingols et al.,<br />
“Modeling Modern Network Attacks<br />
and Countermeasures Using Attack<br />
Graphs,” Proc. Ann. Comp. Security<br />
Applications Conf., IEEE, 2009, pp. 117-<br />
126). However, a defender also needs<br />
a distributed command, control, and<br />
battle management (C2/BM) system<br />
to maintain situational awareness of<br />
and respond to cyberattacks in nearreal<br />
time (N. Howes, M. Mezzino,<br />
and J. Sarkesain, “On Cyber Warfare<br />
Command and Control Systems,”<br />
Proc. 9th Ann. Int’l Command and Control<br />
Research and Technology Symp.,<br />
2004; www.dodccrp.org/events/9th_<br />
____________________<br />
ICCRTS/CD/papers/118.pdf).<br />
_________________<br />
LAW AND POLICY<br />
Turning now to the “permissible”<br />
and “preferable,” the customary<br />
guiding principles of jus in bello,<br />
“customary legal standards for the<br />
conduct of war”—discrimination,<br />
necessity, proportionality, and chivalry—also<br />
apply to cyberwarfare,<br />
as does the jus ad bellum, “law governing<br />
the transition from peace to<br />
war” (J.B. Michael, “On the Response<br />
Policy of Software Decoys: Conducting<br />
Software-Based Deception in<br />
the Cyber Battlespace,” Proc. 26th<br />
Ann. Int’l Computer Software and<br />
Apps. Conf., IEEE, 2002, pp. 957-962).<br />
Cyberattacks can have the equivalent<br />
effects of attacks waged with kinetic<br />
weapons, rising to the level of a “use<br />
of force” under international law (J.B.<br />
Michael, T. Wingfield, and D. Wijesekera,<br />
“Measured Responses to Cyber<br />
Attacks Using Schmitt Analysis: A<br />
Case Study of Attack Scenarios for<br />
a Software-Intensive System,” Proc.<br />
Published by the IEEE Computer Society 0018-9162/10/$26.00 © 2010 IEEE<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
26th Ann. Int’l Computer Software<br />
and Applications Conf., IEEE, 2003,<br />
pp. 622-627).<br />
Thus, regardless of the technical<br />
measures used, law and policy must<br />
be in place to guide defenders as<br />
they craft responses to cyberattacks.<br />
Although a response might be legal,<br />
policy dictates the latitude in applying<br />
the law, taking into consideration<br />
such factors as the impact on society,<br />
diplomatic relations, and even<br />
privacy concerns, such as a given<br />
response’s level of intrusiveness. The<br />
currency of the topic of cyberpreparedness<br />
is evidenced by the recent<br />
front-page news account of the legal<br />
and policy discussions that ensued<br />
prior to the cyberattack sponsored<br />
by the US Department of Defense to<br />
dismantle an online forum used by<br />
terrorists to plan kinetic attacks on<br />
US troops (E. Nakashima, “For Cyberwarriors<br />
Murky Terrain; Dismantling<br />
of Saudi-CIA Web Site Illustrates need<br />
for Clearer Cyberwar Policies,” The<br />
Washington Post, 19 March 2010, pp.<br />
A1 and A16). Policy issues included<br />
the impact on US-Saudi relations and<br />
whether the response should be conducted<br />
as an intelligence or military<br />
operation.<br />
In addition, techniques for conducting<br />
principled analyses must be<br />
ready to help minimize legal uncertainty<br />
about cyberincidents and allow<br />
the most complete range of effective<br />
responses. Whether the response is<br />
conducted via kinetic or cyber means,<br />
it must be lawful (T. Wingfield, The<br />
Law of Information Confiict: National<br />
Security Law in Cyberspace, Aegis<br />
Research Corp., 2000).<br />
LEVERAGING THE<br />
LEGAL CELL<br />
We propose merging the three<br />
dimensions of cyberpreparedness<br />
by adding a new type of virtual cell<br />
to cybersystems: the legal cell.<br />
Virtual cells within such systems<br />
serve as dynamic virtual<br />
communities in which cyberopera-<br />
tors can interact in support of making<br />
informed decisions. Cyberoperators<br />
encompass subject-matter experts<br />
in cyberoperations along with the<br />
related communities of the diplomatic<br />
corps, intelligence analysts, the<br />
military, politicians, legal authorities,<br />
law-enforcement agents, economists,<br />
and those responsible for creating<br />
and maintaining the national critical<br />
infrastructure. Cyberoperators can<br />
create, join, leave, and even dissolve<br />
cell instantiations.<br />
The legal cell provides cyberoperators<br />
with the means to obtain<br />
advice from experts in information<br />
operations (IO) law. Within cyber C2/<br />
BM systems, cells subscribe to infor-<br />
We propose merging<br />
the three dimensions<br />
of cyberpreparedness<br />
by adding a new type<br />
of virtual cell to cybersystems:<br />
the legal cell.<br />
mation and the system publishes it<br />
continuously in a digestible format.<br />
This differs from the information-pull<br />
approach incorporated into most of<br />
today’s C2/BM systems when used in<br />
conjunction with kinetic warfare.<br />
Through the legal cell, IO experts<br />
can maintain a current picture of the<br />
cyberspace situation and provide<br />
advice as needed. This is an important<br />
capability, given the rapid tempo<br />
of cyberbattles and the high degree<br />
of space compression, which asserts<br />
that the physical distance from a<br />
target does not matter as it would<br />
with kinetic weapons and that a<br />
flattened command structure is necessary<br />
for conducting cyberwarfare.<br />
On instantiation of a legal cell, the<br />
system populates it with presumptions<br />
and algorithms. In this context,<br />
presumptions follow black-and-white<br />
if-then rules automatically enacted by<br />
mobile agents, whereas algorithms<br />
involve more complex data processing<br />
than with production rules but,<br />
like presumptions, are processed<br />
without human intervention and<br />
whose results trigger a course of<br />
action.<br />
These three elements—the law,<br />
presumptions, and algorithms—are<br />
what Tikk and Wingfield refer to as<br />
the “pyramid,” representing decision<br />
making along a continuum of<br />
operational speed and the inherent<br />
limitations on what types of problems<br />
computers solve in support of decision<br />
making.<br />
ATTACK RESOLUTION<br />
Given the unpredictability and<br />
quickness of cyberattacks, a rapid<br />
response is critical, necessitating<br />
use of at least some autonomic<br />
systems. According to a report by<br />
the National Institute of Standards<br />
and Technology (NIST) outlining a<br />
smart grid cybersecurity strategy<br />
and requirements (http://csrc.nist.<br />
gov/publications/drafts/nistir-7628/<br />
draft-nistir-7628_2nd-public-draft.<br />
__<br />
pdf).<br />
Ultimately, the cyberoperation<br />
leader will ascertain the effect of<br />
the attack’s automated response,<br />
particularly in the military because<br />
a commander cannot delegate<br />
responsibility for the actions of their<br />
command. While a commander may<br />
delegate the authority to execute<br />
certain actions on to a subordinate<br />
within the command, the commander<br />
still retains full and complete responsibility<br />
for the outcome of those<br />
delegated actions, for good or bad.<br />
Some defensive systems that involve<br />
using kinetic weapons require extensive<br />
automation, such as those used<br />
for ballistic missile defense, in which<br />
the duty cycle for core functions of<br />
the so-called “kill chain”—detect,<br />
track, assign weapons, engage, and<br />
assess outcome—cannot be performed<br />
by humans swiftly enough to<br />
achieve the desired levels of operational<br />
effectiveness.<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
91
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
92<br />
COMPUTER<br />
SECURITY<br />
An example of a presumption in<br />
this context is: “If a tracked object<br />
enters a restricted airspace, then<br />
assign a weapon to that object and<br />
engage.” An instance of engaging<br />
the human operator would occur if,<br />
for example, the US were to have a<br />
chance to intercept missiles over<br />
another country. In this case, intercepting<br />
the missiles would be lawful<br />
but the potential consequences—<br />
such as residual debris from the<br />
missiles’ chemical, nuclear, or biological<br />
payloads landing on the other<br />
country’s territory—would need to be<br />
weighed against the risk of the missiles<br />
reaching their targets.<br />
Other aspects of preparedness<br />
could be incorporated into cyber<br />
C2/BM systems, such as a brokering<br />
capability to facilitate controlled dissemination<br />
of information among<br />
cyberoperators from different<br />
administrative domains who are collaborating<br />
in an ad hoc but formal<br />
coalition, or persistent operations to<br />
defend assets through their combined<br />
cyberwarfare resources.<br />
For example, a legal advisor might<br />
need to subscribe to certain data<br />
feeds to pull together the information<br />
required to make a legal determination,<br />
but he or she might not have a<br />
need to know about where the data<br />
originated or related information.<br />
That is, the brokering capability provides<br />
a means for enabling the sharing<br />
of information by protecting the anonymity<br />
of the information sources<br />
and their methods of collection, only<br />
sharing what cyberoperators playing<br />
particular roles are entitled to access.<br />
Such an information-sharing capability<br />
would have been useful to the<br />
informal assembly of private- and<br />
public-sector organizations that came<br />
to the aid of Estonia in 2007.<br />
Systems have become increasingly<br />
interconnected through trends such<br />
as the adoption of cloud <strong>computing</strong><br />
and the creation of systems of systems.<br />
These compositions provide<br />
one or more value-added capabilities<br />
that none of the individual systems<br />
can deliver on their own. Preparedness<br />
for cyberattacks will entail<br />
cooperation between the many stakeholders<br />
in these systems, even with<br />
sound mechanisms for containment<br />
of behavior between systems.<br />
Efforts at achieving cyberpreparedness,<br />
such as that by NIST, are<br />
a step in the right direction, as the<br />
NIST report on the smart grid shows:<br />
Some of the responses [to cyber<br />
attacks] must be autonomic—timely<br />
response is a critical requirement for<br />
grid reliability. However, for a quick<br />
response to treat the symptom locally<br />
and effectively, the scope and extent<br />
of the impact of the failure needs to be<br />
quickly determined. Not all responses<br />
are autonomic however. New research<br />
is needed to measure and identify<br />
the scope of a cyber attack and the<br />
dynamic cyber threat response options<br />
available in a way that can serve as a<br />
decision support tool for the human<br />
operators.<br />
We believe that our<br />
research is on target<br />
regarding support for<br />
cyber command-and-control understanding,<br />
planning, and decision<br />
activities. Preparation must include<br />
provision of integrated full-spectrum<br />
capabilities in cyber C2/BM systems<br />
along with specialized dynamic virtual<br />
cells like the proposed legal cell<br />
enabling collaboration among cyberoperators<br />
proactively.<br />
James Bret Michael is a professor in<br />
the Department of Computer Science<br />
and a member of the Center for Cyber<br />
Warfare at the Naval Postgraduate<br />
School. Contact him at bmichael@<br />
nps.edu.<br />
_____<br />
John F. Sarkesain is a senior engineer<br />
with the Aerospace Corporation. Contact<br />
him at john.f.sarkesain@aero.org.<br />
Thomas C. Wing eld is a professor<br />
at the George C. Marshall European<br />
Center for Security Studies. Contact<br />
him at ____________________<br />
thomas.c.wing eld@marshallcenter.org.<br />
_______<br />
Georgios Dementis is a lieutenant<br />
in the Hellenic Navy. Contact him at<br />
ydementis@gmail.com.<br />
_______________<br />
Gonçalo Nuno Baptista de Sousa is<br />
a lieutenant in the Portuguese Navy.<br />
Contact him at _______________<br />
goncalobsousa@gmail.<br />
___ com.<br />
Editor: Jeffrey Voas, National Institute<br />
of Standards and Technology;<br />
j.voas@ieee.org<br />
_________<br />
________<br />
_________________<br />
Disclaimer<br />
The views and conclusions<br />
contained herein are those<br />
of the authors and should not<br />
be interpreted as necessarily<br />
representing the official policies<br />
or endorsements of the US<br />
Government.<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
BOOKSHELF<br />
Topology for Computing, Afra<br />
J. Zomorodian. This emerging<br />
field utilizes theory from<br />
topology and the power of <strong>computing</strong><br />
to solve problems in diverse fields.<br />
Recent applications include computer<br />
graphics, CAD, and structural<br />
biology, all of which involve understanding<br />
the intrinsic shape of some<br />
real or abstract space. The author<br />
strives to present basic concepts<br />
from topology and Morse theory so<br />
that nonspecialists can grasp and<br />
participate in current research in<br />
computational topology.<br />
This book’s self-contained presentation<br />
of mathematical concepts<br />
from a computer scientist’s viewpoint<br />
combines point set and algebraic<br />
topologies, group theory, differential<br />
manifolds, and Morse theory. The<br />
author also presents some recent<br />
advances in the area, including topological<br />
persistence and hierarchical<br />
Morse complexes. Throughout, the<br />
focus is on computational challenges<br />
and presenting algorithms and data<br />
structures when appropriate.<br />
Cambridge University Press; ____ www.<br />
cambridge.org; ISBN-978-0-521-<br />
13609-9, 258 pp.<br />
Symbolic Dynamics and Geometry<br />
Using D* in Graphics and Game<br />
Programming, Brian Guenter and<br />
Sung-Hee Lee. The authors explain<br />
how to use the D* symbolic-differentiation<br />
system for applications<br />
in computer games and engineering<br />
simulation. They describe how<br />
to create procedural 3D geometric<br />
models, link them together to form<br />
multibody physical systems, and<br />
simulate and display their physical<br />
behavior in real time.<br />
The symbolic-differentiation capabilities<br />
of D* can be used in a wide<br />
variety of technical applications,<br />
including computer graphics, engineering,<br />
and mechanical simulation.<br />
Many applications of D* are covered,<br />
but two—real time Lagrangianphysics<br />
simulation and procedural 3D<br />
0018-9162/10/$26.00 © 2010 IEEE<br />
geometric modeling—are developed<br />
in great detail.<br />
A K Peters, Ltd; www.akpeters.<br />
___ com; ISBN-978-1-56881-280-9,<br />
250 pp.<br />
Leading the Virtual Workforce:<br />
How Great Leaders Transform<br />
Organizations in the 21st Century,<br />
Karen Sobel Lojeski. Just 20 years<br />
ago, going to work meant driving<br />
to a physical location to interact<br />
face-to-face with a boss and coworkers.<br />
Today, this might only require<br />
stepping across the hall to a home<br />
office or joining a videoconference.<br />
According to the author, the implications<br />
of these changes are staggering<br />
and require a whole new leadership<br />
model. She asserts that the virtual<br />
workforce has exploded, with mobile<br />
workers set to become 73 percent of<br />
the US workforce by 2011.<br />
According to Lojeski, physical separation,<br />
technology mediation, and<br />
disconnected relationships characterize<br />
this new virtual distance. These<br />
dynamics lead to a psychological<br />
separation that negatively affects<br />
productivity, innovation, and trust.<br />
When virtual distance is relatively<br />
high, innovation falls by more than<br />
90 percent and project performance<br />
suffers. The author concludes that<br />
creating context, cultivating community,<br />
and co-activating new leaders<br />
builds greater trust, higher levels<br />
of satisfaction, and better behavior<br />
overall.<br />
Wiley; www.wiley.com; 978-0-470-<br />
42280-9; 512 pp.<br />
Touch of Class: Learning to Program<br />
Well with Objects and<br />
Contracts, Bertrand Meyer. The<br />
author provides an introductory<br />
programming text that can make<br />
learning to program fun and rewarding.<br />
Instead of traditional low-level<br />
examples, Meyer builds his presentation<br />
on a rich object-oriented<br />
software system supporting graphics<br />
and multimedia, which students can<br />
Published by the IEEE Computer Society<br />
use to produce applications from day<br />
one. They can then explore “from the<br />
outside in” as they learn new programming<br />
techniques.<br />
Coverage is notable in both its<br />
depth and breadth. In addition to<br />
core programming concepts such<br />
as control structures, algorithms,<br />
and fundamental data structures, it<br />
encompasses recursion, reference<br />
and pointer manipulation, and topological<br />
sort as examples of algorithm<br />
and API design, event-driven programming,<br />
and high-level function<br />
closures.<br />
Springer; www.springer.com; 978-<br />
3-540-92144-8; 876 pp.<br />
Inside Larry and Sergey’s Brain,<br />
Richard L. Brandt. This book<br />
focuses on what drives these two<br />
men and where they will take Google.<br />
Looking at this brainchild of two brilliant<br />
minds, the author examines<br />
Google’s business decisions in light<br />
of its founders’ ambitions and beliefs.<br />
Larry is the main strategist, while<br />
Sergey is the primary technologist<br />
and idealist. Through interviews with<br />
current and former employees, competitors,<br />
partners, and senior Google<br />
management, the author demystifies<br />
the secret society that is Google while<br />
clarifying several misconceptions.<br />
Viking Press; http://us.penguingroup.<br />
___ com/; 978-1-59184-276-7; 256 pp.<br />
Send book announcements to<br />
___<br />
newbooks@computer.org.<br />
APRIL 2010 93<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
94<br />
COMPUTER<br />
THE PROFESSION<br />
Currently, it has taken the form of an<br />
eBook reader with an easy-to-read<br />
display. However, even when we leverage<br />
an innovative distribution system<br />
using wireless technology, presenting<br />
static books falls short of employing<br />
the computer to full advantage.<br />
With larger displays, fiexible and<br />
lightweight units, and full color we<br />
may see more dramatic changes.<br />
Will eInk replace printed paper in<br />
all domains or be the savior of traditional<br />
newspapers? If the technology<br />
matures the consequences will be<br />
dramatic for many industries. But this<br />
particular if entails speculation.<br />
Instead of focusing on possible<br />
advances in new technologies, we<br />
observe that change may also come<br />
based on ingredients that have been<br />
present for some time. Email and TCP/<br />
IP provide good examples. It took<br />
many years from when the technology<br />
and standards emerged to when<br />
they saturated society and made a<br />
major impact.<br />
POS<br />
The technology that provides<br />
our case study here is the simple<br />
point-of-sale (POS) terminal. This<br />
technology was not developed to<br />
change the world, but simply to<br />
make monetary transactions easier.<br />
By using a credit or cash card, the<br />
terminal lets us perform an alldigital<br />
transaction with no cash<br />
involved. The advantages of this<br />
are so substantial that in many<br />
countries a large percentage of all<br />
monetary transactions are digital,<br />
based on POS terminals or using<br />
credit cards over the Internet. Data<br />
is captured automatically and can be<br />
transferred at almost no cost.<br />
At the same time, this information<br />
can be used directly for inventory<br />
Continued from page 96<br />
control, accounting, and statistics.<br />
In my home country, Norway, people<br />
can avoid cash altogether, because<br />
all shops, hotels, restaurants, gas stations,<br />
cabs, and many buses allow<br />
digital payment. Most banks offer free<br />
service, and cards are used also for<br />
very small amounts. Even the pizza<br />
boy brings along a wireless POS terminal.<br />
Looking at value, 98 percent of<br />
all monetary transactions in Norway<br />
are digital. In Stockholm, people can<br />
even pay their bus fare by cell phone.<br />
Small countries have an advantage<br />
and can often offer high dissemination<br />
numbers for new technologies.<br />
National standards are easier to<br />
implement in a small country than in<br />
a large one. Fewer installations make<br />
it easier to update equipment, while<br />
a homogeneous population makes it<br />
Small countries have an advantage and can often offer<br />
high dissemination numbers for new technologies.<br />
simpler for people to accept new services.<br />
However, larger countries are<br />
following suit in the digital economy.<br />
A few years ago travelers needed<br />
cash when in cities such as Rome and<br />
Madrid. Today nearly all businesses<br />
accept a card.<br />
CASHfiFREE SOCIETY<br />
When only a small fraction of<br />
transactions are in cash an interesting<br />
question arises: Can we remove<br />
cash altogether? Money, in the form<br />
of coins, has been in use for nearly<br />
three thousand years. Paper bills<br />
have been used in Europe for nearly<br />
four hundred years, and much longer<br />
than that in China. It seems dramatic<br />
to convert to a true digital economy.<br />
There are, however, many advantages<br />
to going digital. Great savings<br />
can be achieved for businesses if we<br />
avoid storing, counting, handling, and<br />
transporting cash.<br />
The advantages for society<br />
as a whole may be even greater,<br />
especially if cash is removed altogether.<br />
As we learn from the news<br />
every day, cash encourages crime.<br />
The public may experience that a<br />
wallet is stolen from a pocket, or<br />
more severely, become the victim<br />
of armed robbery. Institutions such<br />
as banks and security transports<br />
must spend signiflcant resources to<br />
thwart criminals and sometimes still<br />
fail to deter them. Death and both<br />
physical and psychological injuries<br />
can be the consequences of holding<br />
all this “bait” in the form of cash.<br />
It would be naive to expect crime<br />
to disappear in a digital economy.<br />
Credit card fraud is already a daily<br />
occurrence. However, today it is stimulated<br />
by the possibility of retrieving<br />
the stolen money in cash from ATMs.<br />
Without cash it will be much easier to<br />
follow the transactions.<br />
We can, however, realistically<br />
hope to make being a criminal less<br />
convenient. A monetary economy is<br />
much more effective than bartering.<br />
People understood this thousands<br />
of years ago. It was easier then to<br />
sell a horse for money that could be<br />
spent freely than to trade it for a cow<br />
and some chickens on the side. The<br />
seller might not need chickens, or the<br />
potential horse buyer might not have<br />
a cow for sale.<br />
What we could expect by going<br />
digital is to enjoy the advantages of<br />
the monetary system without being<br />
threatened by criminals. The pusher<br />
down the street, for example, would<br />
have problems if customers no longer<br />
had anonymous cash handy for their<br />
transactions. They would be forced to<br />
accept gold, PCs, TVs, and refrigerators<br />
instead, thereby confronting all<br />
the hassles of a barter economy.<br />
DIGITAL CRIME<br />
Criminals can also go digital,<br />
although this requires <strong>computing</strong><br />
competence. Today, with improved<br />
information security systems, successful<br />
cybercrime implies a fairly<br />
high level of competence. Such skill<br />
can also be sold in the open economy<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
at lucrative prices, and digital criminals<br />
can be thwarted by digital police.<br />
Some tasks, such as detecting whitewashing,<br />
might even be performed<br />
automatically.<br />
Do we see big brother here? Cash<br />
is anonymous while digital money<br />
can be tracked. For ordinary lawabiding<br />
citizens this should not<br />
be considered a threat as long as<br />
good laws to protect public privacy<br />
remain in place. However,<br />
tax authorities now have a weapon<br />
against the black market economy.<br />
For example, it won’t be so easy to<br />
pay the carpenter, off-the-record,<br />
without cash. Some might view this<br />
as a disadvantage, but we will gain<br />
instead a more fair tax system and<br />
increased state income.<br />
Willing or not, we are moving<br />
slowly but smoothly into a cashfree<br />
society. Today the $100 bill is<br />
the highest denomination in circulation,<br />
with $500, $1,000, $5,000,<br />
and $10,000 bills no longer used.<br />
As inflation takes a percentage of<br />
the real value of the $100 bill every<br />
year, we will soon only have cash<br />
as small change. On the fiip side, it<br />
is interesting to note that the US still<br />
has a one-cent coin. In Norway, the<br />
lowest valued coin is now flfty øre or<br />
approximately nine cents, up from<br />
the one øre that was removed from<br />
circulation in 1972.<br />
The process toward a cash-free<br />
society will be accelerated when the<br />
real costs of using cash are placed on<br />
the individual cash-paying customer,<br />
not shared among all customers. The<br />
growth of true Internet banks, where<br />
all transactions are digital, poses a<br />
severe threat to banks that still have<br />
high cash handling costs. It might<br />
also become more awkward to use<br />
cash. Many countries now require a<br />
national bank notiflcation whenever<br />
large sums are withdrawn or deposited<br />
as cash. We could go further,<br />
perhaps placing a risk tax on the<br />
use of cash to compensate for public<br />
injury and other expenses that follow<br />
from robberies.<br />
RISK<br />
Computing professionals must<br />
be concerned about the risk of getting<br />
into a situation where people<br />
no longer have cash as a backup.<br />
Truthfully, though, we have already<br />
reached this stage. Look into your<br />
wallet and count the bills. Is that<br />
amount sufflcient for food, rent, gas,<br />
and all other expenses? For how long?<br />
While there have been incidents of<br />
credit card and banking system hacking,<br />
computer security is steadily<br />
improving. As with cars, safety only<br />
became an issue late in the technology’s<br />
development. First we had to<br />
solve the “important” problems: getting<br />
the systems to run, making their<br />
services affordable, adding core functionality,<br />
and offering a commercially<br />
aesthetic design.<br />
Most likely, one of the small countries<br />
will flrst take the leap toward<br />
an all-digital economy. As I have<br />
noted, it is easier to get the necessary<br />
infrastructure in place. This<br />
may be done to issue cash cards<br />
to persons who do not qualify for<br />
commercial banking services, or to<br />
implement improved ID systems and<br />
other safeguards. It is also easier to<br />
remove cash from a currency in use<br />
on a national level only, unlike the<br />
dollar and euro, which already have<br />
widespread acceptance.<br />
Given that there are clear<br />
advantages to being the<br />
flrst country to go all digi-<br />
IEEE<br />
THE #1 ARTIFICIAL<br />
INTELLIGENCE<br />
MAGAZINE!<br />
tal, we can expect this development<br />
to happen sooner rather than later.<br />
Crimes will be averted, and national<br />
industry and service providers will<br />
have a home market for technologies<br />
that might be in widespread use in<br />
just a few years.<br />
This transition to a digital economy<br />
can be performed in measured<br />
steps, starting with removing the<br />
high-denomination bills and placing<br />
cash-handling costs on the<br />
shoulders of cash-paying customers.<br />
This process could persist until the<br />
economy is fully digital, or banks<br />
might see a beneflt in keeping smalldenomination<br />
bills and coins in circulation.<br />
As <strong>computing</strong> professionals,<br />
we are privileged to take part in these<br />
dramatic historic developments.<br />
Ultimately, we should consider it an<br />
improvement if bandits replace guns<br />
with keyboards—there will at least<br />
be fewer injuries.<br />
Kai A. Olsen is a professor at Molde<br />
College and the University of Bergen,<br />
and is an adjunct professor at the University<br />
of Pittsburgh. Contact him at<br />
_______________<br />
Kai.Olsen@himolde.no.<br />
Editor: Neville Holmes, School of Computing<br />
and Information Systems, University of<br />
Tasmania; neville.holmes@utas.edu.au<br />
________________<br />
Selected CS articles and columns<br />
are available for free at ____<br />
http://<br />
_________________<br />
ComputingNow.computer.org.<br />
IEEE Intelligent Systems delivers<br />
the latest peer-reviewed research on<br />
all aspects of artificial intelligence,<br />
focusing on practical, fielded applications.<br />
Contributors include leading experts in<br />
<br />
<br />
<br />
Visit us on the Web at<br />
www.computer.org/intelligent<br />
APRIL 2010<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
95
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
96<br />
COMPUTER<br />
THE PROFESSION<br />
Computing a<br />
Better World<br />
Kai A. Olsen,<br />
Molde College and University of Bergen, Norway<br />
While government leaders struggle to implement significant<br />
change, <strong>computing</strong> professionals increasingly achieve this goal<br />
as a side-effect.<br />
As <strong>computing</strong> professionals<br />
we have been<br />
involved in many projects.<br />
Most have had a<br />
limited scope, duration, and budget.<br />
These milestones span decades, from<br />
developing a system for sending text<br />
messages between universities and<br />
research centers in 1969, to manufacturing<br />
a chip for a calculator in<br />
1971, to setting standards for electronic<br />
communication in 1974, to<br />
designing a computer system that<br />
offers an improved user experience<br />
in 1981, to simplifying access to scientiflc<br />
papers in 1990, to developing<br />
new technologies for ranking Web<br />
pages in 1996, and to creating an<br />
online student directory with photos<br />
in 2003.<br />
I suspect few people involved in<br />
these projects had any idea they were<br />
changing the world. Yet, in retrospect,<br />
we see this is what really happened.<br />
The Arpanet project gave us the flrst<br />
e-mail system in 1969, Intel developed<br />
the microprocessor in 1971, and an<br />
international effort gave us the TCP/<br />
IP standard for data communication<br />
in 1974. Then, in 1981, researchers<br />
at Xerox Parc designed the flrst<br />
complete graphical workstation; Tim<br />
Berners Lee deflned the basis for the<br />
World Wide Web at CERN in 1990,<br />
Larry Page and Sergey Brin created<br />
the foundations for Google in 1996,<br />
and Mark Zuckerberg created Facebook<br />
in 2003.<br />
CHANGING LIVES<br />
Combined, these <strong>computing</strong><br />
advances have changed the <strong>lives</strong> of<br />
millions throughout the world. In the<br />
industrial countries we work, shop,<br />
play, and socialize using a computer.<br />
Whole business areas are experiencing<br />
this revolution. Music, movies,<br />
and books are now separated from<br />
their physical representation, with<br />
a consequently huge impact on the<br />
industry. Photography has gone<br />
digital. Analog products, such as<br />
fllm, cameras, and their connected<br />
services—are now disappearing.<br />
Newspapers that have existed for<br />
more than 200 years are in danger<br />
of closing down as the competition<br />
from the net becomes overwhelming.<br />
Meanwhile, TV is losing viewers to the<br />
Internet and sites like YouTube.<br />
Physical libraries, with collections<br />
in the form of clay tablets, papyrus,<br />
or books, have been an integral<br />
part of educational institutions for<br />
thousands of years. Today digital<br />
collections are taking over and the<br />
physical library has an uncertain<br />
future in many domains. Companies<br />
that hardly existed flve to ten years<br />
ago—such as Google, Facebook, and<br />
Twitter—are today known by everybody.<br />
New services and applications<br />
are offered every day to make our<br />
<strong>lives</strong> more effective and, perhaps,<br />
more interesting. It is tempting to<br />
compare these trends with politics.<br />
While many state leaders struggle to<br />
implement signiflcant change, <strong>computing</strong><br />
professionals increasingly<br />
achieve this as a side-effect.<br />
CATALYST<br />
Clearly, the <strong>computing</strong> industry<br />
is today’s main catalyst for change.<br />
No other industry has a comparable<br />
impact and none is as dynamic. As<br />
professionals in this area we are<br />
truly shaping the world into something<br />
better—or so we hope. Some<br />
argue that <strong>computing</strong> has become<br />
a commodity, like electricity, something<br />
you still need but that has lost<br />
its competitive advantage. However,<br />
the Googles, YouTubes, Wikipedias,<br />
and Twitters show that the pace has,<br />
if anything, accelerated. So what can<br />
we expect in the next decennium?<br />
eInk offers one new technology<br />
that flows from <strong>computing</strong>. In the<br />
past 10 years it has moved from the<br />
labs to commercial product status.<br />
Continued on page 94<br />
Published by the IEEE Computer Society 0018-9162/10/$26.00 © 2010 IEEE<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
_____________________<br />
____________________________<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F<br />
Running in<br />
Circles<br />
Looking for<br />
a Great<br />
Computer<br />
Job or Hire?<br />
The IEEE Computer Society Career Center is the best niche<br />
employment source for computer science and engineering jobs, with<br />
hundreds of jobs viewed by thousands of the finest scientists each<br />
month - in Computer magazine and/or online!<br />
_____________________________________________________<br />
http://careers.computer.org<br />
The IEEE Computer Society Career Center is part of the Physics Today Career Network, a niche job board<br />
network for the physical sciences and engineering disciplines. Jobs and resumes are shared with four partner<br />
job boards - Physics Today Jobs and the American Association of Physics Teachers (AAPT), American Physical<br />
Society (APS), and AVS: Science and Technology of Materials, Interfaces, and Processing Career Centers.<br />
> Software Engineer<br />
> Member of Technical Staff<br />
> Computer Scientist<br />
> Dean/Professor/Instructor<br />
> Postdoctoral Researcher<br />
> Design Engineer<br />
> Consultant<br />
A<br />
Computer Previous Page | Contents | Zoom in | Zoom out | Front Cover | Search Issue | Next Page M S BE<br />
aG<br />
F